- Home
- SIEM capabilities
- Threat detection
- Insider threat management
Stay ahead of insider threats with Log360
An internal threat refers to a threat caused by someone from the inside of an organization who could potentially cause damage or steal data from them for their own financial gains. The primary cause of such threats is disgruntled employees.
Log360's insider threat management capabilities help spot such attacks within minutes by looking for abnormal user behavior , and mitigate them with the built-in incident response module.
Gain extensive insights into user behavior
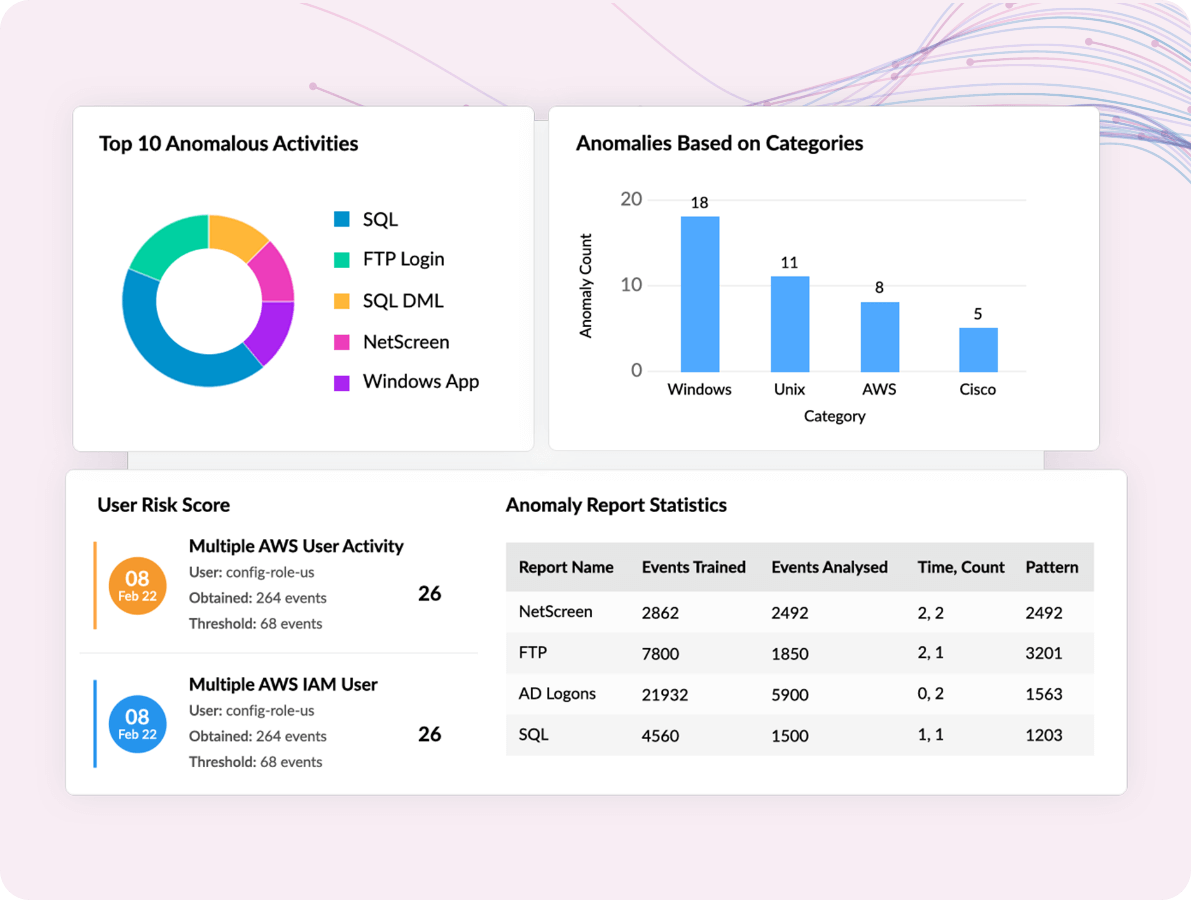
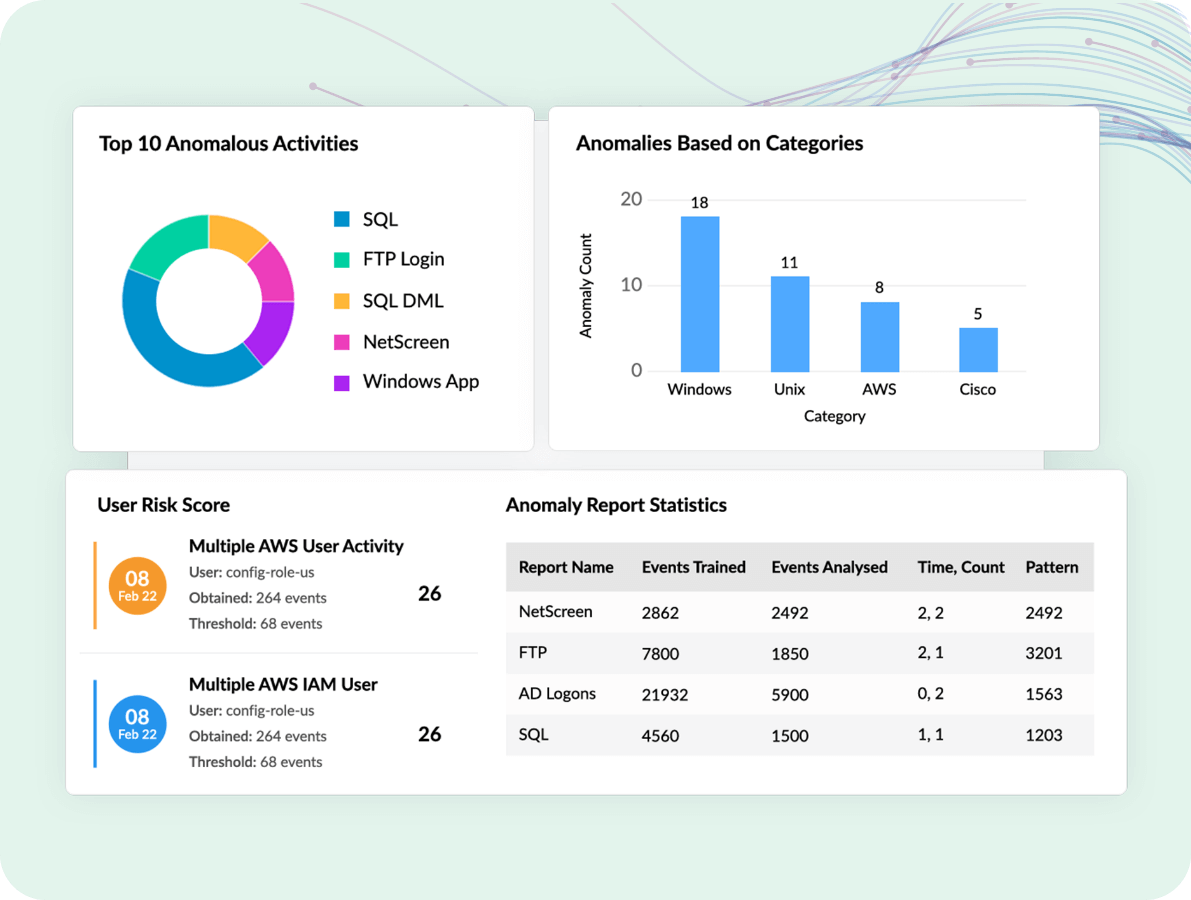
Conventional security solutions may protect your endpoints from threats, but they cannot detect advanced security threats from users and entities. Log360's user and entity behaviour analytics (UEBA) features are powered with machine learning to help detect insider threats effortlessly.
The solution creates a baseline by monitoring user behavior over a period of time. Any deviation from the baseline is flagged as an anomaly and a risk score is assigned. This helps the security team easily prioritize threats and mitigate them.
