Direct Inward Dialing: +1 408 916 9892
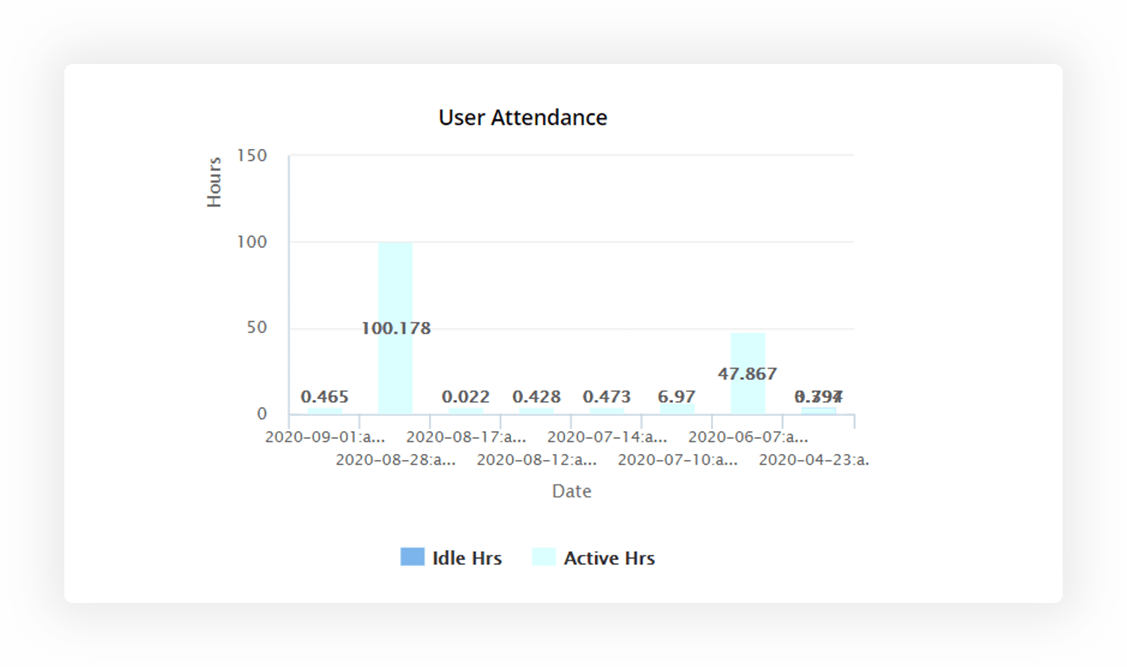
Monitor both your remote and on-site employees' work hours to determine billable hours accurately.
Track and record user actions across Active Directory (AD), file servers, NAS devices, and more.
Use UBA to quickly spot malicious insiders, privilege misuse or escalation, and other security issues.
Gain instant insights into how effective your workforce really is by clocking their work hours regularly, analyzing their time spent inactive, tracking their login and logout patterns, assessing the number of employees working from home, and more.
