The gpresult command is a built-in Windows diagnostic tool that displays the Resultant Set of Policy (RSoP), the actual Group Policy settings currently applied to a specific user or computer. System administrators often use it to verify if Group Policy Objects (GPOs) are applied correctly, troubleshoot policy conflicts, audit security settings, and confirm policy compliance across domain-joined machines.
The gpresult command displays the RSoP report, a snapshot of all Group Policy settings that were applied to a user or computer the last time a Group Policy was processed. It shows which GPOs were applied, which were filtered or denied, and the precedence order to resolve conflicts.
RSoP works in two modes:
Here's the syntax for the gpresult cmdlet:
gpresult [/s <Computer>] [/u <Domain\User>] [/p <Password>]
| Parameter | Description |
|---|---|
| /r | Displays a summary of RSoP data, including applied GPO names, OU path, domain information, and group memberships. This is the most commonly used flag for day-to-day policy verification. |
| /v | Adds registry key paths, logon script filenames, last script execution times, and additional policy setting details beyond the /r parameter. This is helpful in tracing where a setting comes from. |
| /z | Displays everything the /v parameter shows along with all the GPOs that have the setting configured, including GPOs that were applied with lower precedence and GPOs that were denied. |
| /h <filename> | Exports the RSoP report to an HTML file. The filename parameter specifies the output path and if no path is given, the file saves to the current working directory. |