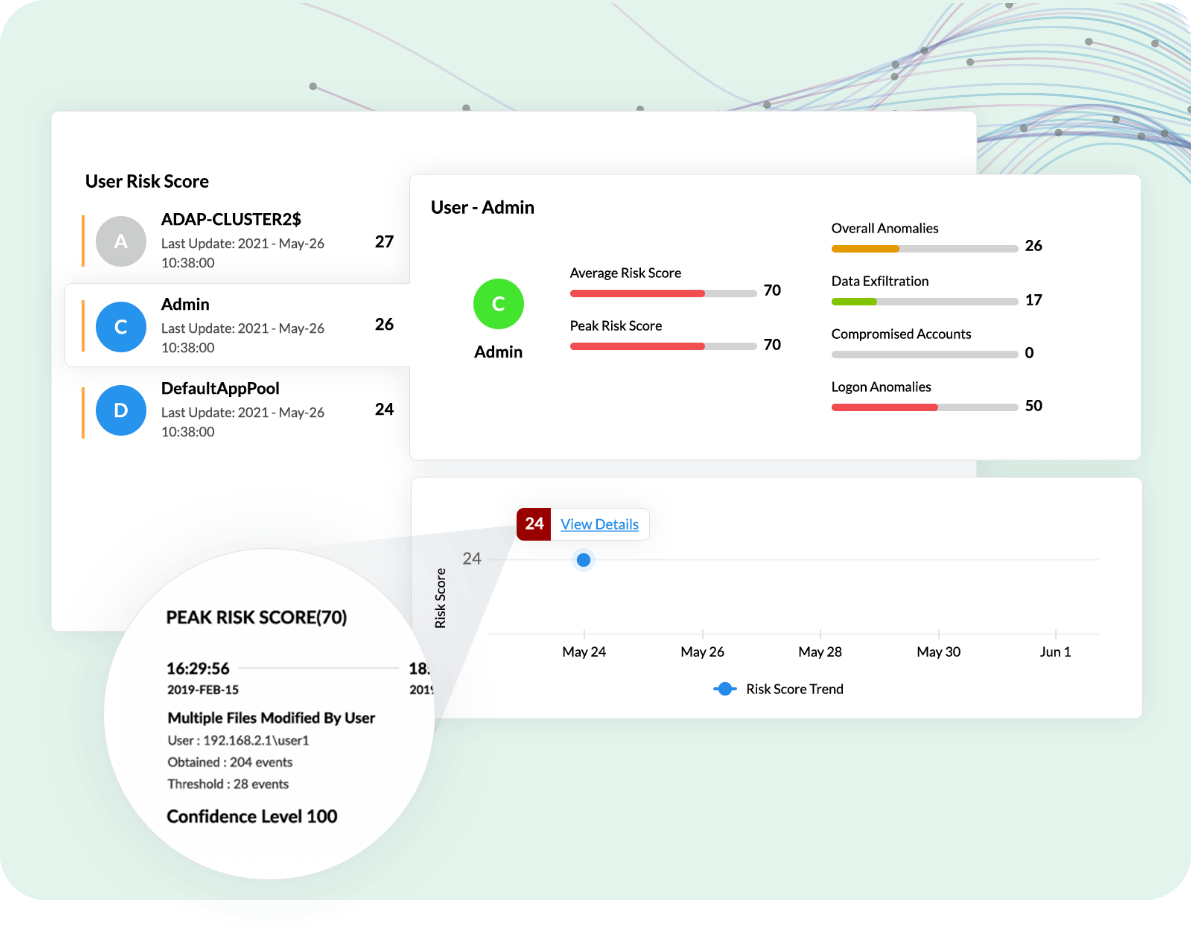
Identify indicators of account compromise
A user account can be compromised in several ways, including brute-force attacks, phishing emails, etc. Once an attacker has access to a user account, they can leverage the account to perform activities such as malicious software installation.
Log360, an insider threat management tool, constantly looks for indicators of compromise such as anomalous login activity, successive logon failures, malicious software installation, and more using machine learning and UEBA.
