Your BYOD plan - savior or security threat?
Nearly 60 percent of businesses allow employees to bring their own devices, but only 39 percent have a BYOD policy in place.
Expanding your mobility horizon
BYOD=smartphones. Smartphones can take your business to new heights or be the security threat you've been dreading, depending on how you play your cards. With so many cons, you might be wondering if it's even worth bringing up a BYOD policy. Take it from us, it's worth the hassle. Like it or not, BYOD is here to stay. If you're running a small or medium-sized business, your tight budget probably limits you from spending large amounts on company-issued devices. This is where BYOD (if executed properly) can benefit you.
BYOD can save your company nearly $350 per employee, per year. And it's not just about cutting costs. It's about increasing efficiency and keeping employees happy. BYOD increases employee productivity by aligning with existing behavior.
Workplace flexibility inevitably results in job satisfaction. Using their own devices instead of learning how to use a new one saves time and is more convenient. Employees love the ease of working, and employers love the money they save. So jump on the wagon and get ahead of it while you can! The solution is in your hand (literally).
For any device management plan to work, you need a multifaceted approach. There are three key areas that need attention:
- A system to make it work
- A crew behind the scenes
- A team that plays by the rules
Erasing micromanagement from the top
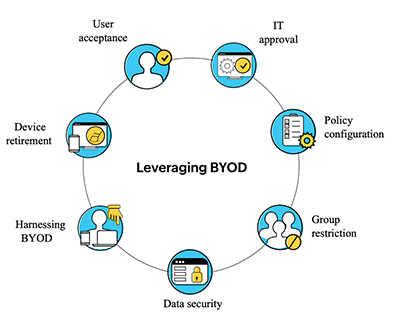
Nearly 60 percent of employees worldwide use personal phones for work-related tasks, and about 90 percent of them continue to do so after work hours. With these numbers, it's no surprise that BYOD has cemented its existence in the workplace. Instead of fighting BYOD, welcome the change—with a set of rules. Before creating a framework, assess the situation and evaluate your needs. A BYOD policy outlines critical security considerations, such as the type of devices that are sanctioned by the organization, the data that can be accessed, and the employees who will be accessing corporate information from these devices. The success of the BYOD trend in an organization completely depends on how the BYOD policy is designed and implemented. In our white paper Leveraging BYOD, we discussed some of these areas of consideration.
Frameworks such as COBIT 5, ISO 27001, NIST 1, or ENISA 2, regarded as general cybersecurity frameworks, are popular among many organizations worldwide. However, case studies reveal that COBIT 5 and ISO 27001 don't directly address BYOD security concerns. NIST 1 and ENISA 2 explicitly address BYOD security. To ensure harmony, choose a protocol that meets all your requirements.
Without a clear set of rules, employees are faced with ambiguity. A strong policy makes the do’s and don'ts of using their own devices at work abundantly clear for employees. Who pays for what? What information can employees access? What happens if a device is lost or stolen? Is personal information monitored? Answering these important questions can liberate users from little challenges that hold them back.
The M-team
The mobility team. The unsung heroes of the IT department, holding down the fort rain or shine. At Zoho Corp, the Sysadmin team handles all internal activities and takes measures to prevent incidents. They work around the clock to provide support to employees around the world. We also have a smaller support team in the US. A team of 50 managing the devices of over 9,000 employees is no small feat. It’s safe to say our endpoint strategy is tried, tested, and triumphant! How do we pull it off?
During a Q&A session with author Nora Roberts, a reader asked, "How do you balance writing and kids?" She said that the key to juggling is to know that some of the balls you have in the air are made of plastic and some are made of glass. If you drop a plastic ball, it bounces, no harm done. If you drop a glass ball, it shatters. So you have to know which balls are glass and which are plastic and prioritize catching the glass ones. This can be applied to almost every aspect of life, including device management.
To make things easier, our Sysadmin team uses a priority matrix. It helps us weigh different factors and assign tasks to Sysadmin agents. A priority matrix can categorize tasks based on impact and urgency. System administrators can design a matrix that works best for them.
