Today's employees have become highly mobile—they work from home, in transit, or while they travel around the globe. Organizations also employ temporary employees, such as contract employees, who only work remotely. All of these people have to connect securely to their organization's networks using VPNs and it's important to monitor accesses to these VPNs, to ensure only authorized people are logging into the network. EventLog Analyzer is the ideal tool to help you achieve this.
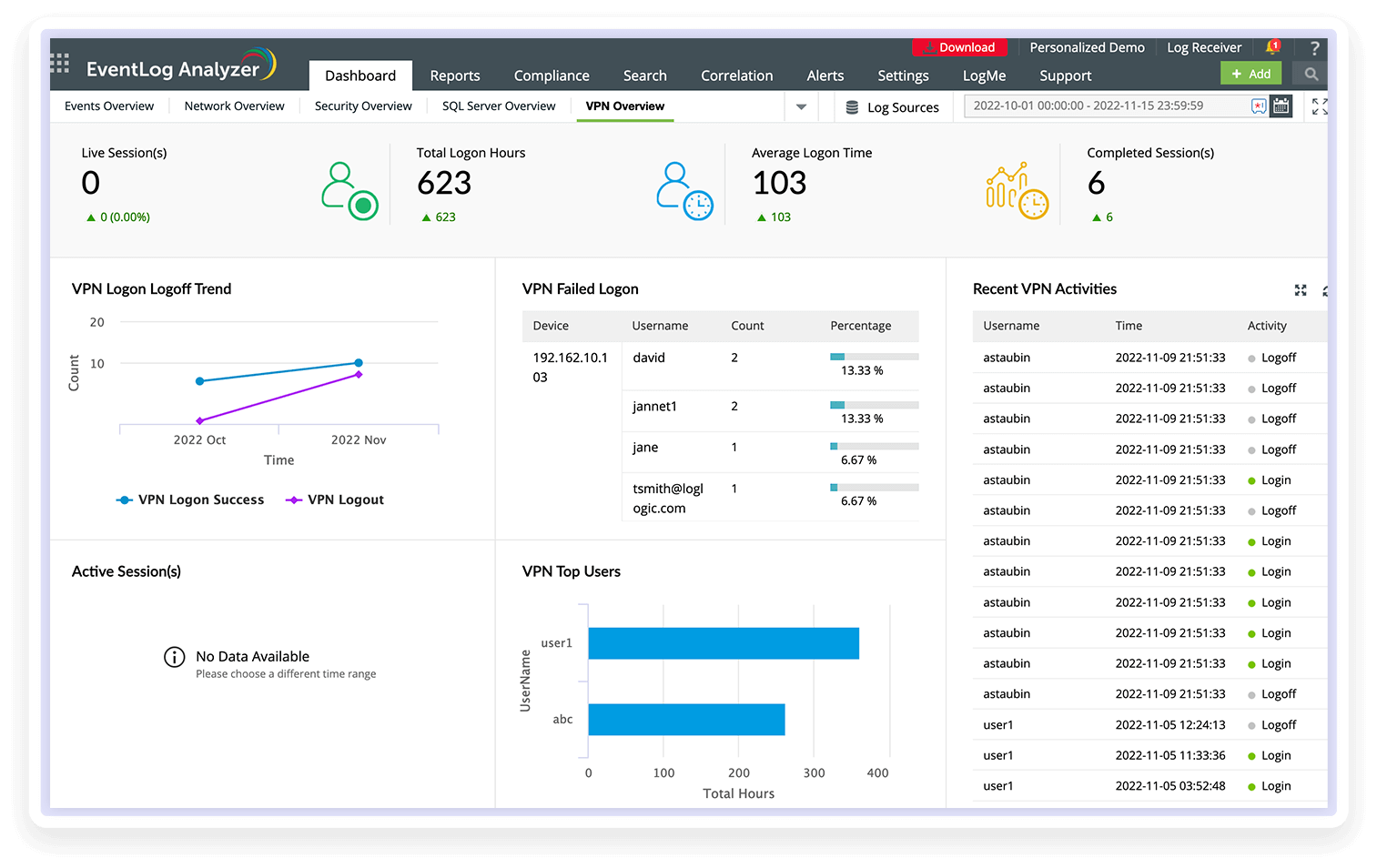
Stay informed about network VPN logins and monitor VPN traffic in real time with EventLog Analyzer's VPN reports. You can also keep track of users who have logged in through a VPN, including the private IP addresses assigned to them. EventLog Analyzer provides complete VPN login monitoring for SonicWall VPN devices. View reports on successful and failed logins, VPN logoffs, and the top logins classified by source, device, and user. The trend reports offer extensive insights through visually intuitive graphs and charts, significantly elevating data visualization for effortless analysis.
