On this page
Ransomware attacks are a hacker favorite, and so is demanding ransom in cryptocurrencies. In fact, security experts have been researching if the increasing popularity of ransomware can be attributed to cryptocurrency and vice versa. According to an HSGAC report, the use of cryptocurrency has further enabled ransomware attacks, and attackers are increasingly targeting hospitals, schools, government agencies, and other critical infrastructure.
What is ransomware?
A ransomware attack is a cyberattack in which threat actors deploy malware to encrypt the data of the victim organization, and demand a ransom in exchange for decrypting that data. Attackers do this by exploiting vulnerabilities in the organization's network to gain entry. They then elevate privileges and move laterally until they gain access to an account with high privileges to carry out their attack. To increase their chances of being paid, attackers may design the ransomware to hunt for and destroy backups. Since these attacks involve the use of encryption algorithms, this malware is also called crypto ransomware. Wannacry, Conti, and BlackCat are few popular examples of crypto ransomware. Some attackers take it a notch further and perform cryptojacking using the victim's device (illegal mining of cryptocurrencies) after encrypting their data.
What is cryptocurrency?
A cryptocurrency is a digital currency created for use over the internet. It's built based on blockchain technology and encrypted using cryptography. The first cryptocurrency, Bitcoin, was created in 2009. However, tens of thousands of cryptocurrencies, such as Monero, Ethereum, and Tether, exist.
What is blockchain?
To understand blockchain, you should first know what a block is.
A block refers to a storage unit that stores and encrypts cryptocurrency transaction records. Each block contains details regarding the sender, receiver, and the number of transacted coins. Blocks also contain two cryptographic hashes: one indicates the block's own hash, and the other is the hash of the previous block.
Blockchain refers to a set of unique blocks that are cryptographically linked to one another. The blocks in a blockchain are stacked on top of one another, with the first (genesis) block at the bottom of the vertical stack. Blockchains facilitate the use of a decentralized and peer-to-peer network to secure and store cryptocurrency transactions. These transactions are digitally timestamped to prevent backdating and double-spending.
Why do attackers demand ransom in digital currency?
Attackers prefer receiving cryptocurrency as the ransom payment for the following reasons:
- It is decentralized: No middlemen are involved in transactions with cryptocurrency. As there is no central authority or third-party involvement, anyone (including the attacker and victim) can join or participate in the public blockchain network and perform transactions without the gateway of a bank.
