- Free Edition
- Quick links
- Active Directory management
- Active Directory reporting
- Active Directory delegation
- Active Directory permissions management and reporting
- Active Directory automation
- Governance, risk, and compliance
- Microsoft 365 management and reporting
- Microsoft 365 management and reporting
- Microsoft 365 management
- Microsoft 365 reports
- Microsoft 365 user management
- Microsoft 365 user provisioning
- Microsoft 365 license managementn
- Microsoft 365 license reports
- Microsoft 365 group reports
- Dynamic distribution group creation
- Dynamic distribution group reports
- Exchange management and reporting
- Active Directory integrations
- Popular products
What is entitlement management?
Entitlement management is the process of defining, governing, and managing what level of access users have to systems, applications, data, and resources across an organization. It involves discovering all existing entitlements, defining access policies, assigning entitlements based on roles or attributes, monitoring usage, and periodically reviewing and certifying access. Without an entitlement management system like ADManager Plus, organizations quickly lose visibility into orphaned privileges, excessive permissions, and outdated roles, all of which significantly increase security risk and compliance exposure.
What is an entitlement?
An entitlement is a specific access right or permission granted to a user or an identity. It could be a group membership in Active Directory (AD) or something complex like a business role that allows an identity to approve financial transactions, access sensitive data, or have administrative control over an enterprise application. They define what actions a user can perform, what data they can view or modify, and what systems they can interact with.
Types of entitlements
Entitlements exist at multiple layers within an organization, and understanding them is essential for building an effective entitlement management strategy.
- User entitlements: These define what an individual user can access, such as group memberships, roles within applications, or folder permissions.
- App entitlements: These are the permissions within an application and are more granular and business-specific. These include roles like Admin or Approver.
- Access entitlements: These control access to network resources such as file systems, databases, servers, and cloud environments.
- Business entitlements: These are privileges such as financial approvals, procurement rights, or access to sensitive customer or employee data. Since they carry direct business risk, they require the highest level of governance and audit.
