Significance of advanced audit policies.
The purpose of security auditing is to ensure that events are logged whenever an activity occurs. However, when every activity is audited, event logs become flooded with irrelevant information that makes it difficult for network administrators to separate critical events from insignificant ones. Advanced audit policy settings help administrators exercise granular control over which activities get recorded in the logs, helping cut down on event noise.
As an example, instead of turning on the DS Access audit policy category to troubleshoot a replication problem—which would generate around eight events every time this activity occurs—an administrator could turn on the advanced audit policy subcategory for Directory Service Replication, which would only generate one event instead of eight.
Groundwork for configuring an advanced audit policy.
- Identify the most important activities in your network that need to be tracked. Check out the 8 most critical event IDs as a starting point.
- Identify the security audit settings that can be used to track these activities.
- Assess the potential advantages and disadvantages (implications on event log size, for example) of each of these setting.
- Configure and manage security audit settings (in addition to audit policies and advanced audit policies, you must also configure System Access Control Lists (SACLs) to enable auditing on directory objects and files/folders).
For information on how to configure SACLs, visit our help document.
Steps to configure any advanced audit policy setting.
Setting an advanced audit policy requires administrator-level account permissions or the appropriate delegated permissions.
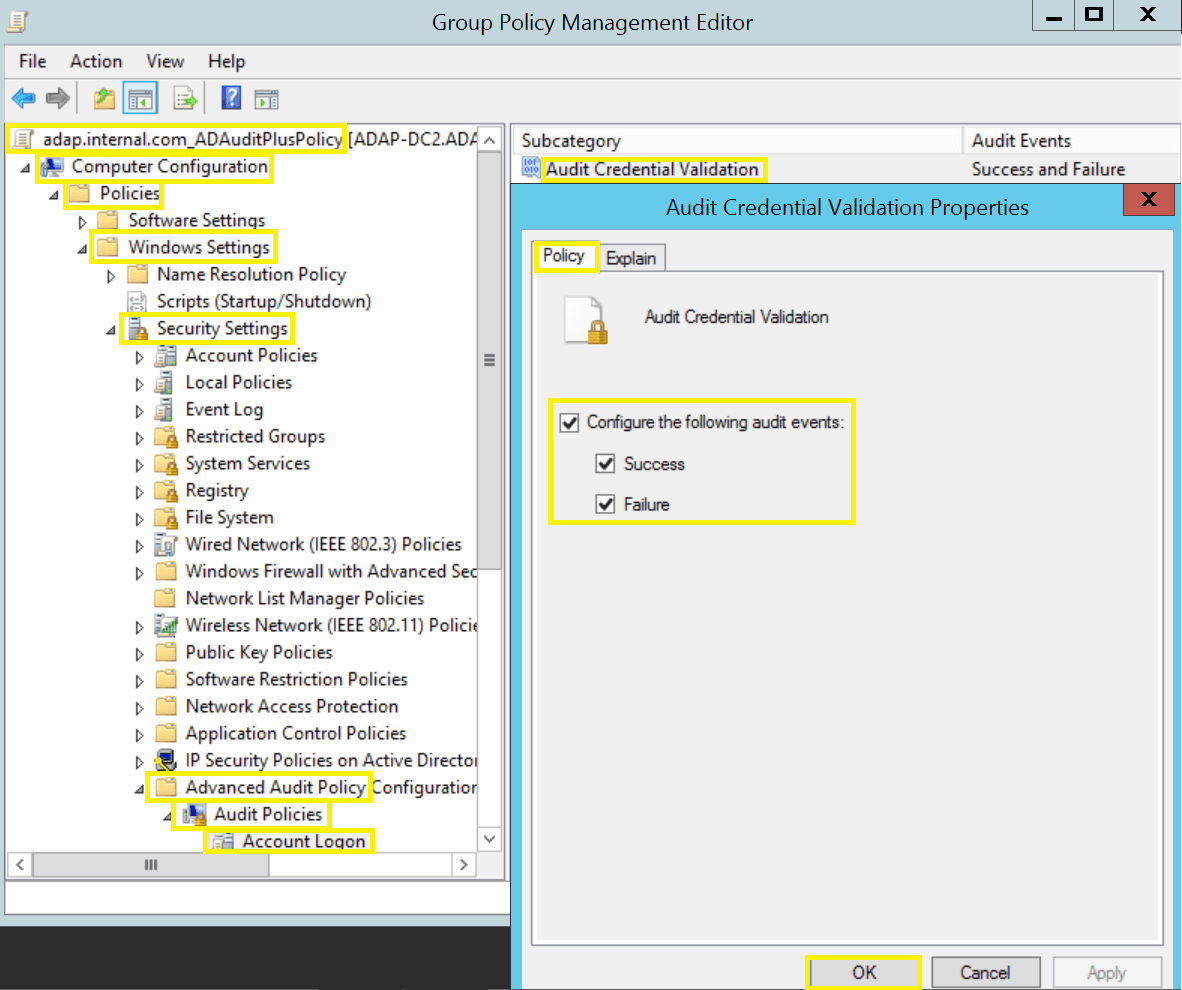
- From the Domain Controller, click Start, point to Administrative Tools, and then Group Policy Management.
