Cybersecurity in education refers to the strategies, technologies, and processes used to protect educational institutions from cyberthreats, such as ransomware, phishing, data breaches, and insider attacks. It involves securing sensitive data, safeguarding remote learning environments, and ensuring compliance with regulations.
On this page
Did you know that 82% of K-12 schools suffered cyberattacks (between July 2023 and December 2024), and 63% were affected by ransomware in 2024? The average cost of recovery was reported to be $3.76 million for K-12 schools, and $4.01 million for higher educational institutions. Due to its vast repository of students' sensitive personal and medical data, along with its openness, diverse user base, and budgetary constraints, the education sector is a prime target for cybercriminals. Strengthening cybersecurity in education requires a multi-layered approach, addressing both technical vulnerabilities and human factors, including regular training, robust security protocols, and incident response planning.
Key cybersecurity challenges in the education industry
The following are the structural or operational limitations that make it difficult for educational institutions to defend against cyberthreats:
- Budget constraints and understaffing: Many K-12 and higher education institutions operate with tight budgets and small IT teams, leaving cybersecurity under-prioritized or reactive. K-12 schools, in particular, allocate a maximum of 8%—with some using shockingly less than 1%—of their IT budgets on cybersecurity. Such limited funding restricts investment in advanced security tools and skilled personnel; and while the $200 million pilot program by the FCC to support cybersecurity services in education is a good start, the fact that it received requests totaling $3.7 billion emphasizes how tight budgets are and underscores the critical importance of cybersecurity in education.
- Legacy infrastructure and unpatched systems: Many educational institutions continue to rely on outdated IT infrastructure—encompassing both software and hardware—that lacks robust security and is often incompatible with modern cybersecurity solutions. The discontinuation of security patch support for these legacy systems significantly increases vulnerability, making institutions prime targets for cyber exploitation.
- Decentralized governance models: Universities and large school districts often operate within siloed IT environments across departments and campuses, resulting in inconsistent security policies and limited visibility. The continual turnover of students and faculty further complicates secure onboarding and offboarding processes. These dynamics make identity and access management (IAM) more complex and hinder the implementation of a unified cybersecurity strategy.
- Remote learning and BYOD: The widespread adoption of remote learning and BYOD has expanded the attack surface within educational institutions. Personal laptops, tablets, and smartphones—often lacking enterprise-grade security controls—introduce vulnerabilities through unmanaged endpoints. These devices operate outside the traditional perimeter of institutional IT oversight, making it difficult for cybersecurity teams to enforce consistent policies, monitor activity, and respond to threats effectively.
- Third-party and vendor risk management: Educational institutions rely heavily on third-party platforms—such as learning management systems, cloud storage, and student information systems—to support academic and administrative functions. However, these services can introduce vulnerabilities beyond institutional control. Educational institutions often lack effective frameworks to assess or monitor the cybersecurity posture of external vendors, resulting in limited visibility and increased exposure to third-party risks. Strengthening vendor oversight is critical to protecting institutional data and ensuring the resilience of digital education systems.
- Lack of cybersecurity awareness: Students, educators, and administrative staff often lack formal training in cybersecurity or digital hygiene. This increases the risk of falling victim to phishing schemes, social engineering attacks, or mishandling sensitive data. As educational institutions increasingly depend on digital platforms, fostering cybersecurity awareness and equipping campus communities to identify threats and practice safe online behavior are vital to building a resilient learning environment.
- Compliance complexities: Educational institutions are required to adhere to data protection regulations such as the Family Educational Rights and Privacy Act (FERPA), Children’s Online Privacy Protection Act, HIPAA, and the GDPR. Ensuring compliance becomes increasingly complex when institutions operate across jurisdictions and rely on a mix of on-premises and cloud-based tools, making it challenging to maintain consistent data governance and avoid regulatory penalties.
Cybersecurity threats in the education sector
Educational institutions face a growing number of cybersecurity threats due to their extensive storage of sensitive data (student and staff records, research data) and often limited cybersecurity resources. Microsoft reported that universities experience an average of 2,507 attempted cyberattacks per week.
The following are the key cybersecurity threats in the education sector:
- Ransomware attacks: These attacks involve hackers encrypting data and demanding payment for its release, disrupting academic operations, corrupting backups, and exposing sensitive personal and personally identifiable data. This can cause significant financial and reputational damage to educational institutions. Schools are viewed as vulnerable due to inconsistent patching and under-resourced IT teams. As mentioned earlier, the mean recovery cost from a ransomware attack for K-12 organizations and higher education institutions has witnessed a multifold increase in 2024.
- Phishing and social engineering: Staff, faculty, and students often lack awareness, making them vulnerable to credential theft, especially for email, learning management systems, and administrative platforms. Adversaries often impersonate trusted sources such as IT departments or faculty, using spoofed domains and urgent financial messaging to trick victims into revealing sensitive information, leading to data breaches and financial losses. Additionally, QR code phishing is surging across campuses, with Microsoft reporting that over 15,000 malicious messages containing QR codes are sent daily to educational institutions via flyers, emails, and digital handouts.
- Malware: This includes viruses, worms, and spyware that can compromise data integrity, disrupt learning environments, and pose security risks for connected devices. The malware usually infiltrates systems via compromised attachments or fake updates and targets smart devices and IoT infrastructure used in modern classrooms.
- Distributed denial of service (DDoS) attacks: These attacks overwhelm networks with traffic, making online learning platforms, exam portals, administrative systems, and other resources unavailable. DDoS attacks are often executed via botnets or compromised student devices, and can be carried out by hackers or malicious insiders. You can learn more about DDoS in educational networks here.