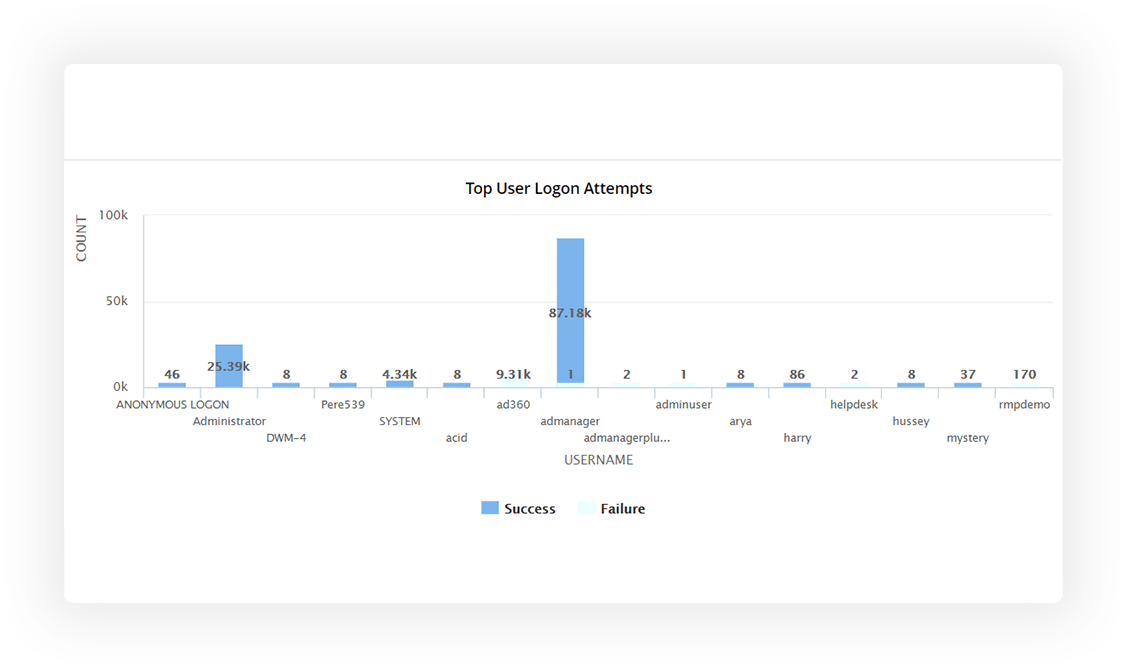
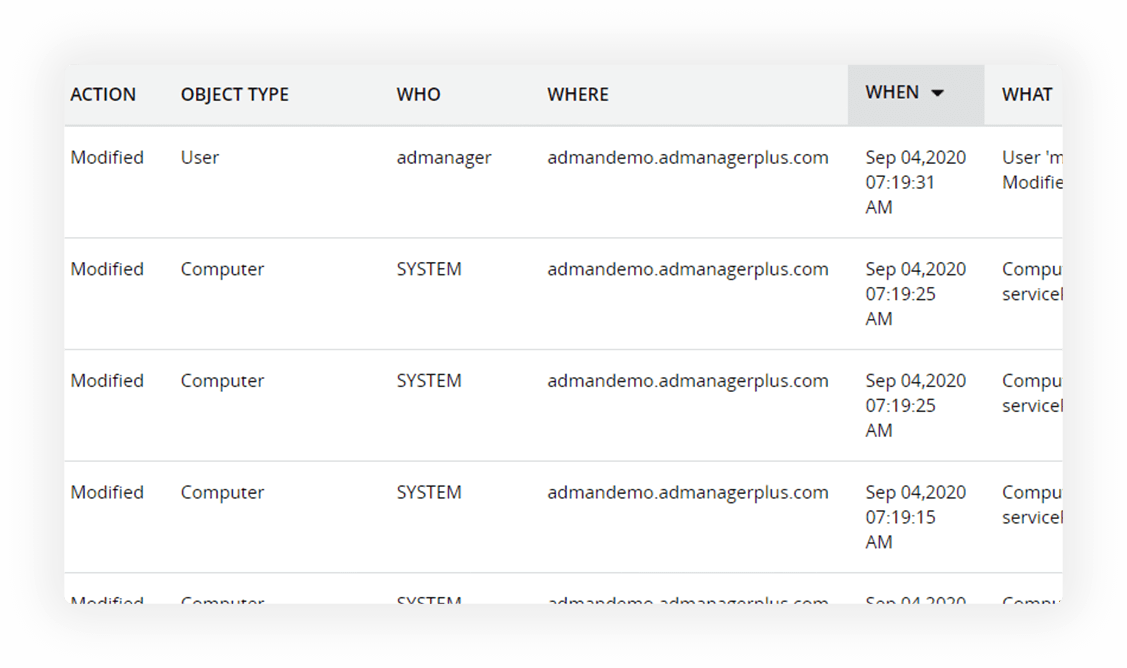
Track user logon and logoff actions with details on who logged in, when, and where.
Identify the actual time employees spent working by excluding their machine idle time.
