Utilize the built-in threat intelligence platform to stop malicious external threats
An external threat refers to the risk of a company being exploited by an outside source using malware, worms, phishing emails, and stolen credentials. Primarily motivated by financial gain, external threat actors try to steal sensitive data residing inside a network and sell it on the dark web or use it bring down the business by launching ransomware or denial-of-service (DoS) attacks.
Log360 automatically scans the network for the indicators of compromise associated with external threats and activates the configured workflows to contain the threat at its initial stages. The solution’s built-in threat intelligence platform helps correlate threat feeds with network activities to effectively spot bad actors in the network premises.
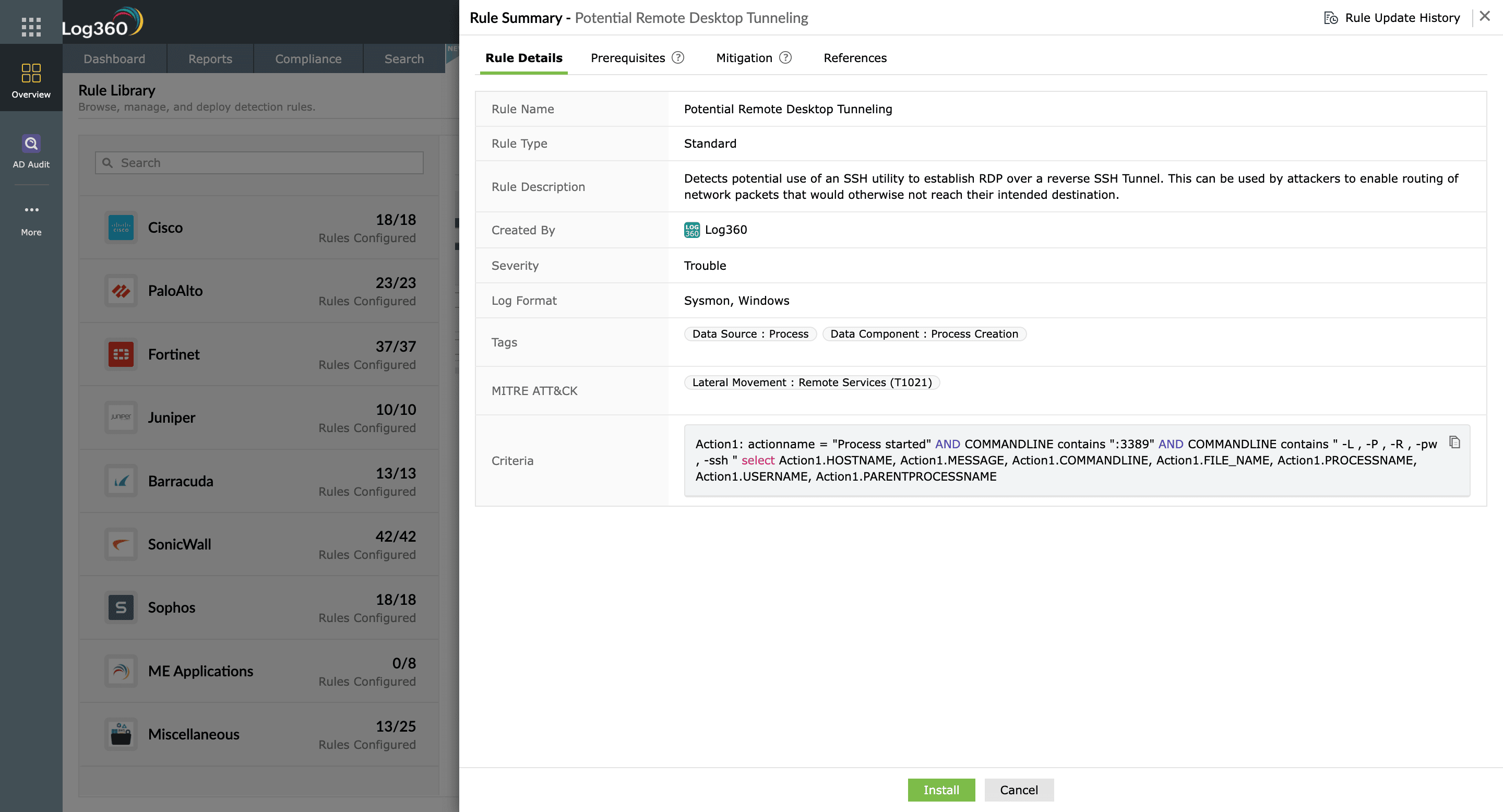
Stop public-facing resource exploits
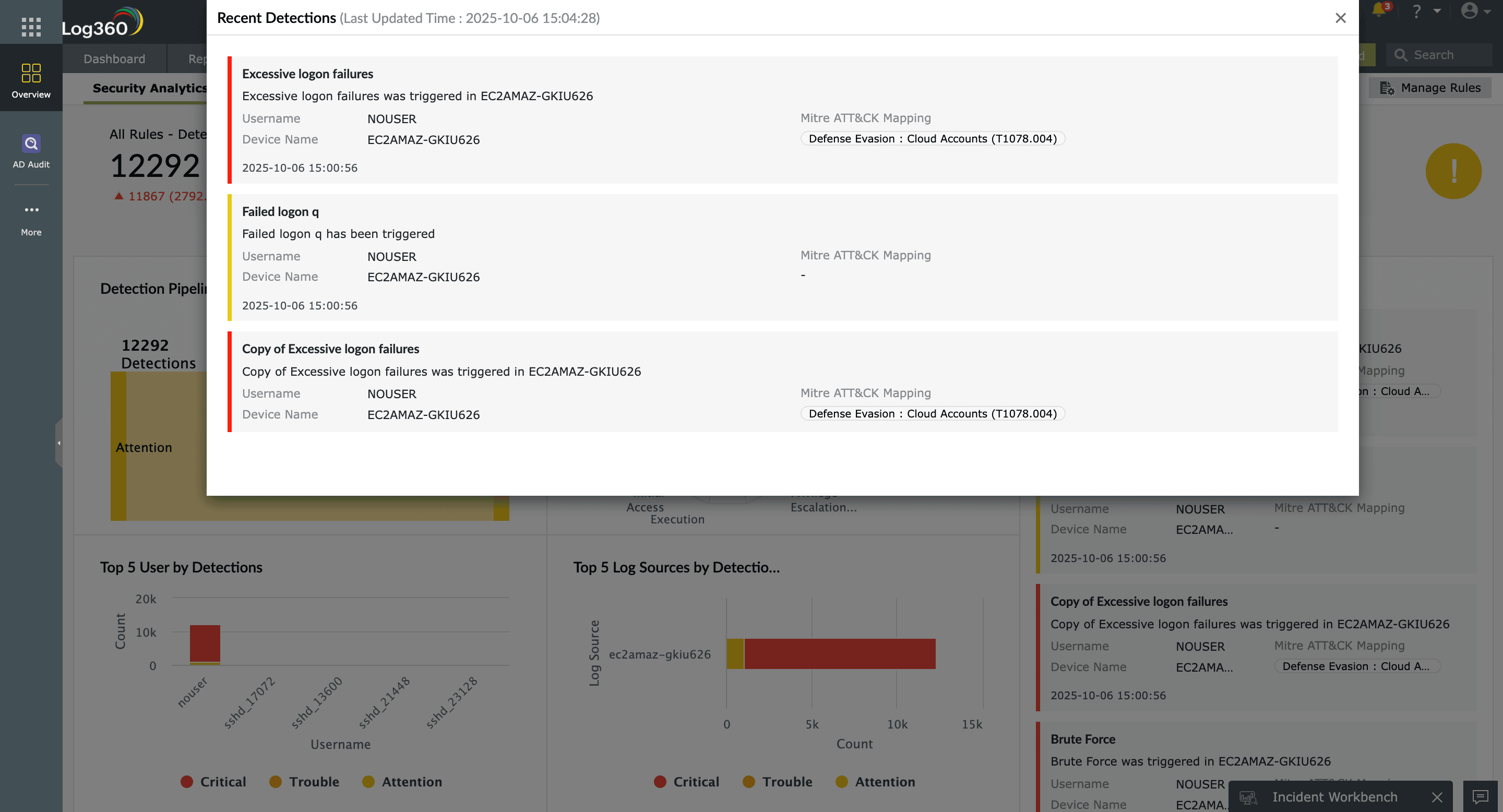
Weaknesses in internet-facing workstations, servers, and applications are often exploited by external threat actors to gain a foothold into the corporate network. Log360 helps monitor the logs of these critical resources to detect abnormal behavior that might indicate attempted or successful exploitation. Its real-time security analytics engine, which uses the MITRE ATT&CK framework, gives insights on SQL injection attack attempts, potential Remote Desktop Protocol exploits, remote code executions, and more.