- From the console tree, click the name of your forest > Domains > your domain, then right-click on the relevant Default Domain or Domain Controllers Policy (or create your own policy), and then click Edit.
- Under Computer Configuration, click Policies > Windows Settings > Security Settings > Advanced Audit Policy Configuration > Audit Policy, then double-click on the relevant policy setting.
- In the right pane, right-click on the relevant Subcategory, and then click Properties.
- Select Success, Failure, or both from the audit events checkbox and then click OK.
The ten advanced audit policy categories in brief.
- Account Logon (four subcategories): Monitors attempts to authenticate account data on a domain controller or on a local Security Accounts Manager (SAM).
- Account Management (six subcategories): Monitors changes to user and computer accounts and groups.
- Detailed Tracking (five subcategories): Monitors the activities of individual applications and users on a computer, and shows how that computer is being used.
- DS Access (four subcategories): Provides a detailed audit trail of attempts to access and modify objects in Active Directory Domain Services.
- Logon/Logoff (11 subcategories): Tracks attempts to log on to a computer interactively or over a network.
- Object Access (14 subcategories): Tracks attempts to access specific objects or types of objects on a network or computer.
- Policy Change (six subcategories): Tracks changes to important security policies on a local system or network.
- Privilege Use (three subcategories): Tracks the use of certain permissions on one or more systems.
- System (five subcategories): Tracks system-level changes to a computer that are not included in other categories and that have potential security implications.
- Global Object Access Auditing (two subcategories): Allows administrators to define computer SACLs per object type for the file system or for the registry.
Choosing to log successes, failures, or both.
You should assess the advantages and disadvantages before choosing to log successes, failures, or both. For example, for files that are frequently accessed by legitimate users, successful access attempts will quickly fill the event log with benign events. Since failed login events can indicate unauthorized access attempts, those are the events that should be audited in this scenario. On the other hand, for files with sensitive information, every access attempt should be logged (both successful and failed), so that you have an audit trail of every user who accessed the file.
Five key points to keep in mind.
- Audit policies are computer policies. This means an advanced audit policy must be applied through GPOs that are applied to OUs containing computers and not user OUs.
- The Default Domain Policy is linked to the domain and affects all users and computers in that domain through group policy inheritance. While the Default Domain Controllers Policy is linked to the Domain Controllers OU and affects only domain controllers. Policy settings that are applied at the OU level override policy settings applied at the domain level.
- When using Advanced Audit Policy settings, be sure to enable Force advanced audit policy settings in order to override audit policy settings. To do so, go to Local Polices > Security Options, and enable Force audit policy subcategory settings.
- Run the Group Policy Results wizard found under the Group Policy Management Console to view a consolidated list of all audit policy settings that will be applied.
- When modifying an existing advanced audit policy, take a backup of the existing GPO so that it can be restored at any time. To take a back up, right-click on the relevant GPO and use the Back Up functionality.