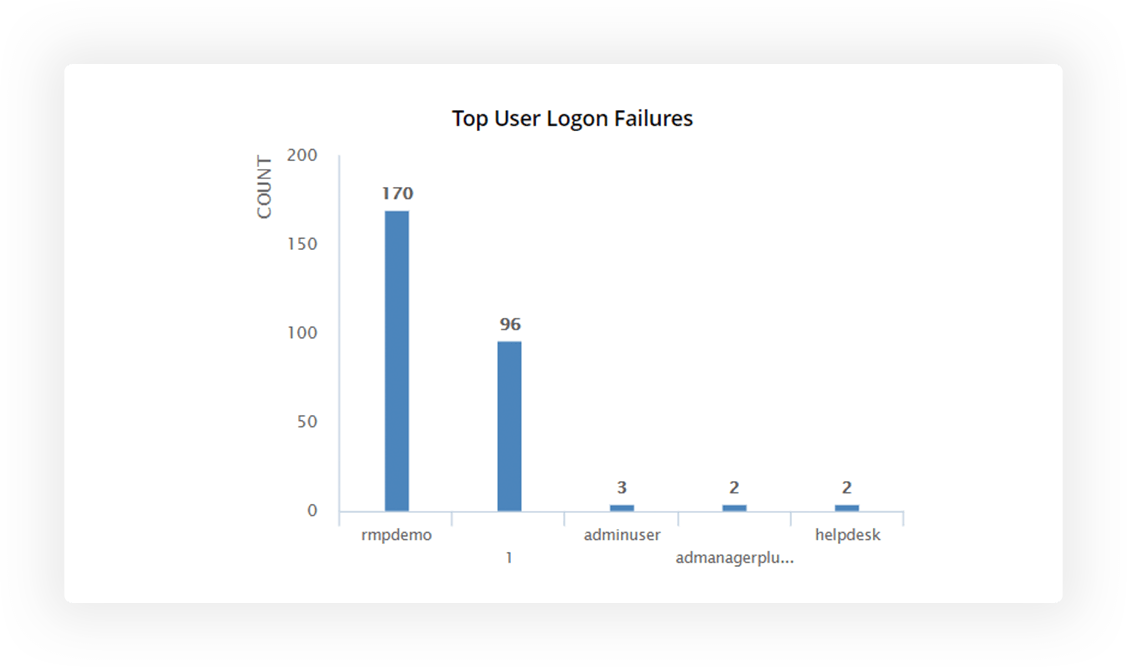
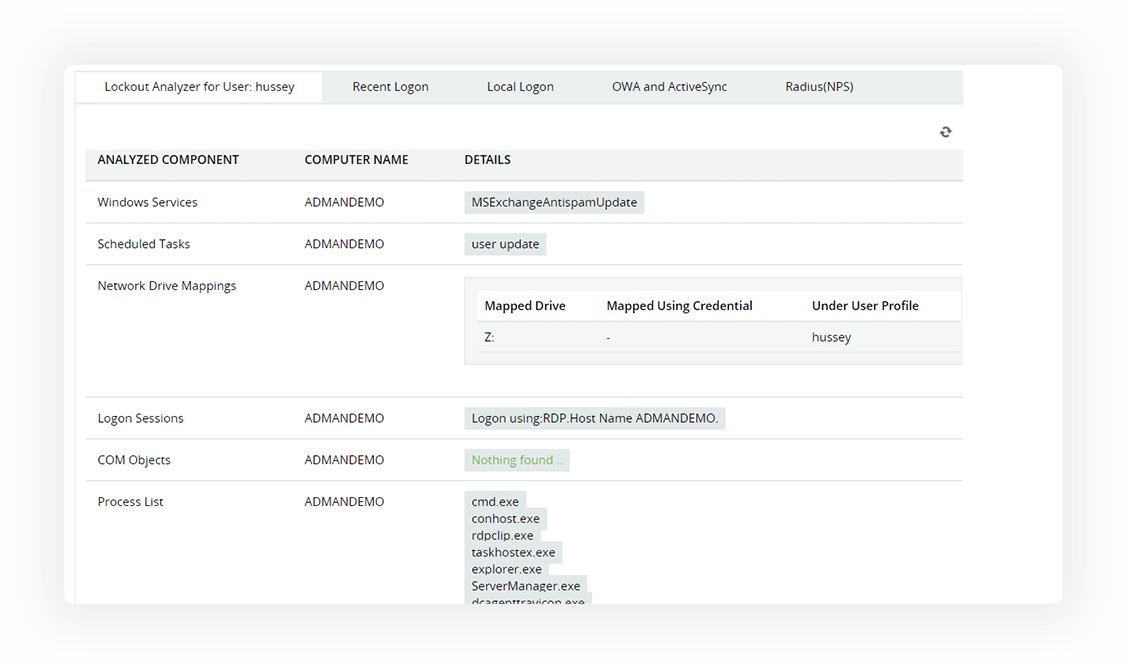
Review users with a high number of login failures with in-depth details on the cause.
