Cloud computing security: A CXO framework for resilience

Summary
Cloud computing security in 2026 is an imperative for business resilience. This article outlines how enterprises must move beyond perimeter defense to a layered, identity-centric security architecture aligned with the shared responsibility model. It explores core pillars such as Zero Trust, IAM, CSPM, DevSecOps, AI-driven detection, and multi-cloud governance, while highlighting maturity progression and executive strategies to reduce risk, ensure compliance, and protect enterprise value.
Cloud adoption has reached a point where security can no longer be treated as a technical afterthought. In 2026, cloud security is directly tied to business continuity, regulatory exposure, and operational resilience. The challenge is now about protecting a constantly moving data lifecycle across identities, APIs, workloads, devices, and third-party connectors.
Cloud computing security refers to the policies, technologies, and controls used to protect cloud-based data, applications, and infrastructure. But in practice, it is also the discipline of ensuring cloud environments remain secure while they scale, change, and distribute across multiple platforms.
The shared responsibility model: Where cloud security really begins
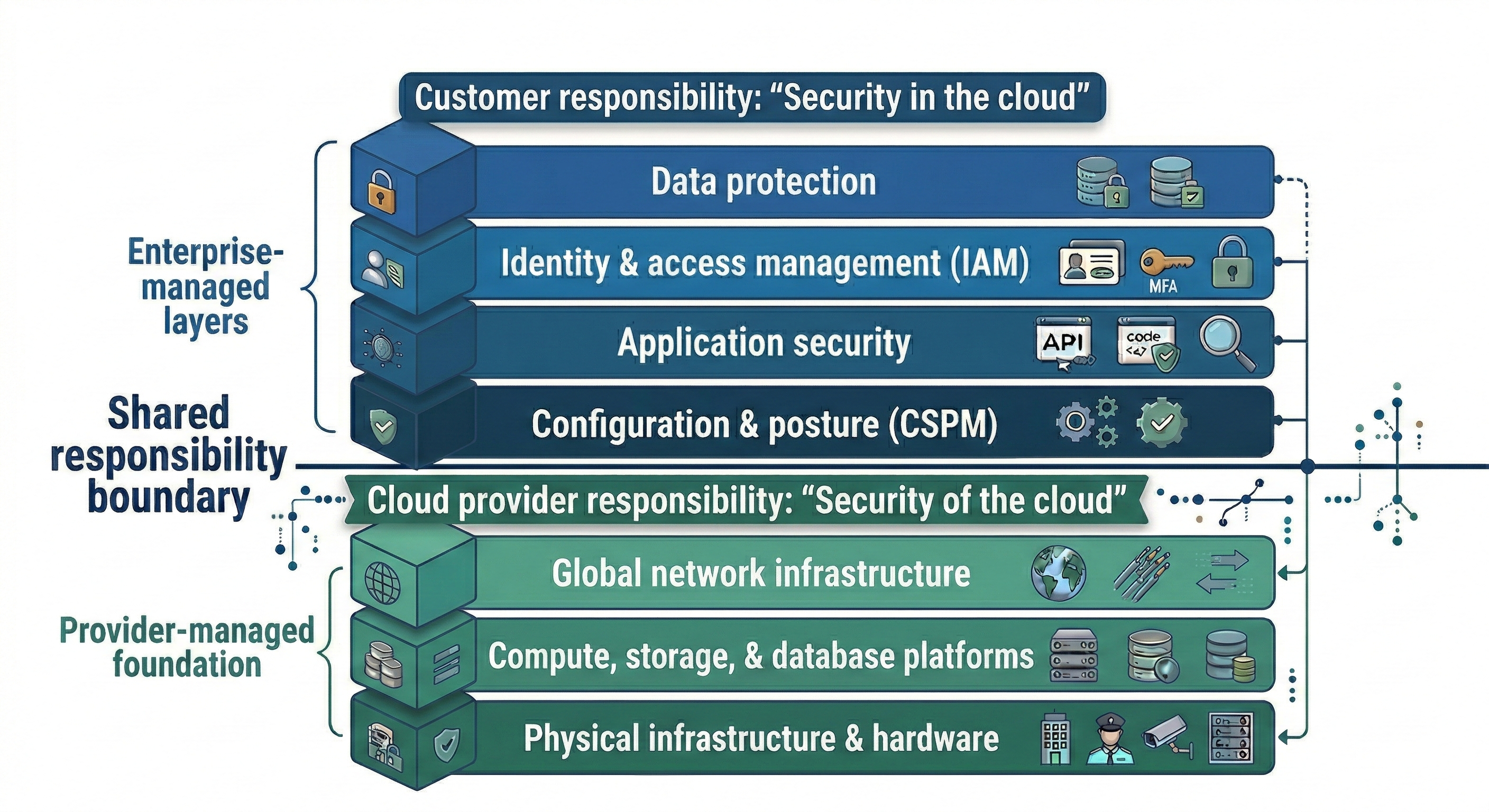
One of the biggest misconceptions in cloud security is assuming the provider is responsible for everything. Cloud providers are responsible for the security of the cloud itself, covering the physical data centers, underlying hardware, global network infrastructure, and foundational platform components.
