Configuration policies in Intune are sets of settings you define and deploy to enrolled devices. They control how devices behave: what the lock screen requires, whether the camera is available, which VPN connection is configured, how the browser behaves. The terms 'configuration policy' and 'configuration profile' are used interchangeably. They refer to the same thing.
- What are Intune configuration policies
- Supported platforms
- How to create a policy
- Security risks
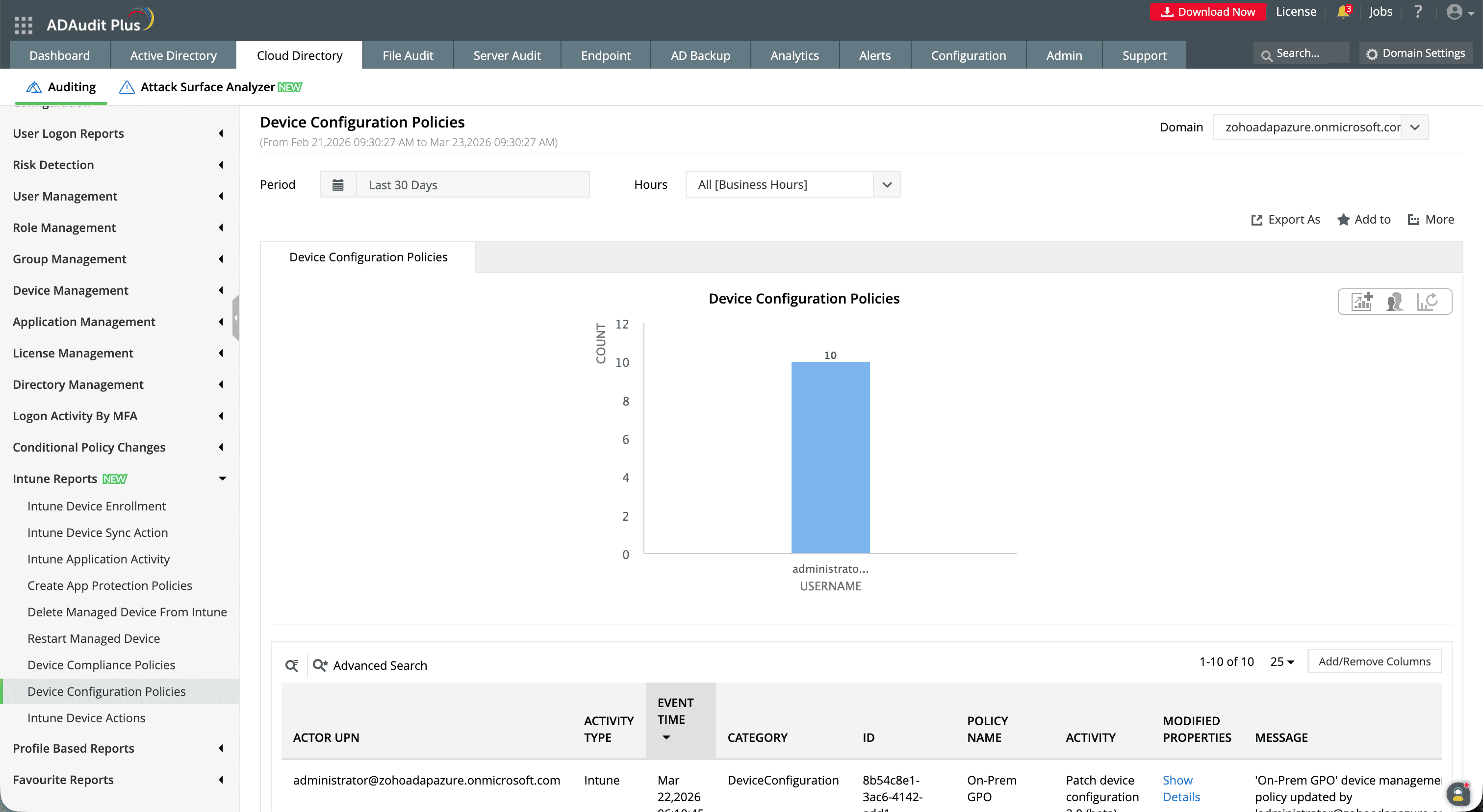
- Monitoring with ADAudit Plus
- FAQ
Configuration policies are how Microsoft Intune controls device settings. They are the cloud equivalent of Group Policy Objects, and that comparison is the quickest way to understand what they do. This guide covers what they are, how they differ from compliance policies, how to create them, where they create security risk when changed without authorization, and how to audit those changes.
What are Intune configuration policies?
An Intune configuration policy is a collection of device or user settings that you define and deploy to enrolled devices. When a device receives a policy, it applies the specified settings and enforces them for as long as the policy remains assigned, enforcing a homepage in Edge, enabling BitLocker, configuring a VPN connection, or restricting the camera.
The best analogy is a Group Policy Object. In an on-premises Active Directory environment, GPOs push settings to domain-joined Windows computers. Configuration policies do the same job for Intune-managed devices across Windows, iOS, Android, macOS, and Linux. The underlying mechanism is different: Intune uses the Configuration Service Provider (CSP) framework rather than the Group Policy engine, but the admin experience is comparable, and Intune supports importing existing ADMX files to migrate existing GPOs.
