- Home
- SIEM use cases
- Process Hunting
How to hunt malicious process lineage
In this page
Understanding the threat:
Attackers often attempt to blend their actions within normal system activity by spawning malicious processes from trusted applications. These unauthorized child processes can serve as entry points for privilege escalation, persistence, or lateral movement, making them a key indicator of compromise.
Identifying these hidden process relationships requires visibility into how processes originate, evolve, and interact over time. Security teams can uncover early signs of malicious activity and prevent broader compromise across endpoints by analyzing process hierarchies and detecting deviations from normal behavior.
Category:
- External threat
Relevant MITRE ATT&CK tactics and techniques:
Tactics:
TA0002 - Execution, TA0005 - Defense Evasion, TA0007 - Discovery, TA0008 - Lateral Movement
Techniques:
T1059 - Command and Scripting Interpreter, T1106 - Native API, T1082> - System Information Discovery, T1055 - Process Injection
Compliance mapping for Process Monitoring:
- CMMC IR.L3-3.7.5: Enables early detection and analysis of abnormal process executions, supporting timely incident response.
- NIST IR-8 (Incident Response): Provides structured mechanisms for investigating suspicious process behavior and containing incidents.
- CIS 17.2 (IG3): Correlates system-level anomalies and process events to improve accuracy in incident detection and response.
The hunt: Real-life threats:
SolarWinds attack (2020): Malicious DLLs executed through trusted SolarWinds processes allowed attackers to move laterally and evade detection for months.
NotPetya (2017): Malicious processes propagated via legitimate admin tools, masquerading as normal system activity, led to rapid system compromise.
Scenario explanation:
A mid-sized enterprise with a hybrid workplace begins noticing unusual activity: PowerShell or WMIC scripts are being launched from trusted applications like explorer.exe or winword.exe.
Employees’ endpoints appear normal, but attackers leverage these trusted parent processes to:
Scenario infographic:
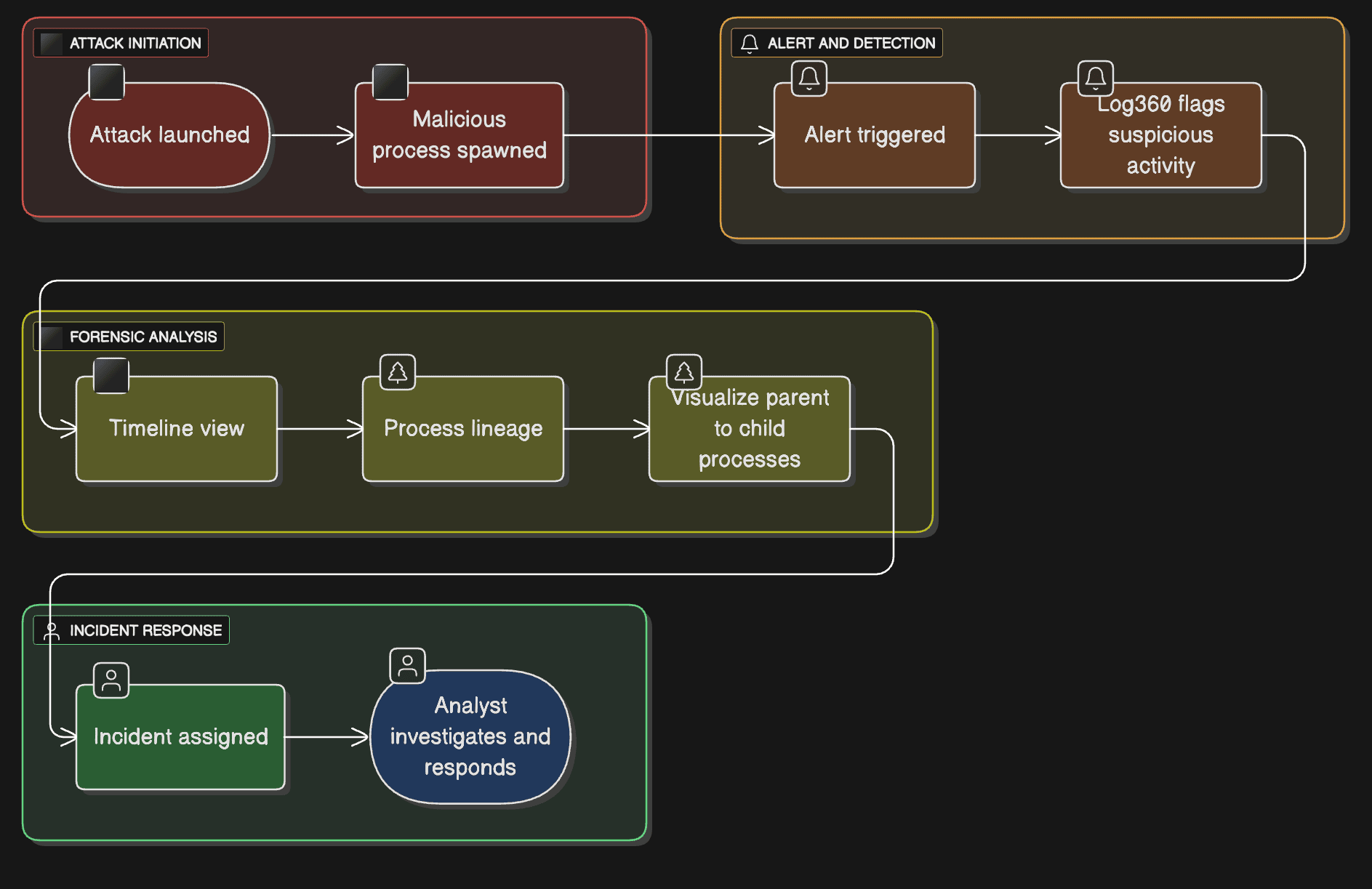
- Maintain persistence across reboots.
- Download and execute additional payloads.
- Move laterally to other systems without triggering standard endpoint alerts.
Why this happens:
- Attackers exploit normal process relationships to evade detection.
- Process lineage is complex and difficult to track manually across hundreds of endpoints.
What can go wrong:
- Unauthorized processes run undetected, enabling privilege escalation.
- Lateral movement spreads malware across critical systems.