| /x <filename> | Exports the RSoP report to an XML file. This is useful for parsing policy data programmatically or storing results in a SQL database. |
| /f | Forces gpresult to overwrite an existing output file. Without the /f parameter, the command returns an error if the specified filename already exists. |
| /s <computer> | Specifies a remote computer name or IP address to query. |
| /u <Domain\User> | Runs the command under the credentials of the specified user account. This is used with the /s parameter to authenticate against a remote machine when the current session does not have access. |
| /p <Password> | This is the password for the /u user account. If the /p parameter is omitted when /u is specified, gpresult prompts for the password interactively. |
| /user <TargetUser> | Specifies the domain user whose RSoP data you would like to verify. This is useful in targeting query policies for a user other than the currently logged-on account. |
| /scope {user | computer} | Limits the output to either user-scoped or computer-scoped policy settings. |
To run the gpresult command:
gpresult /r
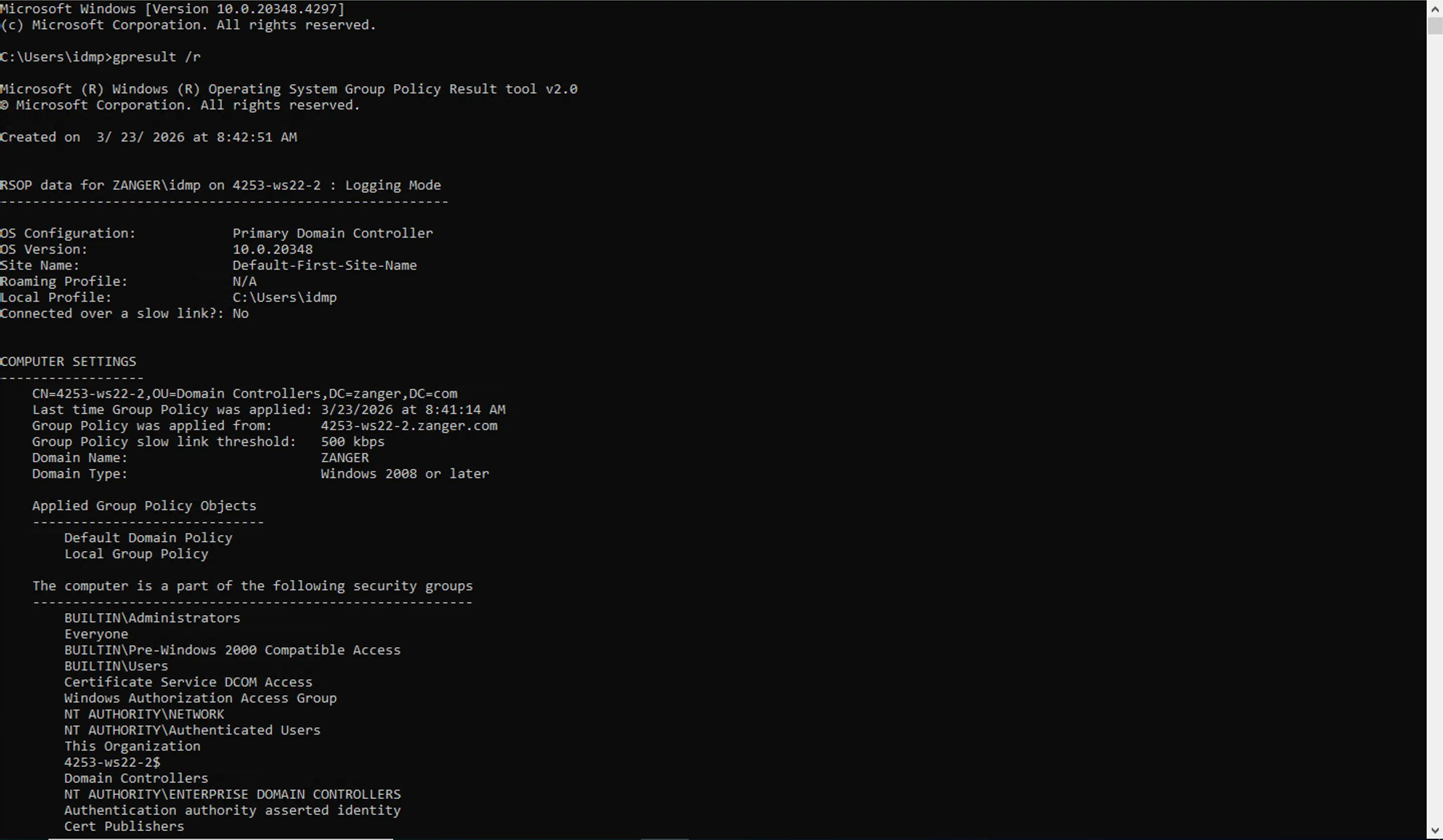
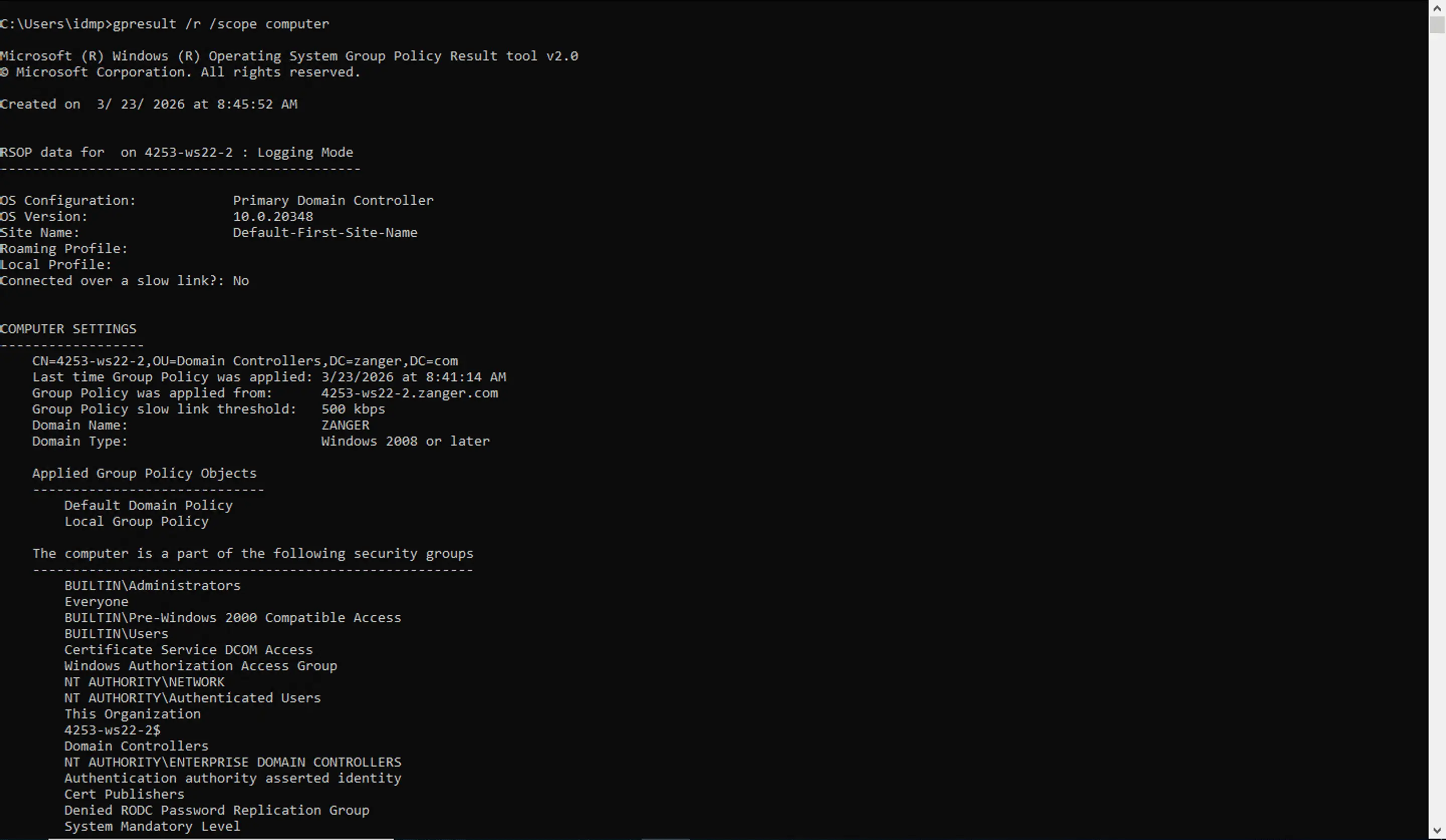
The /scope computer parameter filters output to show the policies under Computer Configuration, such as password policies, software deployments, and security settings that apply regardless of who is logged on. Unlike /scope user, it always requires an elevated Command Prompt. The output includes the machine's OS configuration and AD site, whether a slow link was detected during the last refresh, the timestamp and domain controller (DC) of the last successful computer policy refresh, applied GPOs in precedence order, and any filtered GPOs.