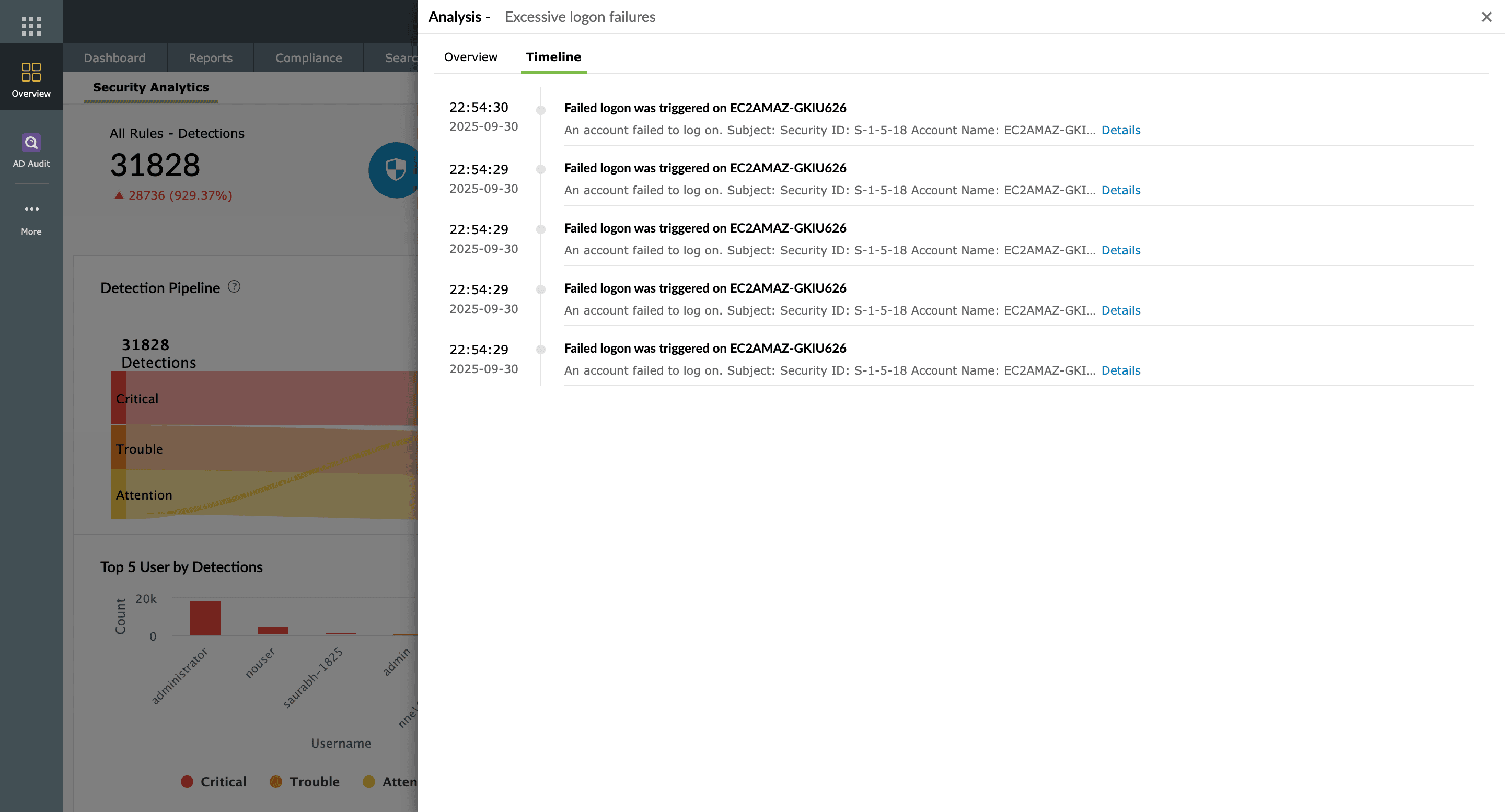
Detect rogue processes
Anything from malware to hacker tools used to steal credentials can be considered a rogue process. Log360 automatically detects malicious software, services, and processes that run on workstation endpoints and servers. The incident timeline provides you with all events associated with the compromised endpoint and user account. You can minimize the damage by first investigating the cause and then killing these malicious processes using workflow rules. Log360 not only detects malicious processes but also helps contain the spread of ransomware attacks.
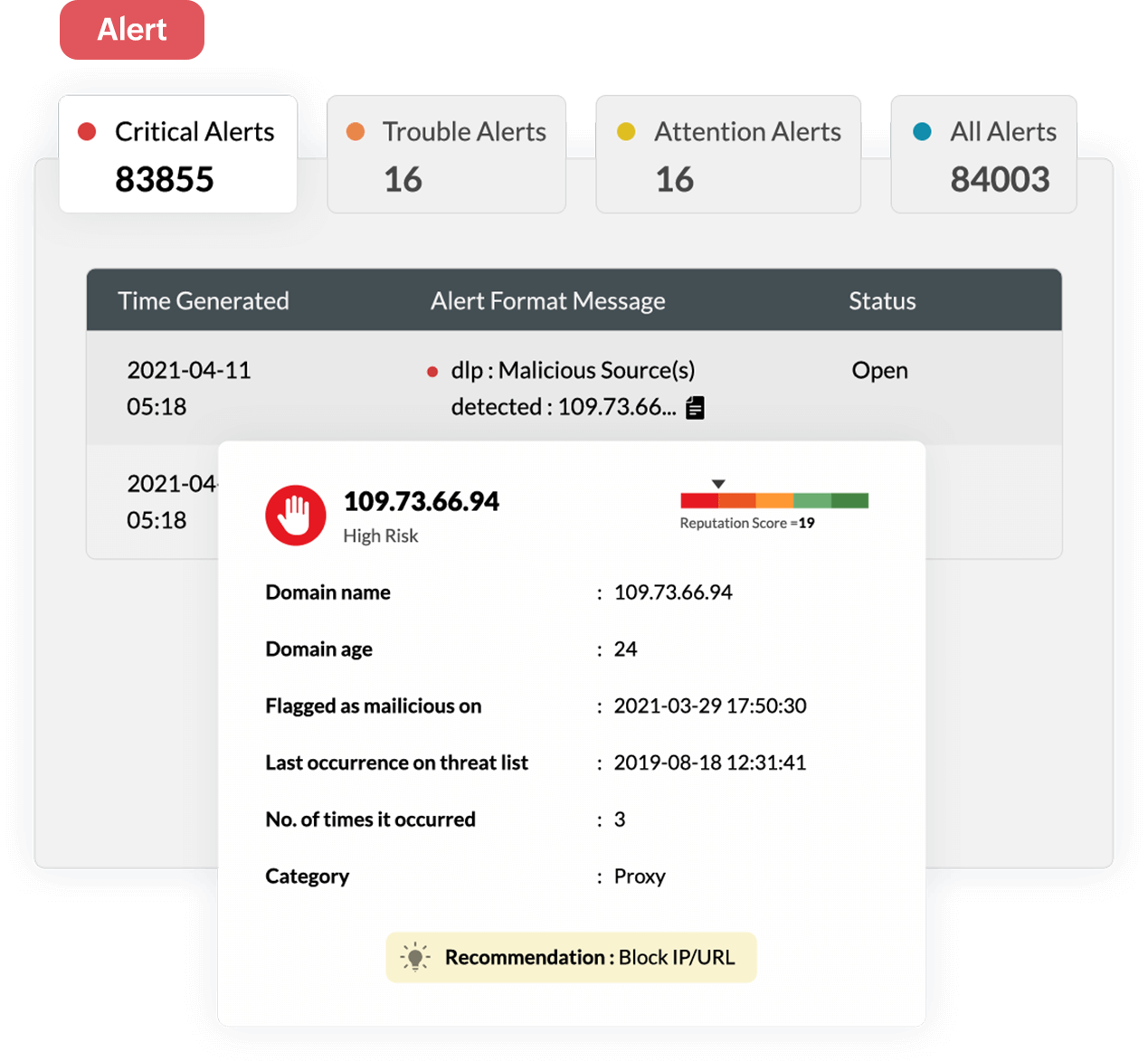
