What is lateral movement (TA0008)?
After gaining an initial foothold in a network, attackers rarely land where they need to be. The data they are after such as domain controllers, financial databases, backup systems, IP repositories lives on systems they cannot reach from their first compromised endpoint. Lateral movement is the process of bridging that gap: navigating through the network, system by system, until the attacker reaches targets with the access or data they need.
In the MITRE ATT&CK® framework, TA0008 (Lateral Movement) describes the techniques adversaries use to move through a network after establishing presence. These techniques range from abusing legitimate remote services that IT teams rely on daily—RDP, SMB, WinRM, SSH to reusing captured authentication material such as NTLM hashes and Kerberos tickets to authenticate as privileged users without ever needing a plaintext password.
MITRE ATT&CK TA0008 — Lateral Movement: Log360 maps 79 detection rules to this tactic across Windows, Active Directory, AWS, Microsoft 365, and network infrastructure. Primary techniques with built-in coverage include Remote Services (T1021) and Use of Alternate Authentication Material (T1550).
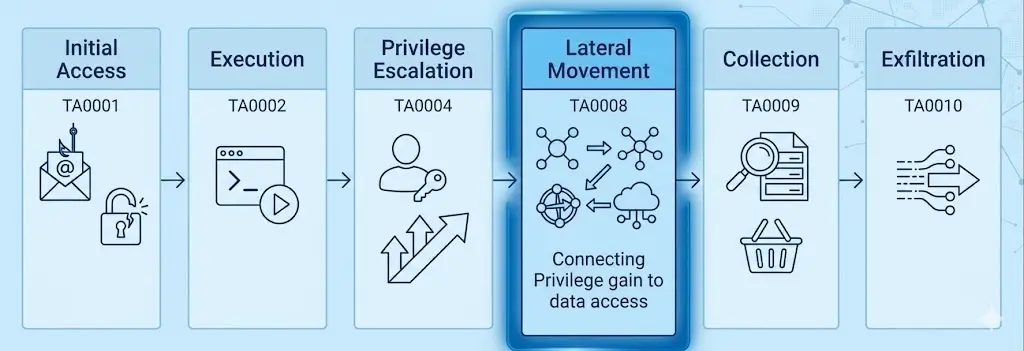
Lateral movement sits in the middle of the MITRE ATT&CK kill chain. It typically follows Privilege Escalation (TA0004)—attackers need elevated credentials before they can move effectively—and precedes Collection (TA0009) and Exfiltration (TA0011), the phases where the real damage occurs. Detecting lateral movement before it reaches its objectives is the highest-leverage intervention point in the entire attack lifecycle.
The lateral movement threat landscape
Lateral movement is not a theoretical concern. It is the technique that separates a contained compromise from a catastrophic breach. When attackers remain undetected during lateral movement, they reach domain controllers, disable security controls, and position themselves for ransomware deployment or large-scale data exfiltration. The business impact of late-stage detection is measured in millions of dollars and months of recovery.
The Mandiant M-Trends 2025 report records a global median dwell time of 10 days, meaning attackers have more than a week on average to perform lateral movement before detection. The CrowdStrike 2025 Global Threat Report documents an average adversary breakout time of 62 minutes from initial compromise to first lateral movement, with the fastest recorded breakout under two minutes.
Notable threat actors known for sophisticated lateral movement campaigns include:
- APT29 (Cozy Bear): The group responsible for the SolarWinds supply chain attack used pass-the-hash and ticket forgery extensively to move from compromised update servers to high-value targets across government and enterprise networks. Their lateral movement often remained undetected for months.
- APT38 (Lazarus Group): This financially motivated group routinely uses RDP and SMB-based lateral movement to propagate from bank employee workstations toward SWIFT systems and core banking infrastructure before triggering fraudulent transactions.
- Ransomware operators (Ryuk, LockBit, BlackSuit): Every major ransomware campaign requires lateral movement before payload deployment. Operators need domain admin or SYSTEM access on every target host, which requires moving to a domain controller via remote services. Without lateral movement, ransomware encrypts only the initial host. Organizations with dedicated ransomware detection capabilities are best placed to identify this lateral movement phase before payload deployment. The BlackSuit ransomware campaign and others like Ryuk (Ryuk ransomware profile) both follow this pattern: gain foothold, escalate, move laterally to the DC, deploy.
The advanced persistent threat landscape has made lateral movement faster, quieter, and more varied in technique. Defenders who rely on perimeter controls alone are fundamentally unprepared: by definition, lateral movement happens entirely inside the perimeter. Enriching detection with threat intelligence markedly accelerates triage by matching observed TTPs against documented threat actor profiles.