Choosing the right parameter is important as each returns a different level of detail. Here is what each flag provides and when to use it:
gpresult /r is the standard starting point for most policy verification tasks. When run as administrator, it returns two sections:
gpresult /v adds a significant amount of extra detail over the /r parameter. In addition to everything /r returns, /v includes:
When multiple GPOs configure the same setting, Windows applies them in LSDOU order with each level overriding the one before it. A GPO linked to a child OU therefore takes precedence over a conflicting setting at the domain level. Within the same container, link order determines the winner.
gpresult /r shows which GPOs were applied but not which one enforced a specific setting. To understand precedence, you can use the /z parameter. It returns everything /v shows, along with:
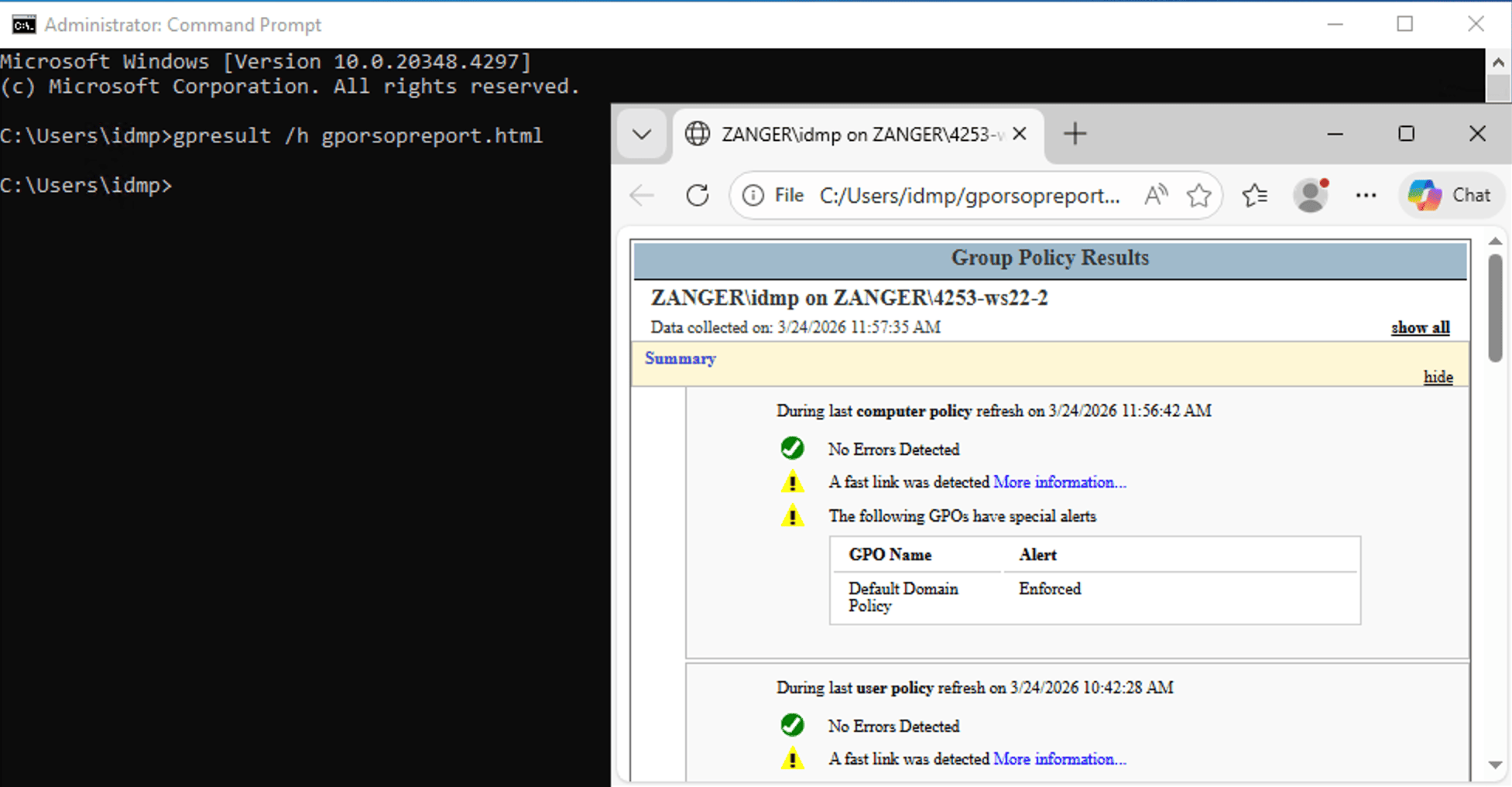
The /h parameter saves the RSoP report as an HTML file that can be opened in any browser. It produces a well-formatted and color-coded report that is far easier to read than the console output, especially for storing as a compliance record. Use the following command to export it:
gpresult /h gpreport.html
To save the file in a specific path, use the following command:
gpresult /h C:\Reports\gposopreport.html
If the file already exists and you want to overwrite it, add the /f flag:
gpresult /h C:\Reports\gprsopreport.html /f
To open the report, navigate to the saved path in File Explorer and double-click the file, or open it directly from the command line:
start C:\Reports\gprsopreport.html
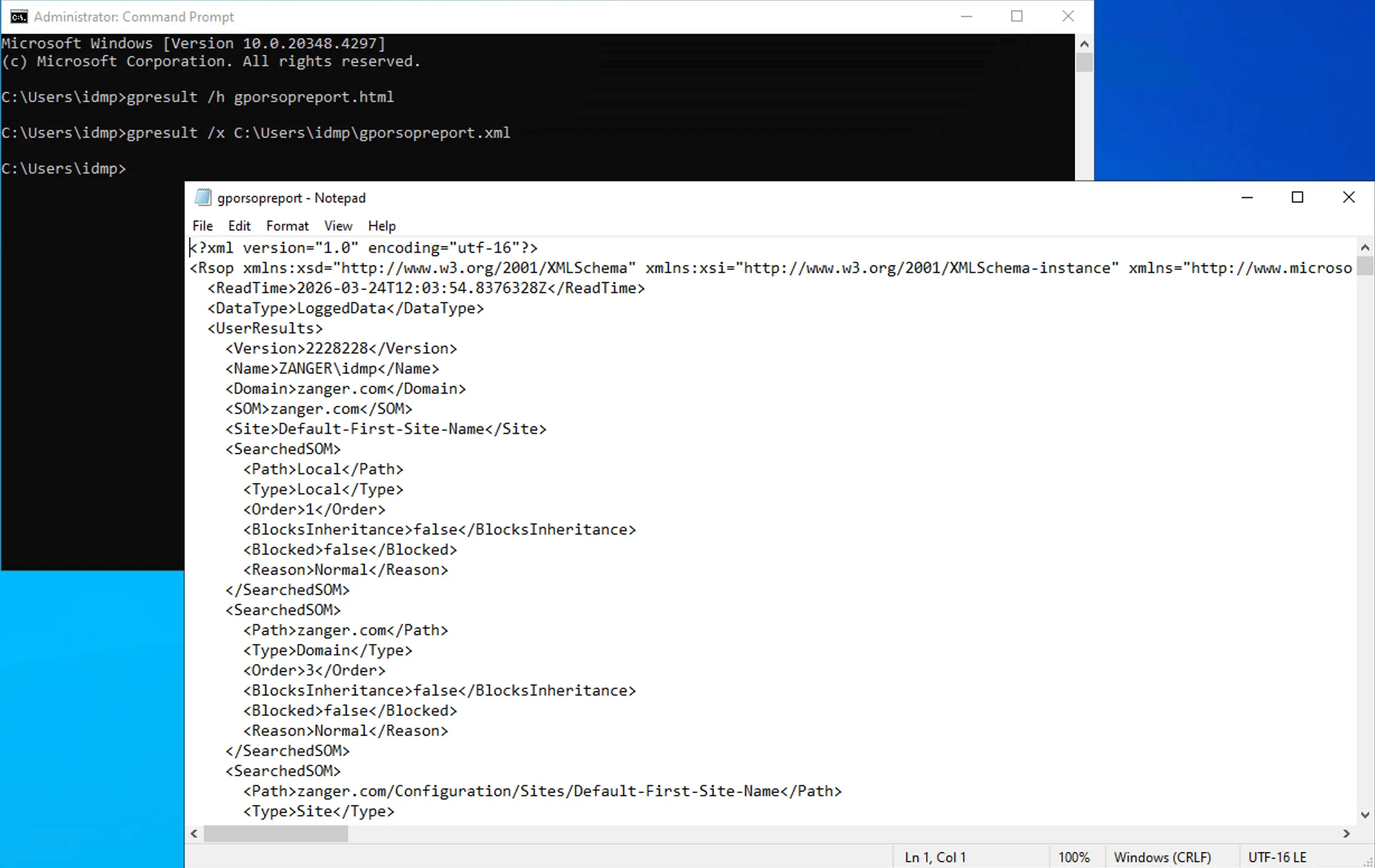
The /x parameter generates an XML version of the same RSoP data. This is useful when you want to parse policy results programmatically.