Identify and cut off malicious sources
Detecting external threats is hard because of their dynamic nature. Log360’s threat intelligence platform is enriched continually with contextual threat feeds and gives full visibility into security threats to your business. With the solution’s advanced threat analytics, you can gain insights into threat sources (malicious IPs, domains, and URLs) that are trying to establish connections to your network, the types of threats (phishing, malware attacks, and more), and the recommended course of remediation. Log360 associates a reputation score for each malicious source to help make threat triage more efficient.
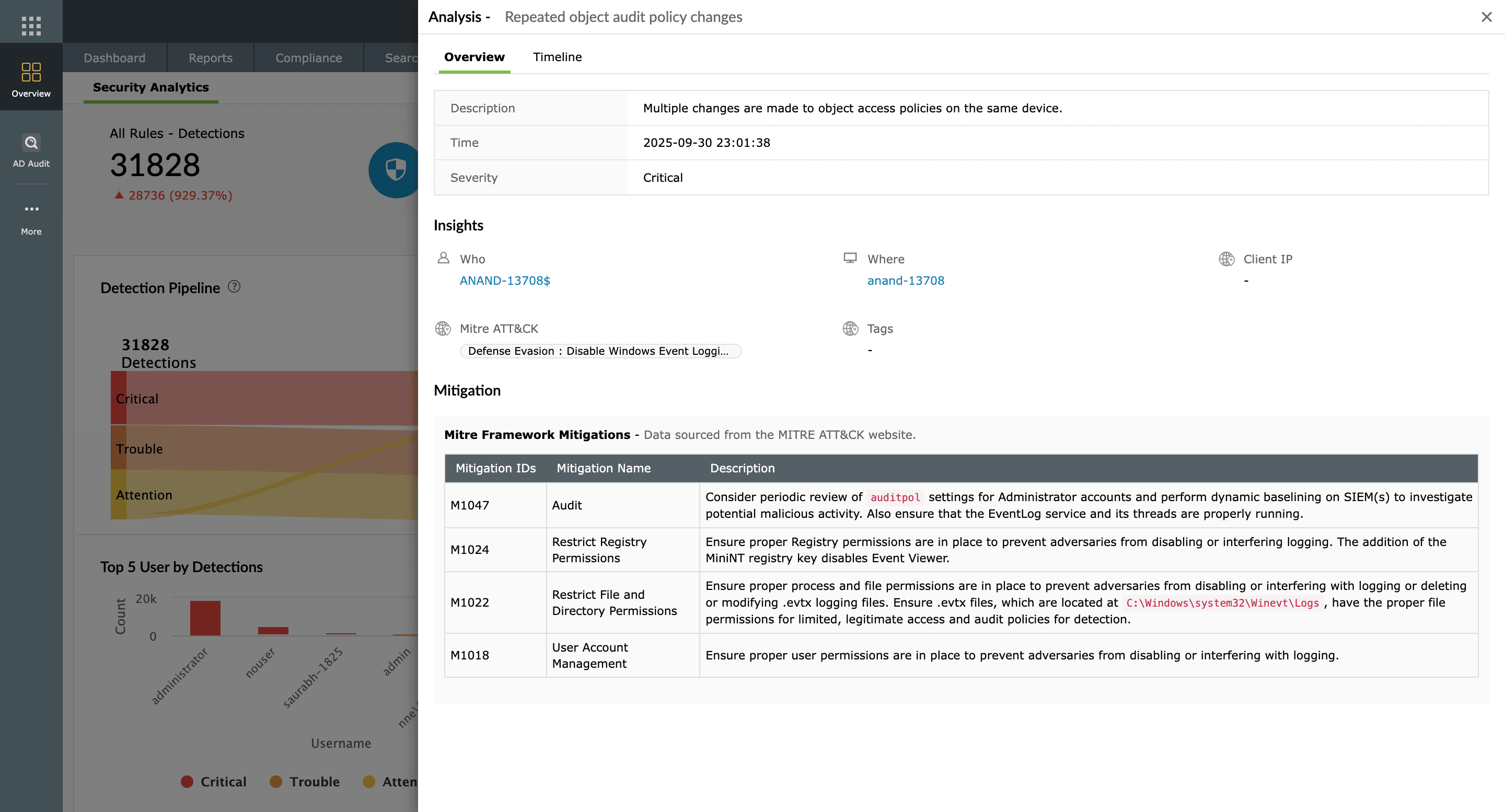
