Configuring firewall rules with ManageEngine Firewall Analyzer
Firewalls form the front line of defense in securing networks from attacks. Firewalls hold absolute control over the traffic between the internet and the company's IT network. The firewall rules' configurations handle the critical task of regulating traffic.
The rules closely scrutinize the incoming and outgoing traffic and allows or blocks it depending on the conditions mentioned in the rules. The more strict the firewall rules are, the stronger the network. Security administration teams should ensure that they configure firewall rules optimally.
Firewall rule configuration challenges faced by security teams
When the firewall is deployed for the first time, Block All should be the default setting. The Allow criteria should be made incrementally. The team may follow a checklist for Allow criteria.
Making changes to the firewall rule configuration for an already deployed firewall can be a tricky. The task will be challenging even for an experienced administrator, especially if performed manually. The challenges are:
- Taking stock of the existing rules.
- Finding the anomaly amongst the rules.
- Removing rule anomalies.
- Cleaning up the unused rules.
- Analyzing the impact of new rules over existing rules.
- Maintaining an error-free workflow when adding or modifying rules.
Firewall Analyzer addresses firewall rule configuration challenges effectively
Firewall Analyzer can tackle all your firewall rule configuration challenges. It provides clear workflows for carrying out rule configuration tasks.
- Fetches all the rules from the firewall devices.
- Analyzes the fetched rules for anomalies.
- Suggests rule re-order to remove rule anomalies.
- Suggests pruning of unused rules.
- Analyzes the impact of new rules over existing rules
- Provides a workflow with review controls for administering firewall rules.
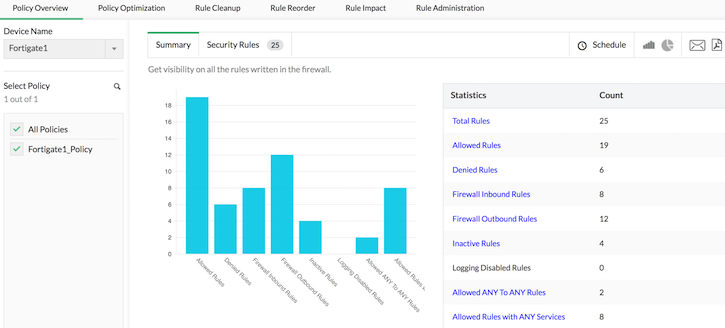
Firewall Policy Overview
Firewall Analyzer fetches all the rules from firewall devices. Of course, you have to configure the device credentials. It generates the policy overview report and categorizes the available rules in to allowed, denied, overly permissive, inbound, outbound, and more.
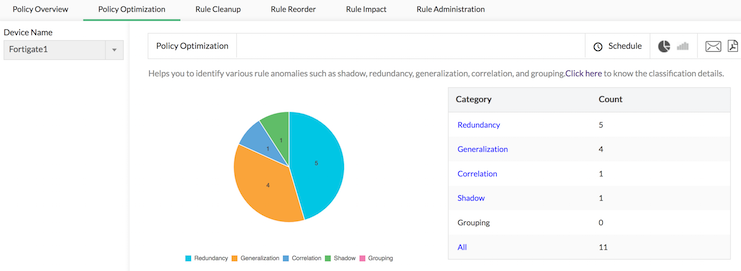
Firewall rule optimization
Firewall Analyzer analyzes the rules to find out the anomaly between rules. It generates an anomaly-based rules report. With this report, you can remove the anomalies between rules by pruning unused rules and reordering the rules as suggested.
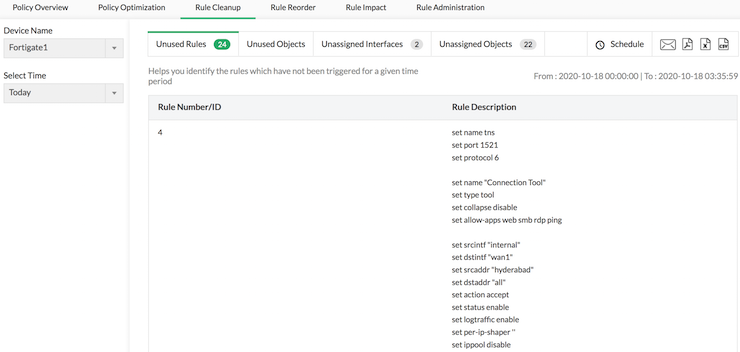
Firewall Rule Cleanup
In this report, you will see the unused rules sitting idle in the rule set. These can turn potentially dangerous if an attacker finds them. You can then focus on removing the unused rules listed in the report.