Techniques at a glance
Log360 provides built-in detection coverage for the two most commonly abused lateral movement techniques in enterprise environments:
| Technique | Description | Platforms | Log360 Coverage |
|---|---|---|---|
| T1021 — Remote Services | Adversaries use legitimate remote access protocols (RDP, SMB, WinRM, SSH, VNC, DCOM) to move between systems using valid credentials | Windows, AD, AWS, Network | 15 pre-built rules covering all 6 sub-techniques |
| T1550 — Use Alternate Authentication Material | Adversaries use captured NTLM hashes or Kerberos tickets (including Golden Ticket forgeries) to authenticate to remote systems without knowing the plaintext password | Windows, Active Directory | 3 pre-built rules; T1550.003 (Pass the Ticket) requires custom rules |
| T1570 — Lateral Tool Transfer | Adversaries transfer tools or other files between systems in a compromised network using SMB admin shares, remote execution utilities (PsExec), PowerShell remoting, SMB over QUIC (UDP 443), or cloud staging platforms such as SharePoint Online. | Windows, Sysmon, SharePoint Online (M365) | 4 pre-built rules |
| T1210 — Exploitation of Remote Services | Adversaries exploit vulnerabilities or misconfigurations in internal remote services — such as RDP (BlueKeep/CVE-2019-0708), WSUS (HTTP injection), SysAid ITSM, and Quick Assist — to execute code and move laterally without needing valid credentials. | Windows, Sysmon | 6 pre-built rules |
Log360 detection rules for TA0008
Log360 ships with pre-built correlation rules covering the primary TA0008 lateral movement techniques. The table below lists the highest-signal rules, sorted by severity:
| Rule name | Technique | Platform | Severity |
|---|---|---|---|
| RDP Session Hijacking Using tscon | T1021.001 — RDP | Windows | Critical |
| Pass the Hash Activity 2 | T1550.002 | Active Directory | Trouble |
| Psexec Execution | T1021.002 — SMB | Windows | Trouble |
| Copy From Or To Admin Share Or Sysvol Folder | T1021.002 — SMB | Windows | Trouble |
| PUA - CSExec/RemCom Default Named Pipe | T1021.002 — SMB | Windows | Trouble |
| HackTool - WinRM Access Via Evil-WinRM | T1021.006 — WinRM | Windows | Trouble |
| Execute Invoke-command on Remote Host | T1021.006 — WinRM | Windows | Trouble |
| HackTool - SharpMove Tool Execution | T1021.003 — DCOM | Windows | Trouble |
| NTLMv1 Logon Between Client and Server | T1550.002 | Windows | Trouble |
| AWS EC2 Instance Connect SSH Public Key Uploaded | T1021.004 — SSH | AWS | Trouble |
| Access To ADMIN$ Network Share | T1021.002 — SMB | Active Directory | Attention |
| Outgoing Logon with New Credentials | T1550.002 | Windows | Attention |
Note: This table shows a subset of Log360's TA0008 detection rules. Log360 ships 79 rules mapped to the Lateral Movement tactic across Windows, Active Directory, AWS, Microsoft 365, and network device platforms. Rules are continuously updated as new techniques are observed. For the complete rule library, visit the Log360 Detection Rules catalog.
Threat hunting beyond automated rules
Correlation rules catch known patterns. Threat hunting goes further: it looks for lateral movement that lacks a rule signature—whether because the attacker uses an uncommon technique variant, operates at low volume to avoid threshold-based rules, or operates during business hours when their activity blends with normal traffic.
Hunt 1: Workstation-to-workstation remote authentication
In legitimate enterprise networks, workstations almost never authenticate to other workstations. All workstation-to-workstation network logons (Event ID 4624, Types 3 or 10) where both source and destination are workstation-class machines (not servers, not jump hosts) are strong lateral movement indicators. In Log360, search for this pattern:
Adjust the source_type and destination_type fields to match Log360's parsed field names for your environment. A single workstation-to-workstation authenticated session outside business hours warrants immediate investigation.
Hunt 2: Service accounts authenticating to new resources
Service accounts have predictable, narrow authentication patterns: they log into specific servers to perform their function and nothing else. Any service account authentication to a system it has never previously accessed is an anomaly worth investigating as a potential PtH or compromised credential scenario. Log360's UEBA module automates this baseline comparison, but you can also hunt manually:
Compare the resulting destinations against a known-good baseline from the previous 30 days. New destinations for service accounts, particularly domain controllers and backup servers, should be triaged immediately. Log360's UEBA risk scoring automates this prioritization, surfacing high-risk accounts deviating from their access baseline.