- Credential stuffing and account takeovers: Due to password reuse and weak or limited MFA adoption, attackers frequently exploit compromised credentials (often acquired from previous breaches) to access sensitive systems like student information and financial aid portals, grading systems, or HR databases.
- Data breaches and identity theft: Schools and universities store PII, financial data, academic records, and even health data—making them attractive targets for identity theft, fraud, or black-market resale. Such privacy violations can result in hefty financial and reputational loss for educational institutions. This is evidenced by the IBM report, which reports that the average cost of a data breach in the education sector in 2025 is $3.8 million.
- Insider threats: Current or former students and employees, or contractors with network access, can pose risks through malicious intent or negligence, leading to unauthorized access, data leaks, or security breaches.
- IoT vulnerabilities: The increasing use of connected devices in education (e.g., interactive learning tools, security cameras, smart cards, wearables, and smart HVAC and lighting systems) creates new vulnerabilities, as these devices often lack strong security measures. Without the required security hardening, these devices give attackers new entry points into the institutional network.
- Cloud security risks: These risks stem primarily from misconfigured cloud settings and inadequate access controls, which can expose sensitive student data, research records, and administrative information to unauthorized access or cyberattacks. As schools and universities increasingly rely on platforms like Google Workspace and Microsoft 365, improper permission settings or a lack of role-based access can lead to accidental data leaks or malicious breaches.
Key logs to be monitored in the education industry
To maintain a secure and efficient digital environment, educational institutions must monitor logs from various sources. This is crucial for protecting sensitive data, ensuring system performance, and complying with regulations such as FERPA and the GDPR.
-
Learning management system (LMS) logs:
LMS platforms like Moodle, Blackboard, or Canvas hold sensitive student and faculty data.
What to monitor:
- User login and logout activity: Track access patterns and detect unauthorized access and suspicious login patterns targeting faculty or admin accounts.
- Course access logs: Monitor which users access which courses and when.
- Assignment submissions and grading logs: Ensure the integrity of academic records and track unauthorized modifications to exams, grades, or learning content.
- Permission changes: Detect unauthorized privilege escalation.
- API usage logs: Monitor integrations with third-party tools for anomalies.
- File uploads and downloads: Identify mass downloads or uploads of potentially malicious files.
- New user creations: Spot fraudulent account creation to bypass authentication controls.
-
Student information system (SIS) logs:
Monitoring SIS logs is essential for identifying unauthorized access, data manipulation, or misuse of student records—safeguarding data integrity, ensuring privacy compliance, and defending against internal and external threats.
What to monitor:
- Data access logs: Track who accessed sensitive student data.
- Record modification logs: Monitor changes to grades, attendance, or personal details.
- Authentication attempts: Detect brute-force or credential stuffing attacks.
- Role-based access changes: Ensure only authorized personnel have access to sensitive data.
-
Firewall logs:
Firewalls act as the first line of defense, making their logs vital for identifying perimeter threats.
What to monitor:
- Blocked and allowed connections: Identify suspicious inbound or outbound connections, especially to high-risk geolocations. Doing so can help detect data exfiltration or malware communication.
- Port scanning or unusual protocol usage: Detect reconnaissance attempts targeting common service ports (e.g., 21, 22, 3389, 445, 1433) and flag reconnaissance activities.
- VPN access logs: Monitor unusual connection times or locations for remote faculty or administrative staff accessing internal systems.
- Repeated denied access attempts: Spot brute-force attacks or malware trying to exfiltrate data.
-
Web proxy and content filtering logs:
Educational institutions often need to control and monitor web usage for compliance and safety.
What to monitor:
- Access to prohibited or high-risk sites: Detect visits to phishing or malware-hosting domains.
- Unusual download activity: Flag large or repeated downloads that could indicate data exfiltration.
- Bypass attempts: Monitor use of anonymizers, VPNs, or proxy tools that may hide malicious activity.
- High volume HTTP/S requests: Identify bot infections or compromised devices.
-
IAM logs:
Authentication logs provide visibility into account security for staff, students, and administrative users.
What to monitor:
- Failed login attempts: Identify brute-force attacks or credential stuffing attempts.
- MFA status: Ensure MFA is enforced and functioning.
- Logins from unusual locations: Spot potential account compromise by correlating with geolocation data.
- Multiple concurrent logins: Detect credential sharing or account misuse.
- Group membership changes: Track admin-level access changes or role modifications.
- Account lockouts and password resets: Detect potential account compromise.
-
Cloud application and application server logs:
Educational institutions rely on these logs to monitor system performance, detect application errors, and investigate security incidents across LMS platforms and student portals.
What to monitor:
- HTTP request patterns: Detect abnormal usage or potential DDoS attacks.
- Error logs: Identify application failures or misconfigurations.
- Session management logs: Monitor for session hijacking or replay attacks.
- File access logs: Track access to sensitive documents or resources.
- Mass data downloads: Detect attempts to extract large volumes of academic or personal data.
-
Database logs:
Helps educational organizations monitor data access and changes, helping protect student records and support audits.
What to monitor:
- Query logs: Detect unauthorized data access or data scraping.
- Failed login attempts: Identify brute-force attacks on database credentials.
- Data modification logs: Track changes to student records or financial data.
- Privilege escalation attempts: Monitor for unauthorized access to admin functions.
-
Email security gateway logs:
Email remains a major attack vector in the education sector.
What to monitor:
- Phishing attempts and spam detection (including spoofed sender addresses): Identify malicious emails targeting staff or students by impersonation and other tactics.
- Email forwarding rules: Detect data leakage via auto-forwarding.
- Login anomalies: Monitor for compromised email accounts.
- Attachment scanning logs: Flag malware or sensitive data sharing.
- High-volume outbound emails: Spot potential compromised accounts sending spam or phishing.