gpresult /x C:\Reports\gprsopreport.xml
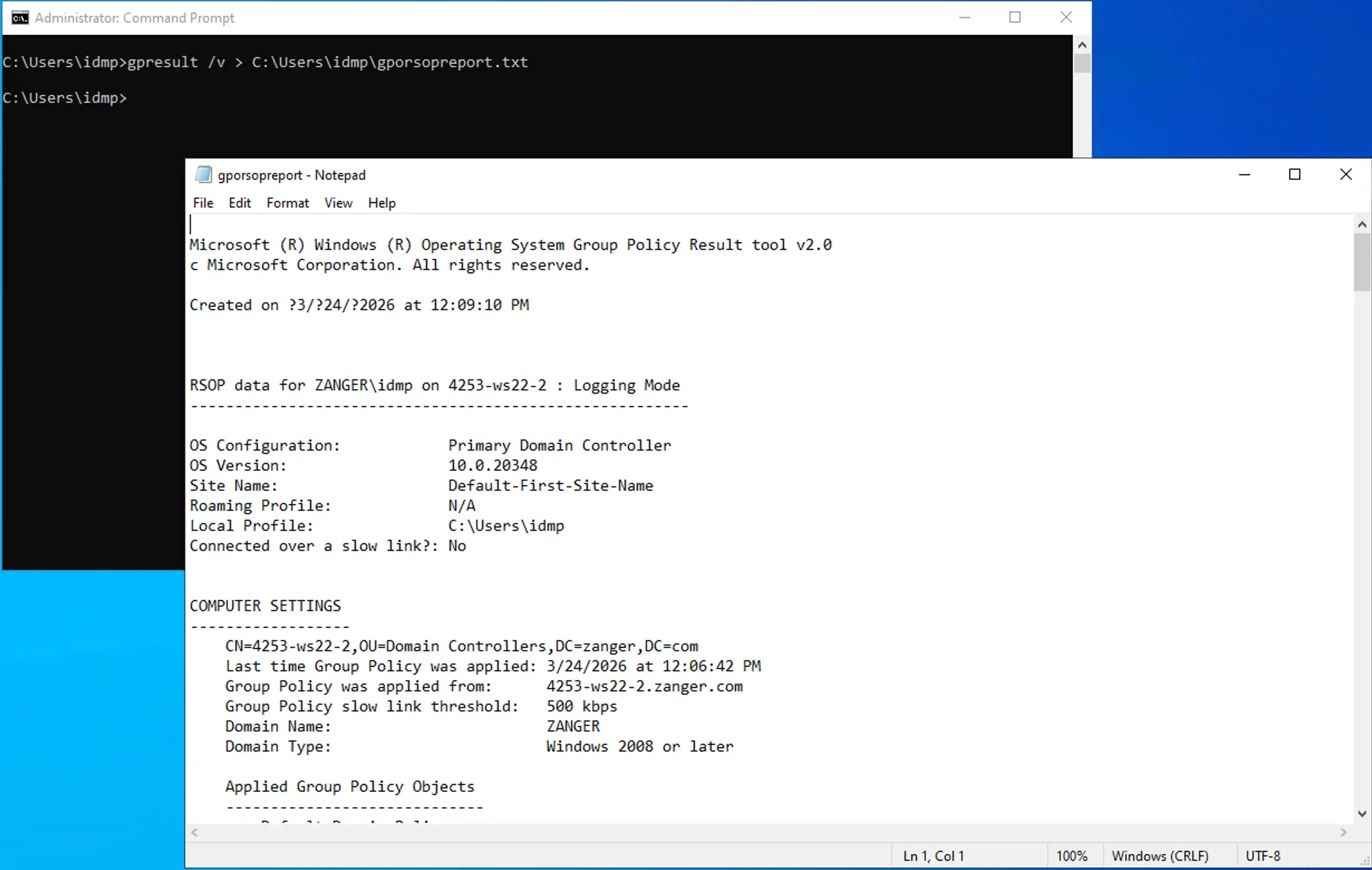
For simple text output, redirect the console output to a file using the > operator. This works with any gpresult flag:
gpresult /v > C:\Reports\policy.txt
The > operator creates the file if it does not exist and overwrites it if it does. Use >> to append to an existing file instead of overwriting.
gpresult /r /scope user
gpresult /r /scope computer
gpresult /r /user DOMAIN\john
gpresult /s PC-234 /r
gpresult output can run to hundreds of lines. Piping it through findstr lets you isolate exactly what you are looking for without scrolling through the full result.
gpresult /r | findstr /i "denied" # show only filtered or denied GPOs
If you want to verify the effect of a policy change you just made, force a refresh first so gpresult reflects the latest state rather than the previous cycle.
gpupdate /force && gpresult /r
RSoP is the Group Policy framework that computes and records the final set of policy settings applied to a user or computer after all inheritance, precedence, filtering, and enforcement rules have been evaluated. Every time Group Policy is processed on a Windows machine, the RSoP provider logs the outcome in WMI. The gpresult command queries that WMI log and presents the data in a readable format.
