Microsoft Entra admin center allows you to manage identities and access policies. You can handle users, groups, devices, app registrations, Conditional Access policies, and sign-in logs for your Microsoft Entra ID tenant.
- Meaning
- Features
- Steps to access
- Navigating the admin center
- Monitoring Entra ID
- FAQ
The Microsoft Entra admin center works as an web-based portal that lets you manage Microsoft Entra ID, which used to be called Azure Active Directory (Azure AD). It has taken over from the old Azure Active Directory blade in the Azure portal and now combines all identity, access, and governance options in one place at entra.microsoft.com.
Organizations using Microsoft 365, Azure, or other Microsoft cloud services rely on Microsoft Entra ID for sign-ins. The admin center is where you control all of that.
What is the Microsoft Entra admin center?
The Microsoft Entra admin center lets administrators like you to manage identity and access. You can use it to set up users, groups, devices, apps, roles, and security policies for a Microsoft Entra ID tenant.
This tool is not the same as the Microsoft 365 admin center at admin.microsoft.com. The Microsoft 365 center focuses on things like subscriptions, billing, Exchange Online, and Teams. Although both tools share user info, they serve different purposes. As of September 2024, license assignments management for Microsoft 365 products is done only through admin.microsoft.com.. The Entra center still handles identity management, Conditional Access and Privileged Identity Management.
Starting October 15, 2024, Microsoft made MFA mandatory to log in to the Entra admin center. Based on Microsoft's announcement, enabling MFA prevents over 99.2% of accounts from being compromised.
What features are available in the Entra admin center?
The table below lists five core functionality areas and the associated licensing tiers.
| Management area | What you can do | License |
|---|---|---|
| Users and groups | You can create accounts, modify, delete, restore, and set up authentication methods. Also work with dynamic group rules. | Free / P1 / P2 |
| Applications | Enable enterprise single sign-on, manage app provisioning and app registrations, and set up OAuth2.0 and OIDC. | Free / P1 / P2 |
| Conditional Access and Identity Protection | Set access policies, monitor risky sign-ins, and view risky user reports. | P1 (CA) / P2 (IP) |
| Roles and PIM | Manage roles, assign them, or activate them when needed (just-in-time) with Privileged Identity Management. | P2 for PIM |
| Monitoring | Check sign-in logs and audit logs, review health dashboards, and view provisioning logs. Note: Retention period for logs is 30 days. | Free / P1 / P2 |
Some key points to mention. To use Conditional Access and single sign-on with over 10 apps, you need Entra ID P1. This comes with Microsoft 365 E3. If you need features like Privileged Identity Management or Identity Protection risk policies, you will need P2, which is part of Microsoft 365 E5. Basic management of users, groups, and apps is included in the free tier.
Steps to access the Microsoft Entra admin center
You must have the Global Reader role or higher to log in. There are three ways to access it.
- Using a direct URL: Open a browser and head to entra.microsoft.com. Sign in there with your org account.
- Through the Azure portal: In the Azure portal, type "Microsoft Entra ID" into the top search bar. Select - Entra ID.
- Inside the Microsoft 365 admin center: Look for Admin centers on the left pane. Click on it then pick the Identity option.
Navigating the admin center
The left pane menu is made of expandable sections for each product. The key sections are:
- Home: See tenant overview, check recent activities, and view security recommendations.
- Identity: Explore users, groups, external identities, and devices in this section.
- Protection: Manage Conditional Access, Identity Protection, and authentication protocols here.
- Governance: Handle entitlement management, access reviews, and lifecycle workflows.
- Applications: To work on enterprise apps and app registrations.
You can use the search bar at the top to look up settings, features, or Microsoft guides instead of browsing through the entire menu. The tenant switcher on the upper-right, lets you move between tenants without needing to log out.
Monitoring Entra ID activity with ADAudit Plus
The Entra admin center keeps sign-in and audit logs for a maximum of 30 days, with seven days available on the free plan. This limit cannot be changed. To access data older than 30 days for audits or security investigations, you need to rely on external tools. ManageEngine ADAudit Plus connects directly to your Entra ID tenant. It gathers data on sign-ins, directory updates, role changes, device activities, application consents records, MFA activity, and Conditional Access policy updates. This tool keeps that data even after Microsoft's retention period ends.