Enterprises remain responsible for “security in the cloud,” including identity, data protection, configuration security, access governance, and application-layer risk.
In 2026, this model is becoming harder to interpret because of serverless and AI-native services. When enterprises rely on managed runtimes, AI services, and automated workflows, they gain speed, but they also inherit security risk where visibility and accountability are less obvious.
Core pillars of a 2026 cloud computing security framework
Cloud security programs that scale successfully are built around a few core pillars. These pillars cover both technical controls and operational discipline, which is critical in multi-cloud, hybrid, and highly regulated environments.
Zero Trust Architecture (ZTA): “Never trust, always verify”
Zero trust has moved from a concept to a practical requirement. In cloud environments, trust cannot be assumed based on location, network segment, or device type. Instead, every request must be continuously validated using identity, device posture, access context, and risk signals. This reduces the likelihood of credential-based attacks turning into large-scale lateral movement across cloud services.
Identity and Access Management (IAM): Least privilege plus non-human identity control
IAM is now the control plane for cloud security. Misconfigured permissions remain one of the fastest ways for attackers to escalate privileges and access sensitive systems. At the same time, enterprises now manage far more non-human identities than human ones. Service accounts, automation bots, CI/CD identities, API tokens, and AI agents often have broad access with weak governance. In modern cloud environments, these identities are frequently the highest-risk security surface.
Data sovereignty and encryption: Securing the full data lifecycle
Cloud security is increasingly shaped by regulation, especially across healthcare, banking, and public sector environments. This introduces the need for stronger data sovereignty controls, sometimes referred to as geopatriation, where data must be stored, processed, and governed according to local legal requirements. Encryption remains foundational, but modern strategies also include confidential computing, which protects data even while it is being processed.
DevSecOps and shift-left security: Security without slowing delivery
DevSecOps is now essential for preventing cloud security from becoming a bottleneck. Security controls must be embedded into CI/CD pipelines so vulnerabilities and misconfigurations are detected early, when fixes are faster and cheaper. This includes security testing, dependency scanning, IaC validation, and policy checks as part of normal development workflows.
Cloud security posture management (CSPM): Continuous control over misconfigurations
Misconfigurations are still one of the most common causes of cloud exposure. CSPM platforms help organizations detect issues such as open storage, overly permissive access policies, missing encryption, or weak logging settings. The biggest value comes when CSPM moves beyond reporting and enables automated remediation, reducing exposure windows from weeks to minutes.
AI-driven threat detection: Finding what humans cannot see
Cloud environments generate massive volumes of logs, metrics, identity events, and API activity. AI-driven detection helps identify abnormal patterns such as suspicious access behavior, privilege escalation attempts, unusual workload activity, or token misuse. This is particularly important in cloud attacks, where adversaries often exploit permissions and APIs quietly rather than using obvious malware.
Managing multi-cloud and hybrid complexity: Closing the visibility gap
Most enterprises operate across AWS, Azure, SaaS providers, private cloud, and on-prem systems. This creates blind spots where policies are inconsistent, telemetry is fragmented, and incident response becomes slow. Cloud computing security must be designed to work across environments, not just within a single provider.
Cybersecurity mesh architecture (CSMA): A modular approach to cross-cloud security
CSMA is emerging as a practical model for multi-cloud and hybrid environments. Rather than forcing a single monolithic platform, CSMA enables modular security capabilities that integrate across cloud providers. This improves interoperability, correlation, and policy consistency, especially when workloads and data move across environments.
Compliance, governance, and ROI: From audits to continuous assurance
Cloud security must meet regulatory and industry requirements, not just internal standards. The trend is moving from point-in-time audits to continuous compliance monitoring, where controls are enforced automatically and evidence is collected continuously. For CXOs, the ROI of cloud security is ultimately measured by blast radius reduction: limiting the business impact of incidents, protecting customer trust, and avoiding major regulatory penalties.