Why entitlement management is critical
Security incidents do not often result from external attackers bypassing defenses but from misuse or abuse of access that was never properly reviewed, restricted, or revoked. Excessive entitlements accumulate naturally over time as users change roles, start new projects, or are assigned responsibilities, leading to a situation where individuals retain access long after it is no longer justified.
Employees may hold privileges they no longer need, contractors may retain access after project completion, and former employees may continue to exist in systems due to incomplete offboarding, all of which lead to security risk and compliance misalignment.
How entitlement management works
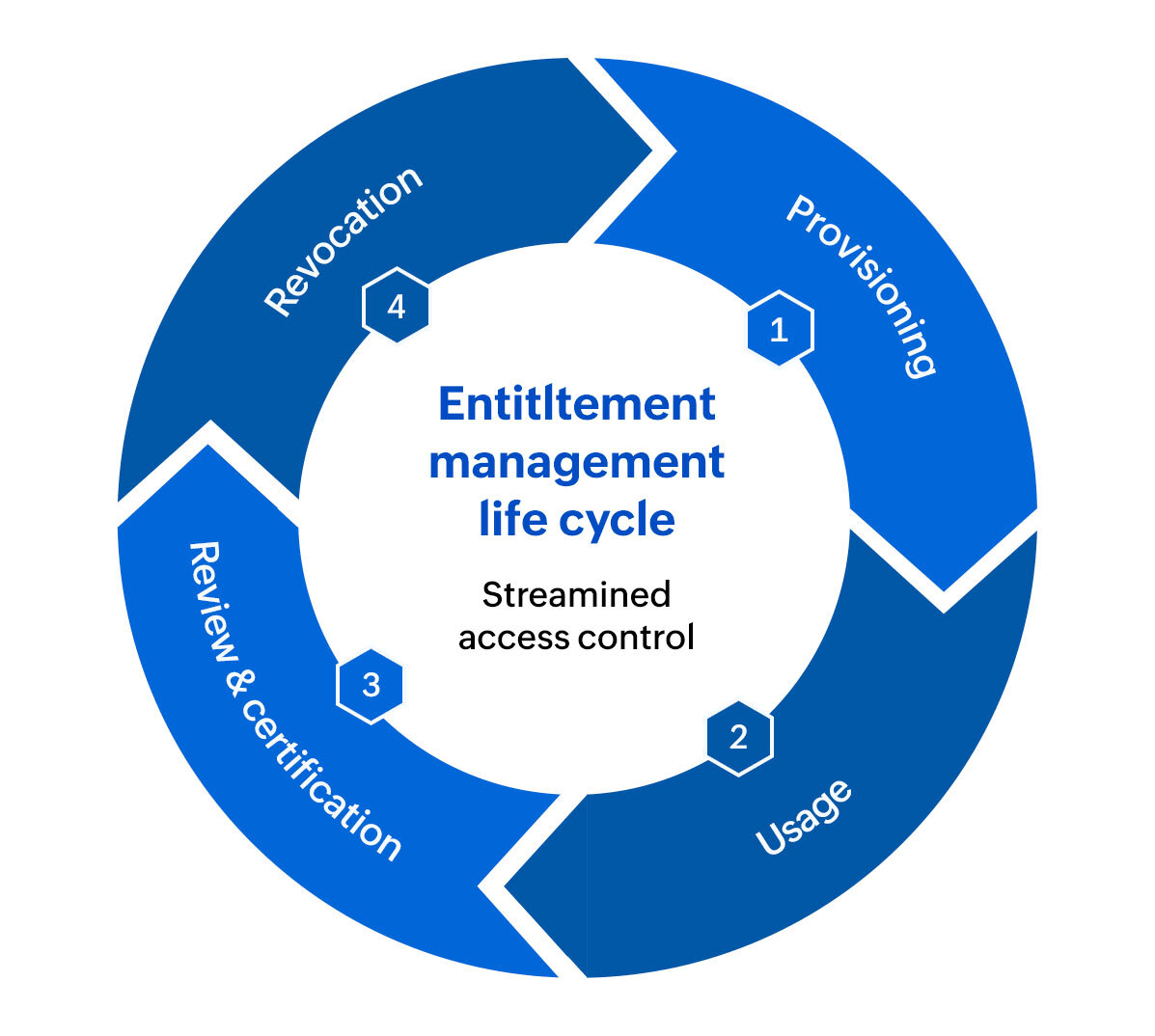
Entitlement management operates as a continuous life cycle rather than a one-time task. From onboarding new employees to offboarding contractors, every change in a user's job role requires entitlement decisions.
The entitlement life cycle comprises four key phases:
1. Provisioning: When a new user joins or changes roles, appropriate entitlements are assigned. This can be done manually by an IT admin using AD groups or automatically based on HR data and role templates.
2. Usage: The user uses their entitlements regularly and access logs and activity monitoring provide visibility into actual usage patterns.
3. Review or certification: Managers and entitlement owners periodically review users' access to ensure it's still appropriate. This is often called access certification or entitlement recertification.
4. Revocation: When users leave, change roles, or when access is deemed unnecessary, entitlements are revoked. Automated deprovisioning reduces the risk of orphaned accounts.
All four stages are critical and help in efficient entitlement management and comply with regulations like SOX, HIPAA, and the PCI DSS.
Entitlement management vs. role-based access control
Role-based access control (RBAC) is an access control model where users are assigned roles which determine their access to network resources. While it simplifies access management, roles can become broad, leading to the accumulation of exceptions and privileges, defying the access control model's purpose.
Entitlement management goes beyond RBAC by governing the permissions within these roles, allowing organizations to manage access at a granular level, across multiple systems, with dynamic policies and continuous validation.