ADAudit Plus also correlates events that are stored in the Entra admin center. It ties together actions like failed sign-ins, password resets, and role changes made by the same user in a clear single view. With ADAudit Plus you can view the following:
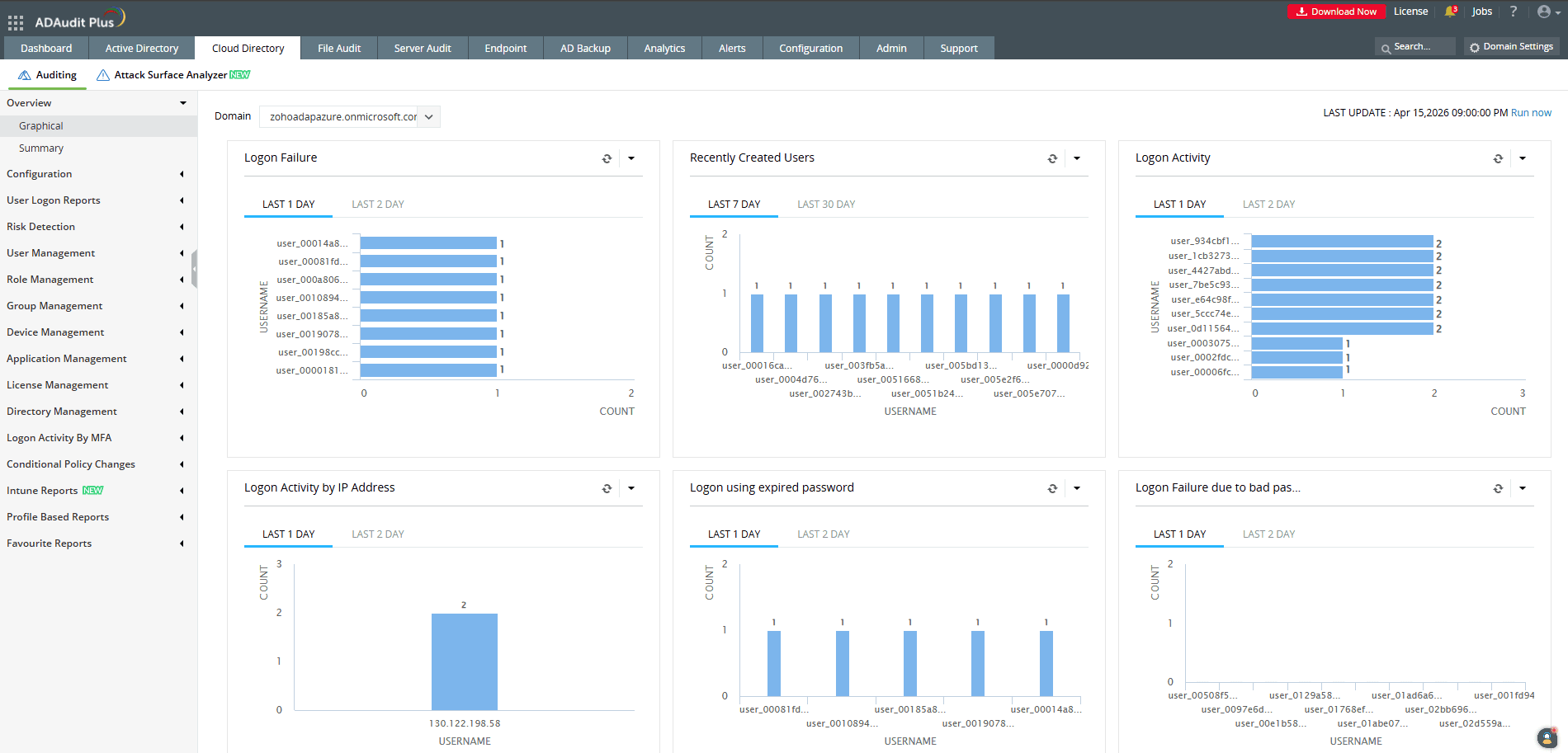
- Sign-in monitoring records logon details like geo-location, device info, MFA status, and Conditional Access results. It also includes a Risk Detection report highlighting things like impossible travel, anonymous IP addresses, password spray attempts, and leaked credentials.
- Legacy login methods using SMTP, IMAP, or POP3, which bypass MFA, are listed in a separate section.
- Changes to users, roles, or groups such as creating or deleting accounts, resetting passwords, or updating role assignments, are logged.
- Activity around apps and permissions, like OAuth2.0 grants or admin approval events, is logged to limit risks tied to OAuth phishing.
- Modifications to Conditional Access policies, including adding, modifying, or removing them, are tracked. Along with, MFA method and enforcement status.
- The tool includes compliance reports that align with standards like SOX, HIPAA, PCI-DSS, GDPR, and ISO 27001. It allows users to export data from both on-premises Active Directory and Entra ID in a single export.
Expand Entra ID monitoring past 30 days
ADAudit Plus connects to your Entra ID tenant to offer detailed reports on sign-ins, roles, policies, and devices. It ensures long-term data storage to align with compliance standards.
Frequently asked questions
The Entra admin center focuses on managing identity-related tasks like Conditional Access, PIM, app registrations, and device management. On the other hand, the Microsoft 365 admin center at admin.microsoft.com handles licensing, billing, Exchange Online, SharePoint, and Teams. As of September 2024, all license assignments are managed at admin.microsoft.com.
Azure works as a cloud platform that handles virtual machines, networking, and storage. On the other hand, Microsoft Entra manages identity, deciding who can log in and what they can access within Azure and Microsoft 365.
Yes. Starting October 15, 2024, Microsoft made MFA a must-have to access the Entra admin center. There is no way to skip this. Passkeys and certificate-based authentication satisfies it.
The Entra admin center keeps logs for just 30 days. ADAudit Plus keeps Entra ID events saved past that time limit and combines things like sign-in activity, audit logs, device events, and role updates into one dashboard. It also comes with ready-made compliance reports to meet SOX, HIPAA, PCI-DSS, GDPR, and ISO 27001 standards. These reports include data from both Entra ID and on-premises Active Directory in a single export.
Experience
ADAudit Plus for free
With ADAudit Plus, you can:
- Monitor Entra ID sign-ins
- Retain logs beyond 30 days
- Track role and policy changes
- Generate ready-made compliance reports
- And much more











