- Home
- SIEM use cases
- MFA Bypass and Fatigue Detection
How to detect MFA bypass and fatigue attacks
In this page
Threat snapshot
Multi-factor authentication was supposed to be the answer to credential-based attacks. And for a long time it was. Then attackers adapted. Today the most effective identity attacks in enterprise environments do not defeat MFA by cracking it; they route around it entirely, or they use it against the user.
MFA fatigue, also called MFA push bombing, exploits the design of push-based authenticators. The attacker has a valid username and password, typically obtained through phishing or credential stuffing. They initiate repeated authentication requests, each of which sends a push notification to the victim's phone. The victim receives one, two, five, twenty push requests in rapid succession. Some users approve one by accident. Some approve one out of frustration. Some approve one because they assume it is a technical glitch. The attacker's goal is not to crack the MFA system; it is to exhaust the user's attention and patience until they click approve.
Beyond fatigue attacks, several other bypass paths have become operationally significant: Temporary Access Pass (TAP) creation by compromised admins, Conditional Access policy modification to weaken or disable MFA requirements, and PIM role escalation to gain standing access that bypasses standard MFA enrollment checks. Each of these attacks leaves a distinct audit trail in Microsoft 365 and Azure AD logs, provided those logs are being collected and monitored.
This page covers all three bypass approaches, maps each to Log360's detection rules, and provides the investigation workflow for responding when these rules fire.
MFA bypass and fatigue, at a glance
| Severity | Critical |
| Category | Identity & Access |
| Attack variants covered | MFA fatigue (push bombing), Temporary Access Pass abuse, Conditional Access policy tampering, PIM role escalation, risky sign-in with device registration, authentication method modification |
| MITRE ATT&CK tactics | TA0006 (Credential Access), TA0001 (Initial Access), TA0003 (Persistence), TA0004 (Privilege Escalation), TA0005 (Defense Evasion) |
| MITRE techniques | T1621 (MFA Request Generation), T1078.004 (Valid Accounts: Cloud Accounts), T1556.006 (Modify Authentication Process: MFA), T1548 (Abuse Elevation Control Mechanism), T1098 (Account Manipulation) |
| Platforms covered | Microsoft 365, Azure AD (Microsoft Entra ID) |
| Log360 detection rules |
|
| SOC maturity level | Level 2 (investigation) |
| Compliance mapping | NIST CSF PR.AC-7, PCI-DSS 8.4, HIPAA Section 164.312(d), ISO 27001 A.9.4.2 |
How MFA bypass attacks work
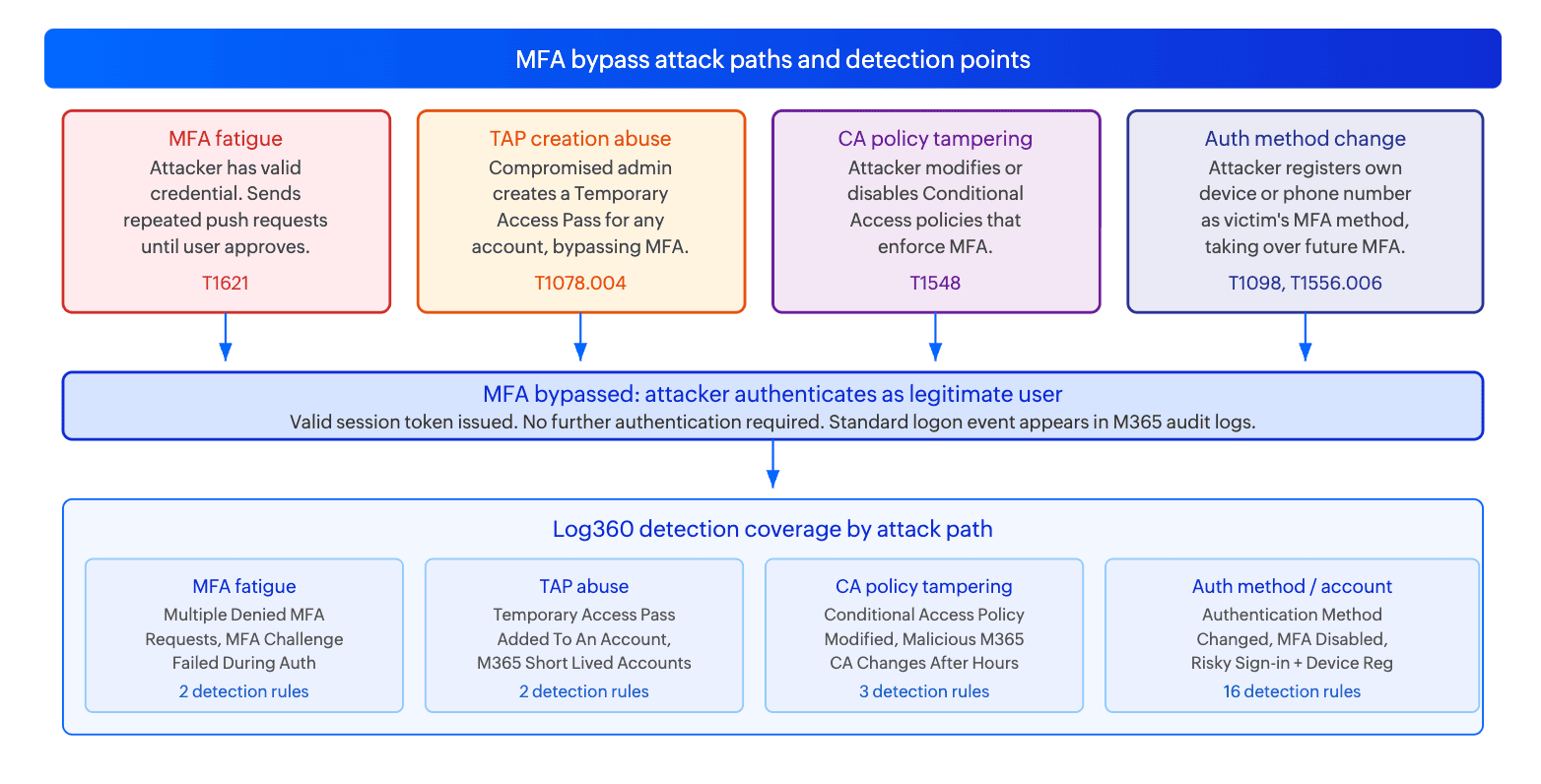
There is no single MFA bypass technique. Attackers choose their approach based on what they already have (a credential, an admin account, helpdesk access) and what the target organization's MFA configuration looks like. The diagram below shows the four most operationally significant paths.