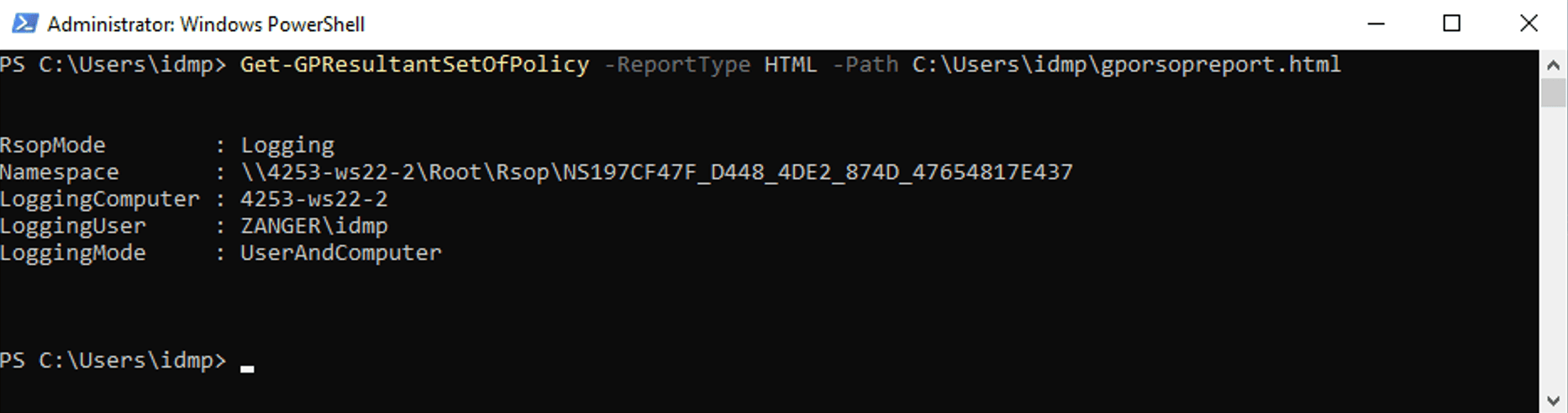
Windows PowerShell includes the Get-GPResultantSetOfPolicy cmdlet, which produces the same RSoP data as gpresult /h or gpresult /x but in PowerShell. It is particularly useful in automation and scripting contexts.
To generate the RSoP report using PowerShell:
Get-GPResultantSetOfPolicy -ReportType HTML -Path C:\Reports\RSoP.html
Here are some key use cases for the gpresult command:
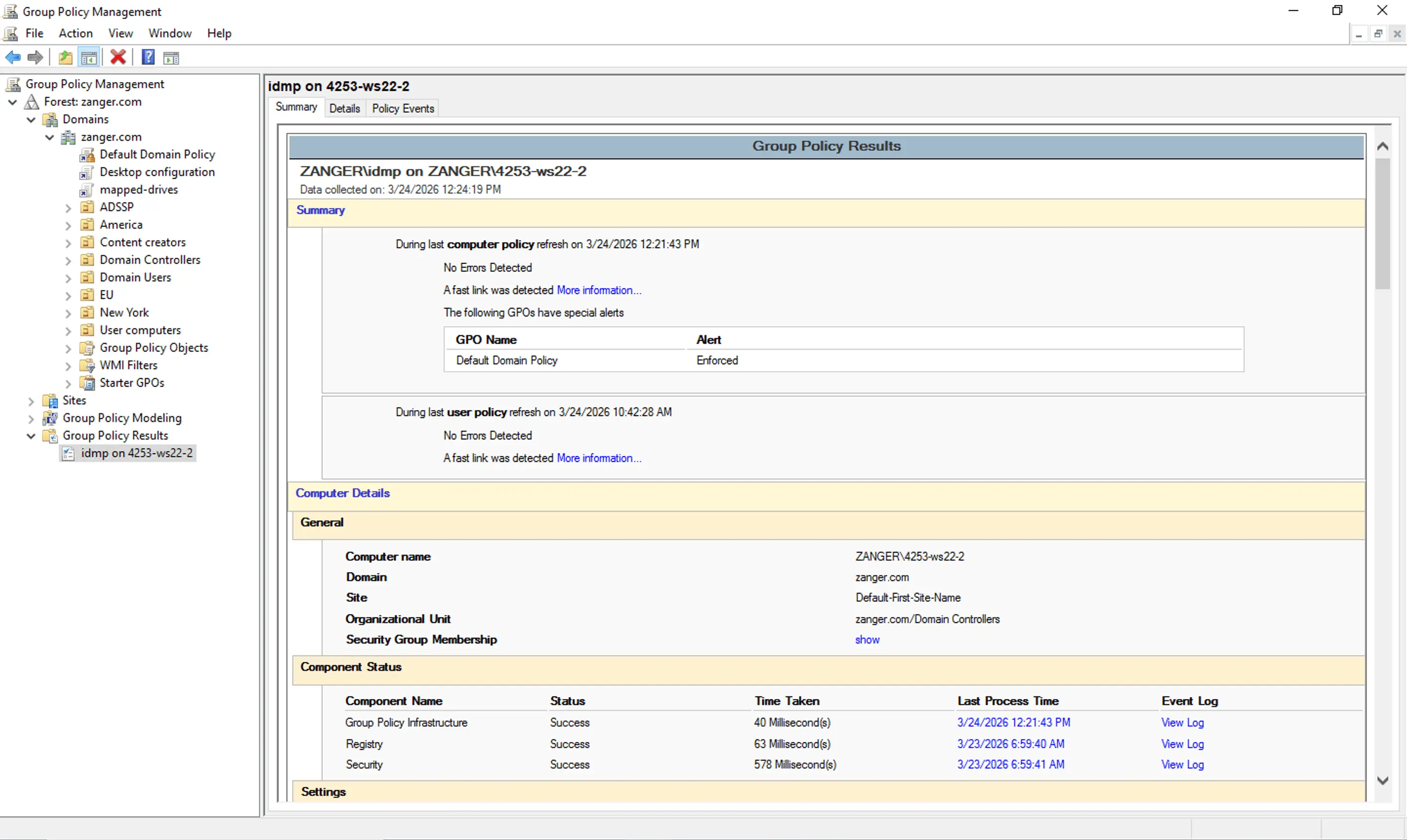
The Group Policy Management Console (GPMC) includes a built-in Group Policy Results Wizard