Key components of an entitlement management system
To manage your entitlements efficiently, you need to ensure that your entitlement management system handles these critical areas:
- Entitlement catalog: An entitlement catalog enables organizations to visualize entitlement structures, understand permission hierarchies, and identify high-risk privileges.
- Automated workflows: Entitlement requests are routed to the appropriate approvers based on predefined workflows. Once approved, entitlements are automatically provisioned and no manual intervention is required. This drastically reduces provisioning time from days to minutes.
- Access certification: Continuous access reviews and certification campaigns provide the governance layer that keeps entitlement structures accurate over time. Managers and system owners are periodically required to validate whether each user's access is still appropriate.
- JIT access: With JIT access, users receive elevated entitlements only for a specific task and for a limited duration. Once the task is completed or the time window expires, access is automatically revoked.
- RBAC: Empowers organizations to group entitlements into standardized roles that reflect job functions such as HR manager, finance analyst, or IT administrator.
- ABAC: Introduces contextual intelligence into access decisions and allows entitlements to be granted or restricted based on user attributes such as department, location, or employment type.
Simplify entitlement management in your organization
ADManager Plus, an IGA solution with capabilities such as risk assessment, access certification, and risk exposure management, enables organizations to securely govern and manage users' access rights across AD and Microsoft 365. With ADManager Plus, you can:
- Gain complete visibility into users entitlements across AD, Microsoft 365, and Exchange, making it easy to understand who has access to what and why.
- Automate entitlement provisioning and revocation using orchestration workflows that assign the right access when users join or change roles and remove all access instantly when users leave.
- Perform continuous risk assessment and identify dormant users, excessive privileges, and dormant access.
- Run automated access reviews and certification campaigns that allow managers and system owners to validate user access periodically.
- Enforce least privilege consistently across the organization, reducing overprovisioning and preventing privilege accumulation.
- Generate audit-ready compliance reports for regulatory frameworks and internal governance requirements.
FAQ
An entitlement is a specific permission or access right that allows a user or system identity to perform certain actions within an application, system, or business process.
An entitlement manager or entitlement owner is the person or team responsible for defining, approving, and reviewing access rights to a specific system or resource. For example, a sales director might be the entitlement manager for a CRM application, responsible for certifying who on the sales team should have access. Entitlement managers ensure that user access aligns with business needs and compliance requirements.
The terms entitlements and access permissions are often used interchangeably, but permissions are the granular settings that define what actions are allowed, while entitlements bundle multiple permissions.
An entitlement policy is a set of rules that defines who can request access, who must approve it, and how long that access should last. This policy ensures that least privilege is maintained throughout the user entitlement life cycle.
Other features
Bulk User Management
Fire a shotgun-shell of AD User Management Tasks in a Single Shot. Also use csv files to manage users. Effect bulk changes in the Active Directory, including configuring Exchange attributes.
Active Directory Computer Reports
Granular reporting on your AD Computer objects to the minutest detail. Monitor...and modify computer attributes right within the report. Reports on Inactive Computers and operating systems.
Active Directory Delegation
Unload some of your workload without losing your hold. Secure & non-invasive helpdesk delegation and management from ADManager Plus! Delegate powers for technician on specific tasks in specific OUs.
Microsoft Exchange Management
Create and manage Exchange mailboxes and configure mailbox rights using ADManager Plus's Exchange Management system. Now with support for Microsoft Exchange 2010!!
Active Directory Cleanup
Get rid of the inactive, obsolete and unwanted objects in your Active Directory to make it more secure and efficient...assisted by ADManager Plus's AD Cleanup capabilities.
Active Directory Automation
A complete automation of AD critical tasks such as user provisioning, inactive-user clean up etc. Also lets you sequence and execute follow-up tasks and blends with workflow to offer a brilliant controlled-automation.
Need Features? Tell Us
If you want to see additional features implemented in ADManager Plus, we would love to hear. Click here to continue