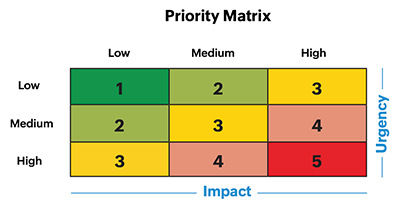
A request may affect the functioning of an organization, a department, a group, or an individual. Can you afford to delay a user maintenance request? Yes. But a software update? Or deploying a patch? Those are glass balls. The Sysadmin team gets hundreds of tickets every day, and it's impossible to attend to all of them immediately. Knowing how to prioritize tasks can be a game-changer. We opted to integrate our help desk with endpoint management to allow employees to raise requests.
Risk management
another key concept in device management, follows a similar structure. The idea of addressing troubles as they arise is divorced from reality and will leave you constantly putting out small fires. If you're lucky, you escape. Risk management shields your organization from data loss and cyberattacks and reduces operational costs. It's also a big time saver. Having proof of compliance will make your life easier during audits.
Stages of risk management
Your risk management strategy can be flexible and include as many stages as required to make sure you've covered all the bases. A standard plan often contains five stages:
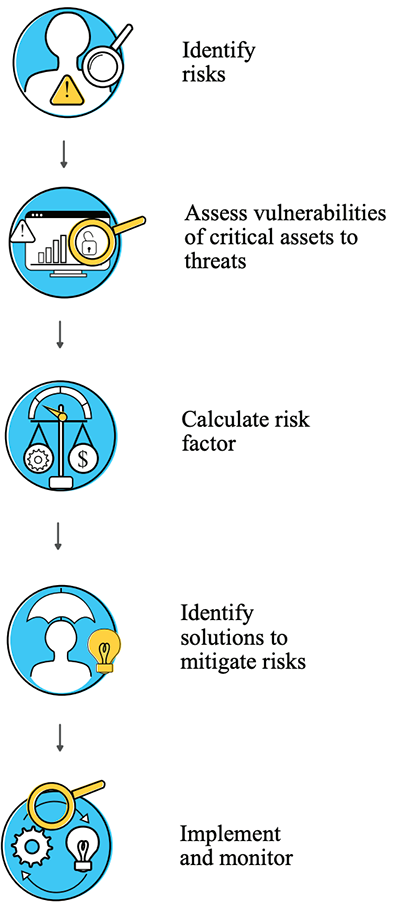
1. Identify risks
How can you be affected? How can an intruder get into sensitive corporate data? Identify potential risks and analyze the likelihood of it occurring within your organization. This is one of the few places where pessimistic thinking may actually work in your favor. Professional red teams are constantly trying to figure out loopholes and gaps in device security that they can take advantage of.
Risks can be identified from any of these factors:
- Threats and vulnerabilities identified from external or internal sources
- Internal or external issues
- Requirements of interested parties
- Assets
- Incidents
Some common threats associated with devices include malicious software, gaining access to a device that has been lost or stolen, negative end-user behavior like jailbreaking, and corporate data leakage. ManageEngine uses a data security tool to monitor risks, which is strongly recommended to keep stakeholders in the loop.
2. Assess vulnerabilities
What's at stake? Determine what can be classified as an asset and how it can be used by adversaries. Assets may be physical, digital, or even people. In our case, a physical asset is the device itself; a digital asset is the information in it; and the asset can also be the device owner or a sysadmin. An asset valuation scale determines the importance of each asset and its impact on the functioning of the organization in terms of confidentiality, integrity, and availability. Vulnerabilities can be exposed by anything from APIs to Bluetooth. Data can be transmitted over Wi-Fi, or files can be accessed when using third-party apps. Identify these vulnerabilities associated with assets and evaluate the ease with which they can be exploited.
3. Calculate risk
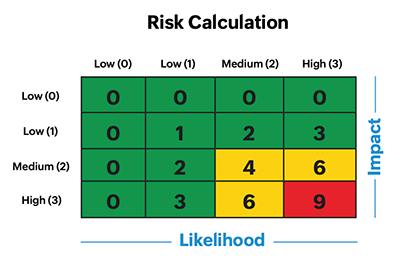
How bad is it? In our book How Zoho Corp handles natural disasters and does business as usual, we discussed in detail the criteria an incident needs to meet to be categorized as a risk and how risk is calculated.
4. Identify solutions
How do we fix it? There are many ways to mitigate risks. Based on the situation, pick a path that best addresses its needs and will reduce the likelihood of these unpleasant surprises.