-
Endpoint detection and response logs:
Endpoints in education environments pose a high risk due to shared devices and BYOD policies.
What to monitor:
- Malware and ransomware alerts: Identify infected devices and respond to threats before they spread.
- Unauthorized software installation: Prevent the use of unapproved and risky applications.
- Suspicious process executions: Flag scripts, macros, or binaries attempting lateral movement.
- USB device usage logs: Monitor for data theft via removable media.
- Device compliance status: Ensure devices meet security standards.
-
Physical access control logs:
Educational institutions use physical access control logs from RFID systems and biometric scanners to monitor entry and exit activity, ensuring campus safety and managing authorized access.
What to monitor:
- Entry and exit timestamps: Track physical access to sensitive areas like server rooms.
- Access denial events: Detect unauthorized entry attempts.
- Badge misuse: Identify potential insider threats.
Benefits of implementing SIEM in educational institutions
A SIEM solution enhances operational efficiency and optimizes resources by automating incident response workflows, reducing the manual burden on understaffed security teams. By centralizing security monitoring into a single platform, SIEM streamlines visibility. Its ability to prioritize high-risk alerts ensures security teams focus on the most critical threats, enabling a proactive security posture that shifts from reactive security to predictive defense strategies.
Here's how SIEM solutions benefit the education industry:
1. Centralized visibility and monitoring