- It is lucrative: As of April 2026, cryptocurrencies such as Bitcoin and Tether Gold are valued at over $75,000 and $4,500 each. With the advent of the Ransomware as a Service model, even amateurs can carry out attacks successfully and easily rake in the profits from their ransomware Bitcoin payments. Figure 1 depicts the market worth of a few cryptocurrencies.
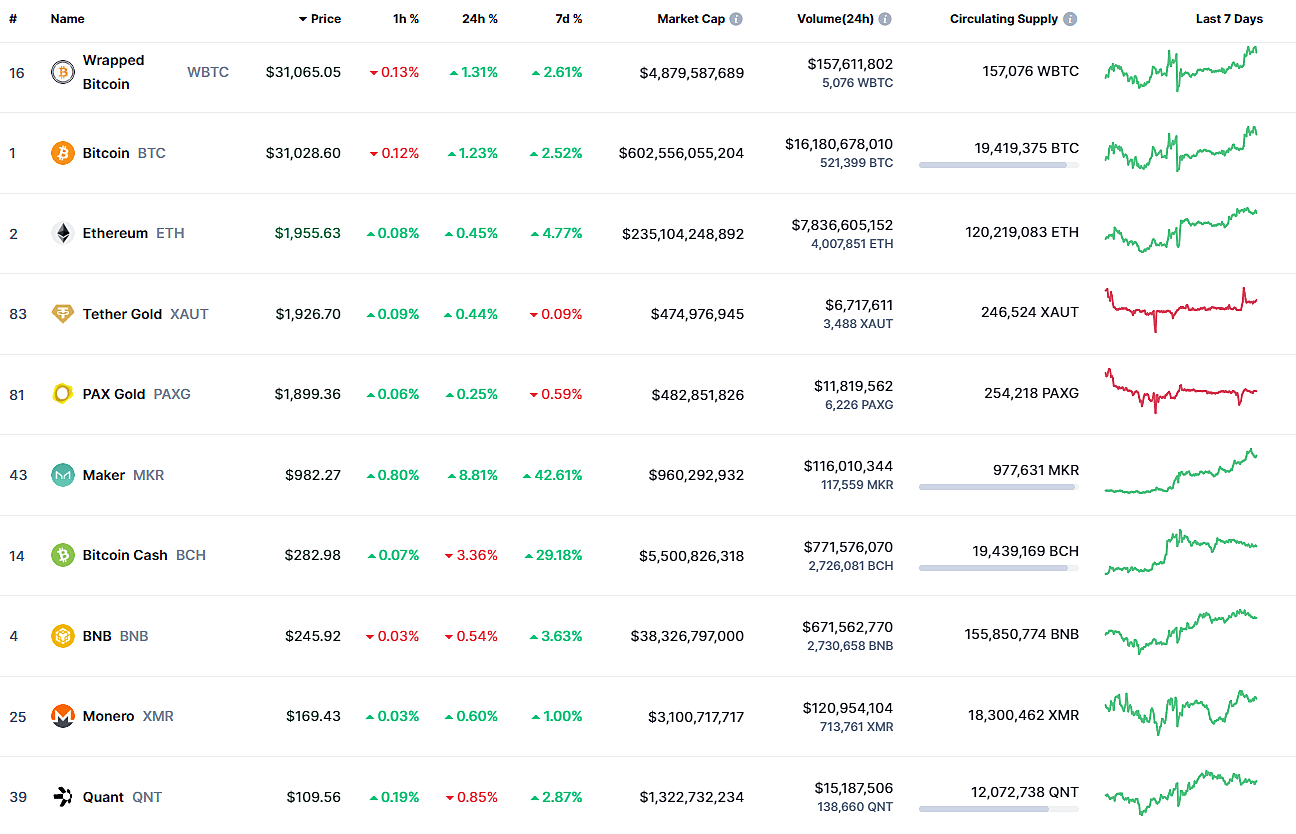
Figure 1: The market worth of a few cryptocurrencies as of Apr. 30, 2026.
- High access and reach: With cryptocurrency exchanges going public and new, affordable cryptocurrencies being launched every other day, their access and reach have increased exponentially. Merchants are starting to accept payments in the form of cryptocurrency, which makes it easier for attackers to demand their victims purchase cryptocurrency for ransom payment, and to quickly dispose of their stolen funds.
- Lack of standard legal jurisdiction across countries: Essentially, cryptocurrency transactions are "borderless." This means that the attacker could be in one country and the victim in another, and it would have no impact on the transaction speed, efficiency, or limit. Moreover, since there is no central authority or global compliance standards for these transactions, and money moves between countries, attackers usually escape the brunt of legal repercussions.
- Difficult to detect: The irony of cryptocurrency transactions is that while the records are all publicly available on the cryptographic ledger of blockchain, the identity of the individuals involved is anonymous. This is because these transactions don't necessarily need Know Your Customer ( KYC ). Moreover, a person can have multiple wallets, each with a different wallet address. Attackers also obfuscate funds to evade detection. This makes tracing the transactions difficult. But, difficult doesn't mean impossible, as evidenced by the $2.3 million worth of bitcoin recovered from Colonial’s ransom payment (roughly $4.4 million worth of bitcoin) by the FBI with the help of a blockchain analytics company, Chainalysis.
To better understand why tracking the transactions is difficult, let's take a look at how the ransom payment process works.
How does the ransom payment process work?
When it comes to paying the ransom, the victim can do it by themselves, or they can engage an incident response vendor (a forensic investigator or negotiation firm) to purchase cryptocurrency. The cryptocurrency now available in the victim's crypto wallet is then transferred to the wallet address mentioned in the ransom note. Usually, the address mentioned by the attacker would not have been previously used, and hence can't be tied back to their previous activities. Cybercriminals also tend to create and use unhosted wallets where the transactions are not monitored by cryptocurrency exchanges. Moreover, to further impede forensic investigations, attackers may also share different wallet addresses for different ransom notes, as was the case in the ESXiArgs ransomware attack.
