- Home
- SIEM use cases
- Credential dumping tools
Detecting the presence of credential-dumping tools
In this page
Understanding the threat:
Credential-dumping tools such as Mimikatz allow attackers to extract plaintext credentials, hashes, or tokens from memory and local credential stores. Once credentials are harvested, attackers can move laterally, escalate privileges, and maintain persistence—all while blending into legitimate administrative activity. Continuous monitoring for the presence and usage patterns of credential-dumping tools is critical to detect and contain credential theft quickly.
Log360 enables the collection of web server, proxy, firewall, and Azure Web Application Firewall (WAF) logs. It then applies built-in detection rules, correlates web threat events with authentication and session activity, enriches outbound and inbound requests via threat intel feeds, and triggers alerts or workflows when a pattern consistent with XSS followed by session misuse is detected.
Category:
- External threat
Relevant MITRE ATT&CK® tactics and techniques
Tactic:
TA0006 – Credential Access
Techniques:
T1003 – OS Credential Dumping, T1003.001 – LSASS Memory, T1003.002 – Security Account Manager, T1070 – Indicator Removal on Host
Compliance mapping:
- CMMC SI.L3-3.14.7:
Supports detection of unauthorized code execution and security-relevant events, enabling timely identification of credential-dumping attempts.
- NIST SI-3 / IR-8:
Aligns with requirements to detect, analyze, and respond to malicious code and security incidents, including credential harvesting activities.
- CIS 10.4 (IG3):
Helps meet the requirement to detect unauthorized software and monitor endpoint activity for indicators of credential theft.
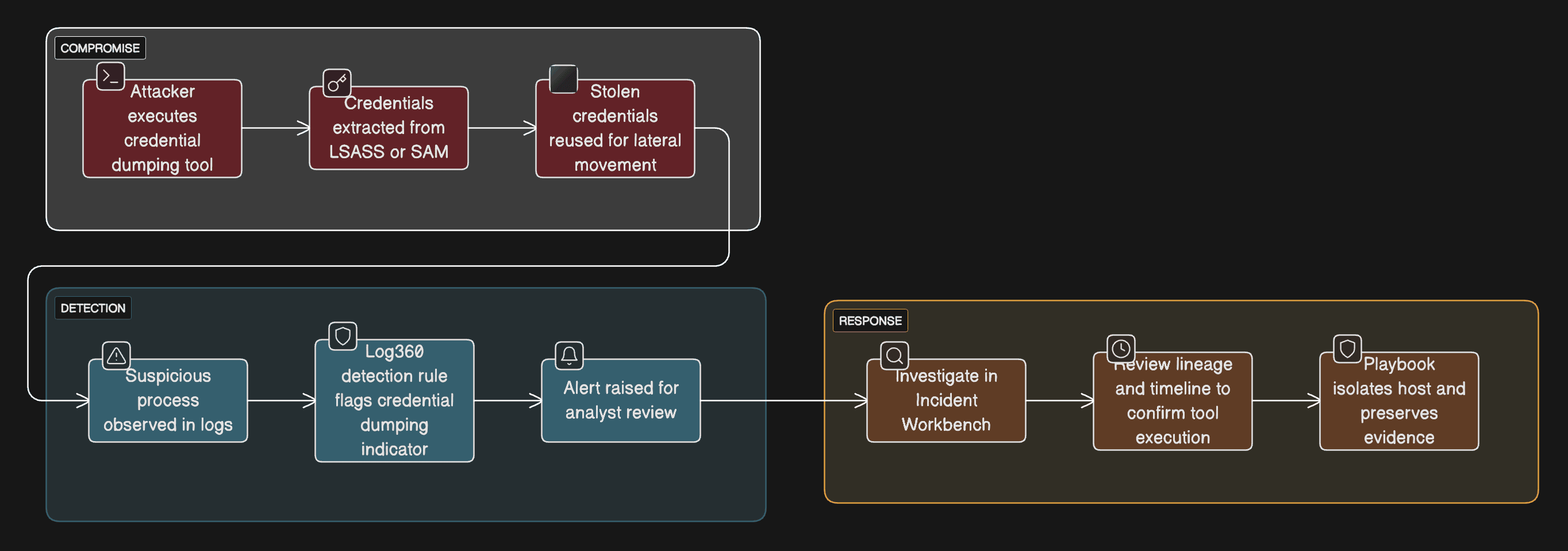
Scenario
A finance team's workstation shows signs of suspicious administrative activity. Investigation reveals that a credential-dumping tool was executed to extract account hashes from the Local Security Authority Subsystem Service (LSASS) memory. The attacker then used the harvested credentials to access other systems and services.