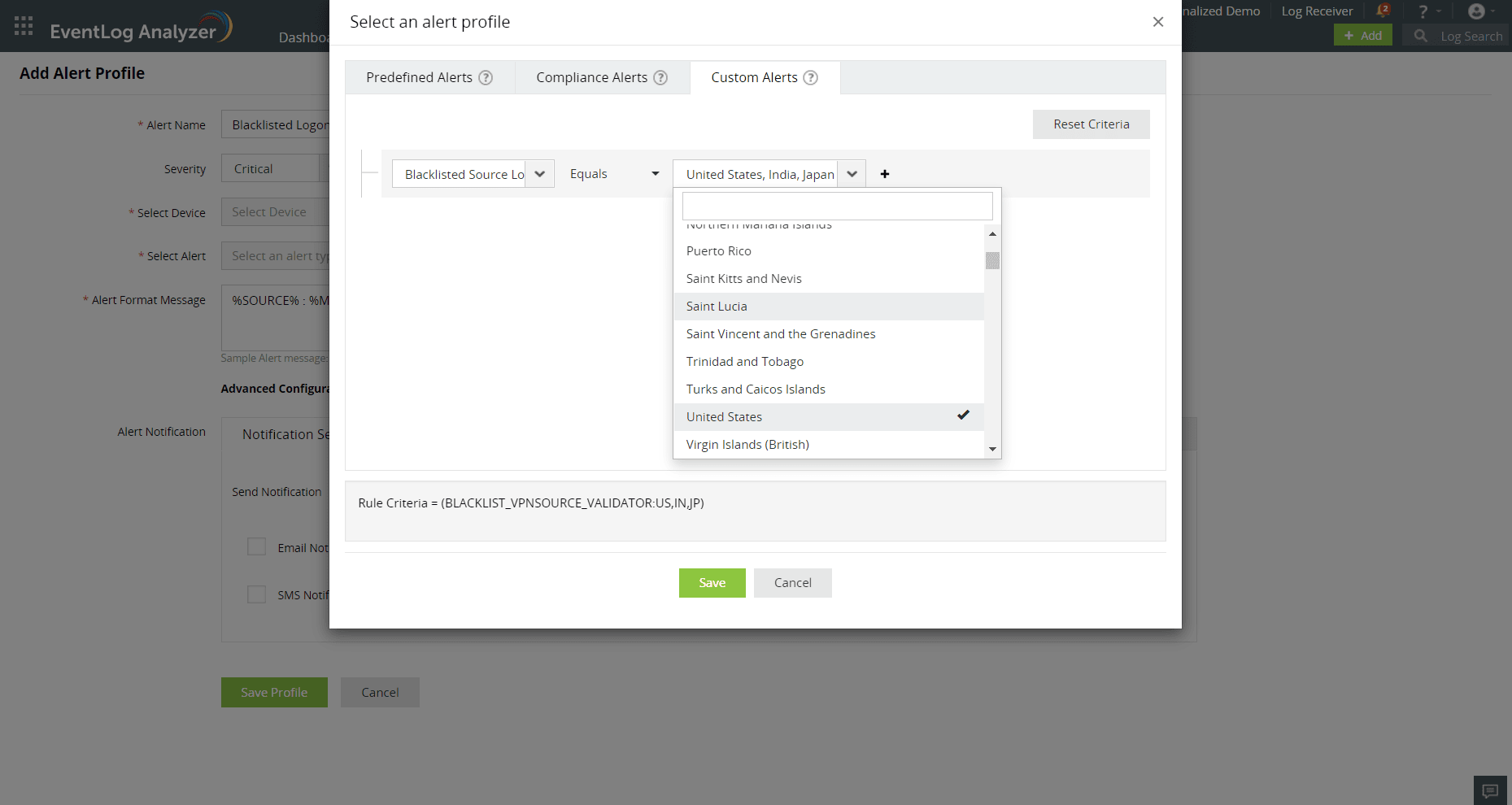
EventLog Analyzer automatically collects logs from VPN devices and generates out-of-the-box reports and alerts for Cisco ASA, SonicWall, Fortinet, Huawei, Sophos, and Meraki devices. You can get a comprehensive overview of your VPN traffic and latency metrics with the help of the solutions centralized dashboard. The solution also offers location based VPN logon monitoring:
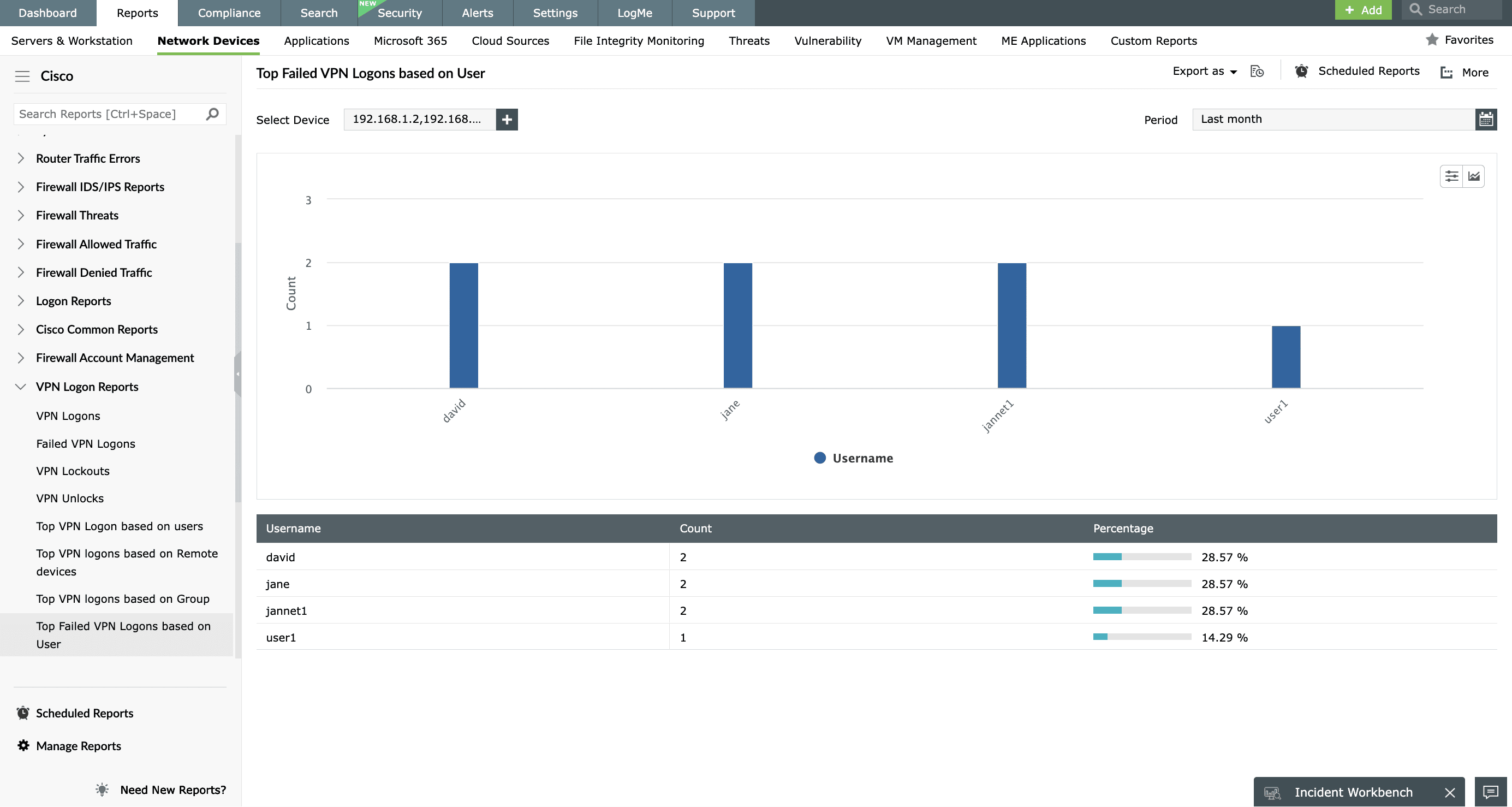
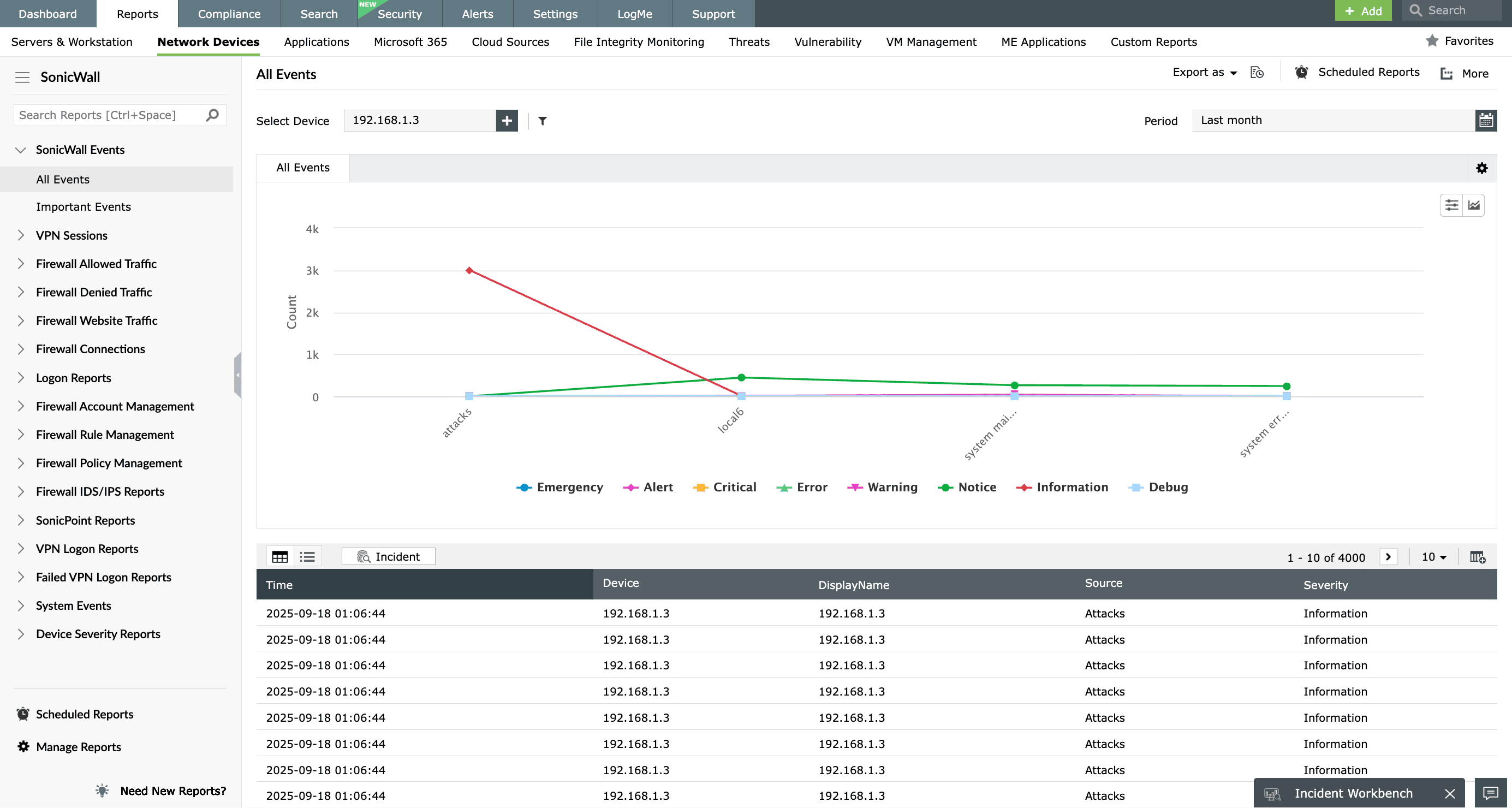
