- Home
- SIEM use cases
- Firewall rule changes
Detecting unauthorized firewall rule changes
In this page
Understanding the threat - What is a firewall rule change?
A firewall rule change is any modification to the access control policies that govern network traffic. This includes adding a new rule to open a port, deleting a rule that blocks a threat, or modifying an existing rule to allow a new source IP address.
For enterprises, the firewall is the primary perimeter defense. A single unauthorized or malicious rule change can instantly create a gaping hole in this defense.
This can come from an attacker with a foothold to open a port and exfiltrate data, or even a well-meaning administrator that accidentally exposes a critical internal server (like a database or RDP server) to the entire internet.
Category:
- Internal threat
Relevant MITRE ATT&CK® tactics and techniques
This use case directly maps to the defense evasion tactic:
- TA0005—Defense evasion:
T1562.007—Disable or modify system firewall: This technique specifically covers adversaries modifying firewall policies to allow their malicious traffic inside systems.
Relevant compliance mapping
- CMMC CM.L1-3.4.1
- NIST CM-3 (Configuration Change)
- CIS 4.1 (IG1)
Scenario
A security analyst at an e-commerce company receives a data breach notification from an external party. The investigation begins, and the analyst backtracks the attack. They find that the attackers exfiltrated 50GB of customer data to an unknown IP address. The analyst is confused, as all nonstandard outbound ports are supposed to be blocked by the company's next-generation firewall.
Digging through raw firewall configuration logs, the analyst makes a shocking discovery: A rule was created at 2:15 am three weeks prior by a compromised junior IT administrator's account. The rule, named temp_test_01, allowed outbound traffic to be sent on port 4444 of the company's internal database server to the attacker's IP. The rule was active for only 45 minutes, just long enough for the data to be stolen. The same account then deleted the rule to cover its tracks.
The company's log management system collected this log, but it was buried among the millions of other traffic allowed and traffic denied logs. There was no specific alert for the firewall rule created event, so the entire breach went completely unnoticed in real time.
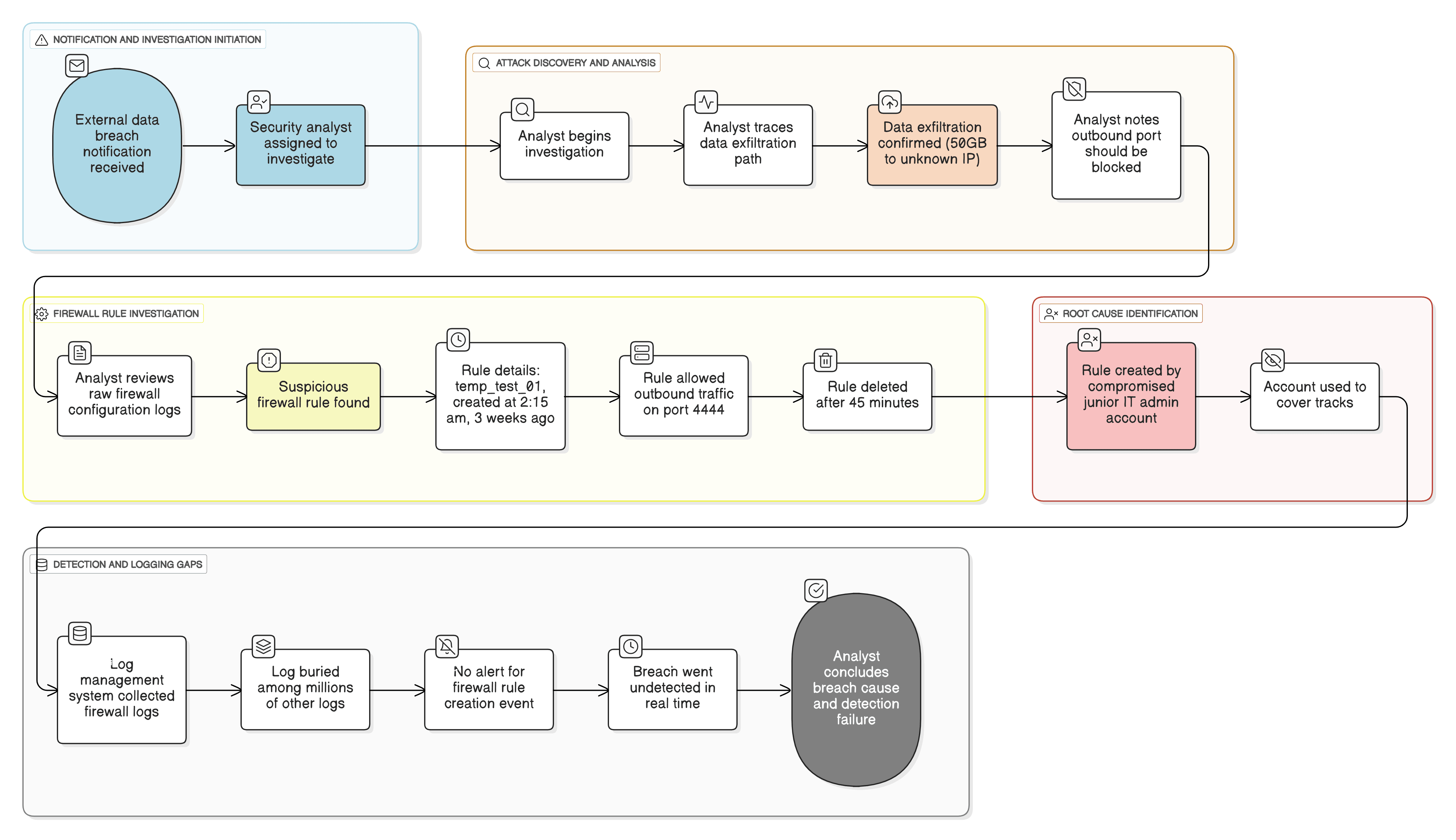
What went wrong?
- No real-time alerting: The most critical security change on the network, a new firewall rule, was logged but did not generate a high-priority alert.