- Unified security monitoring: Consolidate logs from academic systems, LMS, SIS, and administrative platforms; firewalls; endpoints; servers; cloud applications; and databases into a single pane-of-glass view.
- Cross-campus insight: Monitor security activity across multiple campuses, departments, and remote learning environments in real time.
- Device discovery: Helps identify all connected devices and systems automatically, ensuring nothing is left unmonitored.
- Unified visibility across cloud and on-premises systems: SIEM bridges visibility across hybrid environments, allowing institutions to monitor both cloud-hosted applications (like Google Workspace or Microsoft 365) and on-premises servers from a single dashboard.
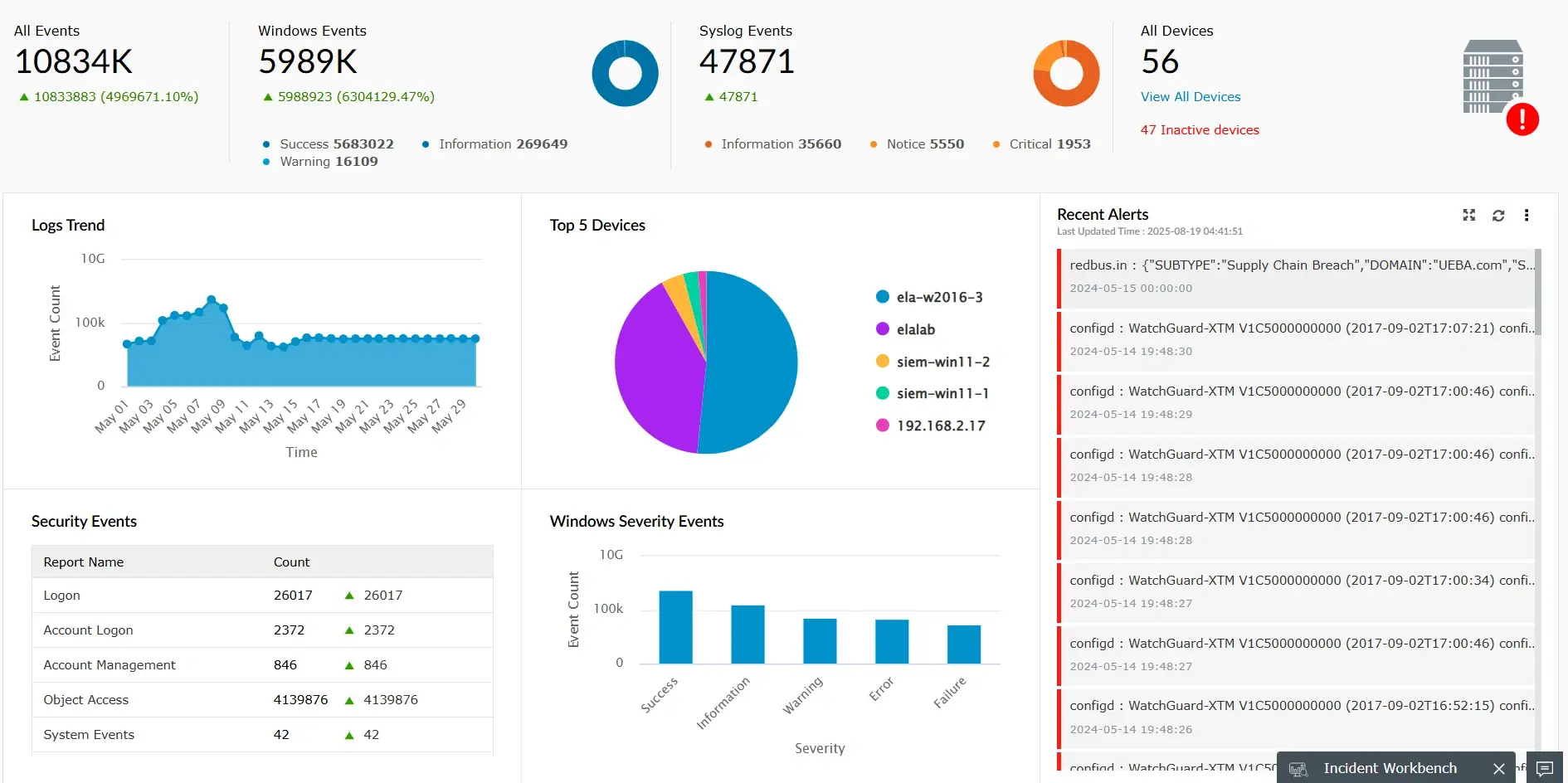
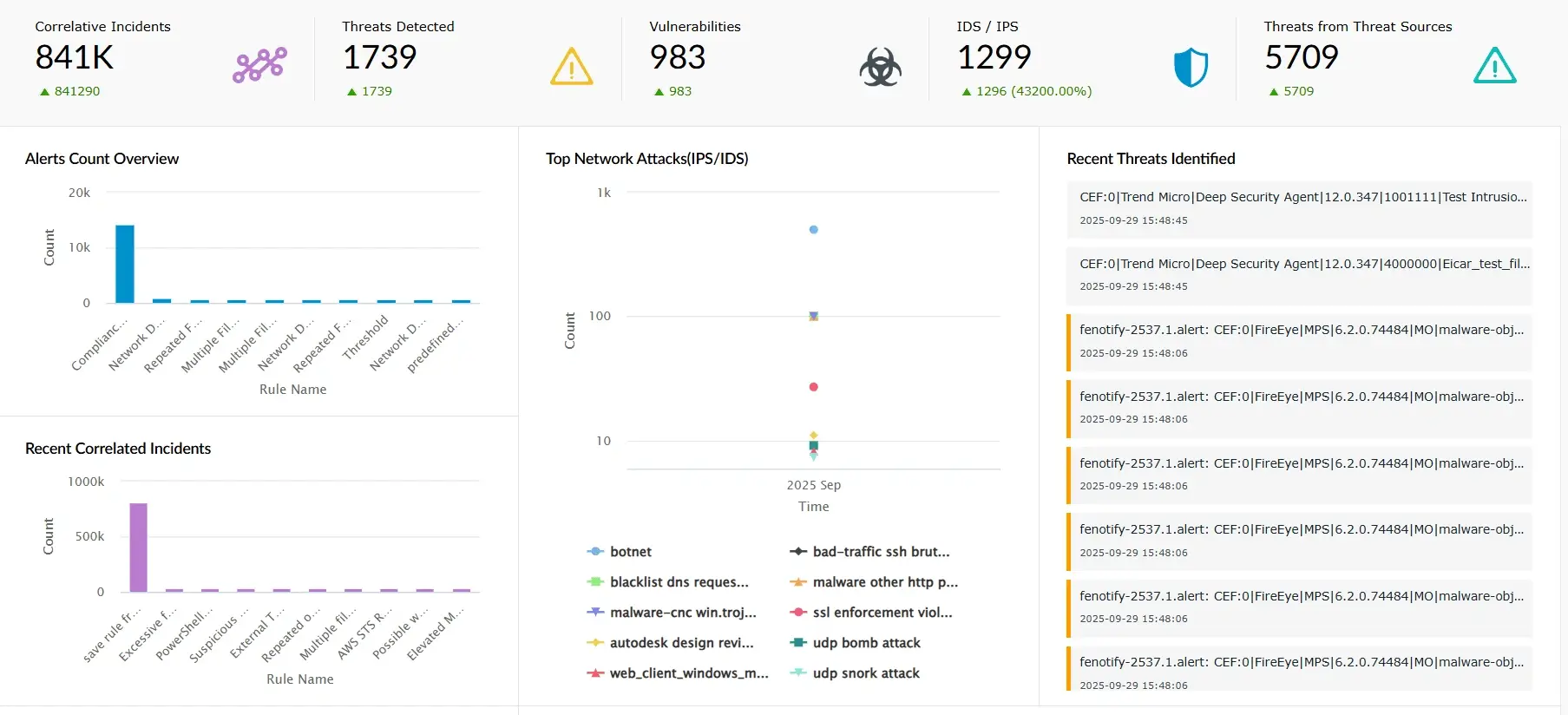
2. Early threat detection and response
- Detect sophisticated attacks early: Leverage user and entity behavior analytics to identify threats like ransomware, APTs, or compromised accounts targeting student, faculty, or research data before they escalate.
- Correlate multi-source events: Combine logs from SISs, LMSs, firewalls, endpoints, and other sources to reveal hidden attack patterns and lateral movement.
- Integration with threat intelligence: SIEM solutions integrate with global threat feeds to recognize known attack signatures.
- Receive real-time alerts: Get instant notifications on suspicious activity to minimize mean time to detect and respond to security incidents.
- Eliminate visibility gaps: Monitor on-premises, cloud, and hybrid learning environments to reduce blind spots and strengthen overall detection capabilities.