EventLog Analyzer helps analyze Cisco ASA VPN logs, enabling a comprehensive review of VPN user activities. Its functionality extends to auditing VPN logins and discovering patterns in login behavior, offering critical insights into network anomalies and unauthorized access through VPN connections.
EventLog Analyzer provides intuitive VPN reports for Cisco ASA VPN logs, including:
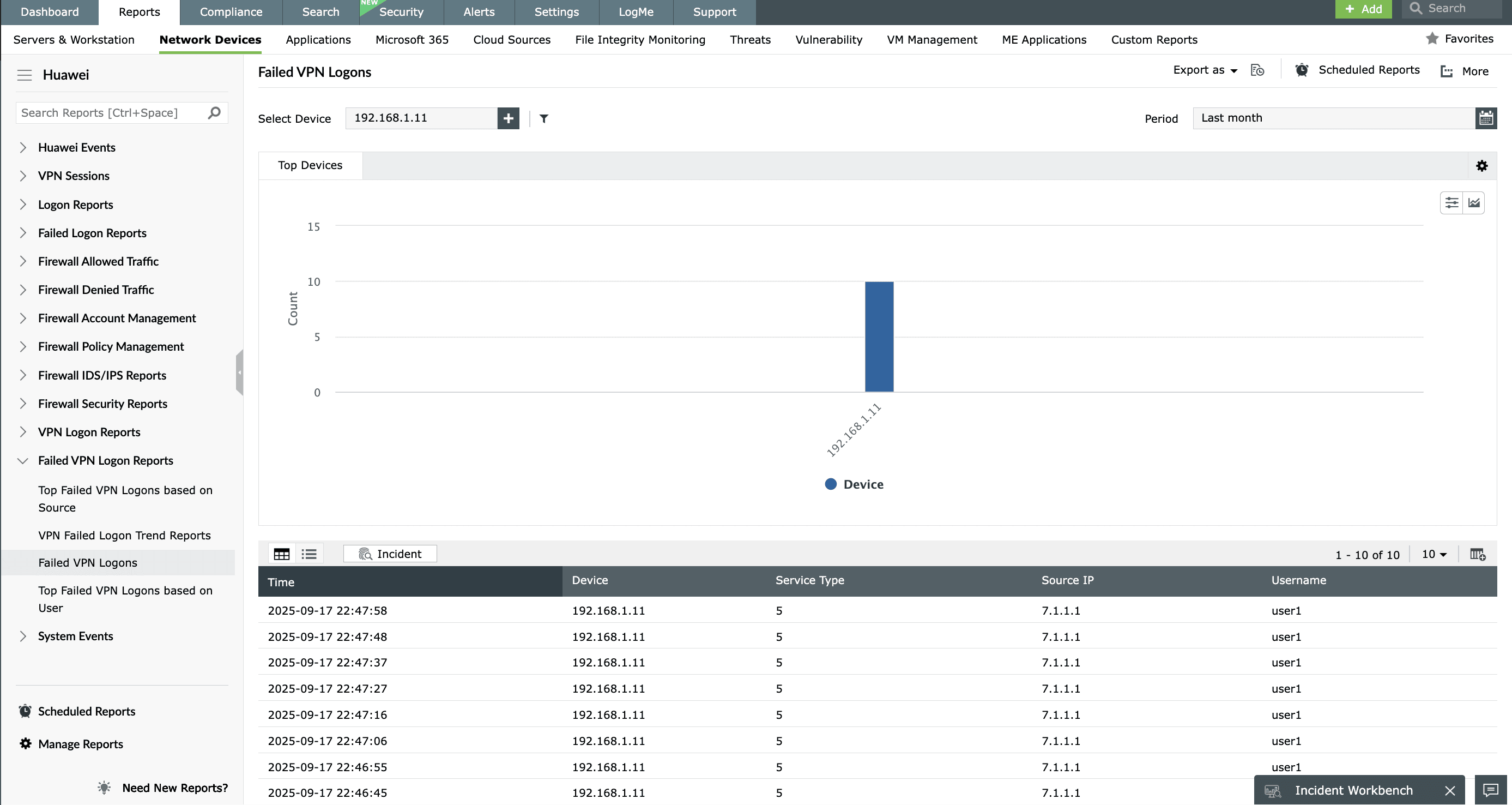
EventLog Analyzer keeps track of VPN connections established within your network. You