MFA fatigue (push bombing) - T1621
The attacker possesses a valid M365 username and password, obtained through phishing, credential stuffing, or password spraying. They initiate authentication repeatedly in rapid succession. Each initiation sends a push notification to the user's registered MFA device. The volume of requests is intentional: the goal is to saturate the user's notification feed until they approve one, either by mistake, fatigue, or the assumption that the requests are a system error.
The attack is particularly effective after hours, on weekends, or during high-stress periods when users are less likely to scrutinize authentication prompts carefully. Some operators combine the push flood with a concurrent phone call to the victim, impersonating IT support and asking the user to "approve the pending notification" to resolve a fabricated account issue. The M365 audit log records each denied push as a distinct event; a burst of denied MFA requests from the same user within a short time window is the primary detection signal.
Log signals: M365 sign-in log entries showing MFA requests with result "MFA denied" or "MFA failed" in rapid succession for the same user, particularly from a new or unrecognized IP address.
Temporary Access Pass (TAP) creation abuse - T1078.004
A Temporary Access Pass is a time-limited, PIN-based credential in Azure AD that allows authentication without MFA. It is designed for legitimate use cases such as onboarding new employees or recovering access for accounts that have lost their MFA device. However, a compromised admin account can create a TAP for any account in the tenant, giving the attacker a credential that bypasses MFA entirely for the duration of the TAP's validity window.
TAP abuse is operationally efficient from the attacker's perspective: a single compromised admin account can generate TAPs for dozens of high-value accounts, each giving a fresh, MFA-bypassing access window. The TAP creation event is logged in the Azure AD audit log and is the earliest detection point for this attack. Once a TAP has been created and used, the attacker's subsequent authentication uses the TAP credential and leaves no MFA failure events at all.
Log signals: Azure AD audit log event "Add Temporary Access Pass method" for any account, especially when performed by an account that does not typically perform administrative identity management actions, or when multiple TAPs are created in a short time window.
Conditional Access policy tampering - T1548
Conditional Access policies in Azure AD define the conditions under which MFA is required for authentication: specific user groups, application types, network locations, device compliance states, and sign-in risk levels. An attacker with sufficient privileges can modify these policies to exempt their access from MFA requirements: adding their IP to a trusted named location, weakening the conditions under which MFA is enforced, or disabling a policy that previously required MFA for all external access.
