- Home
- SIEM use cases
- RDP Abuse
How to detect RDP abuse with Log360
In this page
Understanding the threat- What is RDP Abuse?
Remote Desktop Protocol (RDP) abuse occurs when attackers manipulate RDP-related settings or registry keys to gain unauthorized remote access into an organization’s network. Adversaries create a hidden doorway into critical systems by enabling RDP where it was intentionally disabled, modifying sensitive configurations, or weakening protective controls. These changes often happen quietly at the registry level, making them difficult to detect without dedicated monitoring.
Once RDP is enabled or altered, attackers can remotely connect to compromised machines, escalate privileges, move laterally across servers, deploy malware, or exfiltrate data—all while appearing as legitimate users. Abused RDP access blends in with normal operations because RDP is a trusted administrative tool in most enterprises, allowing attackers to maintain persistence for days or even weeks. This makes unchecked RDP modifications a high-risk vector for modern attacks, particularly ransomware operations and hands-on-keyboard intrusions.
Category
Endpoint
Relevant MITRE ATT&CK mapping
This use case directly maps to the Impact tactic:
- TA0008 – Lateral Movement: T1021.001 (Remote Services: Remote Desktop Protocol – RDP)
- TA0005 – Defense Evasion: T1112 (Modify Registry), applicable when RDP-related registry keys are tampered to enable/alter RDP settings.
Relevant compliance mapping
- C003 - AC.2.013
Scenario
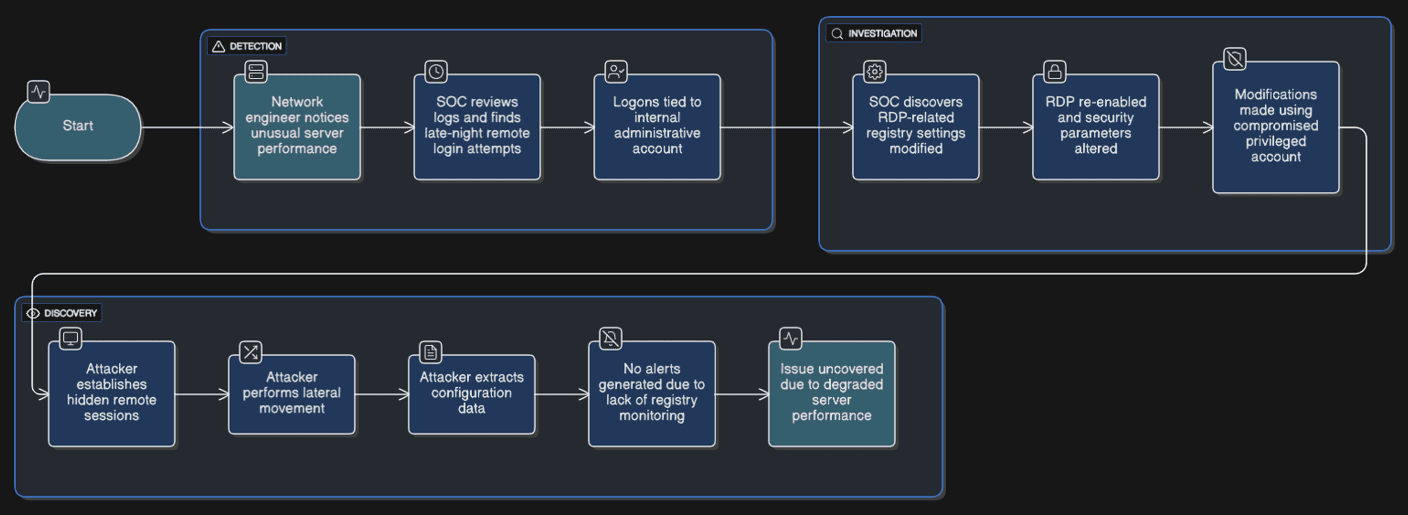
A network engineer at a manufacturing company noticed unusual performance issues on a critical application server during a routine system check. When the SOC reviewed the logs, they found several late-night remote login attempts that did not align with any approved maintenance activity. The logons appeared legitimate at first because they were tied to an internal administrative account that frequently accessed the server.
Upon deeper investigation, the SOC team discovered that key RDP-related registry settings had been modified three days earlier. RDP, which had been intentionally disabled on this sensitive server, was quietly re-enabled, and certain security parameters such as RestrictedAdminMode had been altered. The modifications were made using a compromised privileged account, allowing the attacker to establish hidden remote sessions, perform lateral movement, and extract configuration data. Since the company did not monitor registry-level changes tied to RDP, none of these suspicious activities generated alerts, and the issue was only uncovered due to degraded server performance.