Cloud security frameworks: Structuring governance at scale
To standardize and validate these controls, mature programs align with established frameworks such as NIST CSF, ISO/IEC 27001 and 27017, and the CSA Cloud Controls Matrix. These frameworks provide structured risk management, consistent control mapping across multi-cloud environments, and defensible compliance positioning—especially critical in regulated industries like healthcare and banking.
Enforcing cloud security controls
To translate these pillars into operational reality, enterprises rely on layered security controls. Essentially, cloud security controls are technical, administrative, and operational safeguards used to deter, prevent, detect, and remediate risks across cloud environments.
Deterrent controls discourage misuse through strong governance, audit visibility, and clearly enforced policies.
Preventive controls block threats before they materialize through least-privilege access, encryption, MFA, and secure configuration guardrails.
Detective controls identify anomalies and misconfigurations using continuous monitoring, CSPM, and behavioral analytics.
Corrective controls contain and remediate incidents through automated response, isolation, patching, and credential rotation.
Together, these controls ensure cloud security is not just designed well but enforced consistently across environments.
Potential challenges enterprises face with cloud computing security
Even with the right framework, execution is where most organizations struggle. Common challenges include:
Blurred accountability in managed and serverless services, where it is unclear what the provider covers versus what the customer must secure
Identity sprawl, especially across service accounts, automation tools, and AI agents
Misconfiguration drift, where secure baselines degrade over time due to rapid changes
Fragmented multi-cloud visibility, leading to inconsistent controls and slow incident response
Compliance complexity, especially when data crosses regions, providers, or regulatory boundaries
Tool overload without integration, where security teams have dashboards but no unified operational control
The cloud security maturity model (CSMM)
Most enterprises already have cloud security measures in place. But how mature, integrated, and automated are they really?
Maturity for cloud computing security typically progresses across four levels:
Level 1: Reactive
Security is tool-driven and incident-based. Controls exist but are inconsistent, siloed, and heavily manual.Level 2: Managed
Policies are defined and standardized across environments. Monitoring is continuous, but remediation is still partially manual.Level 3: Integrated
Security is embedded into DevOps workflows. Controls are automated, identity-centric, and enforced consistently across multi-cloud environments.Level 4: Adaptive and predictive
Security is intelligence-driven. AI-based detection, automated remediation, continuous compliance, and cross-cloud visibility operate as a unified architecture.
| Maturity level | Where you are | Where you should be |
|---|---|---|
| Level 1: Reactive | Manual reviews, periodic audits, siloed tools, basic IAM policies | Establish centralized visibility, baseline IAM governance, and automated misconfiguration detection |
| Level 2: Managed | Defined policies, CSPM deployed, MFA enabled, some DevSecOps practices | Automate remediation, implement Zero Trust architecture, integrate identity lifecycle controls |
| Level 3: Integrated | Security embedded in CI/CD, automated guardrails, cross-cloud monitoring | Introduce AI-driven threat detection, continuous compliance validation, non-human identity governance |
| Level 4: Adaptive | Real-time detection, automated response, unified telemetry, compliance automation | Continuous optimization, predictive risk modeling, and architecture-level resilience across hybrid environments |
Implementing cloud computing security effectively: Best practices for CXOs
For CXOs, the following actions are what typically separate mature cloud security programs from reactive ones.
Treat identity as a board-level security priority
Invest in identity governance, least privilege enforcement, and lifecycle controls for both human and non-human identities. In most cloud incidents, IAM is either the initial entry point or the escalation path.
Shift from “security reviews” to automated security controls
Security cannot scale through manual processes. Embed security into CI/CD, enforce policies through infrastructure-as-code guardrails, and automate remediation for high-confidence misconfigurations.
Build for multi-cloud consistency, not single-cloud optimization
Even if one hyperscaler is dominant, most enterprises still rely on SaaS, identity providers, and secondary clouds. Standardize security policies and telemetry collection across environments to reduce blind spots.
Operationalize compliance through continuous monitoring
Instead of treating compliance as a periodic audit, integrate continuous compliance checks into cloud operations. This is especially critical in banking, healthcare, and regulated industries where audit failures become business risks.
Invest in resilience and incident readiness, not just prevention
Cloud security must assume failure. CXOs should ensure incident response, forensics readiness, and recovery workflows are tested regularly, especially for identity compromise and data exposure scenarios.
Effective cloud computing security in 2026 depends on building systems that remain secure under constant change. Organizations that succeed will treat cloud security as resilience engineering, anchored in zero trust, identity governance, data sovereignty, DevSecOps, continuous posture management, and cross-cloud visibility. For CXOs, the strategic goal is clear: reduce the blast radius of threats, strengthen compliance readiness, and ensure the cloud remains a growth enabler rather than a hidden risk.