Detect user account compromise
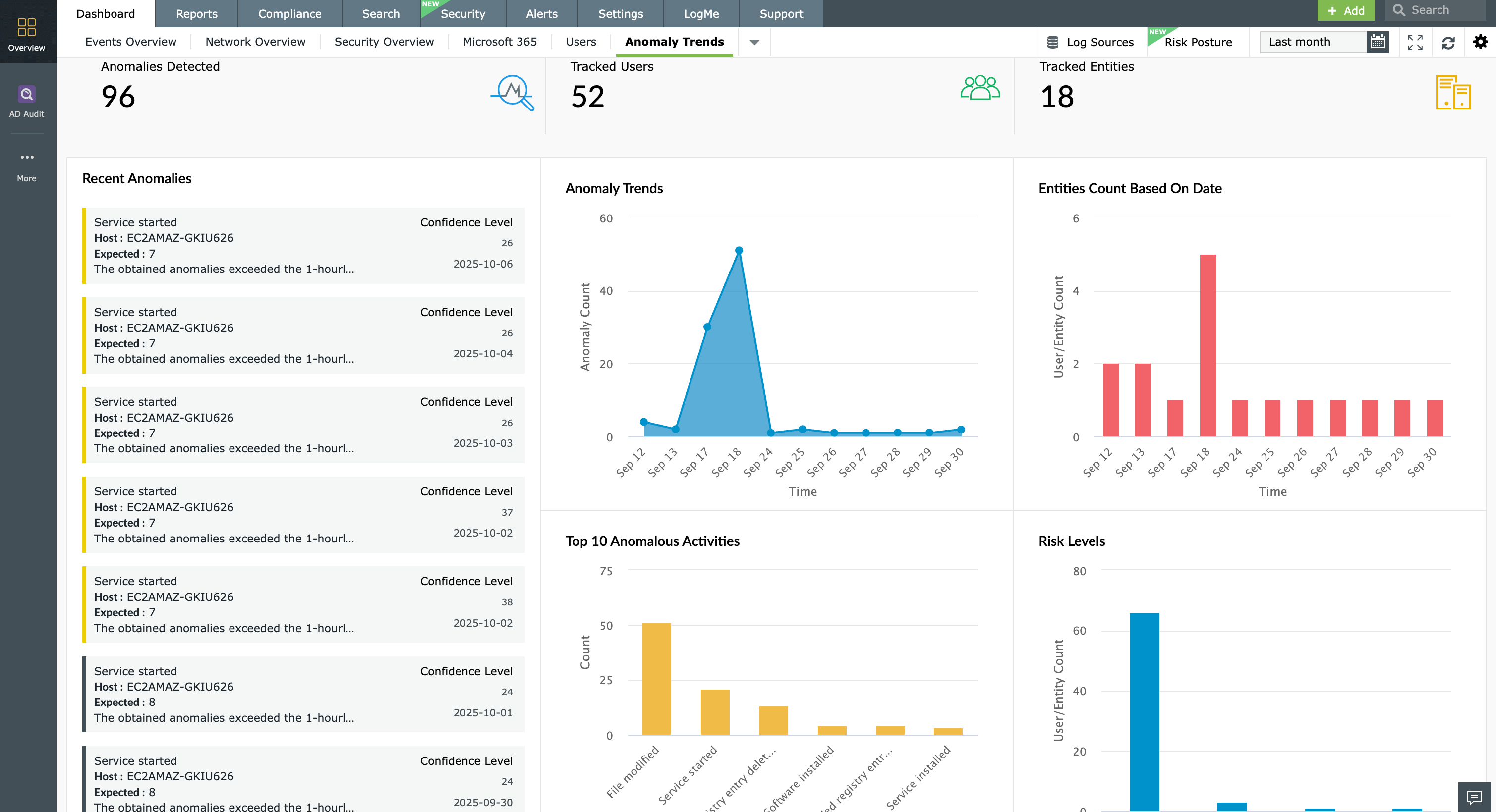
Successful account compromises of users with privileged access can cause substantial damage without triggering the common alarms associated with external attacks . Log360 spots user account compromises with machine learning (ML)-based user and entity behavior analytics (UEBA). Log360’s integrated and dynamic risk management module associates risk scores with every user activity to accurately detect compromised user accounts. The higher the risk score, the more threat the user account poses to the network. Using this information, you can take immediate remediation efforts such as disabling user accounts with the incident workflow module.
Uncover ransomware attacks
Ransomware attacks are popular among external attackers because of their success rates. Log360 protects sensitive data from ransomware attacks by providing real-time notifications for security events that could potentially turn into a ransomware attack. Security professionals can quickly investigate and respond to these threats with incident timelines, forensic investigation, and automated workflow rules. With Log360, you can intervene at the early stages of ransomware attacks and stop them before they spread.
Intercept advanced persistent threats
Advanced persistent threats (APTs) are targeted attacks launched by highly skilled hackers. These attackers infiltrate the network with sophisticated tactics and techniques and move laterally in the network over long periods to avoid detection. APTs are harder to detect because the intrusion, lateral movement, and exfiltration may evade traditional detection techniques.
Modern defensive approaches such as ML-based UEBA can help uncover these techniques accurately. Log360’s UEBA module detects APTs at different stages through abnormal activities such as irregular network traffic, unusual logins, suspicious resource accesses, and more. With Log360’s detailed investigation reports where every activity is tied to a risk score, a security analyst can better trace the steps of attackers and stop them before they cause damage.