- Lack of context: The system did not correlate the rule change with the user account's typical behavior. An admin adding a rule at 2:15am from an unusual workstation should have been a critical event.
- Temporary change: The attacker's tactic of creating and quickly deleting the rule was successful because the security team's monitoring was not in real time. The window of detection was missed entirely.
How firewall change monitoring helps
- Instant notification: A SIEM solution immediately parses and categorizes a firewall rule change log as a high-priority event, distinct from all other traffic logs.
- Provides accountability: A clear, immutable audit trail of who made what change and when is provided, essential for both security forensics and compliance.
- Enforces change management: Teams can compare the automated alert from the SIEM with their internal change management tickets. Any rule change that does not have a corresponding approved ticket is immediately treated as a critical, unauthorized incident.
- Compliance: Regulations like PCI DSS (Requirement 1.1.7) and SOX mandate that firewall rules are reviewed regularly. Real-time change monitoring automates this process and proves compliance to auditors.
Threats at the gate: Real-world trends
- Living off the land (LotL): Attackers increasingly use legitimate administrative tools, like the firewall's own management console, to achieve their goals. Modifying a firewall rule is stealthier than deploying malware and blends in with normal IT activity.
- Alert fatigue: Security teams are so overwhelmed with high-volume traffic logs that critical, low-volume configuration change logs (like a rule modification) are almost always missed without a dedicated use case to flag them.
Use case objective
To provide immediate, real-time visibility and alerting for all modifications to firewall rules (additions, deletions, and edits) to prevent unauthorized network access, detect defense evasion tactics, and maintain a continuous compliance posture.
Prerequisites
- Firewall devices must be configured to send both traffic (syslog) and audit/configuration logs to the Log360 server.
- Auditing must be enabled on the firewall's management plane to ensure all administrative changes are logged.
How to detect firewall rule changes with Log360
Detecting firewall rule changes in Log360 is achieved by enabling pre-built correlation rules for real-time alerts and using detailed audit reports for investigation.
