A configuration policy changes device settings by delivering and enforcing a value on the device. A compliance policy checks whether device settings meet your requirements by evaluating and reporting compliant or noncompliant. Configuration policies configure; compliance policies check. You need both: one enforces the state, the other detects when the state has drifted.
- Difference between Intune compliance & configuration policy
- How conflicts work
- Security risks
- Monitoring with ADAudit Plus
- FAQ
Compliance policies and configuration policies both appear in Intune's device management interface, both can involve passwords and encryption, and both target users or device groups. They do fundamentally different things. One configures; the other checks. Every other difference follows from that.
What each policy type does
Configuration policies
A configuration policy delivers a setting to a device and enforces it. When the device checks in, it applies the specified value, for example enabling BitLocker, blocking the camera, deploying a VPN profile, or setting the Edge homepage. The device holds that state for as long as the policy is assigned. It does not report a pass or fail. It just sets the value.
Compliance policies
A compliance policy evaluates a device against a set of rules and returns a result: compliant or noncompliant. It does not change any settings. If a device fails a rule (wrong OS version, encryption off, firewall missing), Intune marks it noncompliant and can trigger actions, from an email notification to blocking access via Conditional Access. Without Conditional Access, a compliance policy reports but does not block.
Side-by-side comparison
| Configuration policies | Compliance policies | |
|---|---|---|
| What it does | Delivers and enforces a setting | Evaluates whether a setting meets your requirement |
| Changes device settings? | Yes: applies the value directly | No: reads the value, does not change it |
| Result | Setting is applied | Device is marked compliant or noncompliant |
| Blocks access? | No | Yes: when paired with Conditional Access |
| Conflict behaviour | Conflict = neither setting applies | Conflict = stricter value wins |
| Linked to Conditional Access? | No | Yes: compliance status feeds Conditional Access |
| Typical examples | Enforce BitLocker, deploy VPN, block camera | Require BitLocker on, require minimum OS version |
How conflicts work
Configuration policies: nothing applies
If two configuration policies target the same setting on the same device with different values, Intune declares a conflict and applies neither. The device keeps whatever value it had before. All other non-conflicting settings in both policies continue to apply. Conflicts show up under Devices > Monitor > Assignment failures.
Compliance policies: stricter value wins
If two compliance policies cover the same setting with different thresholds, Intune uses the stricter value. One policy requires Windows 11 22H1, another requires 22H2, and the device is held to 22H2. Multiple overlapping compliance policies effectively merge into the strictest combined ruleset.
Which to use when
| Scenario | Use this |
|---|---|
| Enforce a setting on all devices regardless of what the user has set | Configuration policy |
| Block noncompliant devices from Microsoft 365 or Azure | Compliance policy + Conditional Access |
| Report which devices are missing a security setting without changing anything | Compliance policy |
| Deploy a VPN profile, Wi-Fi connection, or email account | Configuration policy: compliance policies cannot push connectivity settings |
| Respond automatically when a device drifts out of compliance | Compliance policy with noncompliance actions |
| Migrate from on-premises Group Policy | Configuration policy: GPO settings map via ADMX import or Settings Catalog |
Security risks when policy changes go unmonitored
Both policy types are targets for unauthorized modification. Changing either affects device security posture across every assigned group, and the Intune admin center generates no real-time alert when either happens.
Configuration policy weakened silently
An admin who removes an endpoint protection rule or lowers a password requirement does not trigger any alert. The change propagates to all assigned devices on their next check-in, typically within eight hours, with no notification to your security team.
Compliance threshold lowered to pass blocked devices
Lowering a minimum OS version threshold or removing an encryption requirement causes previously noncompliant devices to become compliant immediately. If Conditional Access was blocking those devices, they regain access the moment they check in. An attacker with Intune admin access can use this to silently restore access for a blocked device.
Both changes are recorded in the Intune audit log, but only after the fact. ManageEngine ADAudit Plus monitors compliance and configuration policy changes in real time and sends immediate alerts when any policy is created, modified, deleted, or reassigned, with before-and-after values for every changed setting.