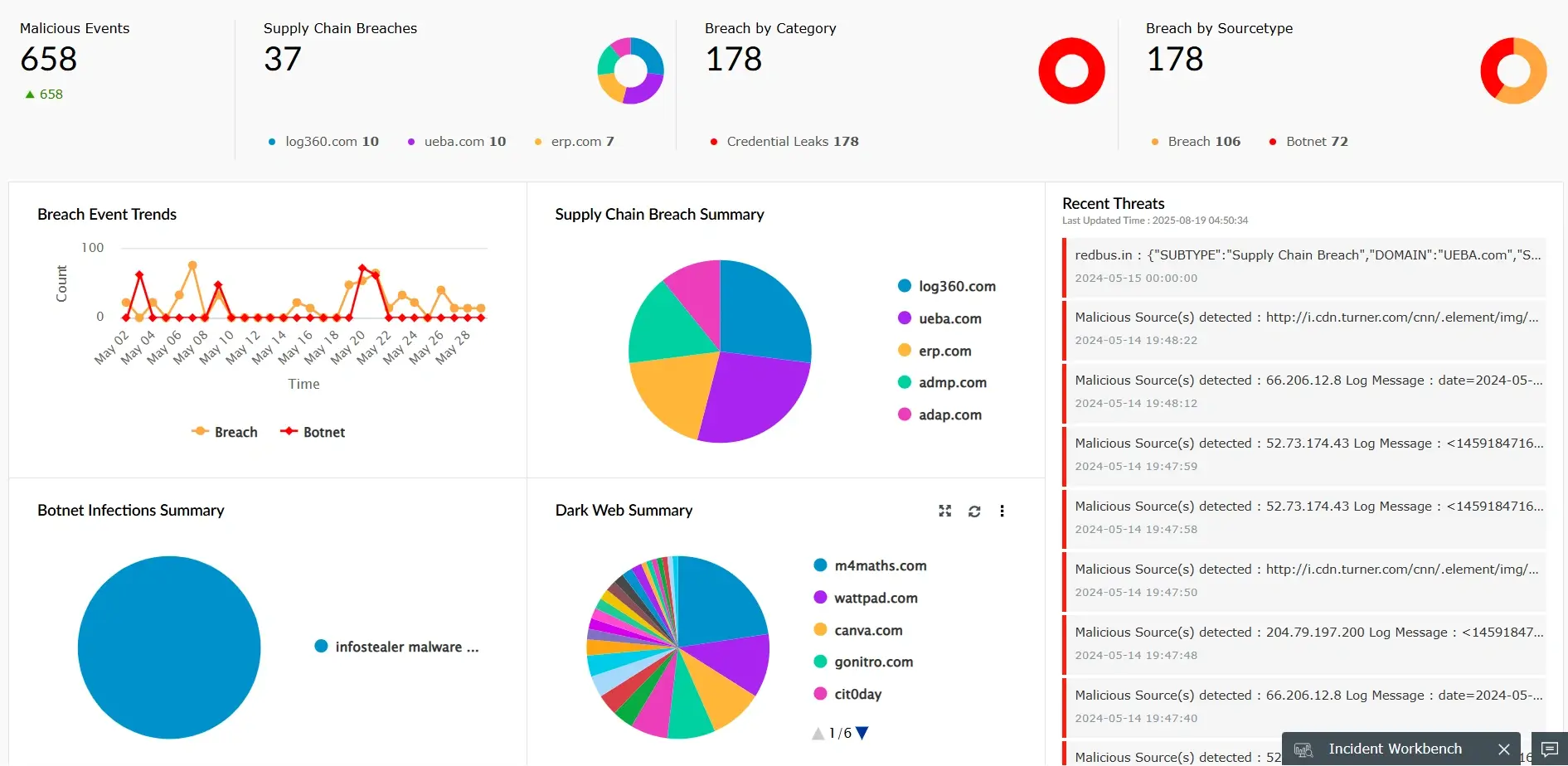
3. Protection of sensitive student and research data
- Safeguard PII: Prevent unauthorized access to student records, financial details, and health data.
- Detect compromised credentials: Leverage dark web monitoring capabilities to identify the compromised credentials of students, faculty, and administrative staff before attackers exploit them.
- Prevent data exfiltration: Detect unusual outbound traffic that may signal a data breach.
- Mitigate insider threats: Identify suspicious access patterns and privilege escalation attempts from faculty, staff, or students.
- Ensure data integrity: Maintain accurate academic records and research results by monitoring tampering attempts.
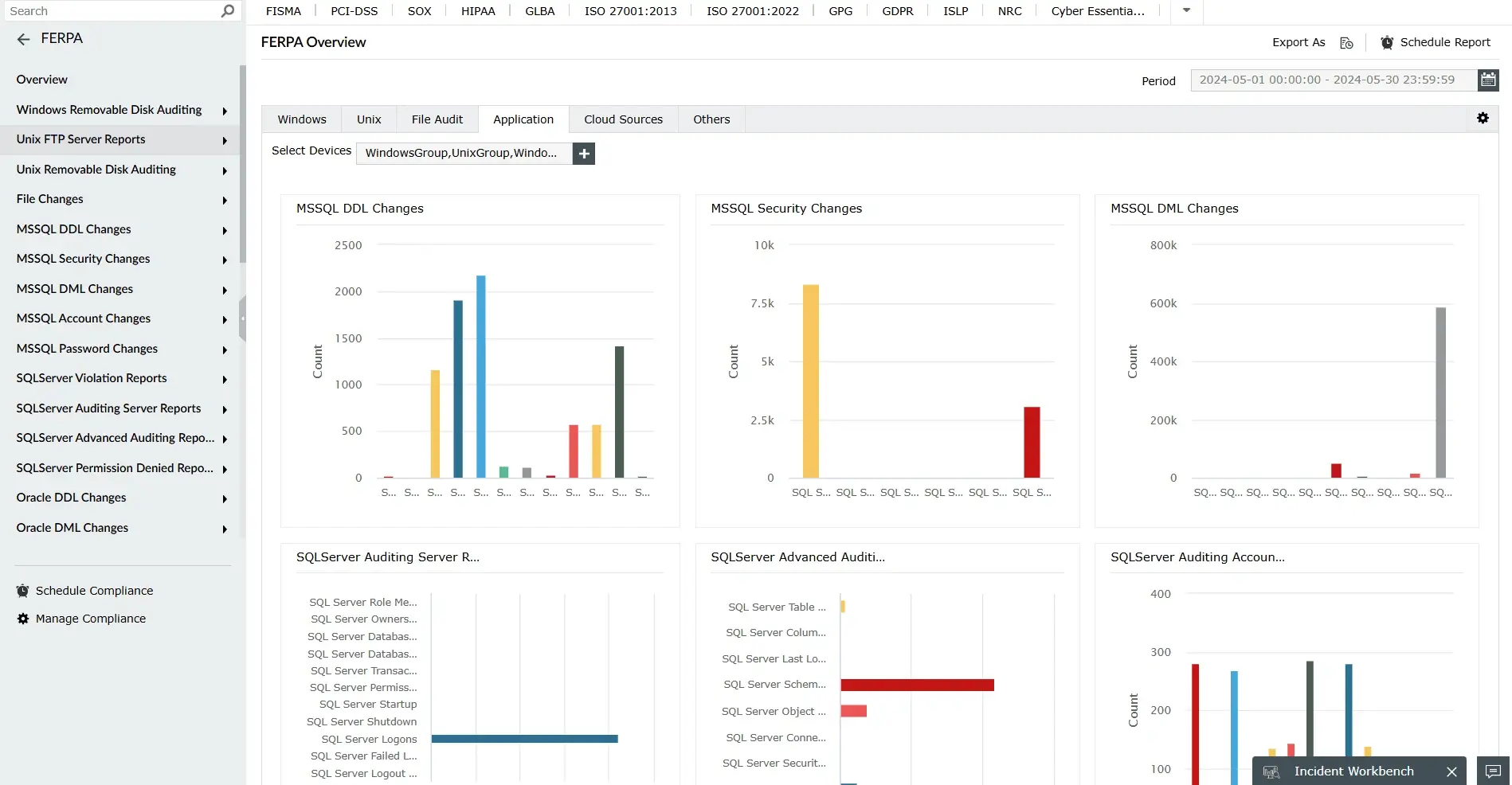
4. Compliance with data privacy regulations