Investigation reveals that an attacker:
- Executed a credential-dumping binary or script on a compromised host.
- Extracted credentials from memory or local stores (e.g., LSASS, SAM).
- Reused harvested credentials for lateral movement and privilege escalation.
Scenario infographic:
Why this happens
- Tools like Mimikatz are effective and widely available, enabling rapid credential theft once an attacker gains sufficient privileges.
- Lack of process-level visibility (e.g., command line, parent process) and insufficient Sysmon or audit configuration makes detection harder.
What can go wrong
- Rapid lateral movement using legitimate credentials.
- Long-term persistence and stealthy exfiltration of sensitive data.
- Difficulty reconstructing the attack timeline if traces are removed.
Prerequisites
- Forward Windows Security logs and Sysmon event data (process creation, driver load, command-line events) to Log360.
- Ensure process creation auditing and command-line logging are enabled on monitored endpoints.
- Ensure critical servers and endpoints are added as log sources in Log360.
How to detect and investigate credential-dumping activity with Log360
Log360 provides targeted visibility and an investigative workflow to detect, validate, and respond to credential-dumping tool usage:
Collect process and command-line data
Ensure Sysmon and Windows process and command-line auditing are enabled so Log360 receives the necessary telemetry to spot suspicious process names and invocation patterns.
Detect tool indicators
The Mimikatz detection rule scans incoming process events for known indicators, like process names and command-line strings, and flags matches for analyst review.
Investigate in the Incident Workbench
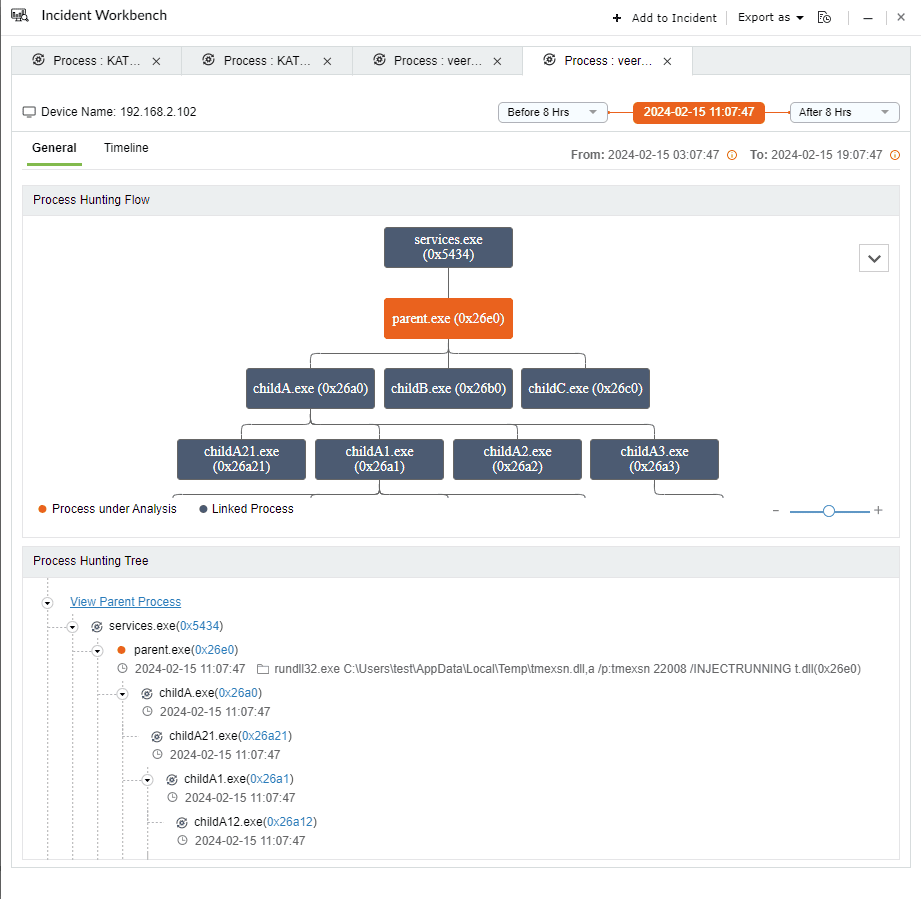
From the alert, invoke the Incident Workbench to examine the host’s process history, parent/child relationships, user context, and related events. Use the timeline to reconstruct execution order and to determine whether credential dumping led to lateral activity.