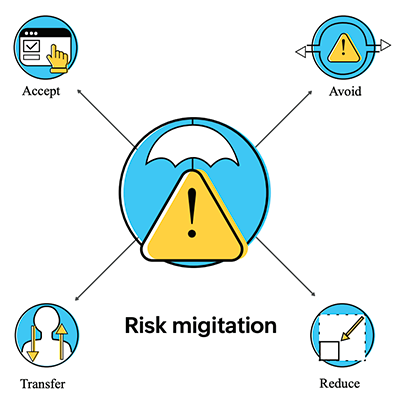
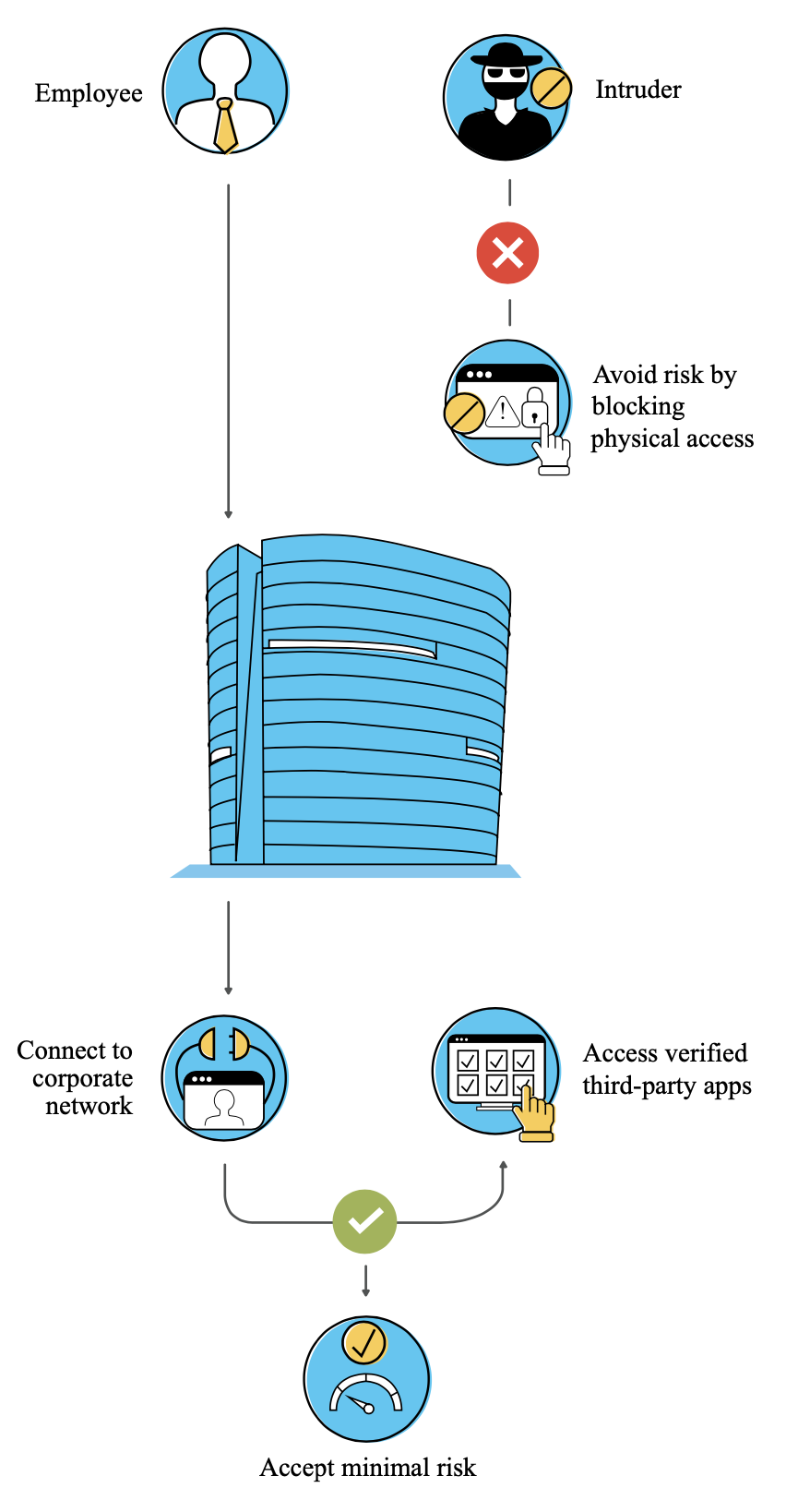
Risk acceptance:
Also known as risk retention, it simply refers to an organization's ability to accept risks. Risks are identified but no action is taken to reduce the said risk due to its minimal impact. For example, not being able to issue a device for new employees during the pandemic is a problem, but it has minimal risks. The organization limited the procurement period and issued devices as soon as possible. Based on the risk rating, the severity of the risks is categorized as LOW (0 to 3), MEDIUM (4 to 6), and HIGH (7 to 9). Zoho's risk acceptance criteria is LOW (0 to 3).