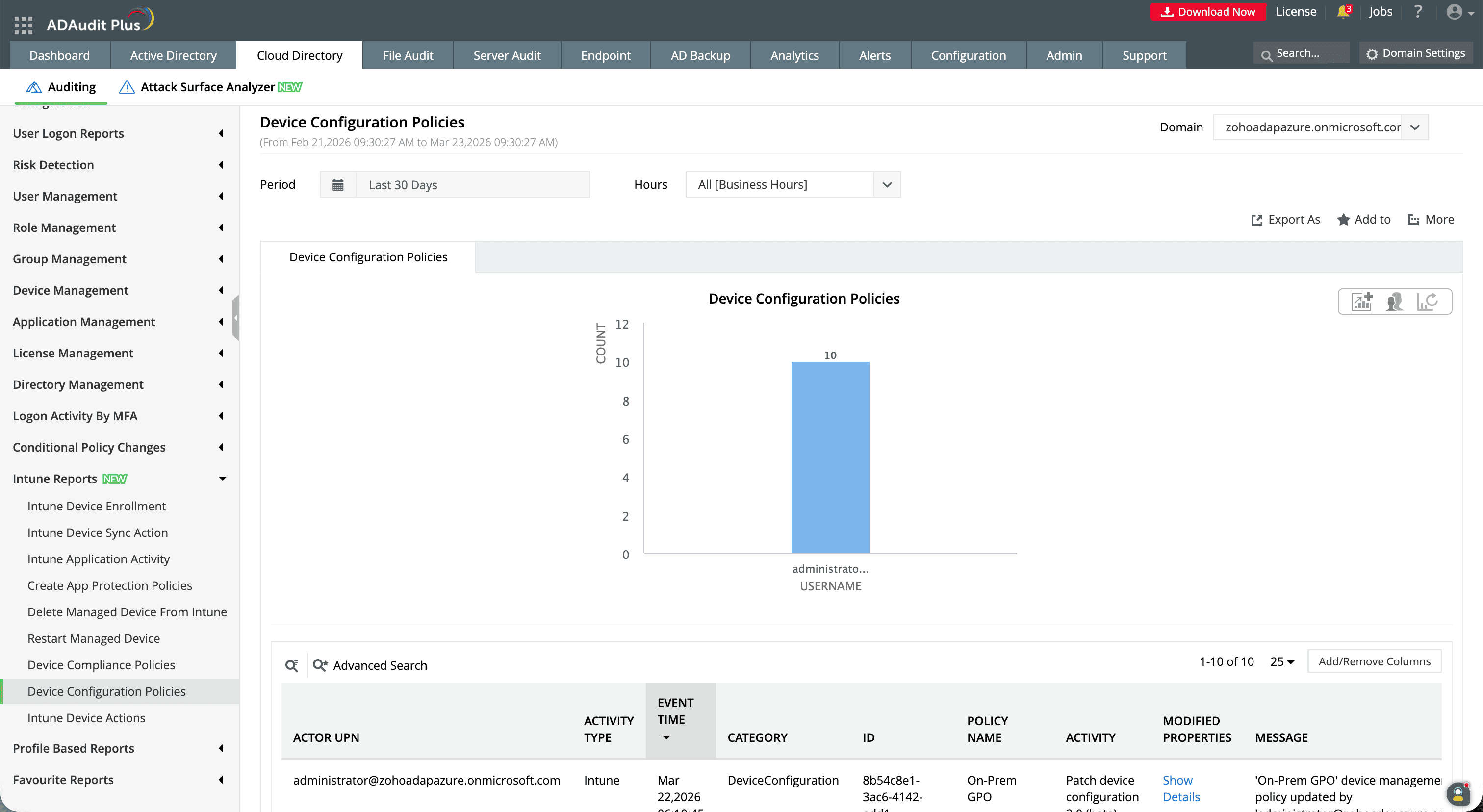
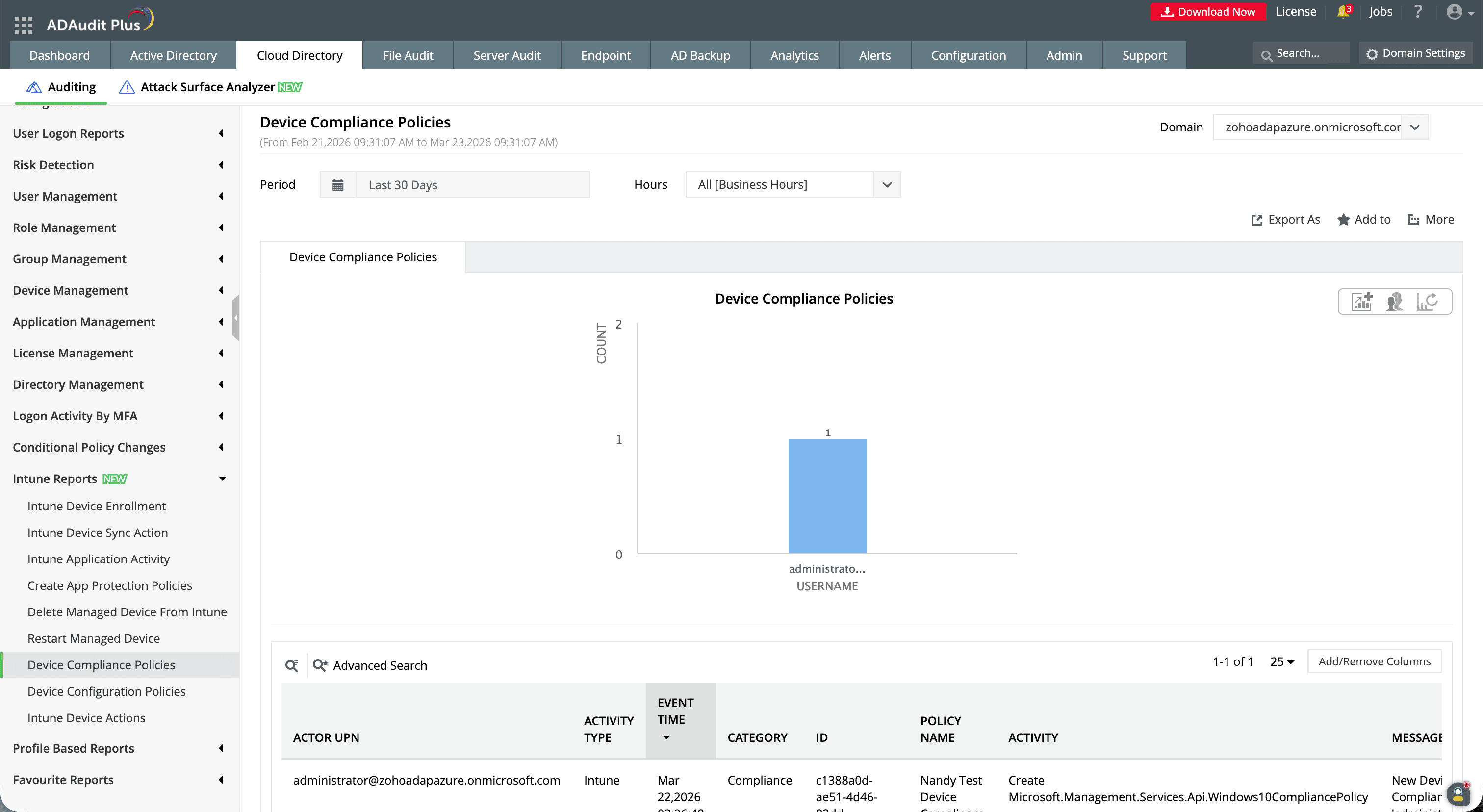
Monitoring Intune policy changes with ADAudit Plus
- Policy creation: who created a policy, which type, which platform, and when
- Setting changes: which settings changed, with old and new values side by side
- Policy deletion: which policy was deleted, by which account, and the timestamp
- Assignment changes: when a policy is assigned to or removed from a user or device group
- Tenant-wide compliance setting changes: changes to the default compliance behaviour
| Capability | Native Intune admin center | ADAudit Plus |
|---|---|---|
| Real-time alerts | No alerts for policy changes | Immediate email and SMS on modification, deletion, or reassignment |
| Before-and-after values | Target(s) field shows changed properties | Old and new values side by side for both policy types |
| Covers both policy types | Separate audit log entries, no unified view | Unified report across compliance and configuration changes |
| Log retention | 2 years in admin center | Configurable archive beyond the 2-year limit |
| Compliance reports | No pre-built reports | SOX, HIPAA, PCI DSS, GDPR, FISMA, GLBA out of the box |
Audit every change to your Intune policies in real time
Try ADAudit Plus free for 30 days. No credit card required.
Frequently asked questions
Yes, this is by design. A configuration policy enforces BitLocker on a device; a compliance policy checks whether BitLocker is on. One writes, the other reads. They do not conflict. If the configuration policy fails to apply and BitLocker is off, the compliance policy detects it and triggers the configured noncompliance response.
If two configuration policies target the same setting with different values on the same device, Intune applies neither. The device keeps its previous value. All non-conflicting settings in both policies still apply. Conflicts appear under Devices > Monitor > Assignment failures.
When a device has multiple compliance policies assigned (because it belongs to several groups), the stricter value for any given setting takes precedence. If one policy requires Windows 11 22H1 and another requires 22H2, the device is held to 22H2. Multiple overlapping policies merge into the strictest combined ruleset for each device.
Experience
ADAudit Plus for free
With ADAudit Plus, you can:
- Get full visibility into logons
- Monitor employee attendance
- Detect attacks like Kerberoasting
- Generate logon audit trails
- And much more