Leverage playbook
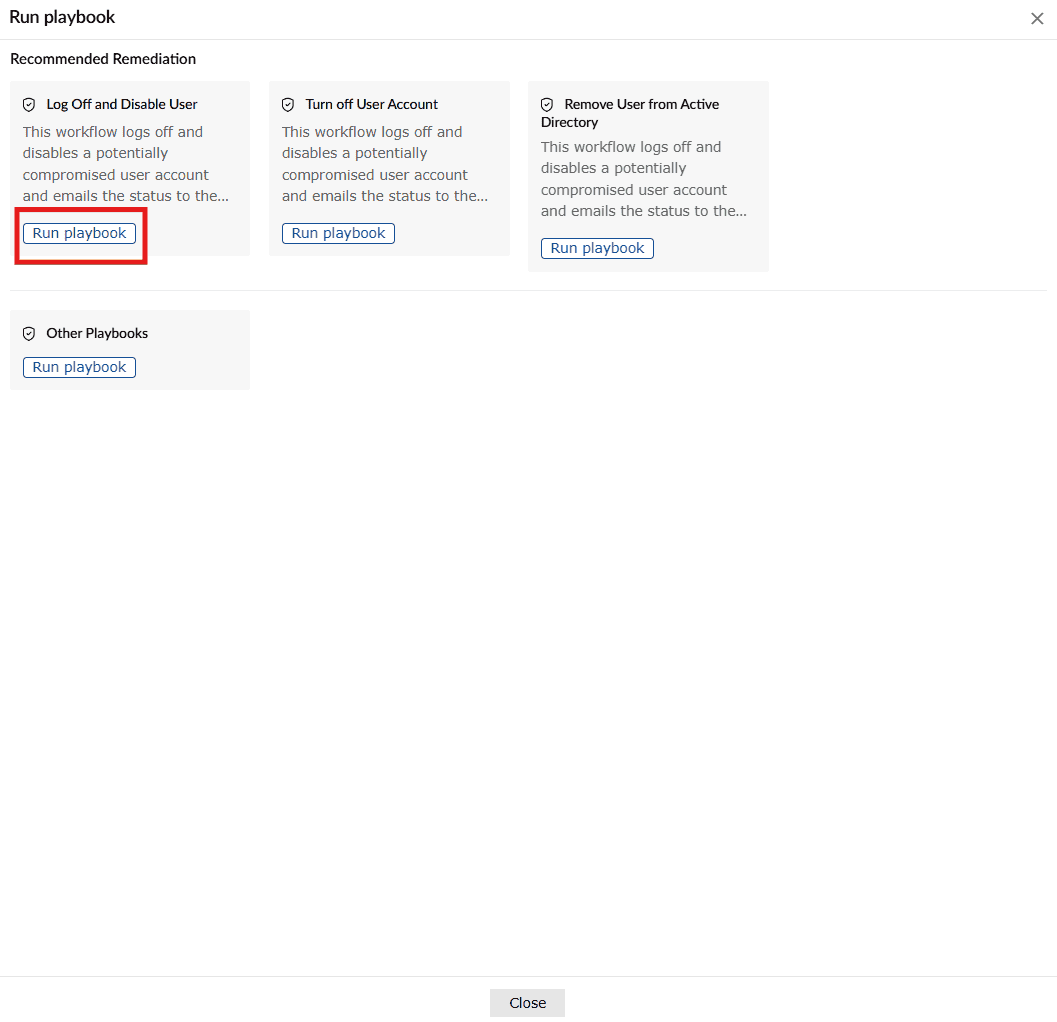
If confirmed malicious, use Log360's automated response workflows to terminate the offending process, isolate the host, or kick off remediation playbooks.