that produces the same RSoP data as gpresult but in a graphical HTML report, with a Settings tab showing the final GPO for each individual policy setting and a Policy Events tab listing all related event log entries.
To generate the report:
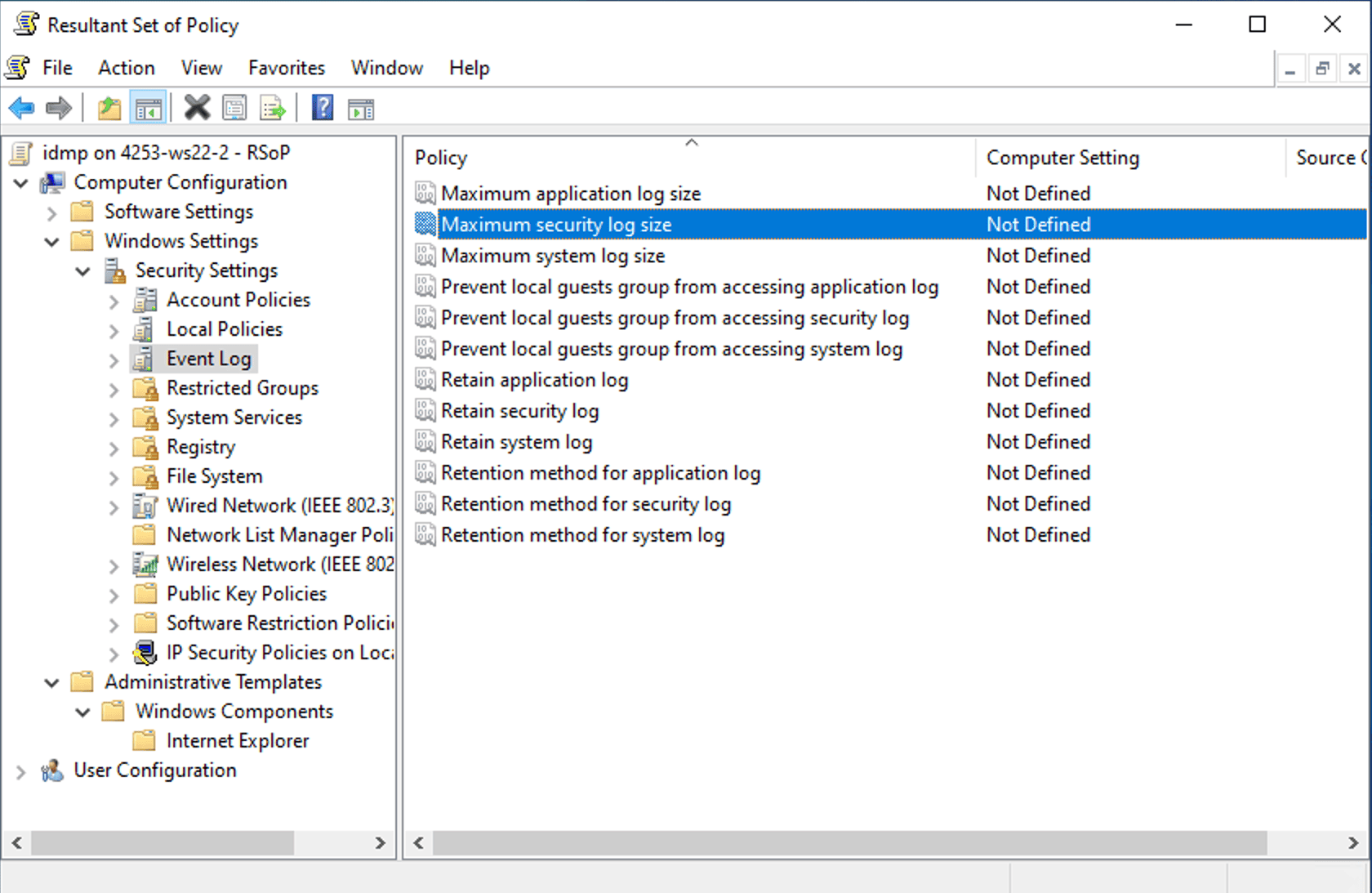
rsop.msc is a built-in MMC snap-in that displays applied Group Policy settings in a graphical tree view, similar to the Local Group Policy Editor. It is the quickest way to get a visual overview of applied policies without generating a report file or using the command line.