Step 1: Enable security rules
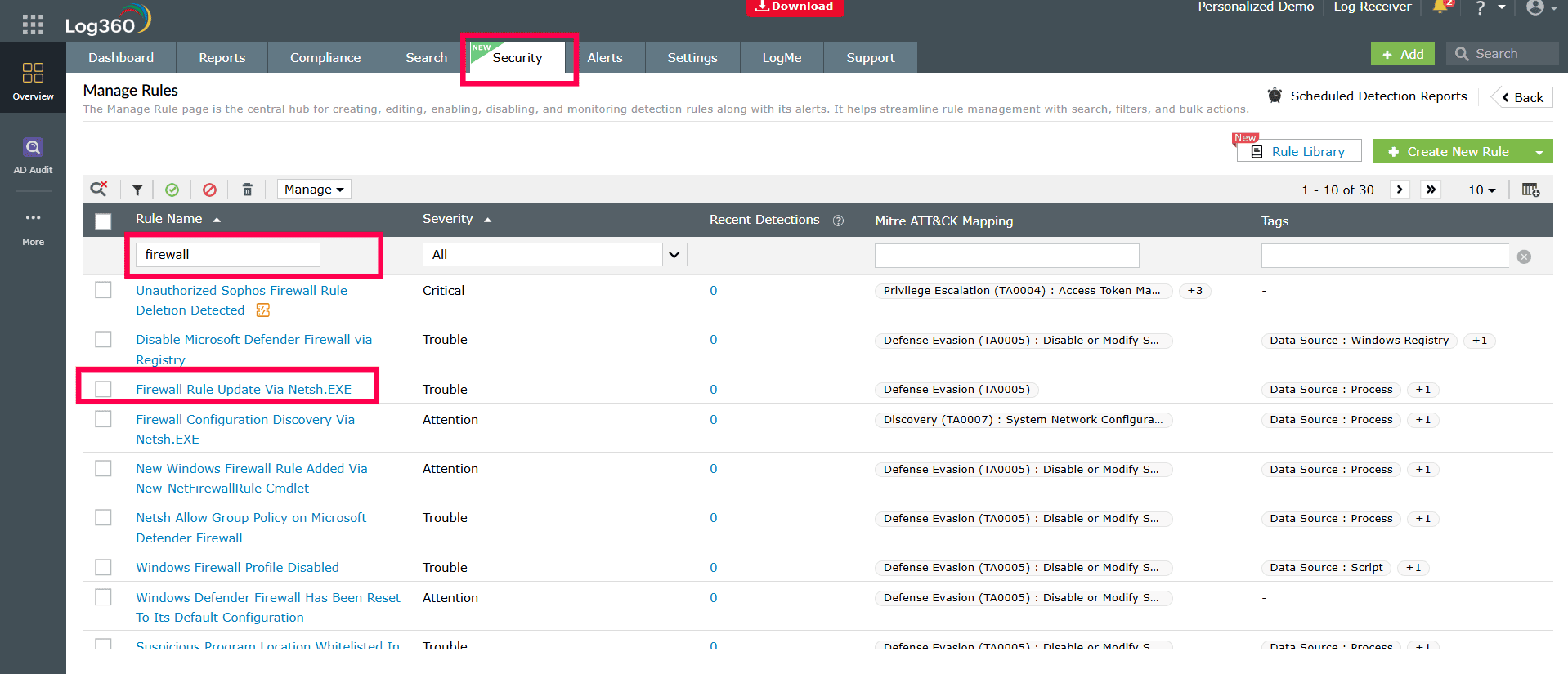
This is the primary, real-time detection method. You will activate the pre-built rules that are specifically designed to detect firewall policy changes.
- Navigate to the Security tab from the Log360 dashboard.
- Use the filters to find rules related to "Firewall" or by specific vendors (e.g., "Sophos," "Palo Alto").
- Activate the relevant rules you want to monitor.
- To ensure you are notified, click Manage on an active rule and configure an Alert Profile to send notifications via email, SMS.