The terms 'configuration policy' and 'configuration profile' are used interchangeably in Intune. They refer to the same thing.
Configuration policies vs compliance policies
Both policy types can involve passwords, encryption, and OS version, which causes confusion. The distinction is action versus evaluation: configuration policies push settings to a device; compliance policies check whether those settings are present.
| Configuration policies | Compliance policies | |
|---|---|---|
| What they do | Push settings to devices: actively configure them | Check whether settings are in place and report a pass/fail result |
| Effect on device | Applies a setting directly | Reports compliance status; does not change device settings |
| Blocks access? | No | Yes: when paired with Conditional Access, noncompliant devices can be blocked |
| Typical use | Deploy VPN, enforce BitLocker, set browser homepage | Require BitLocker to be on, require a minimum OS version |
You need both. Configuration policies enforce the settings; compliance policies verify they are active. Deploying only compliance policies tells you which devices are noncompliant. It does not fix them.
The two profile types: Settings Catalog and Templates
When you create a configuration policy, you choose one of two profile types.
Settings Catalog (recommended)
The Settings Catalog is a searchable library of every setting Intune can configure, all in one place. You start with a blank policy and add exactly the settings you need. For Windows, the catalog contains thousands of settings drawn from Windows CSPs and ADMX files. For macOS, iOS, and Android it continues to expand with each service release. Microsoft recommends this for all new policies. It offers more granular control and surfaces settings unavailable in any template.
Templates
Templates group related settings under a named category: VPN, Wi-Fi, email, kiosk, endpoint protection, and so on. You pick a template and configure the pre-selected group of settings it contains. For Windows, Microsoft is migrating existing Templates into Settings Catalog versions and is not adding new ones. Use the Settings Catalog for any new Windows policy. Existing template-based policies continue to work without immediate migration.
Note on Administrative Templates
ADMX-backed settings are available in both profile types. In the Settings Catalog, filter by 'Administrative Templates.' You can also import third-party ADMX files (for Chrome, Firefox, or other applications) and manage them as custom configuration profiles using OMA-URI.
Supported platforms
Each configuration policy targets one platform. You cannot create a policy that applies to multiple platforms at once.
- Windows 10 and later (including Windows 11)
- iOS and iPadOS
- Android device administrator: Google is deprecating this for GMS devices; Microsoft recommends moving to Android Enterprise
- Android Enterprise (fully managed, dedicated, corporate-owned work profile, personally owned work profile)
- macOS
- Linux (Ubuntu Desktop 22.04 LTS and 24.04 LTS, Red Hat Enterprise Linux 8 and 9)
Common configuration categories
The settings available vary by platform. These are the most frequently configured categories across Windows, iOS, Android, and macOS:
| Category | What you can configure |
|---|---|
| Password and screen lock | Minimum password length and complexity, maximum failed attempts before lockout, screen lock timeout. |
| Encryption | BitLocker for Windows, FileVault for macOS: enforce encryption at rest and configure recovery key escrow. |
| Browser settings | Edge, Chrome, and Safari homepage, new tab page, extension restrictions, password manager, and safe browsing. |
| Wi-Fi and VPN | Deploy corporate Wi-Fi profiles with SSID, security type, and credentials. Configure VPN server, authentication method, and always-on VPN. |
| Configure Exchange email accounts on devices without requiring users to enter server settings manually. | |
| Device restrictions | Disable the camera, block sideloaded apps, restrict screen capture, prevent factory reset. |
| Endpoint protection | Windows Defender settings, firewall rules, and attack surface reduction rules. |
| Kiosk | Lock a device to run one app or a defined set of apps, used for shared devices and public-facing endpoints. |
| Certificates | Deploy SCEP and PKCS certificates for Wi-Fi, VPN, and email authentication. |
| Custom / OMA-URI | Target any Windows CSP setting not available in the catalog by specifying its OMA-URI path and value directly. |
How to create a configuration policy in Intune
Step 1: Open the policy creation wizard
intune.microsoft.com.
Devices > Manage devices > Configuration, then select Create > New policy.
- Select a platform and choose Settings Catalog or Templates as the profile type. For Windows, select Settings Catalog.
- Select Create.
Step 2: Basics
- Enter a name that identifies the platform, feature, and scope, for example: 'Windows - BitLocker Encryption - All Corporate Devices.'
- Add a description documenting what the policy does and who created it.
- Select Next.
Step 3: Configuration settings
Add settings, search for the setting by name or category, select it, close the picker, and set the value.
- For Templates: configure the settings pre-grouped in the chosen template.
- For Custom OMA-URI: select Add and specify the OMA-URI path, data type, and value.
- Select Next.
Step 4: Assignments
- Under Included groups, select the user or device groups this policy applies to.
- Under Excluded groups, add any groups that should be exempt.
- Select Next, review, then select Create.