- Regulatory alignment: Automate log collection and retention to align with compliance mandates like FERPA, the GDPR, and HIPAA.
- Enable continuous compliance monitoring: Use automated alerts and dashboards to detect potential regulatory breaches in real time.
- Streamline audit readiness: Generate compliance reports with minimal manual effort.
- Demonstrate due diligence: Provide evidence of proactive cybersecurity measures to boards and regulators.
- Policy enforcement: Educational institutions can enforce access controls and monitor policy violations.
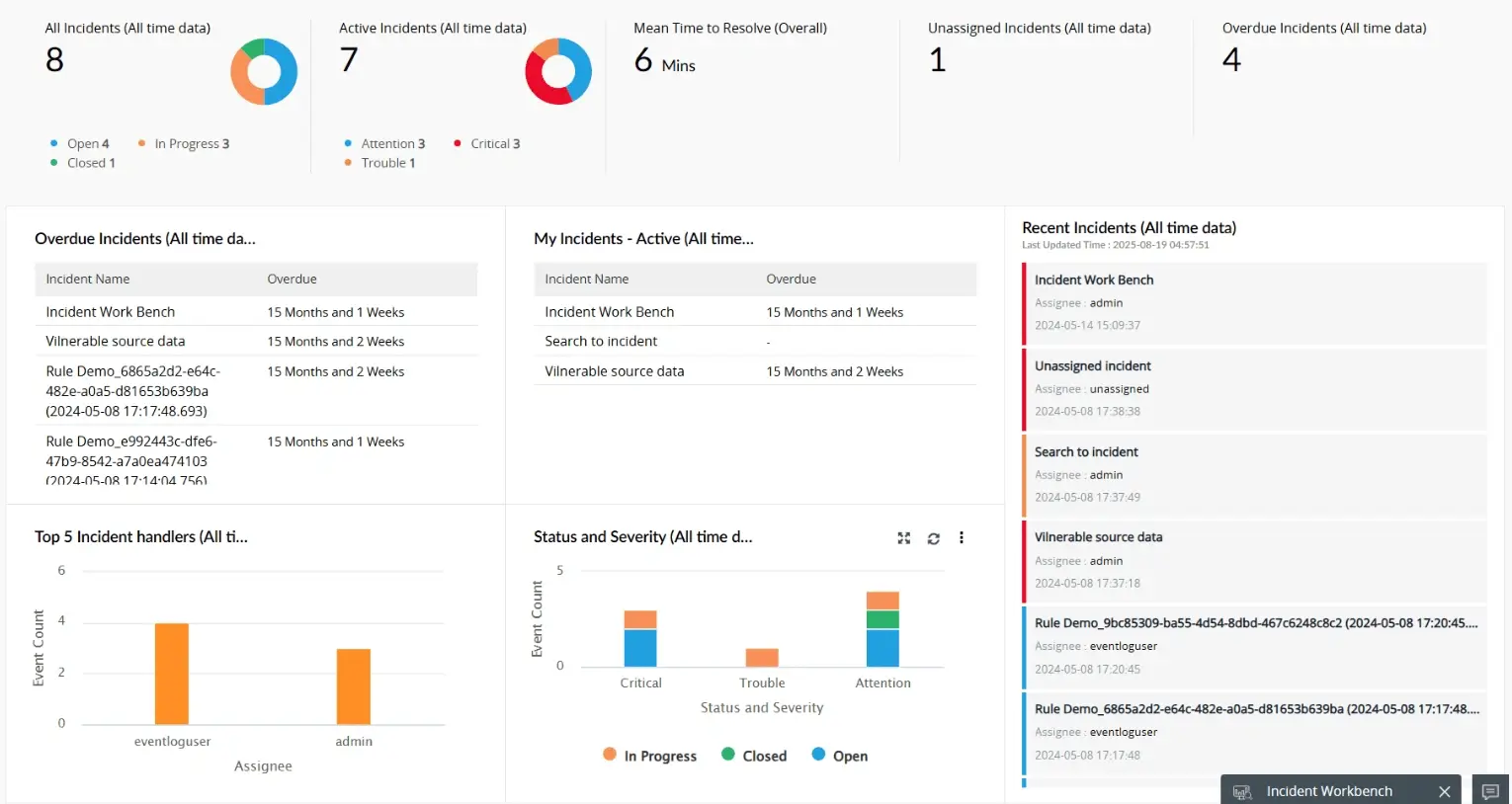
5. Faster incident response
- Automated workflows: SIEM can trigger automated responses to certain threats, such as account lockdown, disabling the user, and shutting down the system, reducing manual intervention.