Risk avoidance
When you decide to terminate an activity that leads to risk, you can choose risk avoidance or termination. Establishing policies that prevent any risk-causing activities even before they are initiated is one way of avoiding risk. For example, by making company-issued devices mandatory, we avoid the risk of having unknown devices within our network.
Risk transfer:
In some scenarios, you can transfer or share the risk with a third party. Sharing the burden often also means sharing control, especially if the risk is something your organization cannot take charge of. This can help reduce future damage. Take the example of insurance. Some organizations opt for corporate gadget insurance that covers accidental damage, theft, loss, and manufacturing defects.
Risk reduction
When the risk can be controlled by taking action, it is called risk reduction or modification. Businesses can assign a level at which risk is acceptable, which is called the residual risk level. Risk reduction is the most common strategy because there is usually a way to reduce risk. Root cause analysis plays a significant role here. If risk modification is chosen, we have to test and monitor the effectiveness of the implemented controls. We can then derive the revised risk score (i.e., the score calculated from the impact and likelihood after applying the control). Taking steps to facilitate secure application, like patch updates, and conducting periodic audits can warrant compliance in the workplace and minimize the threat of cyberattacks.
5. Implement and monitor
You cannot just implement a one-time solution and close the case. That's like putting a band-aid over a bullet hole. The trick is to make sure you're always prepared to tackle these risks and protect your organization. Repeating and continually monitoring the processes can help ensure maximum coverage of known and unknown risks. You avoid impulsive reactions and being in firefighting mode at all times to rectify problems that could have been anticipated. The result? Happy employees and customers, and a resilient organization.
So now you have policies that meet your requirements, and a framework to make it work. What's next? A well-structured Sysadmin team is the last piece of the puzzle. For all the parts to fit and make sense, you need to assign roles. When your Sysadmin team has clear responsibilities, there's no room for confusion. It allows them to tackle requests and tasks efficiently.
Role or team |
Responsibility |
Manager |
|
Leadership |
|
IT Services (24x7) |
Uses a shift-based system to respond to Level II and III requests like maintaining servers and application servers, monitoring services and alerts, and configuring backups |
Pit stop |
Responds to tickets submitted by employees Handles issues like configuring applications, troubleshooting applications and hardware, providing or upgrading laptops, OS re-installation, and licensing software |
IT Asset & Compliance |
Manages assets such as laptops, phones, monitors, and other peripherals Provisions devices to the Pit stop team based on employee requests |
Fostering a culture backed by tech
In 2019, human error was the cause of over 21 percent of data breaches in corporations.
"Culture eats strategy for breakfast." Does this mean strategy is not crucial? No. It means strategy is secondary. It means a rich and powerful culture paves the way for success in an organization. Before you use a product, it's important to take into account what the end user (in this case, employees of ManageEngine) might think. It's crucial to consider their feelings and not make them feel like the company is tracking them 24/7 or invading their privacy. We knew we needed to monitor devices while they were on our network. However, it wouldn't be right to access employees’ personal apps. An employee might be reluctant to have UEM on their device since features such as geolocation are active, and many may be reluctant to be followed on their free time or have their call history seen.
This is where containerization came in. Containerization aims to secure a portion of a device’s resources (for example, application, storage, or network access) from other applications and systems running on the same device. It ensures that enterprise data and an employee’s data are completely isolated from one another. The flow of data in and out of the container is prohibited, thereby securing corporate data and giving users complete control over their personal data. Win-win!
While we're discussing employees, remember that you're only as strong as your weakest link. A posh, high-tech, secure device management plan is meaningless if employees don't know the rules. Focus not just on the device but the person using it. Employees should be aware of company policies as well as laws pertaining to their clients and countries. ManageEngine has always put emphasis on being a privacy-first organization, eliminating third-party trackers and "backdoor deals." It is mandatory for employees to undergo privacy awareness training (PAT).