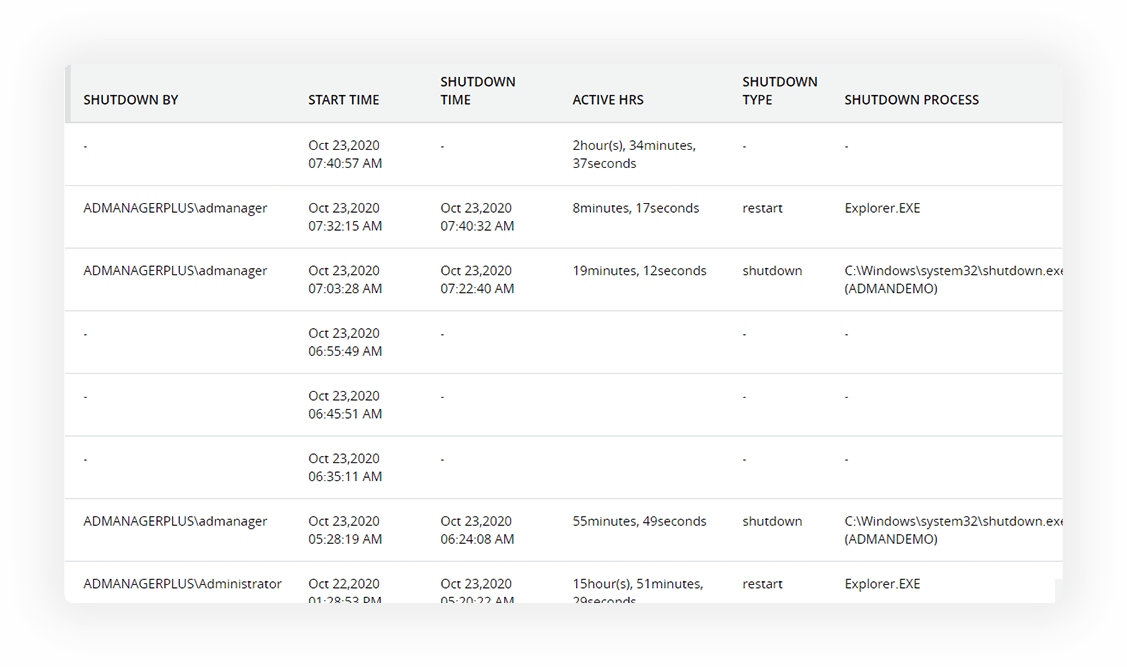
Monitor workstation activities including startup and shut down, remote session connections and disconnections, etc.