- Root cause analysis: It helps security teams quickly identify the source of an incident and contain it.
- Incident prioritization: Alerts are ranked by severity, allowing teams to focus on the most critical threats first.
- Reduced recovery time: Faster response leads to quicker recovery and less disruption to academic operations.
SIEM use cases in the education industry
Cyberbullying detection in educational institutions through SIEM
Cyberbullying has become one of the most critical digital safety concerns in schools and universities, often taking place across chat platforms, LMSs, and collaboration apps. A SIEM solution enables real-time monitoring and automated alerts to swiftly identify and respond to cyberbullying incidents.
Challenges:
- Cyberbullying often goes undetected on chat apps, LMS platforms, and collaboration tools. It may also involve unapproved applications that evade IT monitoring.
- Indicators such as offensive messages, targeted login attempts, or abnormal peer-to-peer activity are scattered across systems, making it difficult to monitor.
- Lack of centralized visibility delays response, impacting student safety and institutional reputation.
How a SIEM solution like Log360 helps:
- Log correlation: Collects communication logs, chat transcripts, and login activities across platforms.
- Keyword and behavioral analysis: Flags patterns like repeated use of abusive terms, unusual login attempts targeting specific students, or sudden spikes in peer-to-peer messaging.
- Network traffic analysis: Identifies unusual traffic patterns such as high-volume data transfer between student devices, suspicious peer-to-peer tunnels, or connections to known risky domains.
- Cloud security: A SIEM with CASB capabilities helps detect and ban shadow and risky applications, and enforce policies to ensure the use of only sanctioned applications in educational institutions.
- Real-time alerts: Notifies security teams immediately in real-time for a quick and timely intervention.
To learn more, read: K-12 cybersecurity: Safeguarding students from cyberbullying and harmful online content.
Securing email, collaboration tools, and smart campus devices with SIEM
Fragmented systems and shared access points create blind spots and vulnerabilities across smart campus environments. A SIEM solution centralizes visibility and correlates events across platforms to detect threats and enforce security policies.
Challenges
Smart campuses depend heavily on email, cloud collaboration, Wi-Fi networks, and shared devices.
- Risks include:
- Phishing and credential theft via faculty and student emails.
- Unauthorized access to lab devices and shared resources.
- Spread of malware in open computer labs.
- CISOs lack a unified view of these disparate attack surfaces.
How a SIEM solution like Log360 helps:
- Centralized visibility: Aggregates logs from email gateways, Wi-Fi controllers, endpoint security, and lab systems.
- Dark web monitoring: Identifies compromised credentials of students, faculty, and staff.
- Threat detection: Identifies spear-phishing, suspicious file sharing, privilege escalation attempts, or simultaneous logins from different geographies.
- Data loss prevention: Tracks suspicious file accesses, modifications, uploads, and downloads to prevent the exfiltration of sensitive academic research, student data, and intellectual property.
- Automated response: Incident response playbook actions get triggered to isolate compromised accounts and devices to contain the threat.
To learn more, read: Comprehensive cybersecurity for smart campuses: Securing email and collaboration tools, computer labs, and shared devices.
Securing gamification and e-learning platforms with SIEM
Gamified learning platforms and e-assessments are prone to cheating, data leaks, and unauthorized access. A SIEM solution helps track user behavior, detect anomalies, and protect sensitive educational data in real time.
Challenges
- Adoption of gamified learning and online exams creates risks:
- Account misuse (shared or stolen credentials).
- Exam integrity breaches (unauthorized content access, script automation of quiz attempts).
- DDoS attacks targeting exam servers during critical times.
- Traditional monitoring lacks forensic depth for incident analysis.
How a SIEM solution like Log360 helps:
- Authentication monitoring: Detects multiple logins from different geographies on the same account, suspicious access, or token misuse.
- Anomaly detection: Flags anomalous user and entity behavior, such as automated scripts attempting rapid submissions or manipulation of scores.
- Custom rule creation: Enables the creation of custom rules and alerts for identifying suspicious threat patterns, unauthorized access, and data exfiltration.
- Access control integration: Works with IAM solutions to enforce strict identity validation for online exams.
- Forensic investigation: Enables root-cause analysis and reporting to strengthen digital exam policies.
To learn more, read: Securing e-learning and gamification platforms: Risks and best practices
How SIEM helps with regulatory requirements in the education industry
For CISOs in the education sector, maintaining compliance with regulatory requirements is critical to protecting student privacy, institutional reputation, and funding eligibility. SIEM solutions play a pivotal role in achieving and demonstrating compliance by centralizing log collection and retention from diverse systems such as SISs, LMSs, network devices, and cloud platforms for the mandated retention periods. They automate compliance reporting with prebuilt and customizable templates that address frameworks like FERPA, the GDPR, HIPAA (for research or health data), and other regional education data policies.
SIEM solutions also enable real-time compliance monitoring by continuously tracking access, data usage, and system activity to ensure adherence to policies while detecting violations early. Additionally, they support audit readiness and forensic investigations by providing complete, time-stamped event trails, reducing the time and effort needed to respond to compliance inquiries. In the education sector, SIEM is an indispensable tool to ensure that data governance, access control, and incident response protocols align with regulatory mandates.