However, rsop.msc does not show all Microsoft Group Policy settings, and it only displays settings that were applied through client-side extensions that support RSoP logging. For a complete picture, use gpresult /h or the Group Policy Results Wizard instead.
To view the RSoP:
To view the Group Policy results for a different user or computer, use the stand-alone wizard instead:
Here's how you can generate this report in ADManager Plus:
Cause: This error occurs when the gpresult command is run without administrative privileges. Without administrator privileges, Windows restricts the RSoP query to user-scoped policy data and blocks access to computer-scoped settings. This also occurs when saving an HTML report to a path the session has no write permission to or when a remote query uses an account that is not a local administrator on the target machine.
To fix this error:
gpresult /h C:\Users\Personal\gpreport.html.
Cause: Running gpresult from a non-elevated Command Prompt returns only user-scoped settings and Windows does not expose computer-scoped RSoP to standard sessions. A secondary cause is running the command with a different admin account than the logged-on user; in that case, gpresult queries the elevated account's context, not the standard user's, and returns the message.
To fix this error:
gpresult /r /user DOMAIN\john
Cause: The GPO may not be linked to the correct OU, is excluded by security filtering or a WMI filter, may have its link disabled, or is blocked by inheritance.
To fix this error:
While the gpresult command is effective for single machines, it has limitations at scale. It queries one computer at a time; provides no historical data; and cannot create, link, or migrate GPOs. ADManager Plus addresses all of these through its GPO management and reporting capabilities without requiring PowerShell or command-line access.
Here's how you can manage and report on your GPOs with ADManager Plus:
rsop.msc is the MMC snap-in that provides a graphical view of the same policy data that gpresult displays in the command line. It is available on all domain-joined Windows machines by pressing Win + R and typing rsop.msc. However, it cannot query remote machines and does not support scripting. For troubleshooting and automation, gpresult is the more capable tool.
By default, gpresult /h saves the HTML report in the directory that Command Prompt or PowerShell is open in when you run the command. To confirm this before running, type echo %cd%. To save to a specific location, provide a full path:
gpresult /h C:\Reports\gpreport.html
gpresult /r returns a summary showing applied GPOs, including GPO names, OU paths, and group memberships, which is sufficient for confirming that a policy is applied. gpresult /v adds the registry key path for each policy setting, logon script filenames, and last script execution times and helps understand where a specific setting is coming from.
gpresult is most commonly used by administrators to:
gpresult displays the results of the last Group Policy processing cycle and which policies were applied. gpupdate forces Windows to immediately reapply Group Policies from the DC. gpresult is useful in diagnosing which Group Policies were applied, while gpupdate /force is useful in pushing a new policy change to a machine without waiting for the next automatic refresh interval.
The gpresult command is available on all major Windows versions from Windows XP onwards. It comes as a built-in tool on Windows 10, Windows 11, and all Windows Server editions from 2003 through 2025, with no additional installation required.
On ARM64 Windows 11 devices, the /h parameter does not work with the default gpresult.exe. You can use C:\Windows\SysWow64\gpresult.exe /h report.html instead.
Use the /user parameter followed by the target username to run gpresult as another user. Ensure that the user has logged on to the machine at least once for RSoP data to exist. Use the following command:
gpresult /r /user DOMAIN\john
To query a different user on a remote machine, combine the /s and /user parameters:
gpresult /s CORP-PC-01 /user DOMAIN\johndoe /r
Running gpresult /r without elevation returns user-scoped policy settings for the current user and requires no special rights. Querying computer-scoped settings, either with /scope computer or the full /r output requires an elevated Command Prompt.
You need either local administrator rights on the remote machine, or the Remotely access Group Policy Results data permission on the domain or OU containing the target computer.