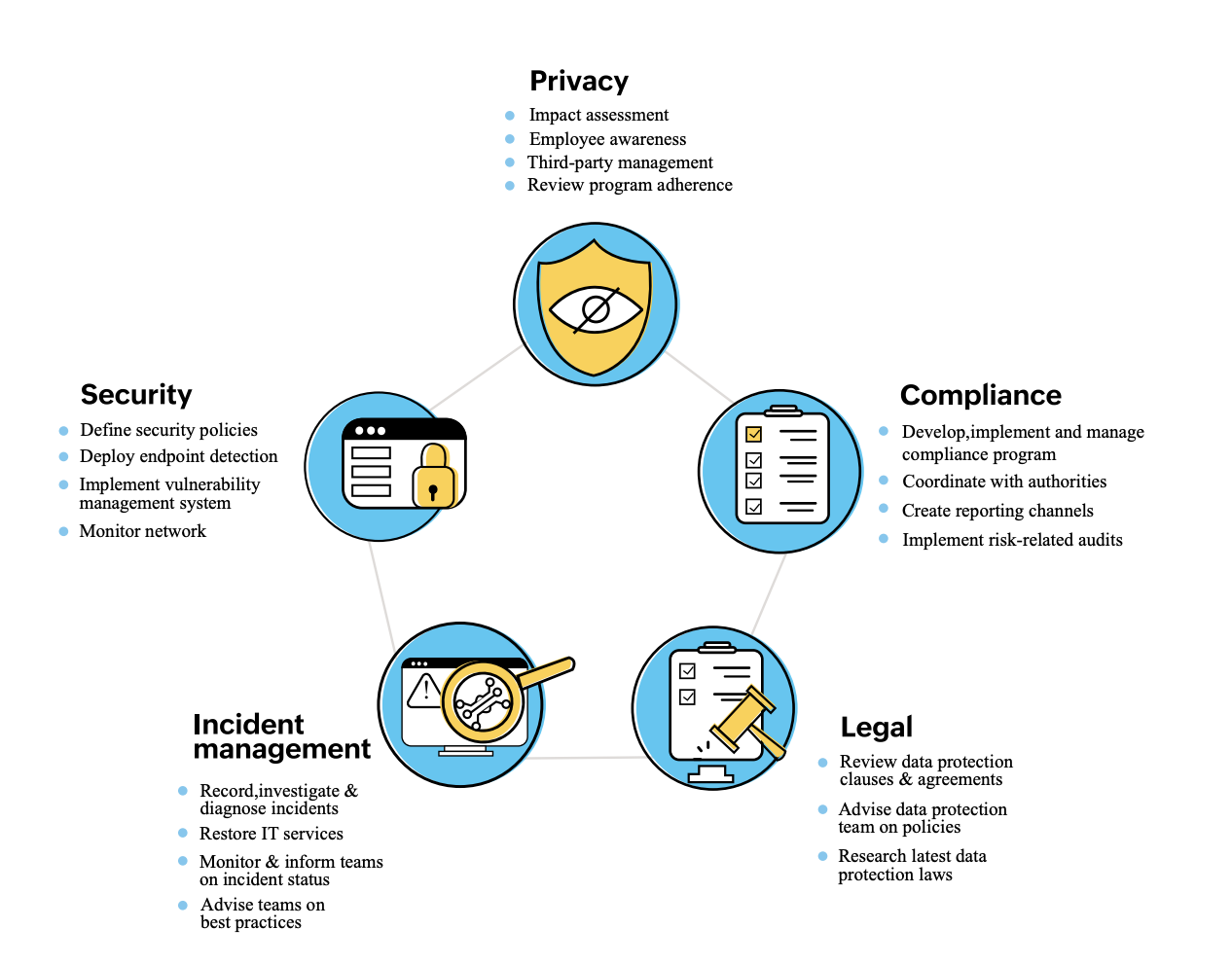
Every new employee gets #giveyourselfPAT and information security management system training to ensure they are aware of data protection practices and their responsibility towards them. This gives employees the information necessary to perform their duties without compromising the security and privacy of the organization. To reinforce the importance of data security and privacy, we also have an annual security and privacy awareness training session for all employees. Each session sheds light on the focal points of security: the what, why, where, and how. It takes a village to make sure an organization is prepared for any threats. At Zoho, we have five teams working hand in hand to stay on top of any risks.