Preserve forensic evidence
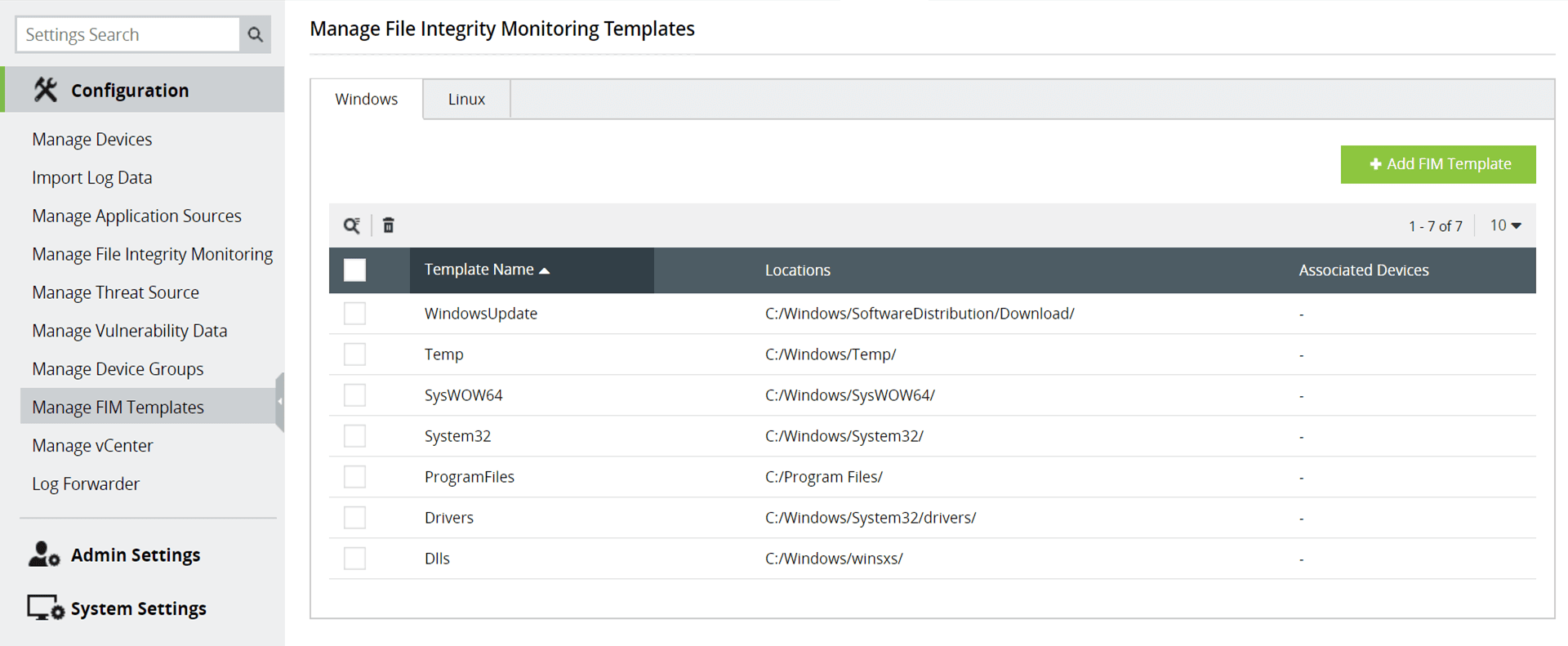
Log360’s retained event data and file integrity monitoring or integrity checks (where enabled) help preserve traces for impact analysis and recovery efforts.
Next steps
- Identification: Mark the alert as part of an incident or open a new incident. Assign to an analyst for investigation.
- Analysis: Use the Incident Workbench to determine scope (i.e., which accounts and systems were affected) and attempt to retrieve any deleted artifacts if available.
- Response: Execute workflows to terminate malicious processes and isolate compromised hosts; revoke or rotate credentials that may have been exposed.
- Remediation and hardening: Enforce least privilege, enable Sysmon and command-line auditing across endpoints, and review patching and EDR posture.
- Post-incident: Conduct impact analysis and update detection rules to reduce false positives and improve detection coverage.