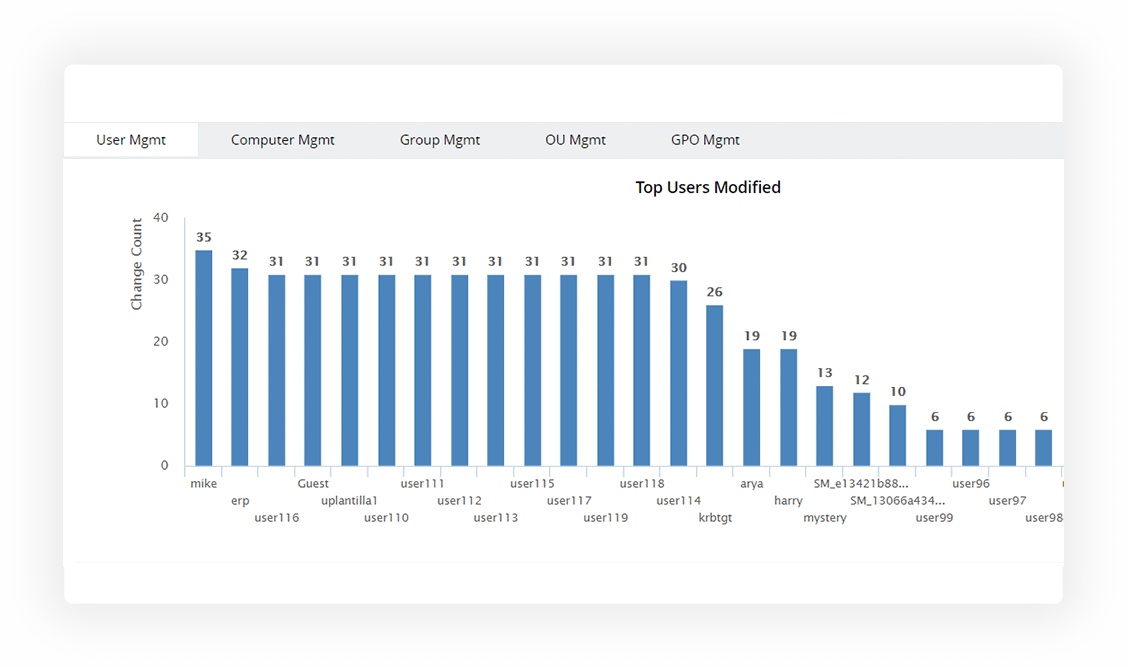
Gain in-depth visibility on changes by monitoring employees' activities across Active Directory (AD), Windows Server, workstations, Windows file servers, EMC/NetApp/Synology storage devices, and Azure AD.
Track all changes made to AD objects and their attributes, GPOs, and more with details on who initiated the change, when, and where.
Scrutinize activities initiated by admins and other high-privilege users selectively.
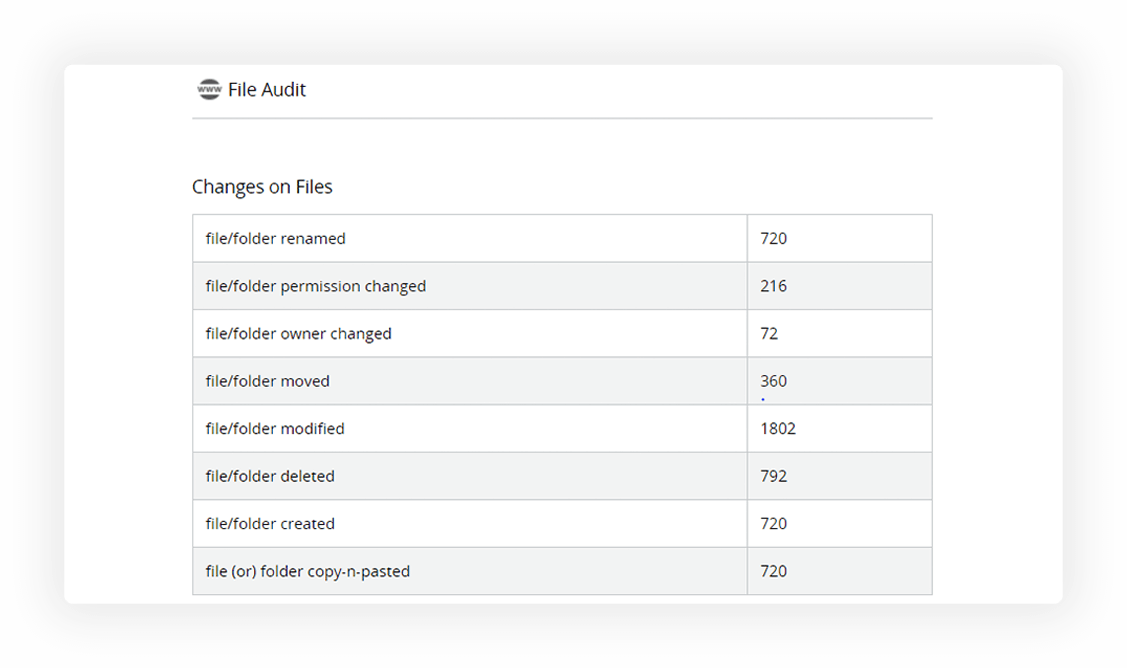
Audit both successful and failed file accesses and modifications by users.