A unified SIEM solution like ManageEngine Log360 can further strengthen compliance efforts in the education industry by offering an integrated platform for log management, threat detection, and compliance reporting. With centralized monitoring of student and institutional data, Log360 helps detect anomalies, prevent data misuse, and maintain a secure digital ecosystem. It also comes with built-in compliance-specific report templates for major regulations, making it easier to generate audit-ready documentation without manual effort.
Log360's real-time alerting and correlation capabilities help detect policy violations the moment they occur, while its long-term log archival ensures records are retained securely in line with regulatory requirements. With centralized visibility and advanced search features, Log360 allows CISOs to quickly trace incidents, prove adherence during audits, and proactively address compliance risks across on-premises, cloud, and hybrid learning environments.
How to choose the right SIEM solution for educational institutions
- Assess institutional needs: Evaluate the scale of your IT infrastructure, number of users, and mix of on-premises, cloud, and hybrid learning environments.
- Consider deployment flexibility: Whether on-premises, cloud-based, or hybrid, the SIEM solution should align with your institution’s IT strategy and data residency requirements.
- Ensure broad log collection: Choose a SIEM solution that can gather logs from SISs, LMSs, endpoints, firewalls, applications, databases, and cloud services.
- Look for advanced analytics: Prioritize solutions with correlation rules, behavioral analysis, and AI and ML to detect sophisticated threats such as ransomware, phishing, and insider attacks.
- Enable real-time detection and response: Ensure the SIEM solution offers real-time alerts, automated workflows, and tools to reduce mean time to detect (MTTD) and mean time to respond (MTTR) to security events in your institution.
- Verify scalability: Confirm the SIEM solution can process high log volumes across multiple environments without performance issues.
- Check integration capabilities: Ensure compatibility with other tools like IAM, UEBA, CASB, EDR, and DLP for a unified security posture. You should also ensure that the SIEM solution integrates smoothly with your existing infrastructure.
- Simplify compliance management: Opt for SIEM solutions with built-in compliance reporting for FERPA, HIPAA, the GDPR, and the PCI DSS to ease audit preparation.
- Look for education-specific use cases: Look for SIEM solutions that offer preconfigured rules and dashboards tailored to common threats and operational needs in academic environments.
- Validate log retention and forensic capabilities: Ensure that the SIEM solution offers secure, tamper-proof log storage and easy access to historical data for investigations and audits.
- Evaluate usability and support: Look for ease of deployment, intuitive dashboards, customization options, and responsive vendor support for long-term operational success.
ManageEngine Log360 is a comprehensive and highly scalable SIEM solution with integrated UEBA, DLP, CASB, and SOAR capabilities. It offers both on-premises and cloud-based deployment options. It collects logs from more than 750 log sources across vendors and analyzes them for threats with the help of predefined rules, ML-based anomaly detection, and AI-based contextual insights for effective threat identification and incident response. It also provides audit-ready reports for FERPA, the GDPR, HIPAA, the PCI DSS, and more. Log360 enables you to configure the log retention period based on your preference and compliance requirements. It provides a powerful search option for performing root cause analysis and forensic investigations. To learn more, request a personalized demo.
Frequently asked questions
Educational institutions often store large volumes of sensitive personal, academic, and research data while operating with limited cybersecurity budgets. These factors, combined with a high number of connected devices and users, make them attractive targets for cybercriminals.
The education industry faces threats such as ransomware attacks, DDoS, malware, data breaches, identity theft, phishing campaigns targeting student and staff emails, exploitation of unpatched systems, insider threats, and attacks on LMS and SIS platforms. Increasing use of cloud-based learning tools has also expanded the attack surface.
The most at-risk data includes personally identifiable information (PII) of students and staff, academic records, financial data, intellectual property from research, and health records maintained under student wellness programs.
Schools can implement MFA, conduct regular security awareness training, use email filtering solutions, patch systems promptly, and leverage SIEM solutions for real-time monitoring and threat detection.
SIEM solutions aggregate and analyze logs from multiple sources—such as SISs, LMSs, firewalls, and endpoints—to detect malicious activity in real time. They enable faster incident detection, automated response, and comprehensive threat visibility, helping security teams identify and mitigate risks before they escalate.
SIEM solutions centralize log management, generate compliance-ready reports, and monitor for policy violations in real time. This helps institutions meet standards such as FERPA, the GDPR, HIPAA, and other regional or grant-specific security requirements.
Yes. SIEM solutions use behavioral analytics and log correlation to detect unusual access patterns or data movements by authorized users, helping to prevent malicious or accidental insider threats.
Modern SIEM platforms can be tailored to the size and complexity of K-12 institutions. With automation, prebuilt rules, and managed SIEM services, even small IT teams can effectively monitor and respond to threats.
By correlating data from multiple sources and triggering automated alerts, SIEM allows IT teams to detect threats quickly and initiate rapid containment measures, significantly reducing MTTD and MTTR.
SIEM provides unified visibility across campus networks, cloud-based learning platforms, and remote devices, ensuring that suspicious activities—such as unauthorized access from unusual locations—are detected and addressed promptly.
Yes. SIEM continuously monitors research database access, detects unusual transfer patterns, and flags compliance violations, helping protect intellectual property from cyber espionage or theft.
Critical log sources include SIS and LMS access logs, Active Directory authentication logs, firewall logs, IDS and IPS logs, endpoint security logs, and cloud service activity logs. Monitoring these helps detect unauthorized access, suspicious activity, and policy violations.
Key factors include log coverage for education-specific systems, advanced threat detection capabilities, built-in compliance reporting, scalability, ease of integration, and vendor support. The SIEM solution should align with the institution's unique risk profile and resource constraints.