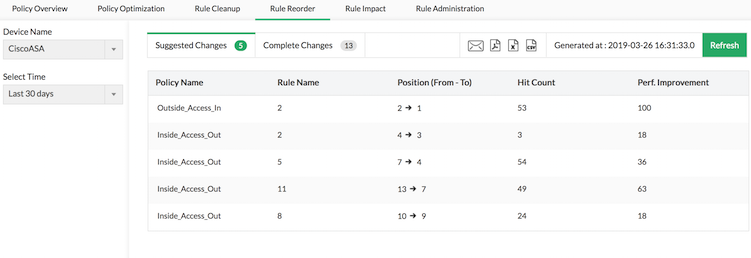
Firewall Rule Reorder
Another technique to remove rule anomaly is to reorder the rules in the rule set. Firewall Analyzer analyzes the anomaly and generates a report suggesting reorder rules in the list. You can use this and change the order of the firewall rules.
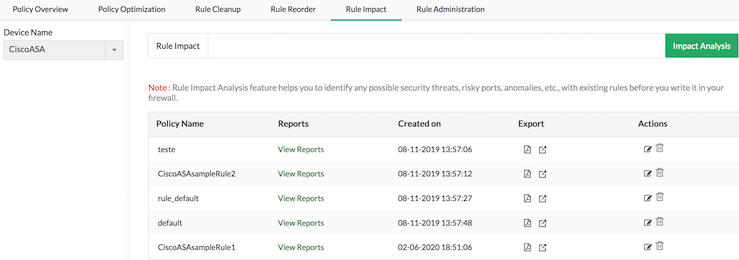
Firewall Rule Impact Analysis
When you try to add a new rule to a firewall device, you have to ensure that the new rule being added does not impact the existing rules adversely. Adding a rule that has an adverse impact on another rule can make the rule set weak, jeopardizing network security. After learning the impact, make the necessary changes and analyze the impact once again. Using this process, you can prevent adverse impacts of new rules.
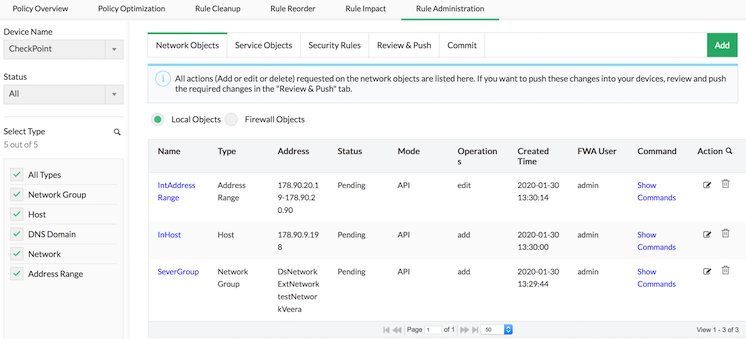
Firewall Rule Administration
When the rule is pushed to the firewall device, the workflow should ensure that the rule is fully pushed and doesn't fail to push to the device. Rules should also offer supervisory review control, so that rules are not pushed by mistake.
Firewall Analyzer's Rule Administration tab does this job. It allows you to add new rules or modify existing rules. New and existing rules are kept in Firewall Analyzer's cache, allowing you to make changes locally before pushing them to devices. After thoroughly checking the effectiveness of the rule, carrying out impact analysis, and reviewing it, you can effortlessly push the rules to firewall devices.
To summarize, Firewall Analyzer simplifies firewall policy management, helps automate the process of configuring firewall rules, and enables security administrators to stick to firewall rule best practices.
Download a free trial of Firewall Analyzer today, and get the most out of your firewall.
Featured links
Firewall Reports
Get a slew of security and traffic reports to asses the network security posture. Analyze the reports and take measures to prevent future security incidents. Monitor the Internet usage of enterprise users.
Firewall Compliance Management
Integrated compliance management system automates your firewall compliance audits. Ready made reports available for the major regulatory mandates such as PCI-DSS, ISO 27001, NIST, NERC-CIP, and SANS.
Firewall Log Management
Unlock the wealth of network security information hidden in the firewall logs. Analyze the logs to find the security threats faced by the network. Also, get the Internet traffic pattern for capacity planning.
Real-time Bandwidth Monitoring
With live bandwidth monitoring, you can identify the abnormal sudden shhot up of bandwidth use. Take remedial measures to contain the sudden surge in bandwidth consumption.
Firewall Alerts
Take instant remedial actions, when you get notified in real-time for network security incidents. Check and restrict Internet usage if banwidth exceeds specified threshold.
Manage Firewall Service
MSSPs can host multiple tenants, with exclusive segmented and secured access to their respective data. Scalable to address their needs. Manages firewalls deployed around the globe.