The policy change itself is logged as an audit event in M365, and the subsequent authentication attempts that would previously have triggered an MFA prompt now succeed without one. The combination of a Conditional Access policy change followed by a successful authentication from a previously blocked or MFA-required context is a high-confidence indicator of this attack. Notably, attackers often make these changes outside business hours to reduce the probability of a real-time alert being acted upon.
Log signals: M365 audit log operation "Update Conditional Access Policy", "Add Conditional Access Policy", or "Delete Conditional Access Policy" performed by an account without a recent change management record, especially outside business hours.
Authentication method modification and account manipulation - T1098, T1556.006
Rather than bypassing MFA in the moment of authentication, this approach modifies the victim's registered MFA methods to substitute the attacker's device for the victim's. The attacker adds their own phone number or authenticator app as the victim's MFA method, then removes the victim's. From that point, any authentication by the victim that triggers a push notification goes to the attacker's device instead.
This is a durable, persistent bypass: once the authentication method is substituted, the attacker can authenticate as the victim at any time without the victim being notified, for as long as the substitution persists. The modification event is logged in the Azure AD audit log as "User registered security info" or "Admin updated authentication methods", and detecting this change promptly is the only way to prevent extended unauthorized access.
Log signals: Azure AD audit events for authentication method registration changes, especially when performed by an admin on behalf of a user, or when a user's MFA registration changes shortly after a risky sign-in event for that account.
Real-world campaigns
Scattered Spider (UNC3944): MFA fatigue combined with social engineering
Scattered Spider is the threat group most associated with operationalizing MFA fatigue at scale. Their technique combines automated push flooding with real-time helpdesk impersonation: the attacker floods the target's phone with MFA push requests while simultaneously calling the IT helpdesk, posing as the targeted employee, and requesting that MFA be disabled or a TAP be issued due to a "lost phone." Organizations in the telecommunications, hospitality, and retail sectors have been targeted using this approach. The campaign that compromised MGM Resorts in 2023 used this exact technique, resulting in an estimated $100M in losses.
The detection path for this attack in Log360 runs through Multiple Denied MFA Requests (the push flood) followed shortly by Temporary Access Pass Added To An Account (the social engineering success) or MFA Disabled for an Account (the helpdesk capitulation). The two rules firing in sequence for the same user within a short time window is a near-certain indicator of a successful fatigue and social engineering attack.
Midnight Blizzard (APT29): Conditional Access policy modification for persistent access
APT29, the Russian SVR-affiliated group, has been documented modifying Conditional Access policies in compromised M365 tenants to establish persistent, MFA-bypassing access. After gaining initial access (typically through token theft or a compromised service account), the group identifies CA policies that would require MFA for their subsequent access patterns and either disables those policies or adds their access path to a trusted named location exemption. The modification is designed to look like routine policy administration and often occurs during working hours to blend with legitimate admin activity, making the Malicious M365 CA Policy Changes After Business Hours anomaly rule an important complement to the standard CA policy change rule.
Attack technique reference table
| Technique | Prerequisite | Duration of bypass | Log360 primary detection rule |
|---|---|---|---|
| MFA fatigue / push bombing (T1621) | Valid username and password for target account | Single session (attacker must re-push for each new session) | Multiple Denied MFA Requests |
| TAP creation (T1078.004) | Admin account with Authentication Policy Administrator or Global Admin role | For TAP validity window (typically 1 to 8 hours, configurable) | Temporary Access Pass Added To An Account |
| Conditional Access tampering (T1548) | Admin account with Conditional Access Administrator or Global Admin role | Persistent until policy is restored | Conditional Access Policy Modified |
| Auth method substitution (T1556.006) | Admin account or compromised user account with self-service MFA registration | Persistent until victim notices and removes unauthorized method | Authentication Method Changed for an User |
| MFA disabled for account (T1556.006) | Admin account with user management rights | Persistent until MFA is re-enabled for the account | MFA Disabled for an Account |
Business impact
- MFA bypass invalidates the primary identity control. MFA is the most effective single security control for preventing unauthorized account access. When MFA is bypassed, the attacker has full authenticated access to all resources the account can reach: email, SharePoint, OneDrive, Teams, connected applications, and any data those services contain. The downstream damage is bounded only by the account's permissions and the attacker's objectives.
- TAP and CA tampering create silent, persistent access. Unlike MFA fatigue, which leaves a trail of denied push requests, a successfully abused TAP or a modified CA policy gives the attacker access that looks identical to legitimate authentication. There are no failed MFA events, no anomalous authentication patterns, and no alerts from standard MFA monitoring. The only detection signal is the TAP creation or CA modification event itself, which may have occurred hours or days before the access begins.
- Identity is the new perimeter in M365 environments. Organizations that have moved workloads to M365 and Azure have by definition made identity their primary security boundary. A bypass of that boundary gives an attacker access to the organization's primary communication and collaboration platform, often including finance, HR, legal, and executive communications that represent the most sensitive data the organization holds.
- Regulatory and notification obligations. Unauthorized access to M365 or Azure AD constitutes access to a covered system under HIPAA, PCI-DSS, and GDPR depending on what data is accessible. A TAP-based access that reaches patient records, cardholder data, or EU personal data triggers breach assessment and potentially notification obligations, regardless of whether data was confirmed to have been exfiltrated.
Detecting MFA bypass and fatigue with Log360
Log360's 23 detection rules for this use case cover all four bypass paths. The prerequisite for all of these rules is that Microsoft 365 unified audit logs and Azure AD sign-in and audit logs are configured to forward to Log360. M365 audit logging must be enabled in the Microsoft Purview compliance portal, and the log forwarding connector must be configured in Log360. Rules are grouped below by the bypass path they target.
MFA fatigue detection
| Rule name | Severity | Platform | MITRE technique | What it detects |
|---|---|---|---|---|
| Multiple Denied MFA Requests | Critical | Microsoft 365 | T1621 | Multiple MFA push requests denied or cancelled for the same user within a short time window. The volume threshold distinguishes a single accidental prompt from a deliberate fatigue campaign. Critical severity because the attacker has a valid credential and is actively attempting access at the time the rule fires. |
| MFA Challenge Failed During Authentication | Trouble | Microsoft 365 | T1078.004 | MFA challenge failure events in M365 sign-in logs. Covers cases where the MFA request was not just denied but failed due to incorrect code entry or expired token, which may indicate an attacker attempting to use an intercepted or guessed OTP rather than push bombing. |
Temporary Access Pass abuse
| Rule name | Severity | Platform | MITRE technique | What it detects |
|---|---|---|---|---|
| Temporary Access Pass Added To An Account | Critical | Microsoft 365 | T1078.004 | A TAP was created for any user account. TAP creation is an administrative action that generates an Azure AD audit event. Any TAP creation outside of a documented onboarding or account recovery workflow should be treated as suspicious until confirmed legitimate. Critical severity because TAP creation immediately creates an MFA-bypassing credential for the target account. |
| M365 Short Lived Accounts | Critical | Microsoft 365 | T1078.004 | Account created, used, and deleted within a short time window. Advanced rule covering the pattern of attackers creating temporary cloud accounts to use as staging accounts for TAP-assisted access, then deleting them to reduce forensic footprint. |
Conditional Access policy tampering
| Rule name | Severity | Platform | MITRE technique | What it detects |
|---|---|---|---|---|
| Conditional Access Policy Modified | Attention | Microsoft 365 | T1548 | Any modification to a Conditional Access policy in Azure AD, including creation, update, or deletion. CA policy changes are relatively infrequent in production tenants; any change not correlated with a change management record warrants investigation. Attention severity because many CA policy changes are legitimate IT operations; the rule surfaces all changes for analyst review. |
| Malicious M365 CA Policy Changes After Business Hours | Attention | Microsoft 365 | T1484 | Anomaly rule that fires when CA policy changes occur outside normal working hours. Attacker-initiated CA modifications frequently occur outside business hours to avoid real-time detection and response. Complements the standard CA Modified rule by adding temporal context that increases the probability of malicious intent. |
| User Added To Group With CA Policy Modification Access | Trouble | Microsoft 365 | T1548 | A user was added to an Azure AD group that has Conditional Access policy modification rights. This is the privilege escalation step that precedes CA tampering: before an attacker can modify CA policies, they need an account with the Conditional Access Administrator or Global Administrator role, which is sometimes granted via group membership. |
Authentication method modification and account manipulation
| Rule name | Severity | Platform | MITRE technique | What it detects |
|---|---|---|---|---|
| MFA Disabled for an Account | Trouble | Microsoft 365 | T1556.006 | MFA was disabled for a specific user account in M365. Legitimate MFA disablement is rare outside of specific support workflows; any instance not correlated with a helpdesk ticket warrants immediate investigation. |
| Authentication Method Changed for an User | Trouble | Microsoft 365 | T1098 | A user's registered authentication method (phone number, authenticator app, FIDO key) was changed. This is the key event for auth method substitution attacks where the attacker registers their own device as the victim's MFA factor. |
| Risky Sign-in with Device Registration | Trouble | Microsoft 365 | T1078.004 | Advanced rule that correlates a risky sign-in event in Azure AD Identity Protection with a device registration action in the same session. This is the signature of an attacker using a compromised credential to register a new device for persistent access, enabling future authentication from that device without triggering MFA. |
| High Risk Sign-In Detected | Trouble | Microsoft 365 | T1586.003 | Azure AD Identity Protection flagged a sign-in as high risk based on its built-in ML risk model, covering signals such as anonymous IP, impossible travel, unfamiliar sign-in properties, and leaked credentials. High-risk sign-ins that result in a successful authentication indicate MFA either was not enforced or was bypassed. |
| PowerShell Sign-In Detected | Attention | Microsoft 365 | T1078.004 | Authentication to M365 using a PowerShell client (identified by user agent). Attackers use PowerShell sign-ins because legacy authentication protocols used in PowerShell connections bypass modern MFA policies in some configurations. Attention severity because PowerShell sign-ins are legitimate for M365 administrators; context determines urgency. |
| Login to Disabled Account | Trouble | Microsoft 365 | T1078.004 | A successful authentication was recorded for an account that is marked as disabled. This should not be technically possible under normal circumstances; successful authentication to a disabled account indicates either a misconfiguration in the disabled account state or a sign-in bypass through a federated identity path that does not correctly enforce account status. |
| Application ID URI Modified | Critical | Microsoft 365 | T1078.004 | The Application ID URI of an Azure AD registered application was modified. This is a technique used to redirect OAuth authentication flows to attacker-controlled endpoints, enabling token capture without triggering MFA. Critical severity because this modification affects the entire application's authentication chain. |
Privilege escalation and persistence in M365
| Rule name | Severity | Platform | MITRE technique | What it detects |
|---|---|---|---|---|
| PIM Role Configuration Changed | Attention | Microsoft 365 | T1078.004 | A Privileged Identity Management role configuration was changed. PIM controls how privileged roles are activated, including MFA requirements for activation. Weakening PIM role activation settings (removing MFA requirement, extending maximum activation duration) is a mechanism for establishing persistent privileged access with reduced authentication friction. |
| Global Administrator Role Addition to PIM User | Trouble | Microsoft 365 | T1098 | A user was added to the Global Administrator role in PIM. Global Administrator in M365 has the highest privilege level and the broadest access across all M365 services. Any addition to this role outside of a documented approval workflow is a high-priority investigation item. |
| Entra ID User Enabled and Password Reset | Critical | Microsoft 365 | T1098 | Advanced rule covering the combined action of a disabled account being re-enabled and its password reset within a short window. This is a common pattern for attackers who identify dormant accounts as attack vectors: re-enable the account, reset the password, use it as a staging identity that may not be enrolled in MFA. |
| Entra ID privileged role assigned | Trouble | Microsoft 365 | T1098.003 | A privileged role (Global Admin, Security Admin, Conditional Access Admin, Authentication Policy Admin) was assigned to a user. Privileged role assignments made to accounts that do not typically hold such roles, or made outside of change management windows, are a standard indicator of privilege escalation or attacker persistence. |
| Added Credentials to Existing Application | Trouble | Microsoft 365 | T1098.001 | New credentials (client secret or certificate) were added to an existing Azure AD application registration. Attackers use this technique to maintain persistent access to M365 data via app-only authentication flows that do not require user-level MFA, even after the compromised user account's credentials are changed. |
| Application Owner Added | Attention | Microsoft 365 | T1098 | An owner was added to an Azure AD application registration. Application owners can add credentials to that application, making this event a precursor to the Added Credentials pattern. Adding themselves as an application owner is a privilege escalation step attackers use before adding persistent app credentials. |
| User ImmutableId Attribute Updated | Critical | Microsoft 365 | T1098 | The ImmutableId attribute of an Azure AD user was updated. ImmutableId is used in hybrid identity environments to link on-premises AD accounts to Azure AD. Modifying this attribute can redirect the cloud identity to a different on-premises account, enabling authentication as the cloud user using on-premises credentials that may not be subject to cloud MFA policies. |
Attack chain visibility
The most dangerous MFA bypass attacks follow a consistent pattern: an initial bypass technique is used to gain access, followed by persistence actions that ensure continued access even after the bypass mechanism is discovered and remediated. The sequences below show the two highest-risk chains.
Sequence A: MFA fatigue leading to TAP creation and persistence
| Step | Log source and event | What it indicates | Time offset |
|---|---|---|---|
| 1 | M365 sign-in log (MFA denied events) | Repeated MFA push requests sent for the same user from the same source IP. Multiple Denied MFA Requests rule fires. The attacker has a valid credential and is attempting to fatigue the user into approving a push. | T+0 to T+30min |
| 2 | M365 sign-in log (successful authentication) | Authentication succeeds for the target user. The user approved a push notification, either accidentally or deliberately. The attacker now has a valid M365 session. | T+30min |
| 3 | Azure AD audit log (TAP creation) | From the newly obtained session, the attacker (if the compromised account has admin rights) creates a Temporary Access Pass for a second high-value account. Temporary Access Pass Added To An Account rule fires. The attacker now has a second, MFA-bypassing credential independent of push fatigue. | T+35min |
| 4 | Azure AD audit log (role assignment) | Entra ID privileged role assigned rule fires as the attacker assigns a privileged role to an account they control, establishing persistent admin access that survives password resets on the initially compromised account. | T+40min |
Sequence B: CA policy tampering for persistent MFA bypass
| Step | Log source and event | What it indicates | Time offset |
|---|---|---|---|
| 1 | Azure AD audit log (CA policy change) | Conditional Access Policy Modified rule fires. A policy that previously required MFA for external access was updated to add the attacker's IP range to trusted named locations, or the MFA requirement was removed from the policy scope. The change was made at 2:00 AM on a Sunday. | T+0 |
| 2 | M365 sign-in log (successful sign-in, no MFA) | The attacker authenticates from their IP using a credential that would previously have triggered an MFA prompt. The sign-in completes with no MFA challenge. The sign-in log shows authentication method as "password only" for a user whose previous sign-ins all show MFA completion. | T+5min |
| 3 | M365 audit log (data access) | The attacker begins accessing M365 resources: SharePoint file downloads, Exchange mail reads, Teams message history. UEBA anomaly scores spike as the access pattern deviates significantly from the account's established baseline for time of day, data volume, and resource types accessed. | T+10min onward |
Investigation playbook
MFA bypass investigations require speed. Unlike brute force attacks where the failure pattern itself is the alert, many MFA bypass techniques fire their detection rule at the moment of bypass, not before. When a rule fires, access may already be in progress. The goal of the investigation is to determine the scope of access that occurred, whether persistence was established, and what data was reached.
Step 1: Triage - identify the bypass method and current status
| Rule that fired | Bypass method | Is access active now? | First action |
|---|---|---|---|
| Multiple Denied MFA Requests | MFA fatigue in progress | Not yet - attacker is attempting. Check if any subsequent successful sign-in occurred. | Check M365 sign-in logs immediately for a successful authentication from the same source IP in the minutes following the denied requests. If found, access is active. |
| Temporary Access Pass Added To An Account | TAP created - bypass credential now exists | Possibly. TAP may have already been used. | Revoke the TAP immediately. Check M365 sign-in logs for any authentication using the TAP (authentication method shows as "Temporary Access Pass") for the target account. |
| Conditional Access Policy Modified | CA policy weakened - bypass may be ongoing | Possibly. Any authentication since the change may have bypassed MFA. | Review the specific change made. Restore the policy immediately if unauthorized. Check sign-in logs for authentications since the change that lacked MFA completion. |
| Authentication Method Changed for an User | MFA device substituted - persistent bypass established | Attacker can authenticate as the user at any time until the change is reversed. | Disable the account immediately. Review the authentication method change to identify the attacker's registered device. Check all sign-ins since the change occurred. |
| MFA Disabled for an Account | MFA removed - account now password-only | Any authentication since disablement has no MFA protection. | Re-enable MFA for the account immediately. Review all authentications since MFA was disabled. |
Step 2: Determine scope of access
- Using Log360's log search, query the M365 unified audit log for all activity by the affected account from the time of the bypass event forward. Filter for high-impact operations: file downloads, email reads, SharePoint access, Teams message history, and admin operations.
- For TAP-based access, identify the exact time window the TAP was valid and query all M365 activity from the target account during that window. TAP-based authentications are identifiable in the sign-in log by authentication method.
- For CA policy tampering, identify the exact change made and determine which users and which access patterns were affected by the weakened policy. Every sign-in from an affected user during the tampered policy period should be reviewed.
- Check whether any admin operations were performed: role assignments, policy changes, new application registrations, TAP creations for other accounts. Each of these extends the scope of the incident beyond the initially compromised account.
Step 3: Investigate using the Incident Workbench
- Click on the affected username in the alert or log search results to open the Incident Workbench. Use the User analytics tab to view the account's full activity overview: sign-in history, resources accessed, UEBA risk score, and behavioral baseline. A successful MFA bypass will show a sudden change in sign-in source IP, device, or location relative to the account's established pattern.
- Use Advanced Threat Analytics on the sign-in source IP to pull threat feed risk scores. IPs used for MFA fatigue campaigns frequently appear in threat intelligence feeds as known attack infrastructure. A high-risk IP completing an authentication that previously had denied MFA requests is a confirmed malicious access event.
- If PIM role changes, application credential additions, or CA policy modifications were detected, open additional Incident Workbench tabs for the admin account that performed those operations. This reveals whether the admin account itself was compromised or whether an attacker escalated from a lower-privilege account.
- Save the Incident Workbench session to an incident. The user activity timeline and risk scoring from this session become the evidence record for breach assessment and any regulatory notification obligations.
Step 4: Check for persistence
- Query the M365 audit log for the following persistence indicators in the time window following the initial bypass: new application registrations, credential additions to existing applications, new service principals, PIM role activations, Global Admin role assignments, and new federated domain additions.
- Check whether any CA policies were modified after the initial bypass. A common pattern is: compromise account via fatigue, modify CA policy to add attacker IP as trusted, then use that trusted IP for all future access without triggering further alerts.
- Check whether any new Authentication Methods were registered for the compromised account or for other accounts the compromised admin accessed. Authentication method registrations made during or after a bypass event are persistence mechanisms.
- Review whether any mail forwarding rules were created in the compromised account's mailbox. Mail forwarding rules (detected by the Mail Flow Rule for Forwarding Created rule) are a common post-compromise persistence action that allows ongoing email surveillance even after the account password is reset.
Step 5: Collect evidence and build the timeline
- Export the M365 unified audit log for the affected accounts covering the full period from the earliest detection rule firing to the time of investigation. This is your primary forensic record for breach assessment.
- Export Azure AD sign-in logs for the affected accounts. Sign-in logs show authentication method, IP, device, location, risk level, and MFA result for every authentication event and are the key artifact for demonstrating whether the bypass was successful.
- If a CA policy was modified, export the policy change audit record including the before and after state of the policy. This documents exactly what was changed and when.
- Export the Incident Workbench session timeline and risk assessment as the compliance artifact for HIPAA Section 164.308(a)(6) (security incident procedures) and NIST CSF DE.AE-5 (incident analysis).
Response and remediation
Immediate containment
- Revoke all active sessions for the compromised account. Use the Revoke-MgUserSignInSession PowerShell cmdlet or the M365 admin portal to invalidate all existing session tokens. This terminates any active attacker sessions immediately. Password reset alone does not revoke existing tokens.
- Revoke any TAPs created during the bypass window. TAPs are listed in the user's authentication methods in Entra ID admin center. Remove all TAPs from affected accounts. If the scope of compromised accounts is unclear, audit all TAP creations in the last 30 days and revoke any that cannot be correlated with a documented onboarding or recovery workflow.
- Restore any modified Conditional Access policies. Review the specific changes made and revert them. Enable report-only mode temporarily if the full impact of reverting a change is unclear, but prioritize restoring MFA requirements over policy stability.
- Remove unauthorized authentication method registrations. Any phone number or authenticator app added to a user's MFA methods during or after a bypass event should be removed. Require the user to re-register their own MFA device after identity verification.
- Disable compromised admin accounts and require re-authentication and MFA re-enrollment via a separate, out-of-band channel before restoring access.
Response actions by trigger
| Trigger | Immediate action | Owner |
|---|---|---|
| Multiple Denied MFA Requests with no subsequent successful sign-in | Block source IP. Notify affected user. Consider temporarily requiring number matching on MFA push to prevent accidental approval. | SOC L1 |
| Multiple Denied MFA Requests followed by successful sign-in | Revoke sessions immediately. Disable account. Begin scope investigation. Block source IP. Open incident. | SOC L2 + Incident Response |
| Temporary Access Pass Added To An Account | Revoke TAP immediately. Investigate who created it and whether it was used. If used, treat as active compromise. | SOC L2 |
| Conditional Access Policy Modified | Review the change against change management records. If unauthorized, restore policy immediately and audit all sign-ins since the change for MFA bypass. | SOC L2 + M365 Admin |
| Authentication Method Changed for an User | Disable account immediately. Remove the unauthorized authentication method. Require out-of-band identity verification before restoring access. | SOC L2 + Incident Response |
| Global Administrator Role Addition to PIM User or Entra ID privileged role assigned | Remove the role assignment immediately if unauthorized. Investigate all admin operations performed by the account since the assignment. Check for downstream persistence actions. | SOC L3 + Incident Response |
Hardening
- Enable number matching for Microsoft Authenticator push notifications. Number matching requires the user to type a two-digit number displayed on the sign-in screen into the Authenticator app. This eliminates accidental approvals and significantly increases the effort required for a successful fatigue attack, since the user must actively engage with the sign-in screen to approve.
- Enable additional context in MFA push notifications, including the application name and geographic location of the sign-in. Users who see "Sign in to SharePoint from Kyiv, Ukraine" in the push notification are far less likely to approve a request they did not initiate.
- Restrict TAP creation to a small number of named administrators and require an approval workflow before a TAP can be created. Configure TAPs with the minimum necessary validity window (one hour rather than eight) and single-use only.
- Require Privileged Identity Management approval and MFA activation for all admin roles, including Conditional Access Administrator and Authentication Policy Administrator. No admin role should allow standing access without MFA-gated activation.
- Enable Azure AD Identity Protection and configure Conditional Access policies to block or require MFA step-up for high-risk sign-ins. High-risk sign-ins that complete without MFA are a gap that the High Risk Sign-In Detected rule surfaces but CA policies can prevent automatically.
False positive tuning
| False positive source | Rules affected | Tuning strategy |
|---|---|---|
| Legitimate TAP creation for onboarding or account recovery | Temporary Access Pass Added To An Account | TAP creation is a normal IT operation during employee onboarding or MFA device loss recovery. Create an exception scoped to specific IT admin accounts that are authorized to create TAPs, combined with a correlation against open helpdesk tickets. Flag any TAP creation from accounts not in the authorized list regardless of time. Do not create time-based exceptions for TAP creation: legitimate TAPs are created in response to specific user requests, not at arbitrary times. |
| Planned Conditional Access policy updates | Conditional Access Policy Modified, Malicious M365 CA Policy Changes After Business Hours | CA policy changes made by authorized M365 administrators during planned maintenance windows generate the same event as attacker-initiated changes. Correlate CA policy change alerts against change management records. Exceptions should be scoped to the specific admin account, the specific policy being changed, and the approved change window. The after-hours anomaly rule requires a separate exception for any planned maintenance that occurs outside business hours. |
| Helpdesk-initiated MFA resets for legitimate users | MFA Disabled for an Account, Authentication Method Changed for an User | IT helpdesk staff legitimately disable and re-enable MFA during support workflows. Create an allowlist of helpdesk service accounts authorized to perform MFA administration. Alert on MFA changes performed by accounts not in that allowlist, or on changes performed without a corresponding open helpdesk ticket. Never create a blanket exclusion for MFA modification events. |
| Authorized PIM role activations and assignments | PIM Role Configuration Changed, Global Administrator Role Addition to PIM User, Entra ID privileged role assigned | PIM role assignments and configuration changes are routine in organizations using Azure AD PIM for just-in-time access. Correlate these alerts against the PIM approval workflow records. Role assignments that went through the PIM approval process with a documented justification and approver are expected; role assignments that bypass PIM (direct role assignments outside the PIM workflow) should always alert. |
| M365 PowerShell administration by IT staff | PowerShell Sign-In Detected | M365 administrators regularly use PowerShell for tenant administration. Allowlist known admin account UPNs from the PowerShell Sign-In rule. Flag PowerShell sign-ins from non-admin accounts, from accounts that have never previously used PowerShell, or from IP addresses not associated with known admin workstations or jump hosts. |