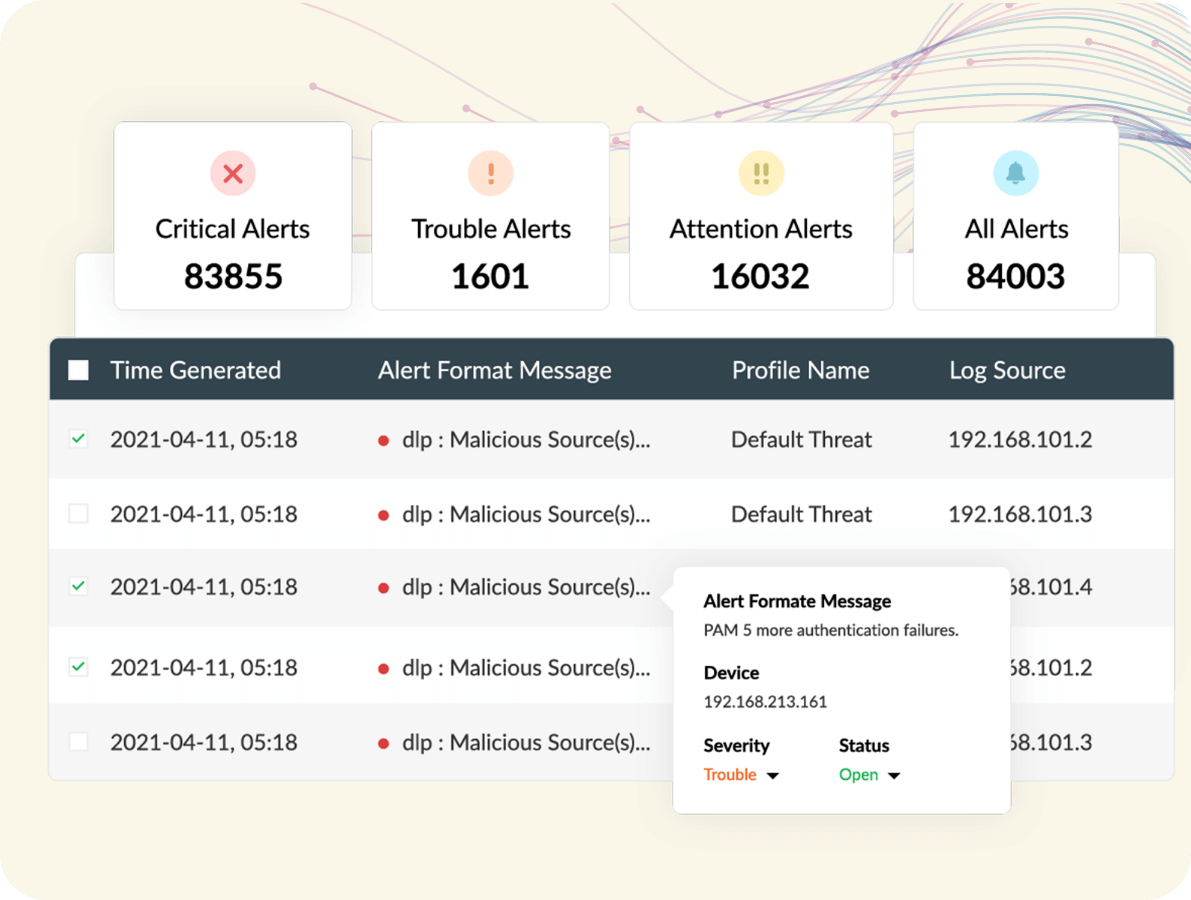
Get real-time alerts and notifications about suspicious activity
The initial moments of an attack are extremely crucial, and acting quickly can prevent your organization from substantial damage. With Log360's real-time alert system, you get instant notifications via email or SMS when any security incident occurs in your organization.
Log360 also comes with more than 1,000 predefined alert patterns that address a wide range of security use cases. Log360 categorizes alerts into three severity levels—Attention, Trouble, and Critical—that help you prioritize and mitigate high-risk insider threats.
Accelerate your incident response with intuitive dashboards and automated workflows
Incident response is an important step in mitigating threats. Log360's intuitive dashboard gives you in-depth information about each security incident in your organization and helps manage them. The security incidents are sorted by priority, source, and severity to help you keep track of each event from detection to resolution.
Log360's incident workflows can be automated to mitigate security threats. These workflows are automatically triggered when an alert is raised and act as an immediate response to a security incident before the intervention of a security admin. You can also create customized workflows that suit your organizations needs using the drag-and-drop interface.
Other reasons to consider Log360 for insider threat management
-
Informative threat feeds
Leverage threat feeds to discover malicious IPs, domains, and URLs.
-
Advanced threat analytics
Protect your organization from malicious intruders with advanced threat analytics.
-
Security of cloud data
Protect cloud data and cloud accounts from unauthorized access.