Discover the reason your employees get repeatedly locked out of their accounts.
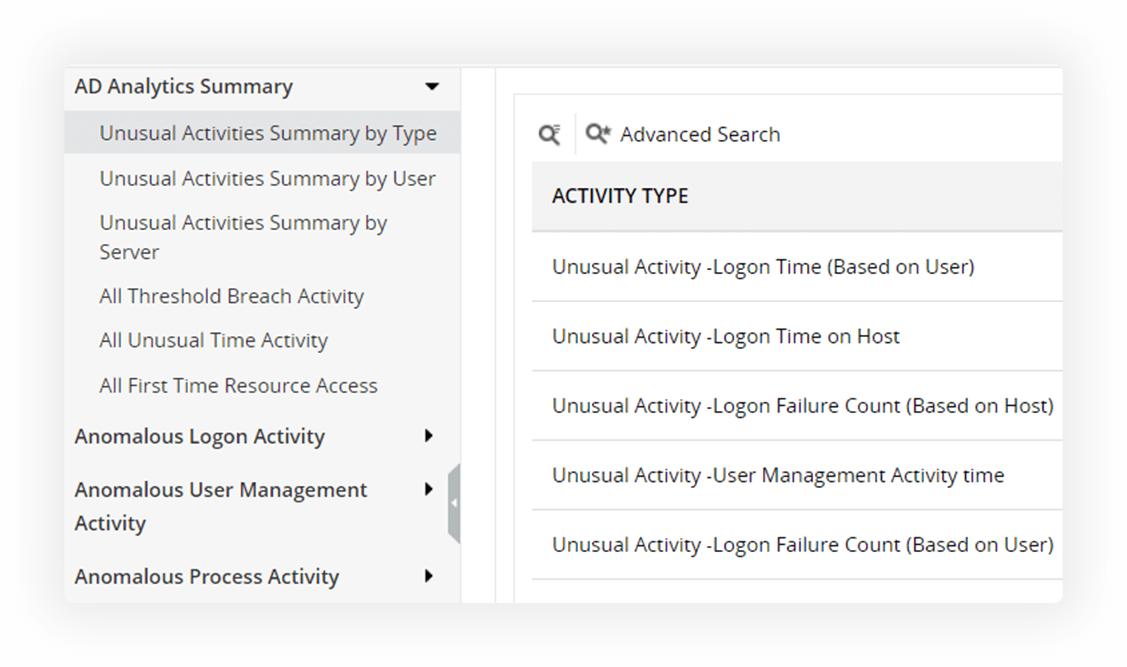
Leverage user behavior analytics (UBA) to map user-specific baselines for file, logon, and user management, and process activities. Flag any anomalies to detect insider threats, privilege abuse, brute force attacks, and much more.
Spot suspicious user activities such as sudden spikes in failed logins, file accesses, and more.