can view details on the private IPs that get allocated most frequently, users who often use VPNs to get private IPs, remote IPs that often access the network, and much more. EventLog Analyzer comes with out-of-the-box VPN reports that get generated based on the VPN logs from Huawei firewall devices. The successful and failed VPN logon trend reports help identify anomalous activities, and patterns of successful and failed logon attempts over time.
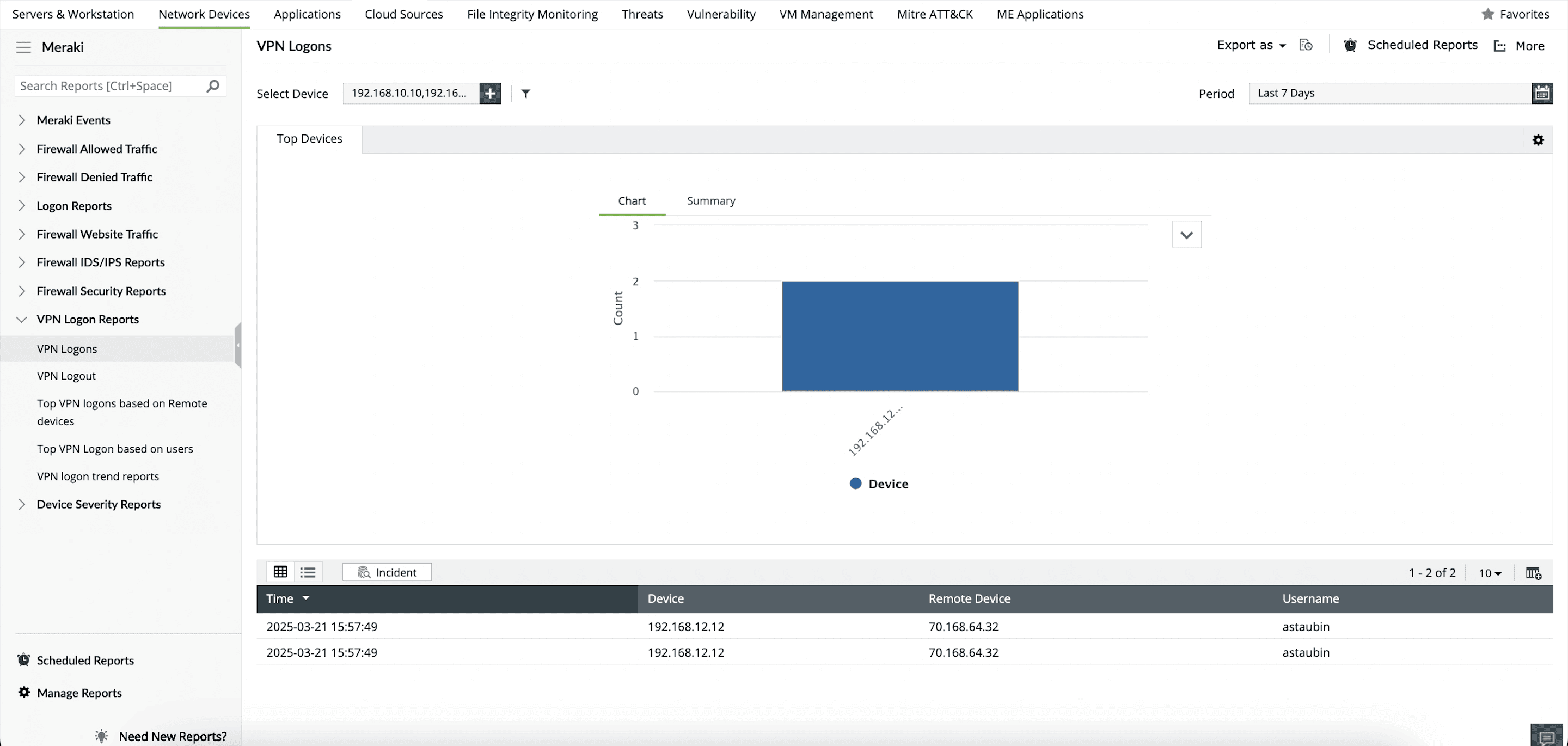
EventLog Analyzer's prebuilt reports for Meraki VPN provide comprehensive information on the most important aspect of VPN logons. There are exclusive reports for successful logons categorized based on devices and users. The trend report helps you understand the VPN logon trends in your network. You can customize reports by applying filters and drill down to raw log information straight from the reports. You can also export or schedule reports at your convenience, and set up email and SMS alerts as required.