Here are some of the key rules you can enable:
| Security Rule Name | Detection Criteria |
|---|---|
| Disable Microsoft Defender Firewall via Registry | Detects when a registry key (e.g., EnableFirewall) is modified, typically to 0, to disable the local host-based firewall. |
| Windows Firewall Disabled via PowerShell | Detects specific PowerShell commands (e.g., Set-NetFirewallProfile -Enabled False) used to programmatically disable the Windows Firewall. |
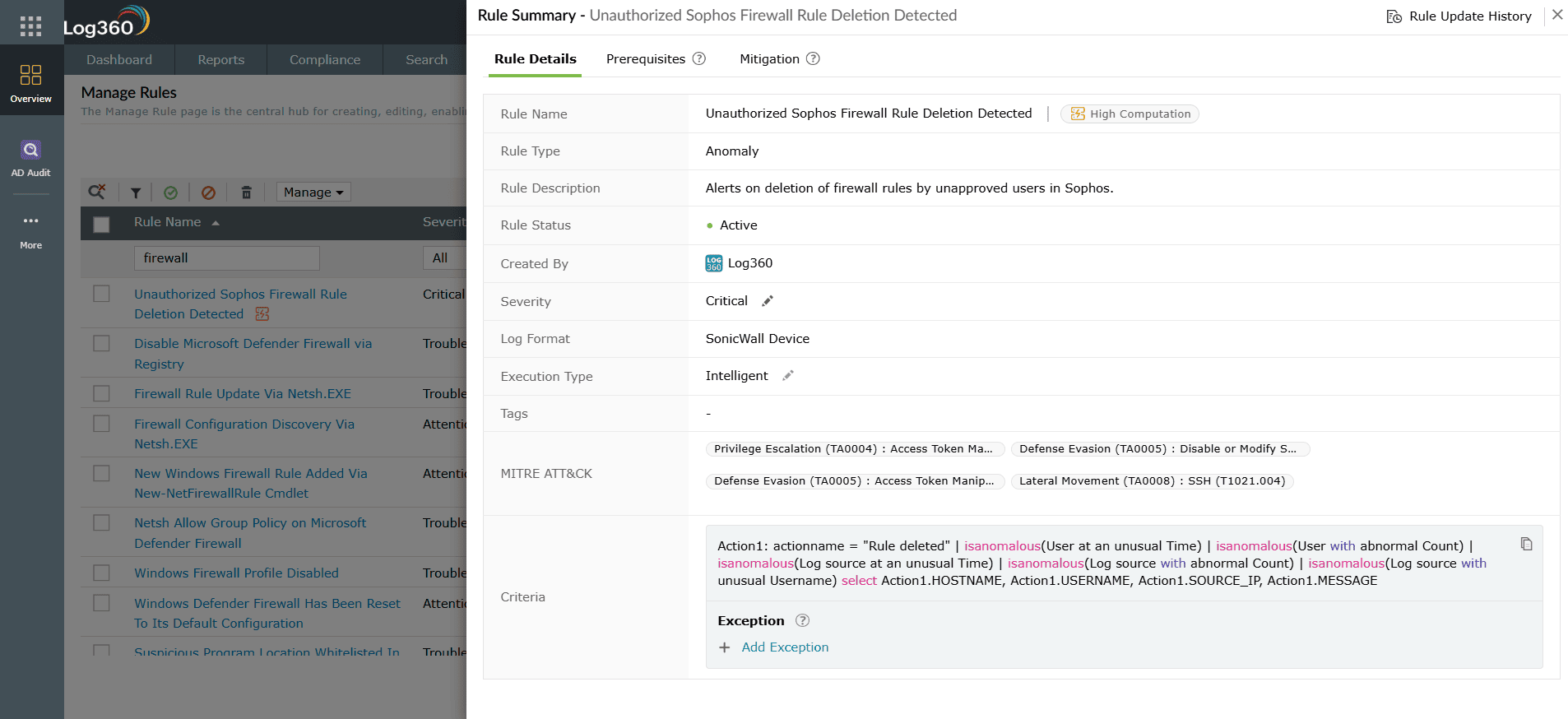
| Unauthorized Sophos Firewall Rule Deletion Detected | Generates an alert when a rule is deleted from a Sophos firewall, which could be an attacker covering their tracks or removing a defensive rule. |
| Unauthorized Firewall Rule Addition Detected | Detects when a new rule is created on a firewall. This is a critical rule for catching attackers who are opening ports for C2 or exfiltration. |
| Unauthorized Firewall Rule Modification Detected | Alerts when an existing firewall rule is edited. Attackers often modify a pre-existing "allow" rule to expand its scope (e.g., add their malicious IP). |
| Unauthorized Firewall Policy Modification Detected | Monitors for changes to an overall firewall policy (which may contain many rules), indicating a high-level administrative change that could have a wide impact. |
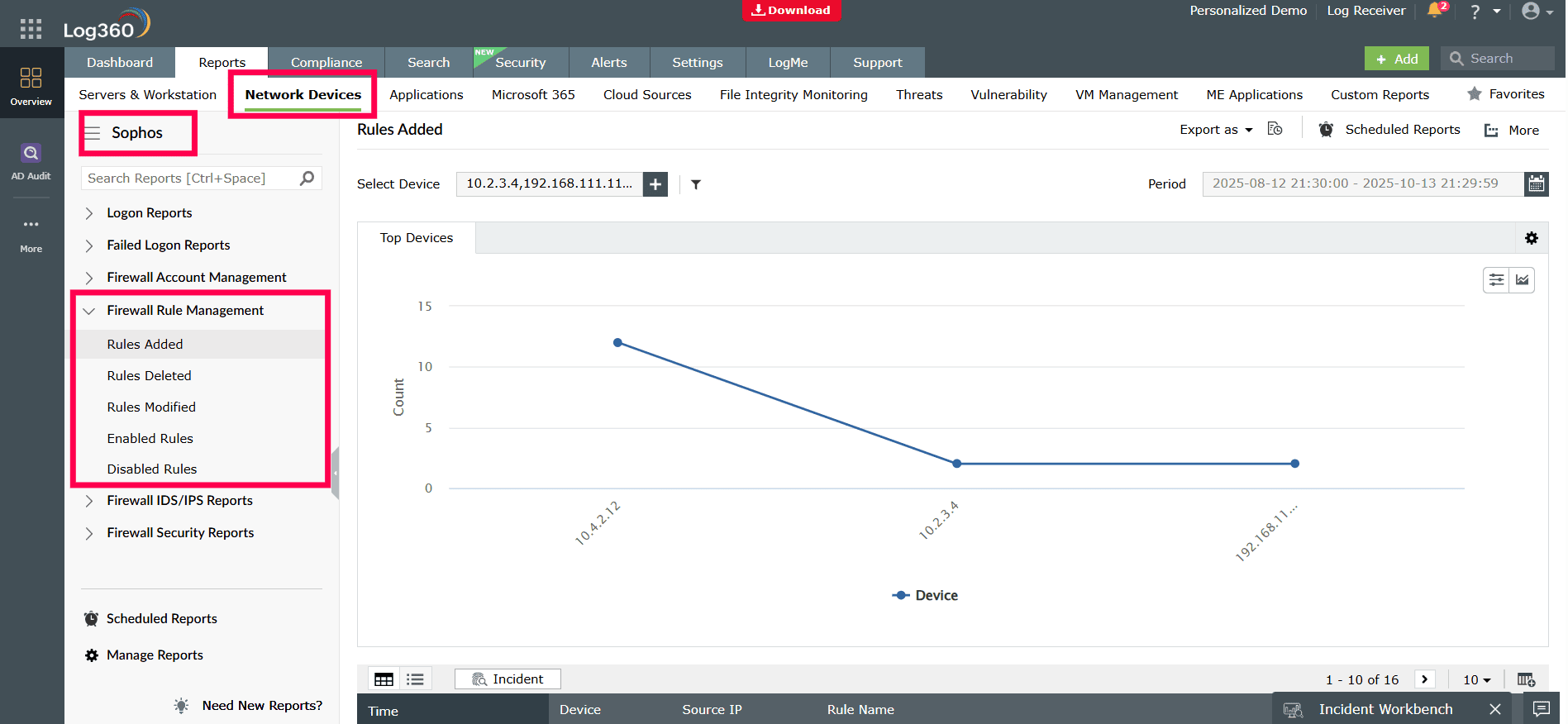
Step 2: Audit and investigate with reports
After an alert, or for routine auditing, you can use Log360's pre-built reports to get the full context of what changed.
- Navigate to the Reports tab > Network Devices > Select a specific vendor > Firewall Rule Management.
- Here, you can instantly view reports for Rule Added, Rule Deleted, Rule Modified, and more. These reports provide the full audit trail for investigation, including the username who made the change, the admin's source IP, the time of the change, and the exact rule details.
Next steps
- Create automated workflows: Configure Log360 to automatically create a high-priority ticket in your help desk system for every firewall rule change.
- Schedule compliance reports: Automate a weekly report of all firewall rule changes to be sent to the network and security managers for review, satisfying PCI DSS and other compliance requirements.