Once the funds reach the wallet mentioned in the ransom note, attackers employ additional measures to mask the trail of stolen funds and protect their identity. These tactics are as follows:
- Using cryptocurrency mixing services: Also called "mixers" or "tumblers," these services enable ransomware actors to obscure the stolen funds by mixing them with cryptocurrency obtained from legitimate transactions. Essentially, a group of people pool their cryptocurrency, such as Bitcoin, together, with each of them taking back bitcoins of equal value but now with a different source thanks to the centralized mixing service. This adds another layer of complexity while trying to identify the true source of the transaction on the blockchain. Figure 2 shows an example of attackers using mixing services to muddy the cryptocurrency trail.
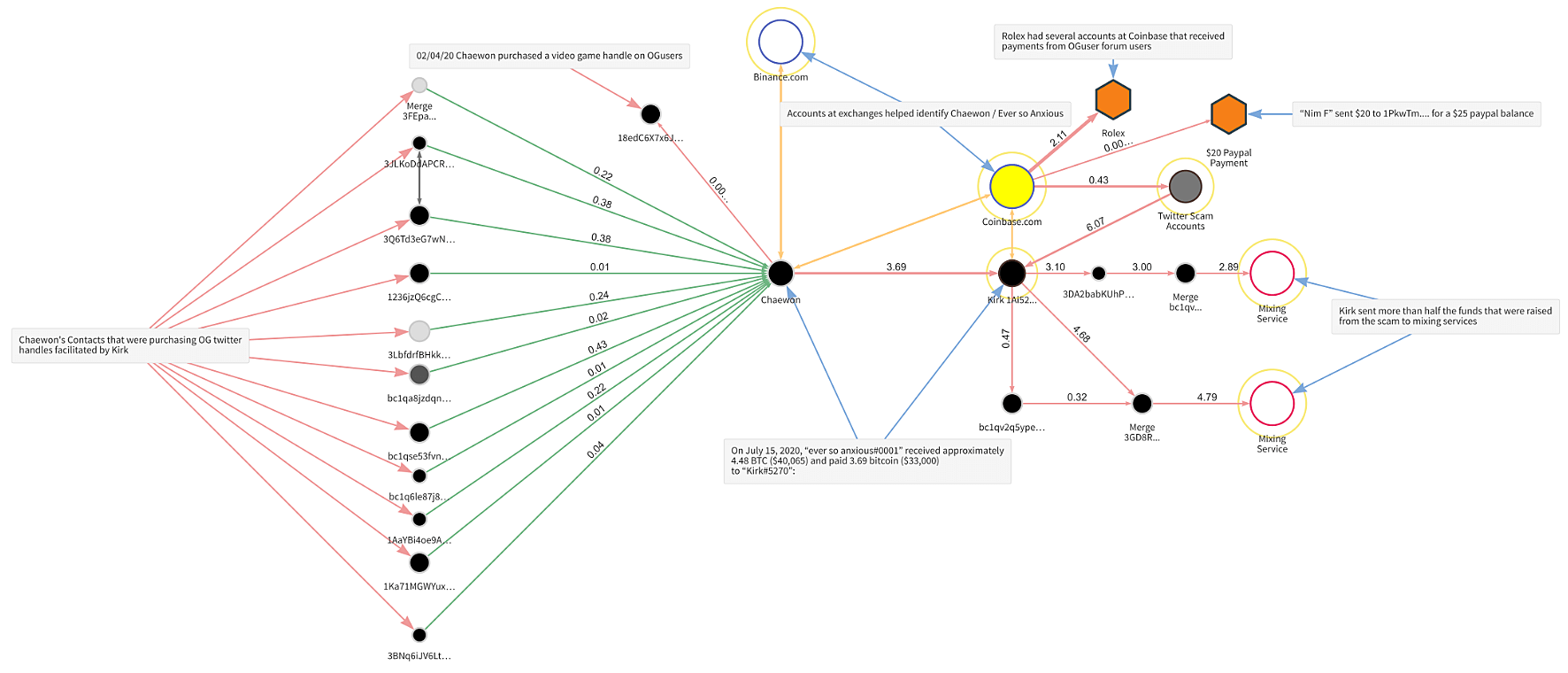
Figure 2: Chainalysis showing the transactions of the Twitter hackers scam in 2020.