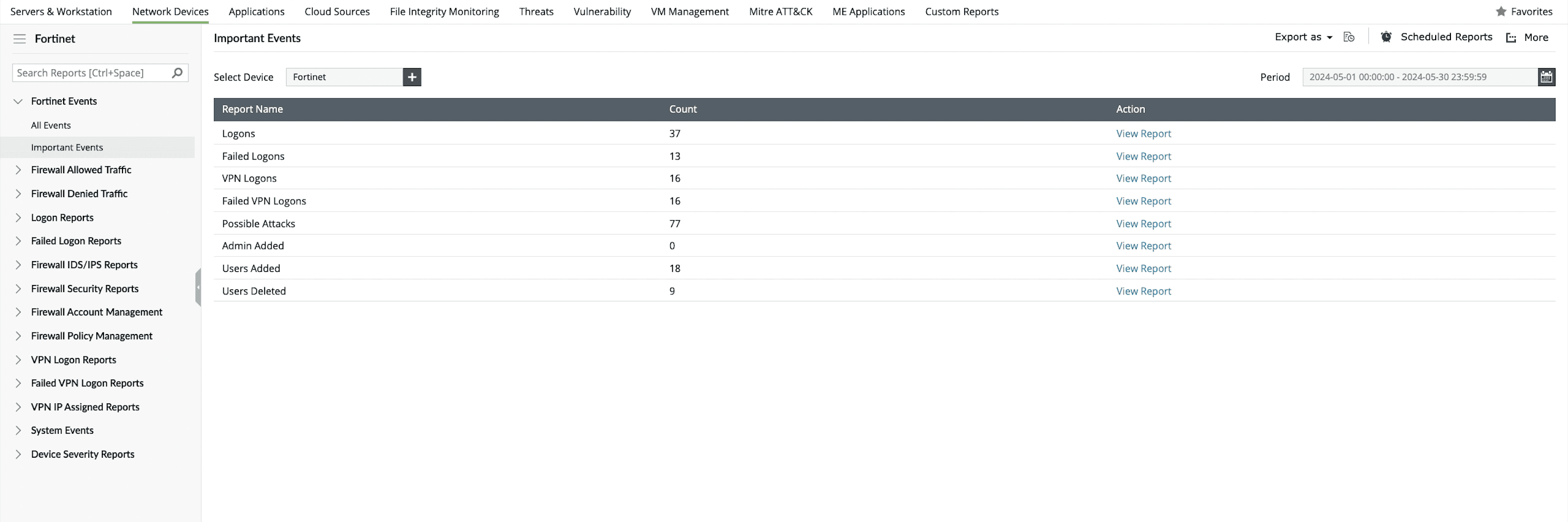
EventLog Analyzer serves as a valuable tool for monitoring VPN logs, ensuring that only authorized users gain access to your network, and fortifying your network security. Fortinet VPN reports provide information on successful and failed VPN logins. The top reports sort logins by device used and VPN user, so you can identify the users and devices that most frequently connect to your organization's VPN. The trend reports are useful in studying Fortinet VPN login patterns.