- Delayed detection increases potential data compromise and operational impact.
Prerequisites:
Ensure process creation auditing, command-line logging, and Sysmon event forwarding are enabled and configured to send logs to Log360.
How to visualize process lineage for threat hunting:
Log360 provides end-to-end visibility into process activity and parent-child relationships, making it easier to detect suspicious or malicious processes. Here’s how it works:
1. Identify suspicious processes:
Log360 collects process creation logs from endpoints to highlight potentially risky processes, such as PowerShell, WMI, or unexpected scripts. Analysts can review alerts or monitor reports to spot unusual activity.
2. Access the Incident Workbench:
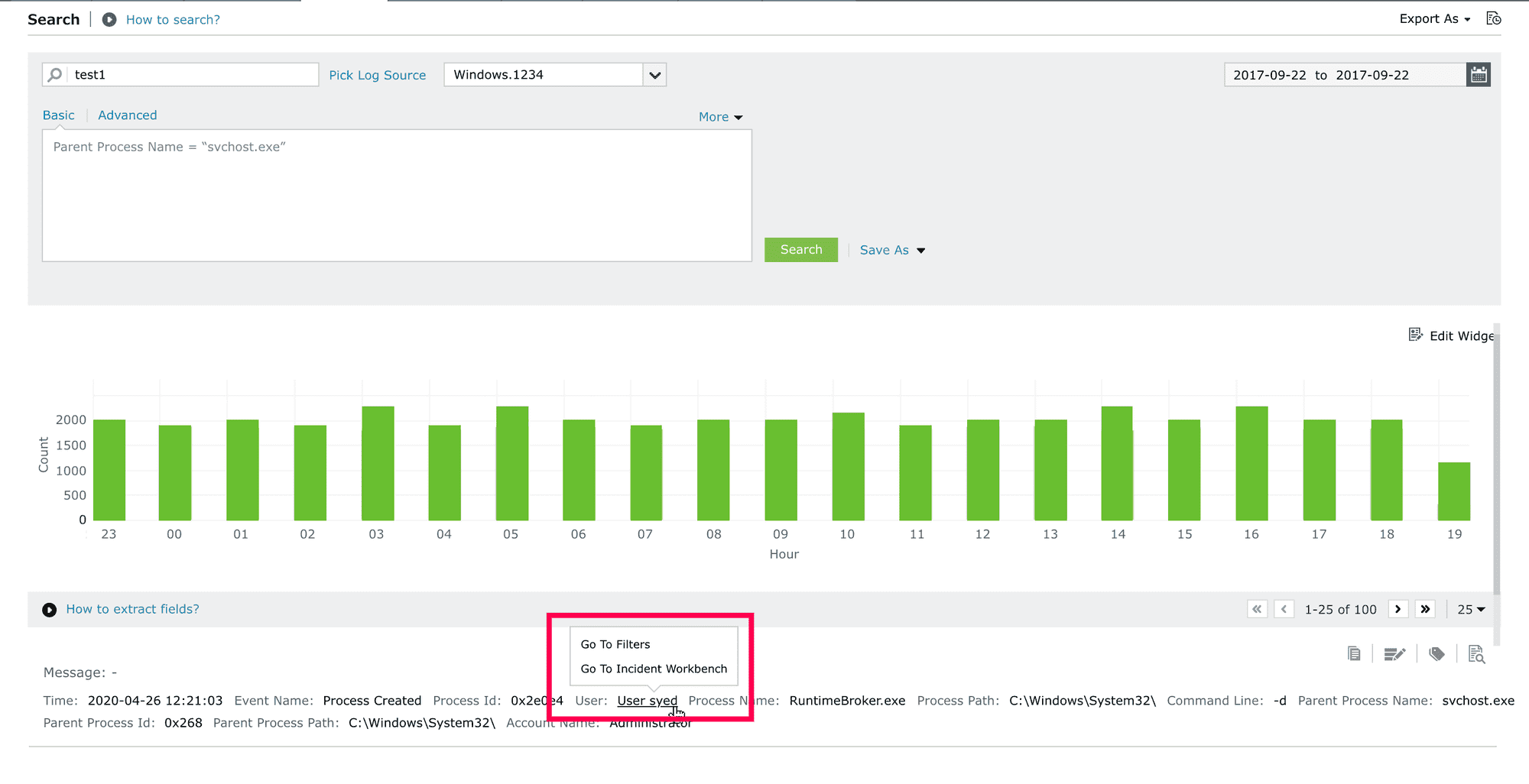
Invoke Incident Workbench from alerts, search, reports, or the incident management console to investigate a suspicious process. Within the workbench, you can adjust the time frame to visualize related process events and understand the full sequence of activity.
3. Visualize process lineage:
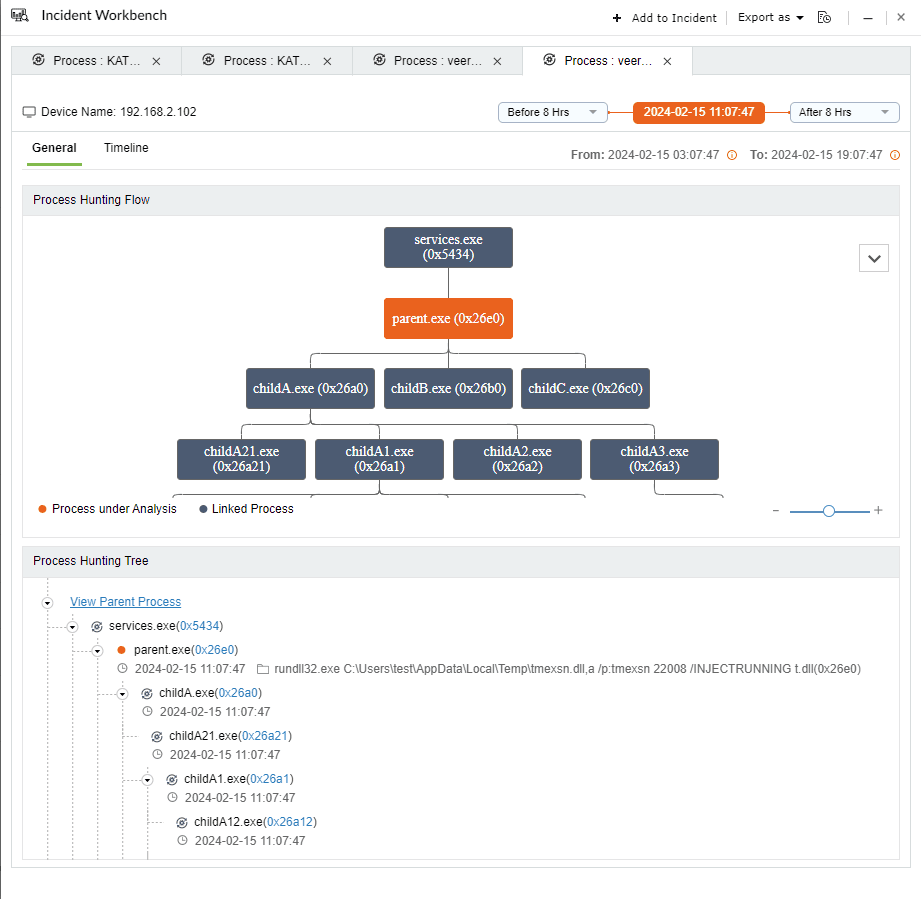
The Process Hunting Tree view displays the full parent-child process hierarchy. Analysts can quickly identify abnormal relationships, like scripts spawned from non-standard applications.
