- How to access
- Types of EntraID sign-in logs
- Why monitor
- How ADAudit Plus helps
Similar to how an on-premises Active Directory maintains a record of all user logins, Entra ID (formerly known as Azure AD) stores information about all sign-ins into a tenant, including applications and other resources within your cloud environment.
This helps you identify the typical login behavior of your users and detect anomalies in real time. Entra ID sign-in logs are crucial for performing auditing on authentication activities, a common requirement across major compliances like NIS 2, DORA, and the GDPR, etc.
How do you access Entra ID sign-logs
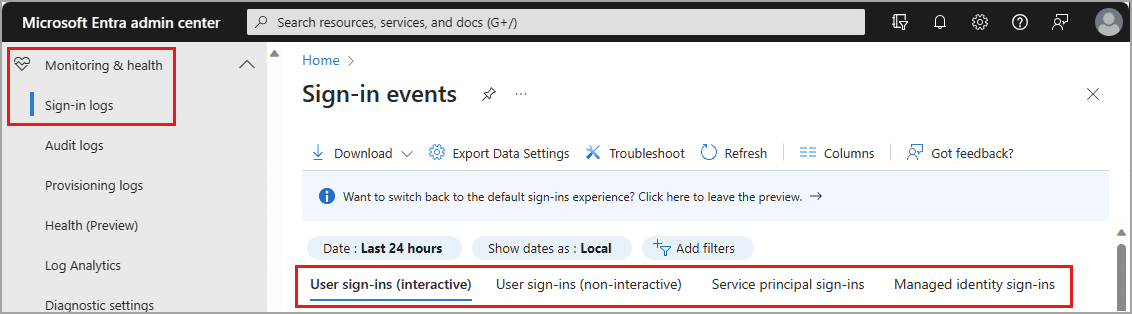
Microsoft Entra Admin Center is a centralized tool to manage applications, services, data, devices, and users within your Entra ID tenant.
To access the sign-in logs from the Microsoft Entra admin center:
- Sign in to the admin center with a role access level of at least Reports Reader.
- Head to Entra ID > Monitoring & Health > Sign-in logs.
Note
Access to sign-in logs is available in all tiers, but retention varies from seven days with an Entra ID Free license to 30 days with an Entra ID P1/P2 license.
These sign-in logs can also be filtered to find events specific to a time, location, or the application used to perform the sign-in.
- Sign in to the admin center with a role access of at least Reports Reader.
- Head to Entra ID > Monitoring & Health > Sign-in logs.
- Choose the Add filters option
- Select a filter option and enter the respective value
- Click Apply to filter out the log(s).
Sign-in logs can also be accessed:
- By forwarding these logs to a SIEM tool, such as ManageEngine Log360 or Microsoft Sentinel, via Azure Event Hubs.
- By querying programmatically using Microsoft Graph API calls.
P1 or higher license is required for Graph API or log export of sign-in logs.
Types of Entra ID sign-in Logs
There are four different sign-in log types:
- Interactive user sign-in logs: They capture all sign-ins where a user directly interacts with an application or a service to authenticate.
Example: A user performing MFA during Entra-ID sign-in.
- Non-interactive sign-in logs: These logs captures the sign-ins where an application or a system utilizes a user's credentials to access resources within Entra ID. In other words, these sign-ins are made on behalf of the user.
Example: A client-application using a user's credential to store a new information database hosted in Azure.
- Service principal sign-in logs: Captures the sign-ins of service principals (application identities) used to access Azure resources authenticated through Entra ID. This sign-in methods requires no human intervention.
Example: An HRMS tool using its credentials to update a user's information available in a database hosted in Azure
- Managed identity sign-in logs: Azure assigns built-in identities to certain native resources. Such identities are called Managed identities and logs associated with them are called the Managed identity sign-in logs.
Example: The Azure Virtual Machines uses its system-assigned identity to access resources within the Entra ID tenant.
Why monitoring sign-in logs is important
Sign-in logs track every attempt performed to access a resource or an application within an Entra ID tenant. Thus, monitoring these logs is crucial for security, compliance and operation health of your Entra ID environment. The sign-in logs can be used to:
- Identify user-behavioral patterns: Sign-in logs helps you analyze and identify typical user behavior patterns.
- Detect attacks and incidents: Monitoring these logs helps you detect attacks such as insider attacks, brute-force attacks, etc.
- Post-incident analysis and troubleshooting: Sign-in logs can be used to identify the reason behind a failed sign-in attempt to resolve them instantly or identify the root cause behind a security breach.
- Compliance auditing: Sign-in logs are crucial for compliance audits such as NIS 2, DORA, the GDPR, etc.
A one-stop solution for all your IT auditing, compliance, and security needs
ADAudit Plus provides capabilities like change auditing, logon monitoring, file tracking, compliance reporting, attack surface analysis, response automation, and backup and recovery for diverse IT systems.
How ADAudit Plus helps in monitoring Entra ID sign-in logs
ManageEngine ADAudit Plus provides a single pane of reporting for all AD changes. It provides real-time, UBA-driven insights to detect suspicious and risky changes. With ADAudit Plus, you gain full visibility into object modifications, logons, account lockouts, permission changes, file activity, and more.
With ADAudit Plus, you can:
- Track all sign-ins, both successful and failed attempts, that take place in your Entra ID tenant with user logon tracking reports.
- Examine the real-time changes made to the users, groups, devices, applications, and more in Entra ID using real-time change monitoring reports.
- Identify risky sign-in activities attempted using parameters such as IP address, geolocation, sign-in pattern etc. using the risk detection reports.
- Track both on-premises and cloud logon activities using the hybrid logon activity report.
- Satisfy the regulatory requirements of the GDPR and HIPAA compliances using the compliance audit reports.
- Identify risk misconfigurations performed across your Entra ID environment and remediate them using Attack Surface Analyzer.
Try all these features and more for free with a 30-day trial. Or hop on a call with our technical experts to learn how ADAudit Plus can help.
Experience
ADAudit Plus for free
With ADAudit Plus, you can:
- Get full visibility into logons
- Monitor employee attendance
- Detect attacks like Kerberoasting
- Generate logon audit trails
- And much more