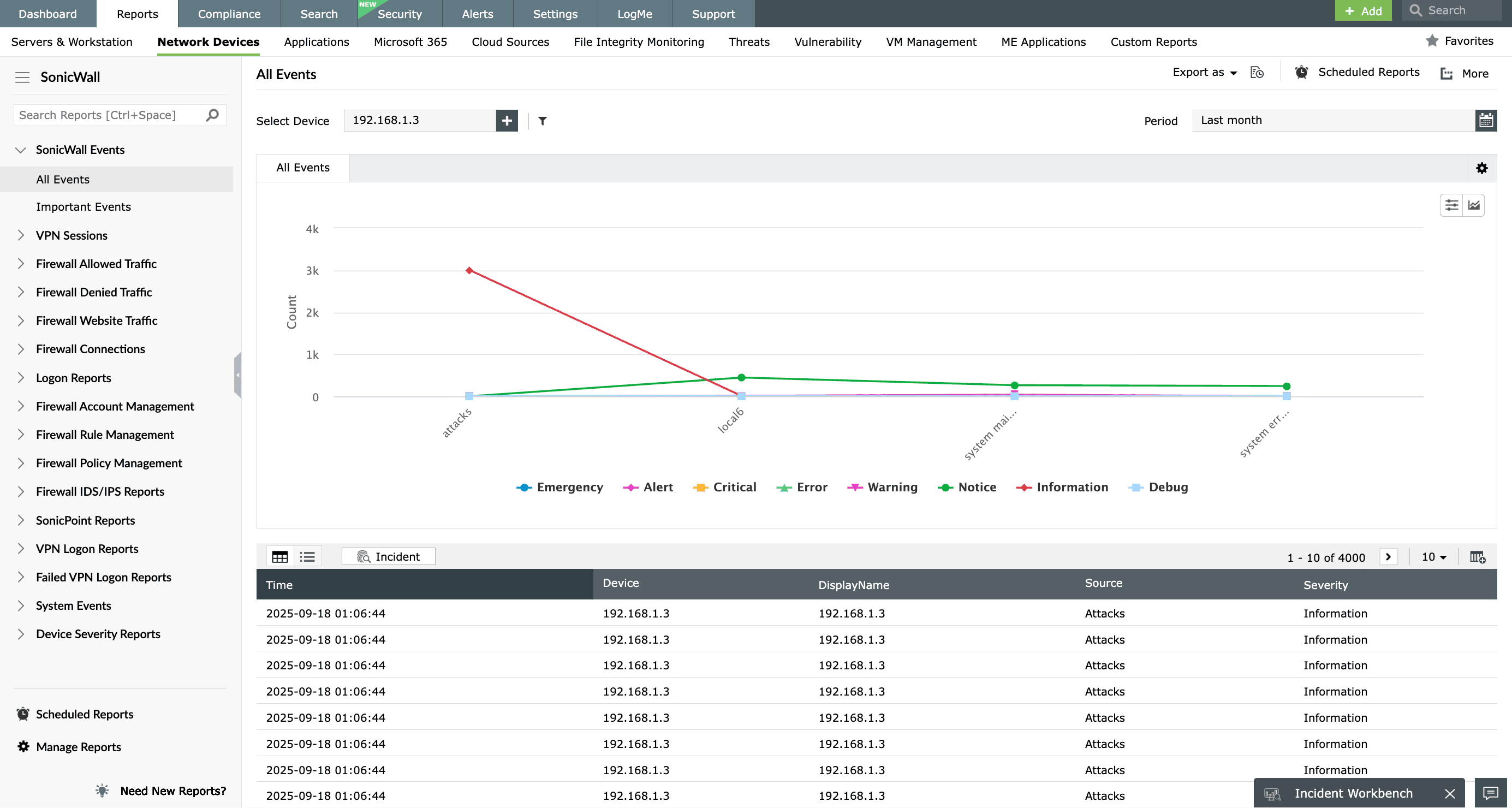
Stay informed about network VPN logins and monitor VPN traffic in real time with EventLog Analyzer's VPN reports. You can also keep track of users who have logged in through a VPN, including the private IP addresses assigned to them. EventLog Analyzer provides complete VPN login monitoring for SonicWall VPN devices. View reports on successful and failed logins, VPN logoffs, and the top logins classified by source, device, and user. The trend reports offer extensive insights through visually intuitive graphs and charts, significantly elevating data visualization for effortless analysis.
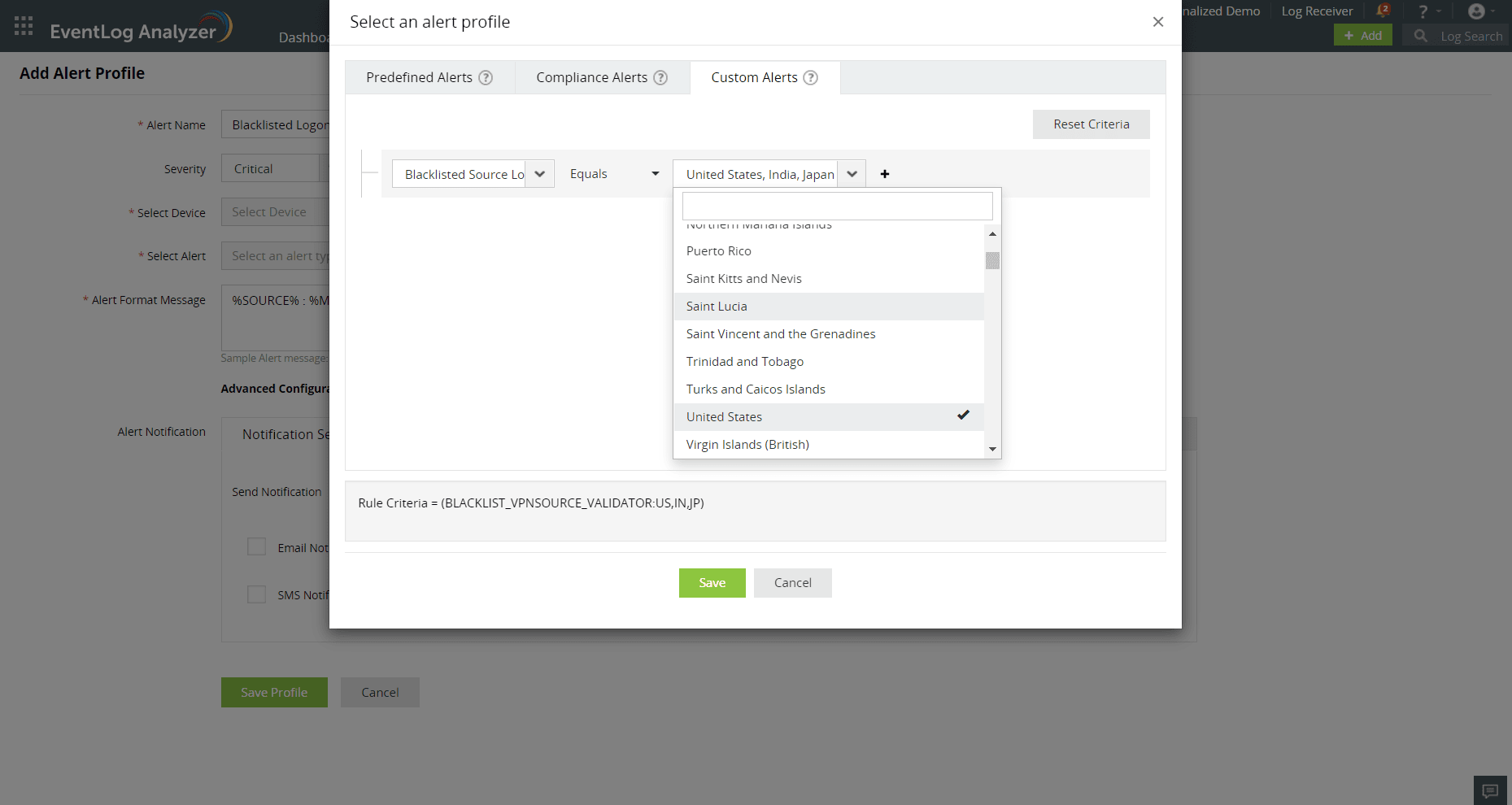
EventLog Analyzer automatically collects logs from VPN devices and generates out-of-the-box reports and alerts for Cisco ASA, SonicWall, Fortinet, Huawei, Sophos, and Meraki devices. You can get a comprehensive overview of your VPN traffic and latency metrics with the help of the solutions centralized dashboard. The solution also offers location based VPN logon monitoring:
Monitor IDS/IPS activities to proactively thwart malicious network traffic and generate real-time alerts when such activity is detected.
Analyze SNMP traps based on severity level, to swiftly detect problems, troubleshoot network issues effectively, and identify potential security threats.
Audit database server logs for MS SQL, MySQL, and Oracle to prevent unauthorized access, monitor account changes, and detect suspicious backup activities.
Monitor web applications like Apache, IIS, and DHCP logs and receive alerts on server usage, errors, and any attack attempts.
Easily comprehend what's happening with your VPN, spot patterns, and find possible security issues using visual charts and graphs.
Enhance your network security by monitoring remote users through VPN logs and accurately detect anomalies.