4. Analyze timelines and event sequences:
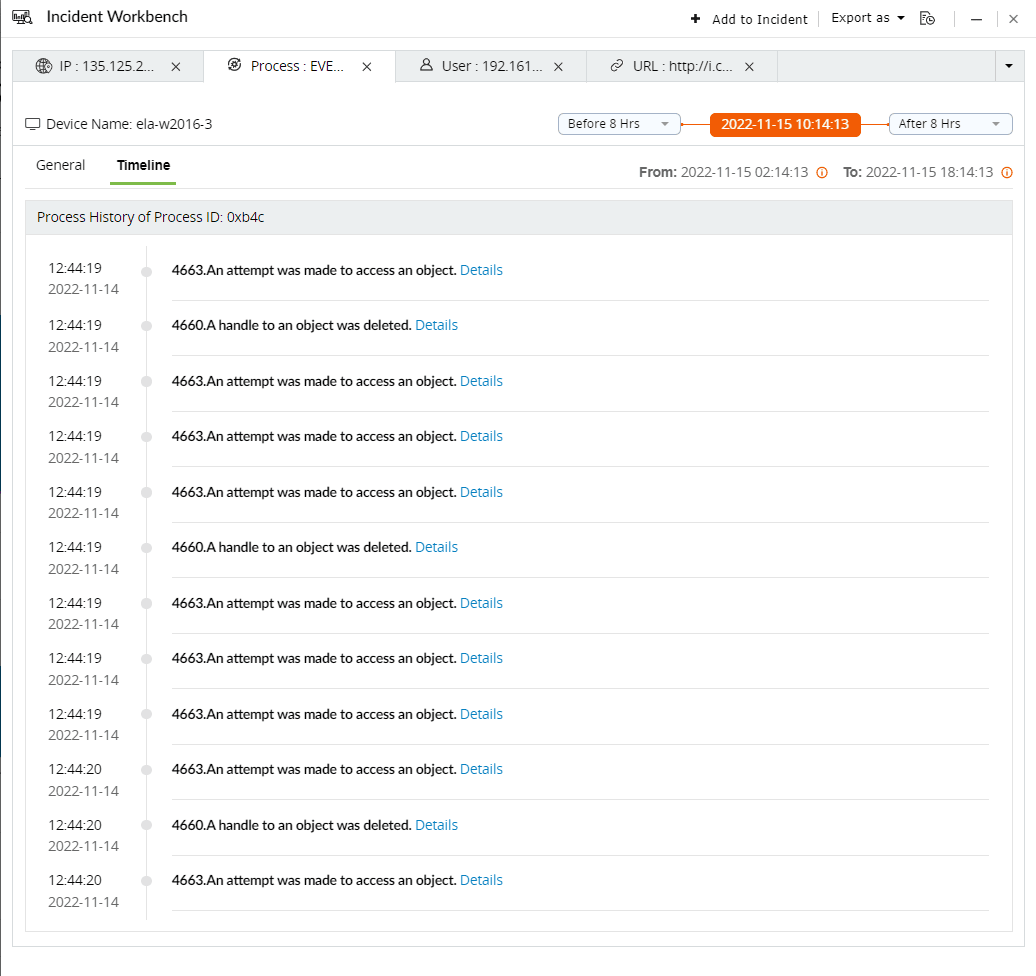
The timeline shows the exact sequence of process events, revealing when the process started and what subsequent actions it triggered. This helps in understanding the impact and scope of suspicious activity.
5. Raise incidents and assign analysts:
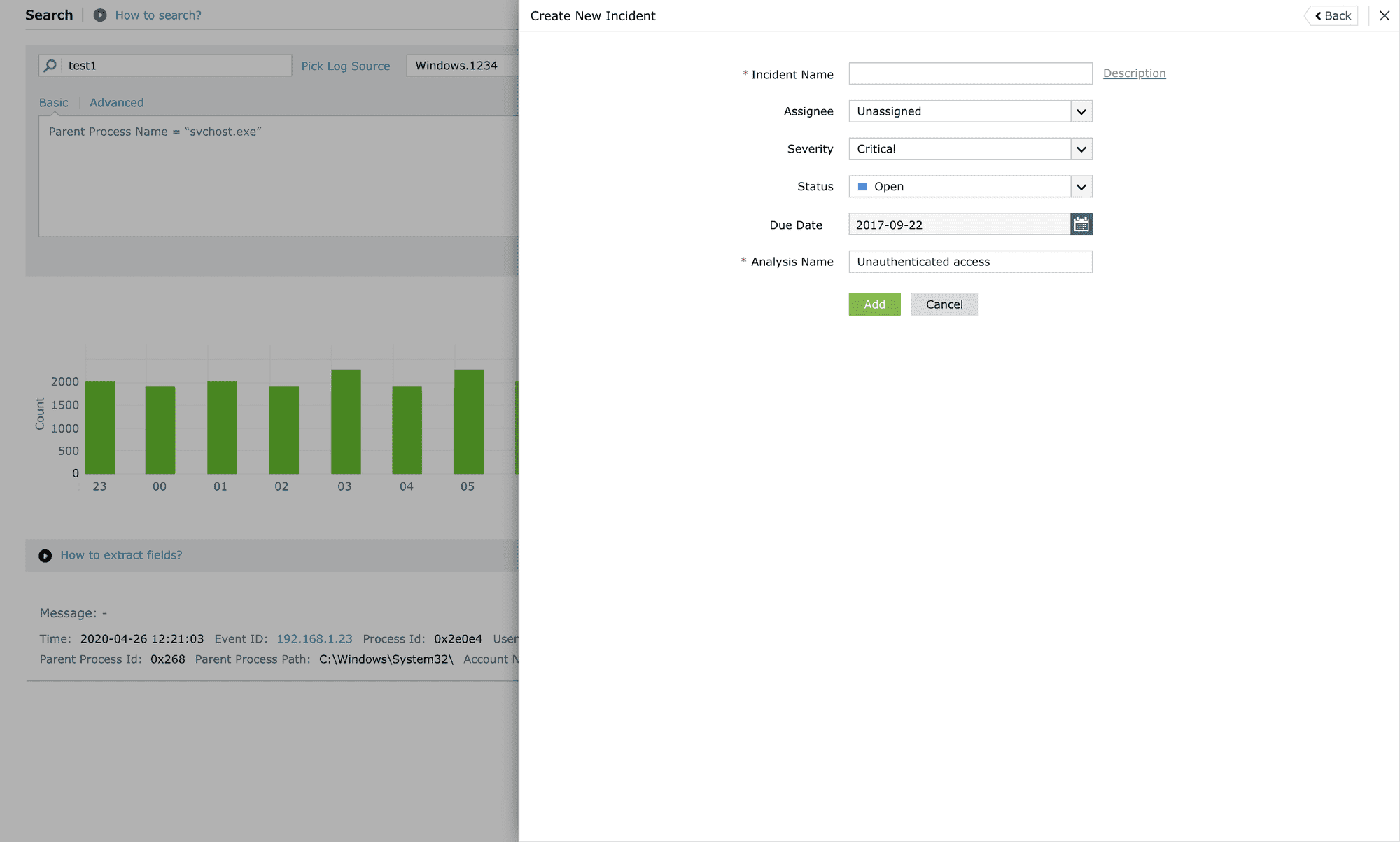
Suspicious processes can be converted into incidents within the Incident Workbench and assigned to the appropriate analyst or administrator for review and response.
6. Configure real-time alerts:
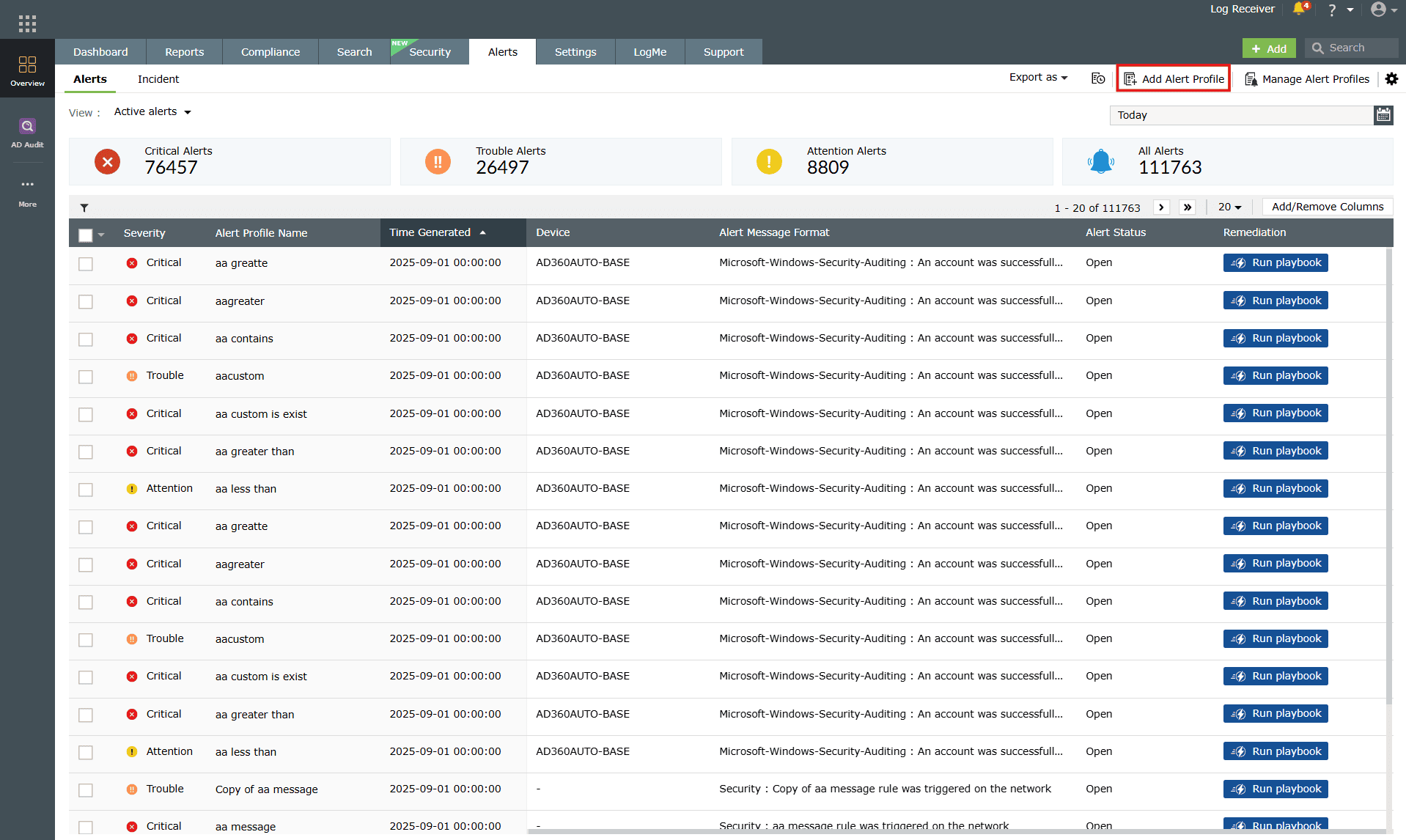
Alerts can be set to notify security teams immediately if similar suspicious process activity occurs in the future, ensuring proactive monitoring.
Next steps:
- Define suspicious process criteria: Identify critical parent processes and risky child process behaviors.
- Implement alerting rules: Configure thresholds and notifications in Log360 for suspicious process activities.
- Regular process review: Periodically analyze process lineage reports to identify emerging threats.
- Incident response playbook: Ensure analysts follow a defined workflow for investigating and containing suspicious processes.