Hunt 3: Lateral tool transfer patterns
Before executing on a target host, attackers often transfer tools via SMB or PowerShell. Look for executables or scripts appearing in administrative share paths outside normal software deployment windows. A log forensics search across file creation events combined with share access events exposes this staging pattern:
Any executable or script created via an admin share path that is not correlated with a known asset management or patching process represents potential attacker tool staging.
Response playbook
Immediate containment (first 30 minutes)
- Isolate the source host: Remove the originating workstation or server from the network. If host isolation is not possible immediately, disable the account used for lateral movement in Active Directory to stop ongoing movement.
- Force password reset for all affected accounts: Invalidate hashes by resetting passwords for every account that was either used in the lateral movement or was present in LSASS on the confirmed source host. For krbtgt, assess whether a double rotation is needed if Kerberos ticket abuse is suspected.
- Block the lateral movement protocols at the segment boundary: If lateral movement is confirmed between specific network segments, temporarily block RDP (3389), SMB (445), and WinRM (5985/5986) between those segments via firewall rules until the scope is determined.
Investigation and scoping (first 4 hours)
- Map all lateral movement hops using Log360's correlated logon timeline across all affected hosts.
- Identify the original breach point and determine what credentials were available there. A structured incident management process ensures each compromised host is tracked as a separate investigation thread.
- Enumerate all systems the attacker reached and assess whether persistence was established on each. Follow the MITRE persistence detection guide for indicators to check on each compromised host.
- Assess whether any high-value targets (domain controllers, PAM servers, backup systems) were reached and whether any changes were made.
Remediation by attack vector
- T1021 Remote Services: Implement network segmentation to restrict which hosts can initiate remote service connections. Deploy jump servers with PAM integration. Enforce SMB signing to prevent relay attacks. Detailed hardening steps are in the T1021 detection guide.
- T1550 pass-the-hash: Deploy Windows Defender Credential Guard to protect LSASS from hash extraction. Disable NTLMv1 and enforce NTLMv2 minimum. Implement LAPS to randomize local administrator account passwords across all workstations, eliminating the identical-local-admin-password attack path. Combine these controls with measures to prevent credential stuffing and lateral movement at the perimeter. Detailed hardening is in the T1550 detection guide.
T1570 — Lateral Tool Transfer: Restrict ADMINandC share access via Group Policy to designated jump servers only. This eliminates the core PsExec and SMB staging path. Disable SMB over QUIC unless explicitly required, as New-SmbMapping -TransportType QUIC has no legitimate routine use in most enterprises. For M365, apply Purview DLP policies to block executable uploads to SharePoint. Enforce SMB signing across all endpoints to prevent relay-based tool staging. Detailed hardening steps are in the T1570 detection guide.
T1210 — Exploitation of Remote Services: Migrate WSUS to HTTPS immediately, SharpWSUS and WSUSpendu require plain HTTP to inject malicious update payloads. Patch RDP continuously because BlueKeep (CVE-2019-0708) requires no credentials, only network access. Disable Quick Assist via Group Policy where it is not a sanctioned IT tool; where it is, correlate session events against open help desk tickets in real time. Micro-segment ITSM platforms like SysAid from the broader network. Treat any SafetyKatz or SharpHound alert as a critical incident requiring immediate host isolation — both indicate active credential harvesting and AD attack-path mapping. Detailed hardening steps are in the T1210 detection guide.
How this tactic connects to others
Lateral movement does not occur in isolation. It is the connective tissue of the attack chain, bridging earlier tactics that establish a foothold and elevate privileges to later tactics that achieve the attacker's objectives. Understanding these connections — and mapping them using the MITRE ATT&CK framework — helps security teams prioritize and communicate detection coverage.
What precedes lateral movement: Attackers almost always perform Privilege Escalation (TA0004) before effective lateral movement begins. A standard user account lacks the administrative credentials needed to access remote services and administrative shares. Without at least local administrator rights, pass-the-hash is limited and remote service access is restricted. Equally important is Credential Access (TA0006): pass-the-hash requires a prior hash capture event, typically through OS Credential Dumping (T1003). Detecting credential access attempts proactively limits the ammunition available for lateral movement.
What follows lateral movement: Once attackers reach their target systems through lateral movement, they shift to Collection (TA0009) to gather the data they came for, or to Impact (TA0012) if the objective is disruption or ransomware deployment. In ransomware scenarios, the final lateral movement hop is typically to the domain controller, from which the attacker deploys the ransomware binary to all domain-joined hosts simultaneously via GPO or PsExec. Detecting lateral movement to the DC is therefore the last viable intervention point before mass encryption begins. Refer to the incident detection and response guide for post-lateral-movement response procedures.