After creation, Intune notifies assigned devices to check in. If the first notification fails, Intune retries three more times. Devices that miss all notifications pick up the policy at their next scheduled check-in, typically within eight hours. Users can trigger an immediate sync from the Company Portal app.
Policy conflicts and precedence
Intune does not apply a strict precedence hierarchy to configuration policies the way Group Policy applies GPO precedence. If two policies configure the same setting on the same device with different values, Intune flags a conflict and applies neither value, and the device retains whatever it had before. All non-conflicting settings in both policies continue to apply normally.
Conflicts are reported under Devices > Monitor > Assignment failures. Resolve them by removing the duplicate setting from one policy or by consolidating the conflicting policies into one.
To avoid conflicts: assign user settings to user groups and device settings to device groups. Mixing assignment targets on the same setting is the most common cause.
Security risks from altered configuration policies
Configuration policies enforce your device security baseline. When they are changed without authorization or removed silently, the security posture of every device in the affected group degrades on the next check-in.
Encryption requirement removed
A policy enforcing BitLocker or FileVault can be modified to remove that requirement. Every device that checks in after the change stops enforcing encryption. Without a compliance policy independently verifying encryption status, the gap may go undetected.
Endpoint protection settings weakened
Windows Defender, firewall rules, and attack surface reduction rules are configurable through endpoint protection profiles. Lowering threat response levels or disabling network protection propagates to all assigned devices on their next check-in, with no user-visible alert.
Device restriction bypass
Policies blocking camera access, restricting app installations, or preventing factory reset can be modified to remove those restrictions. A policy deletion or assignment removal can silently re-enable capabilities that were locked down, particularly significant on kiosk and shared devices.
VPN and Wi-Fi profile manipulation
VPN and Wi-Fi profiles contain connection endpoints and authentication methods. A modified profile can redirect devices to a different endpoint or downgrade the authentication method. Because devices apply updated profiles silently, there is no user-visible signal.
Silent assignment removal
Removing a policy assignment from a device group does not notify the device or the user. Settings previously enforced either persist at their last value or revert to device defaults, either way creating an unexpected security gap.
These changes are all captured in the Intune audit log, but the admin center does not alert in real time when they occur. ManageEngine ADAudit Plus monitors Intune configuration policy changes and generates immediate alerts when a policy is created, modified, deleted, or reassigned, so your security team is notified before affected devices check in.
Monitoring configuration policy changes with ADAudit Plus
Intune records every configuration policy change in its audit log, but without real-time alerting you rely on periodic reviews to catch unauthorized changes. By the time a weakened endpoint protection policy is noticed, it may have already propagated to hundreds of devices.
What ADAudit Plus tracks
With ADAudit Plus' Intune admin center auditing, you can monitor and report on:
- Configuration policy creation: who created a policy, on which platform, and when
- Setting changes: which settings were modified, with before-and-after values
- Policy deletion: which policy was deleted, by whom, and the timestamp
- Assignment changes: when a policy is assigned to or removed from a group
- OMA-URI and custom profile changes: modifications to custom configuration values
How ADAudit Plus extends native Intune
| Capability | Native Intune admin center | ADAudit Plus |
|---|---|---|
| Real-time alerts | No alerts on policy changes | Immediate email and SMS alerts on modification, deletion, or reassignment |
| Log retention | 2 years in admin center | Configurable archive beyond the 2-year limit |
| Compliance reports | No pre-built reports | Out-of-the-box reports for SOX, HIPAA, PCI DSS, GDPR, FISMA, GLBA |
| Before-and-after values | Target(s) section shows changed properties | Old and new values side by side in report view |
| Cross-platform visibility | Intune portal only | Unified view across Intune, Entra ID, on-premises AD, file servers, workstations |
A one-stop solution for IT auditing, compliance, and threat response
Try ADAudit Plus free for 30 days. No credit card required.
Frequently asked questions
In the Microsoft Intune admin center at intune.microsoft.com. Navigate to Devices > Manage devices > Configuration to see all policies, create new ones, and check assignment status. You can also work per-platform by selecting a platform under Devices (for example, Windows or iOS/iPadOS).
A configuration profile pushes settings to a device and enforces them. A compliance policy checks whether those settings are present and reports a pass or fail. It does not change the device. A configuration policy enforces BitLocker encryption; a compliance policy verifies it is on. You need both: one configures, the other validates.
There is no strict precedence order. If two configuration policies apply conflicting values for the same setting on the same device, Intune flags a conflict and applies neither. All non-conflicting settings in both policies apply normally. Conflicts appear under Devices > Monitor > Assignment failures. Resolve them by removing the duplicate setting from one policy or merging the conflicting policies.
Sign in to the Intune admin center, go to Devices > Manage devices > Configuration, and select Create > New policy. Choose a platform, select Settings Catalog (for Windows and most new policies), name the policy, add the settings you want, then assign it to a user or device group. The full creation walkthrough is covered in the How to create a configuration policy section above.
Experience
ADAudit Plus for free
With ADAudit Plus, you can:
- Get full visibility into logons
- Monitor employee attendance
- Detect attacks like Kerberoasting
- Generate logon audit trails
- And much more