Gain insights into user activity and behavior within the VPN, helping you detect unauthorized access, data breaches, or insider threats.
Trigger alerts in response to repeated failed VPN login attempts from a single source or if login occurs from unusual locations.
VPN logs are records generated by VPN devices that tracks your user connections, authentication, session duration, traffic, errors, and security events. Network-to-network VPNs use certificates, while client-to-network VPNs use user authentication like usernames and passwords. VPNs use protocols like Internet Protocol Security (IPSec), OpenVPN with secure sockets layer (SSL), or Layer 2 Tunneling Protocol (L2TP) for encryption. VPN log plays a vital role in monitoring network activity, troubleshooting issues, and ensuring compliance with regulations.
VPN monitoring involves continuous tracking of firewalls and VPN devices to ensure private networks are secure from hackers. It also involves scrutinizing their availability, health, performance, and latency. Through vigilant monitoring of VPN traffic, you can ensure that data sent across your network remains encrypted and is swiftly transmitted. It also involves identifying major resource users and monitoring bandwidth usage.
Monitoring VPN logs is crucial for user analysis, situational awareness, foreign IP monitoring, and compliance. You can easily track any suspicious activity and optimize your network traffic with VPN log monitoring.
EventLog Analyzer serves as a robust VPN logging tool that offers out-of-the-box support for a wide range of VPN devices, facilitating real-time monitoring, alerting, and reporting. Its customizable features and comprehensive analysis capabilities empower you to enhance your network security, meet compliance requirements, and maintain the integrity of your VPN infrastructure.
EventLog Analyzer as a VPN log monitoring tool helps you: