- Home
- SIEM use cases
- Impossible travel
How to detect impossible travel activity
In this page
Understanding the threat:
Impossible travel refers to a scenario where a user’s account logs in from two distant geographical locations within an unrealistically short time frame. This often indicates compromised credentials, session hijacking, or the use of anonymizing tools such as VPNs or proxies to mask unauthorized access. Detecting these anomalies helps identify potential breaches before attackers can move laterally or exfiltrate data.
Category:
- External threat
Relevant MITRE ATT&CK® tactics and techniques
Tactics:
TA0001 – Initial Access, TA0002 – Execution, TA0003 – Persistence
Techniques:
T1078 – Valid Accounts, T1027 – Obfuscated Files or Information, T1566 – Phishing
Compliance mapping:
- CMMC AC.L2-3.1.20:
Supports the identification of anomalous remote access by detecting logins from geographically distant locations that cannot occur legitimately, helping enforce secure remote access controls.
- NIST AC-17 (Remote Access):
Aligns with requirements to monitor, analyze, and control remote access by identifying suspicious sign-ins, impossible travel events, and unauthorized location-based access attempts.
- CIS 6.3 (IG2):
Helps meet the control requirement to detect abnormal authentication patterns, including improbable logins, and provides visibility into unauthorized remote access behavior.
Scenario explanation:
A multinational consulting firm with employees in multiple regions notices logins to its cloud environment from Mumbai and Frankfurt within two minutes—both using the same user credentials.
Scenario infographic:
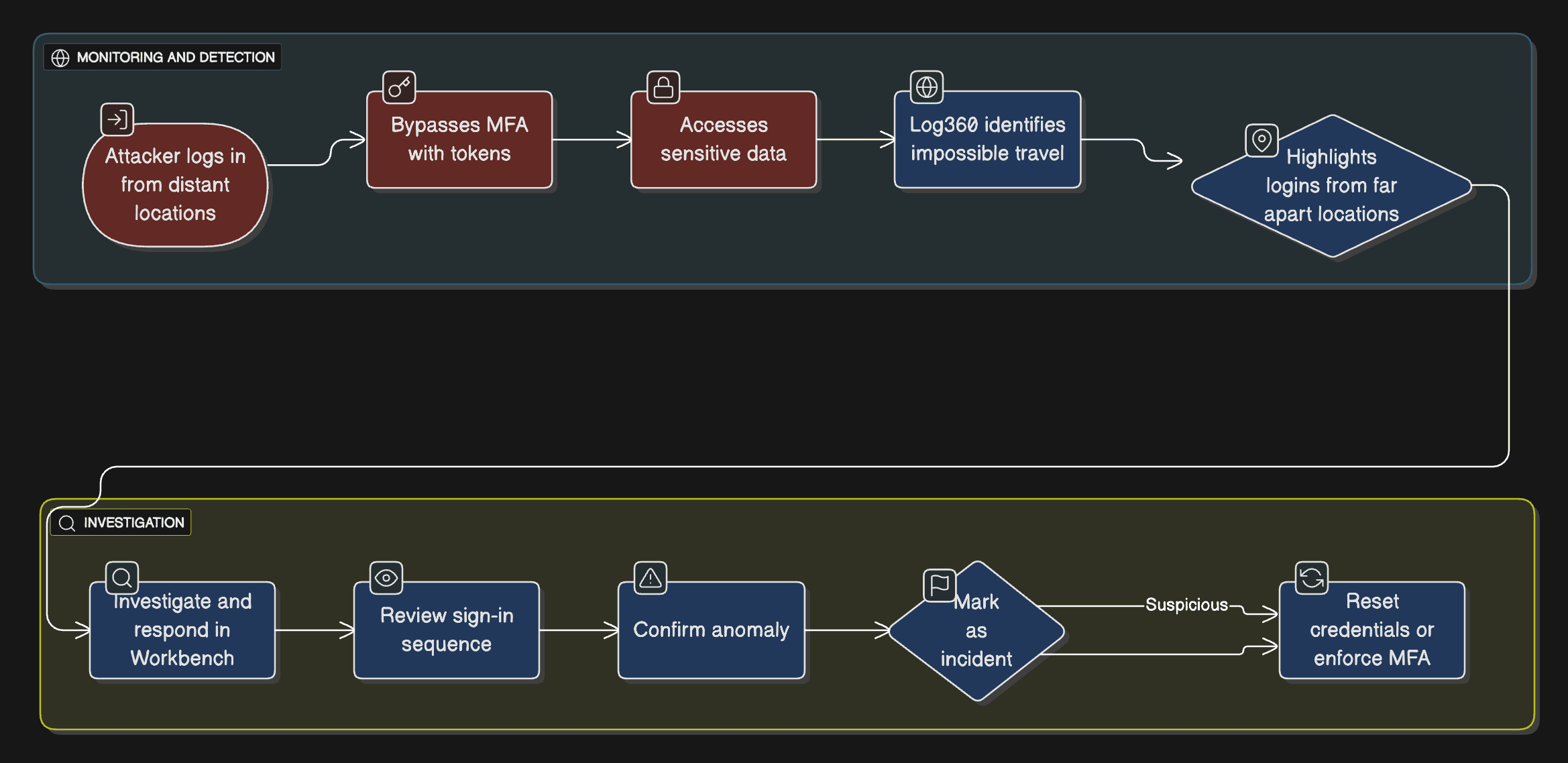
Further investigation reveals that an attacker:
- Used stolen credentials obtained through phishing to access the account from a remote IP.
- Attempted to bypass MFA using session tokens and device spoofing.
- Accessed sensitive files and modified permissions for data exfiltration.
Why this happens:
- Credential theft and token reuse enable attackers to authenticate as legitimate users.
- Lack of geolocation-based correlation across authentication logs.
- Overlapping VPN or proxy use masks real login origins.
What can go wrong:
- Unauthorized access to confidential business data.
- Lateral movement across linked cloud applications.
- Breach of compliance due to exposure of customer or financial data.
The hunt: Real-life threats
Microsoft 365 Credential Theft (2023): Attackers used stolen tokens to log in from different countries within minutes, bypassing MFA and accessing SharePoint data.
Okta Support System Breach (2023): Threat actors accessed customer data after authenticating from geographically improbable locations, exploiting stolen credentials.
Prerequisites:
- Forward authentication logs from Active Directory, Entra ID (Azure AD), and Microsoft 365 to Log360.
- Ensure sign-in logs include IP address, timestamp, and location metadata.
How to detect impossible travel activity with Log360:
1. Monitor login activity:
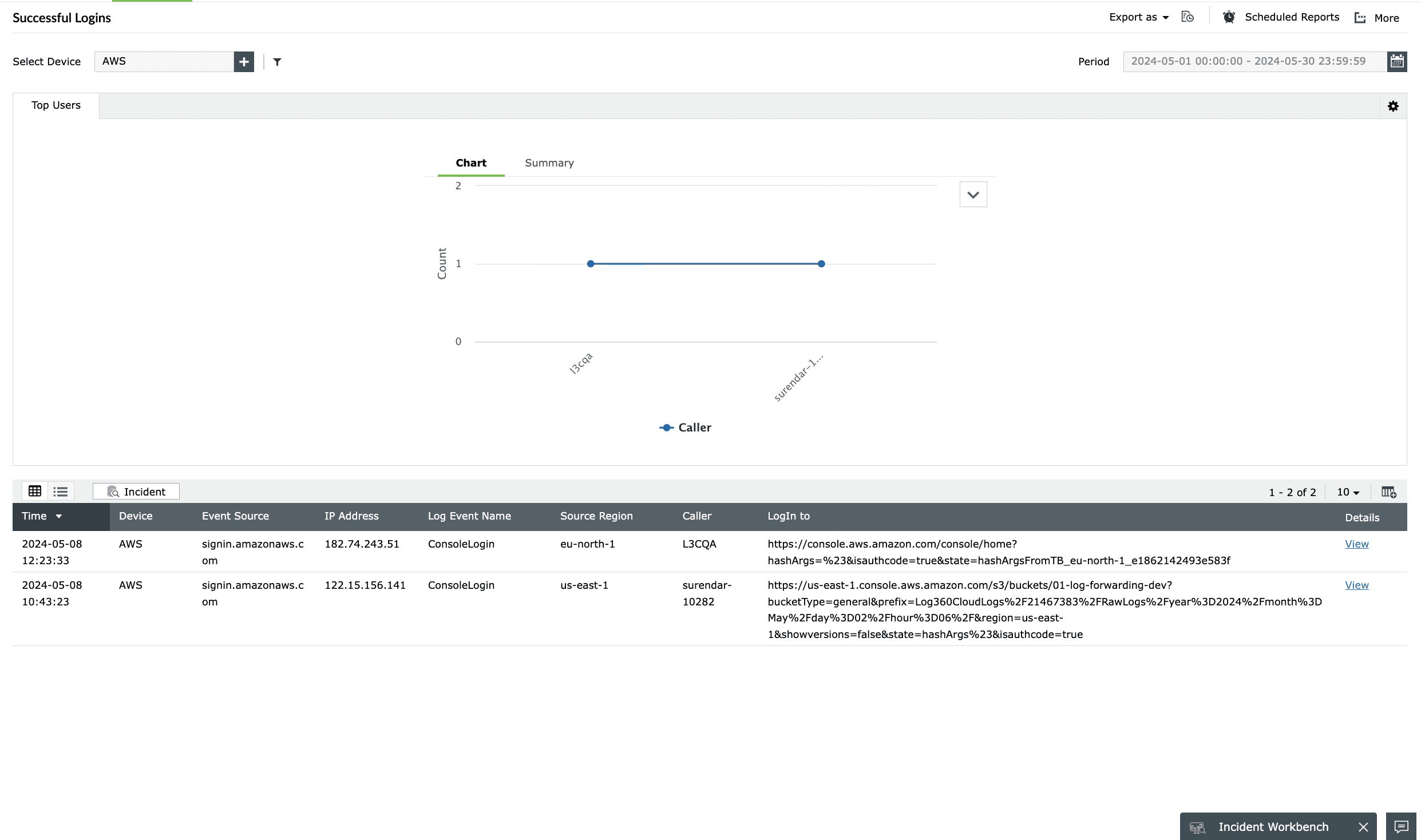
Log360 continuously collects authentication data from VPNs, Active Directory, and cloud applications to establish a baseline of typical user locations and login times. The consolidated sign-in data helps establish user location trends and normal access behaviors.
2. Detect location-based anomalies:
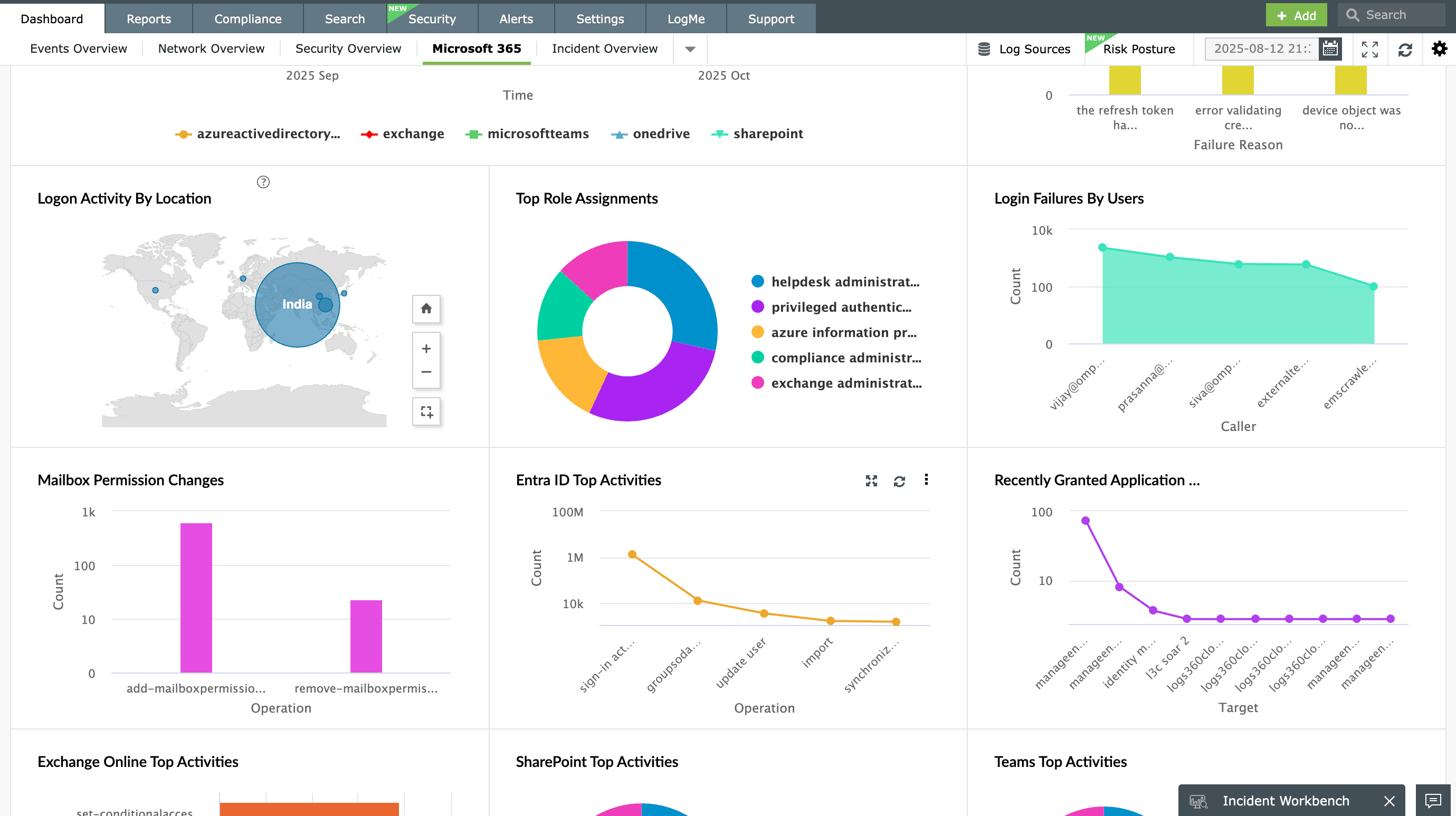
Log360 correlates sign-in activity across environments and highlights anomalies where logins occur from distant geographic locations within an improbable timeframe. These deviations are surfaced in dashboards and reports for analyst review, enabling faster identification of suspicious access patterns that could indicate credential misuse.
3. Investigate with Incident Workbench:
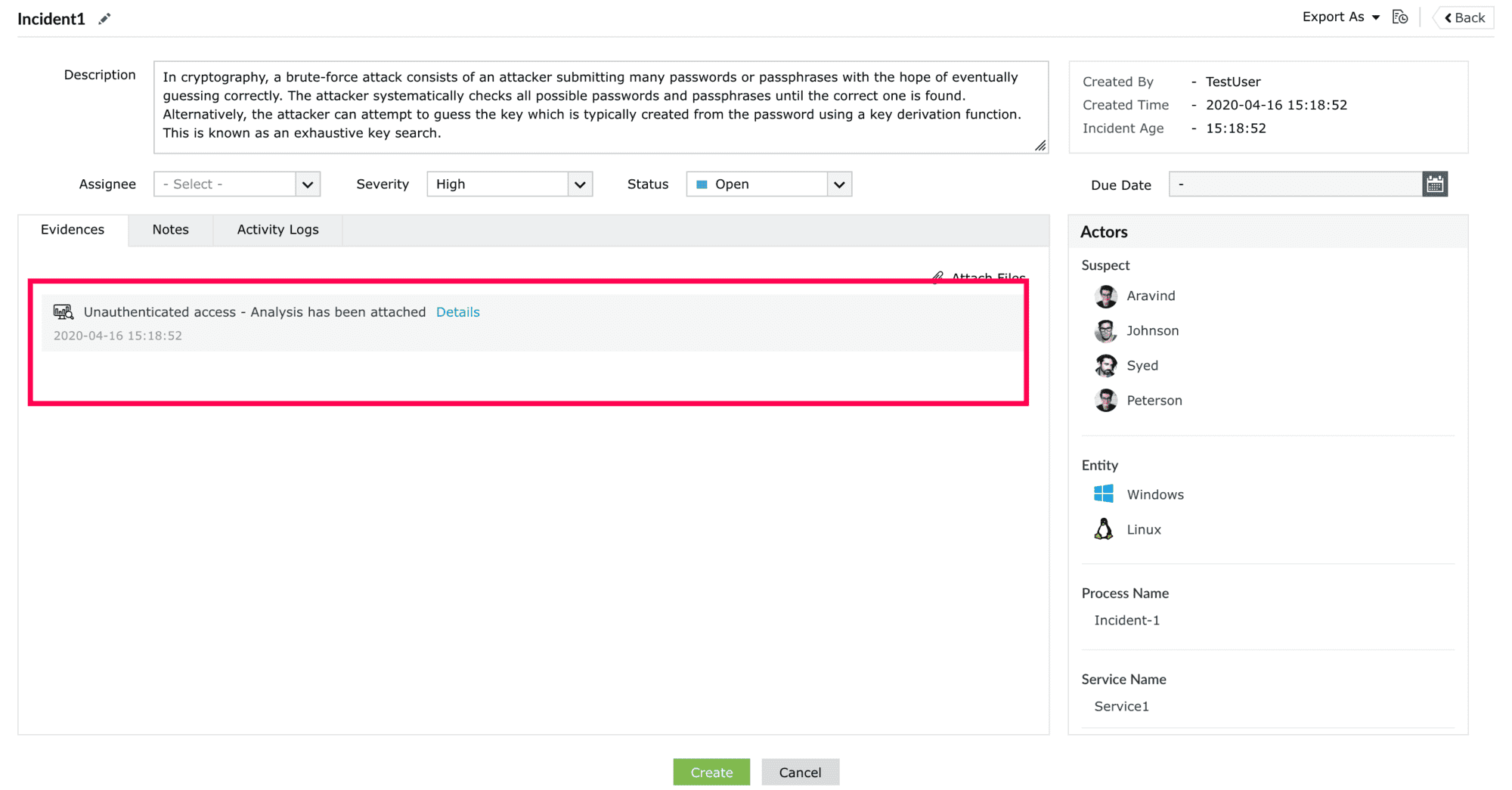
From the alert or report, analysts can invoke the Incident Workbench to investigate the suspicious sign-ins in detail. Here, they can review related authentication activities, analyze the event sequence, and validate whether the travel pattern is legitimate. If confirmed suspicious, the activity can be marked as an incident directly from the workbench and assigned to the appropriate analyst or administrator for further action, such as enforcing MFA, resetting credentials, or terminating active sessions.
4. Analyze and respond with Zia Insights:
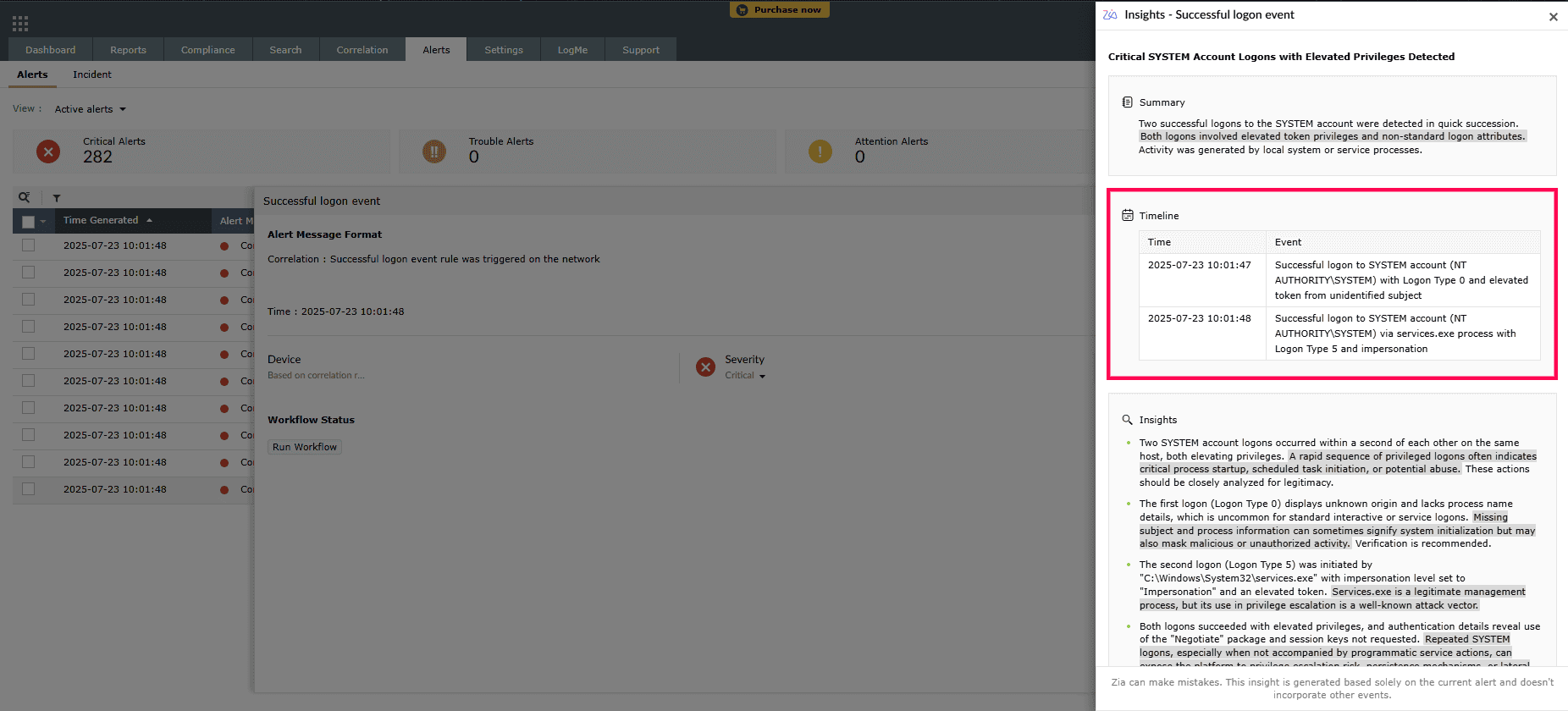
Zia Insights automatically maps the event to relevant MITRE ATT&CK® techniques, providing contextual insights, affected users, and a summarized attack chain. Analysts can use these insights to determine impact, confirm compromise, and take immediate remediation actions such as session termination or credential reset.
Next steps
- Enforce conditional access and geo-fencing policies.
- Mandate MFA for all remote and cloud logins.
- Educate users about phishing and credential hygiene.
- Review impossible travel alerts periodically to refine thresholds and minimize false positives.