The privileged account as the lateral movement multiplier
Most lateral movement ultimately traces back to privileged account abuse. A single captured domain admin hash grants access to every Windows system in the domain. A compromised service account with delegated rights can pivot from helpdesk systems to financial servers without ever touching a domain controller. User and entity behavior analytics combined with event correlation are the primary detection mechanisms for catching this abuse, because the protocols themselves are legitimate—only the behavior is anomalous.
ManageEngine Log360 for lateral movement detection
Log360 maps 79 pre-built correlation rules to TA0008 Lateral Movement across Windows, Active Directory, AWS, Microsoft 365, and network device platforms. The integrated UEBA module builds behavioral baselines for remote access patterns, surfacing anomalous lateral movement that rule-based detection alone cannot identify. When lateral movement activity is detected, Log360's investigation dashboard correlates authentication events across source and destination hosts to map the complete lateral movement path in a single view.
Related content
Deep-dive detection guide for T1021 Remote Services: all six sub-techniques (RDP, SMB, WinRM, SSH, VNC, DCOM), 15 Log360 detection rules, investigation workflow for mapping the full lateral movement path, and hardening recommendations.
Comprehensive guide to detecting T1550 pass-the-hash and alternate authentication material abuse: how NTLM hash reuse works, why it bypasses password controls, Log360 detection rules, and Credential Guard deployment guidance.
Privilege escalation is the prerequisite for effective lateral movement. The TA0004 detection guide covers exploitation techniques, valid account abuse, scheduled task manipulation, and system process creation methods attackers use to obtain the credentials they need before moving laterally.
Need to explore ManageEngine Log360? Schedule a personalized demo
Frequently asked questions
What is lateral movement in cybersecurity?
Lateral movement refers to the techniques adversaries use to navigate through a network after gaining initial access, as catalogued under MITRE ATT&CK TA0008. Attackers move laterally to reach systems they could not access from their initial foothold: domain controllers, financial systems, backup infrastructure, and data repositories. The primary techniques include abusing legitimate remote services such as RDP and SMB (T1021) and reusing stolen NTLM hashes or Kerberos tickets (T1550).
How do I detect lateral movement in my environment?
Effective lateral movement detection combines rule-based correlation with behavioral analytics. Enable auditing for logon events (Event IDs 4624, 4648, 4776), network share access (5140, 5145), and service installation (7045) across all Windows systems and domain controllers. Deploy a SIEM like Log360 to correlate these events across hosts—lateral movement always involves multiple hosts and authentication events that, when analyzed in isolation, look benign. The addition of UEBA builds anomaly detection baselines that catch low-and-slow lateral movement that rule thresholds cannot detect.
What is the difference between lateral movement and privilege escalation?
Privilege escalation (TA0004) is about gaining higher permission levels on the current host—moving from a standard user to a local administrator or from local admin to domain admin. Lateral movement (TA0008) is about moving from one system to another within the network. In practice, they are tightly coupled: attackers escalate privileges to get credentials that enable lateral movement, then use lateral movement to reach new hosts where they escalate again. Detecting privilege escalation proactively limits the fuel available for lateral movement.
How long does it take attackers to start moving laterally after initial compromise?
According to the CrowdStrike 2025 Global Threat Report, the average adversary breakout time is 62 minutes from initial compromise to first lateral movement. The fastest observed breakout was under 2 minutes. This narrow window means organizations cannot rely on overnight analysis or end-of-day review cycles. Real-time detection with automated response, as provided by Log360's incident detection capability, is required to catch lateral movement before attackers reach high-value targets.
Does pass-the-hash require the attacker to know the account password?
No. Pass-the-hash (T1550.002) works by presenting the NTLM hash of a password directly to the Windows authentication protocol, which verifies the hash without requiring the plaintext. The attacker only needs the hash, which is extracted from compromised systems using tools like Mimikatz. This is why resetting a password after a pass-the-hash attack is effective—it changes the hash value, invalidating the captured artifact. However, attackers often repeat the hash capture immediately after a reset if they retain access to the source host, making host isolation the higher-priority containment action.
- What is lateral movement (TA0008)?
- The lateral movement threat landscape
- Techniques at a glance
- Log360 detection rules for TA0008
- Threat hunting beyond automated rules
- Response playbook
- How this tactic connects to others
- Related content
- Frequently asked questions