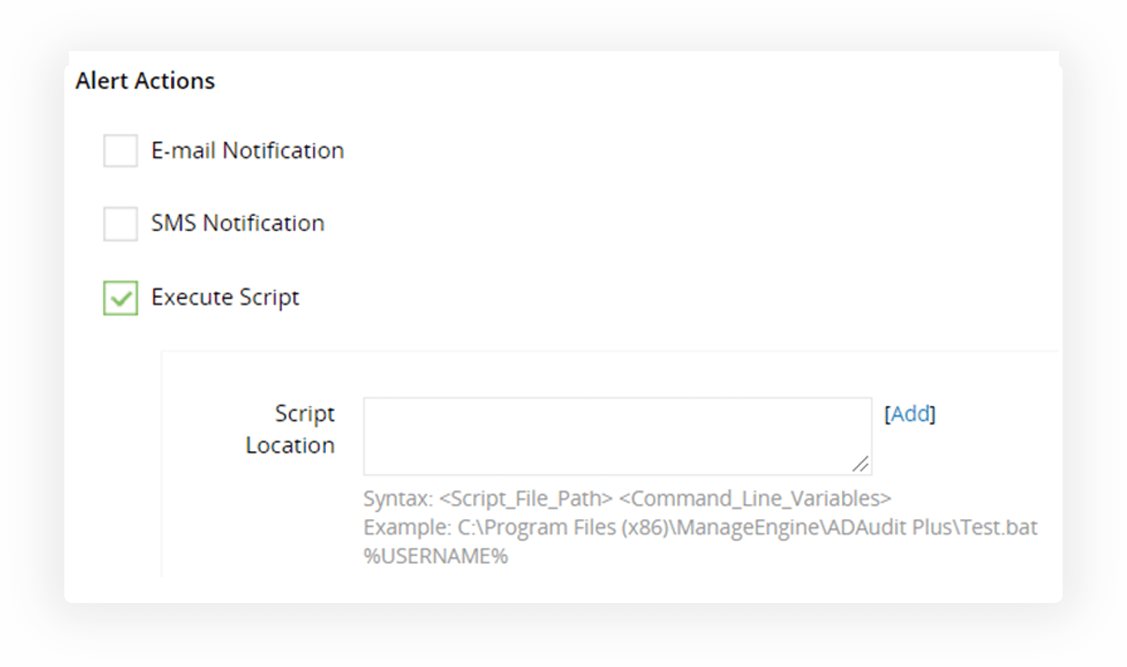
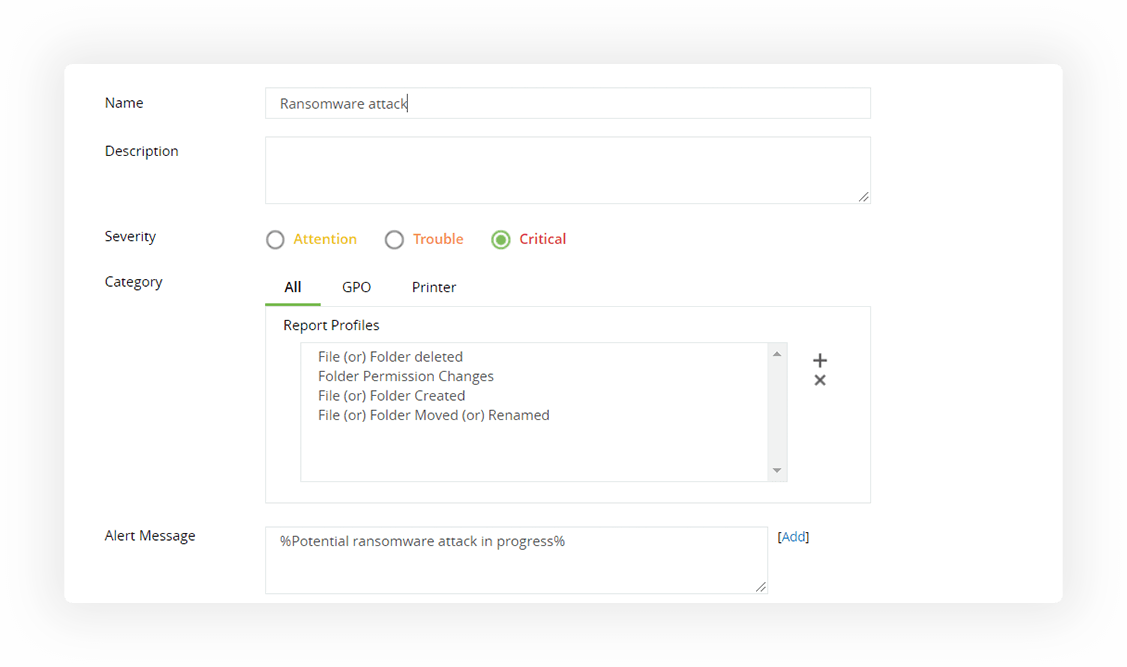
Detect and quarantine potential ransomware attacks instantly by shutting down the infected system.
Automate instant scripted responses to contain the damage inflicted.
Our Active Directory auditing software offers extensive out-of-the-box compliance reports that helps.
Audit file accesses and modifications across EMC, EMC Isilon, NetApp, and Synology devices.
Perform change monitoring on all activities across the Windows server environment in real-time.