Firewall Policy Overview
Firewall policies/rules control the traffic between the LAN and the Internet. The critical part is to monitor and manage the firewall filter rules judiciously so that the normal business traffic flows smoothly and any anomalous traffic is blocked/prevented.
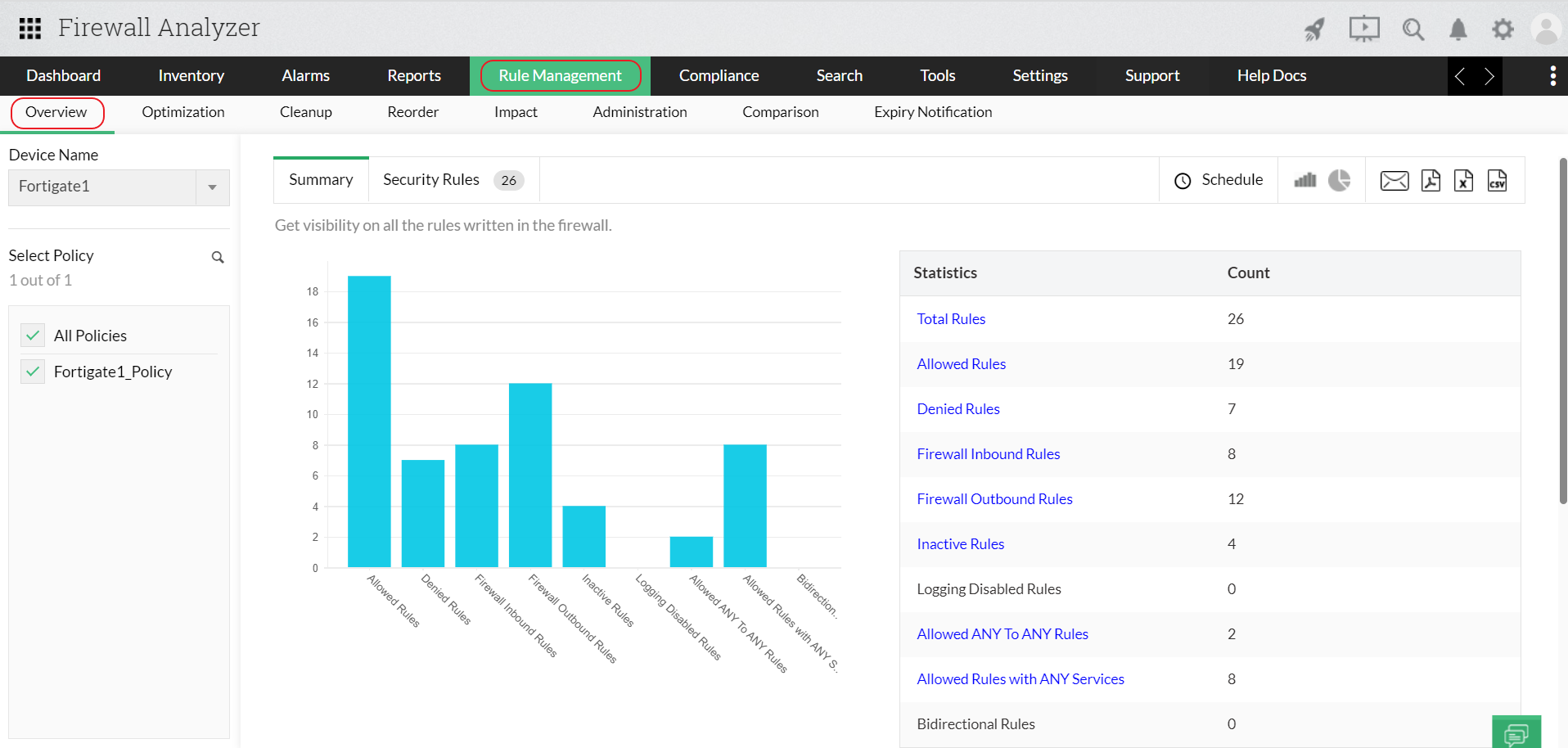
To get a snapshot of rules controlling the traffic flow through the firewall, you need a firewall policy overview report (firewall monitoring policy). Firewall Analyzer, a firewall policy analysis tool, provides the firewall policy overview report. This firewall policy planning report provides a high level picture of allowed and denied rules. The report can be drilled to get the traffic details for each firewall filter rule. The report provides firewall policy rules details. They are, rule name, source, destination, source interface, destination interface, the services using the rule and more.
With this firewall policy anlayzer, you can also filter the report (firewall filter rules) progressively to narrow down the rule details search.
Refer Configure Firewall Rules page to know how to configure firewall rules.
Request for a personalized demo
Featured links
Firewall Reports
Get a slew of security and traffic reports to asses the network security posture. Analyze the reports and take measures to prevent future security incidents. Monitor the Internet usage of enterprise users.
Firewall Compliance Management
Integrated compliance management system automates your firewall compliance audits. Ready made reports available for the major regulatory mandates such as PCI-DSS, ISO 27001, NIST, NERC-CIP, and SANS.
Firewall Log Management
Unlock the wealth of network security information hidden in the firewall logs. Analyze the logs to find the security threats faced by the network. Also, get the Internet traffic pattern for capacity planning.
Real-time Bandwidth Monitoring
With live bandwidth monitoring, you can identify the abnormal sudden shhot up of bandwidth use. Take remedial measures to contain the sudden surge in bandwidth consumption.
Firewall Alerts
Take instant remedial actions, when you get notified in real-time for network security incidents. Check and restrict Internet usage if banwidth exceeds specified threshold.
Manage Firewall Service
MSSPs can host multiple tenants, with exclusive segmented and secured access to their respective data. Scalable to address their needs. Manages firewalls deployed around the globe.