- Using the chainhopping method: Here, attackers exchange funds in one cryptocurrency (for example, Bitcoin) for another (e.g., Monero). Privacy coins like Monero were created to support anonymous transactions and protect user identity. So, if such an exchange occurs, it can halt, or at the very least, pose a serious challenge to forensic investigations. That's why attackers sometimes demand ransom in Monero instead of Bitcoin, even though the latter is valued higher. For example, the FOG ransomware redirected its victims to a Monero wallet as per a threat report from April 2025.
- Using stolen accounts: Attackers either employ money-mule providers to set up wallets or use stolen credentials of legitimate users to avoid getting caught.
Figure 3 depicts the ransom payment pathway and potential intervention points as illustrated by the Ransomware Task Force.
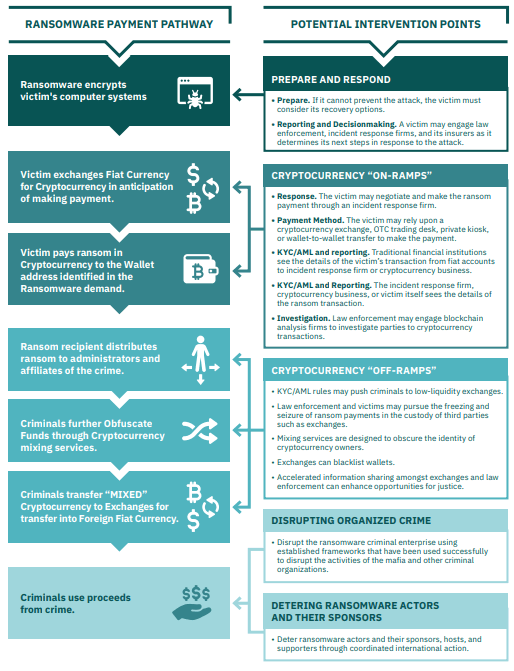
Figure 3: Ransom payment pathway and potential intervention points.
Ransom: To pay or not pay?
This is the million dollar question, and the answer depends on the following factors:
- How good the organization's data backup solution is
- Its cyber insurance plan and coverage
- The cost of ransomware downtime
- Fear of data exposure
- Legal considerations of paying ransom
Security experts and law enforcement agencies usually advise against making ransom payments. This is because they fear the stolen funds will be used for more nefarious purposes, and might also encourage attackers to strike more often. A recent study reveals that 78% of organizations that paid ransom were targeted again, and 63% of those experienced a higher ransom demand. That's why security advisories and governments advise against paying ransom and encourage organizations to focus on increasing their cyberdefense and resilience against ransomware.
How can a SIEM solution help defend against ransomware?
A unified SIEM solution with integrated DLP and CASB capabilities provides:
- Real-time security monitoring
- Automated incident response
- Exemplary log forensics
- Complete cloud visibility
- User and entity behavior analytics
With the insights gained from a SIEM solution's threat intelligence, correlation engine, and anomaly detection capabilities, organizations can prevent and defend against various attacks including ransomware.
Related solutions
ManageEngine AD360 is a unified IAM solution that provides SSO, adaptive MFA, UBA-driven analytics, and RBAC. Manage employees' digital identities and implement the principles of least privilege with AD360.
To learn more,
Sign up for a personalized demoManageEngine Log360 is a unified SIEM solution with UEBA, DLP, CASB, and dark web monitoring capabilities. Detect compromised credentials, reduce breach impact, and lower compliance risk exposure with Log360.
To learn more,
Sign up for a personalized demo