Scenario infographic
What went wrong
No visibility into RDP configuration changes: The company monitored remote logins but did not track modifications to RDP-related registry keys. RDP was silently re-enabled on a sensitive server without triggering any alerts.
Weak detection for registry tampering: Critical security settings like RestrictedAdminMode were altered, but because registry-level auditing was not enabled or monitored, these high-risk changes went completely unnoticed.
Compromised privileged account: The attacker used a valid admin account to reconfigure RDP access. Since the account’s behavior was not base lined or monitored for anomalies, the malicious configuration drift appeared as normal administrative activity.
How RDP abuse monitoring helps
RDP configuration and registry-change monitoring directly addresses the gaps above by enabling:
Granular auditing of RDP settings: Continuous tracking of changes to high-risk registry keys ensures any attempt to enable RDP, weaken protections, or modify access controls is logged and alerted instantly.
Real-time alerting on configuration drift: Unauthorized attempts to re-enable RDP or alter secure parameters trigger immediate alerts, giving the SOC time to intervene before attackers initiate remote sessions.
Detection of privileged account misuse: When paired with UEBA, deviations in admin behavior—such as modifying RDP settings outside maintenance windows, are flagged, helping identify compromised or misused accounts early.
Threats in the data: Real-world trends
- RDP as a top attack vector: RDP continues to be one of the most abused entry points in cyber incidents. Many ransomware groups rely on misconfigured or re-enabled RDP to gain footholds inside networks. Security reports consistently show RDP involvement in a majority of hands-on-keyboard intrusions.
- Registry tampering for stealthy access: Attackers increasingly modify RDP-related registry keys to quietly enable remote access and weaken security settings. This tactic helps them bypass traditional remote access monitoring and maintain persistence without being detected for days or weeks.
Prerequisites
- Windows registry auditing enabled: Ensure auditing is turned on for relevant RDP-related registry keys, such as HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server\fDenyTSConnections and RestrictedAdminMode settings.
- Log360 installed and configured: The endpoints and domain controllers where RDP is configured should be added as log sources.
- UEBA baseline configured: Normal user and admin login patterns must be established to detect anomalous behavior.
- Privileged account monitoring: Ensure that all administrative accounts are tracked for unusual RDP activity.
How Log360 detects RDP abuse
Step 1: Enable Windows Registry and RDP log ingestion
To monitor RDP abuse, first configure Log360 to collect Windows Event Logs and registry changes relevant to RDP settings.
- Navigate to Settings > Log Sources > Windows Devices and ensure all endpoints and domain controllers are added.
- Enable registry auditing for keys such as:
- HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server\fDenyTSConnections
- Keys controlling RestrictedAdminMode and other sensitive RDP settings.
- Ensure that Log360 parses both logon events and registry modification events, making them searchable for alerting and correlation.
Step 2: Establish user and admin behavior baselines
RDP abuse is often detected by identifying deviations from normal admin behavior.
- Go to UEBA > Baselines in Log360.
- Allow Log360 to learn typical user and admin patterns, including:
- Normal login times and locations
- Expected frequency of RDP connections
- Regular access to sensitive servers
- Typical registry changes performed by admins
- This baseline enables Log360 to flag unusual activity such as off-hours RDP logins or unauthorized configuration changes.
Step 3: Monitor RDP activity reports
Once baselines are in place, review RDP-related reports to detect suspicious activity.
- Navigate to Reports > Remote Access > RDP Activity.
- Key report groups to monitor:
- RDP Logon Report: Tracks logins to critical servers, including source IP and time
- Registry Changes Report: Lists changes to RDP-related keys and settings
- Remote Session Patterns: Highlights new, unusual, or off-hours connections
- These reports help SOC teams detect unauthorized RDP enablement or suspicious session patterns.
Step 4: Detect RDP abuse using correlation rules
Configure correlation rules to link multiple RDP-related behaviors indicating potential compromise.
- Go to Correlation > Create Rule and add conditions such as:
- Registry keys for RDP re-enabled outside approved windows
- Changes to RestrictedAdminMode or other sensitive settings
- Off-hours logins from privileged accounts
- Logins from unusual IPs or new devices
- Log360 correlates these events to generate alerts for potential RDP abuse.
Step 5: Set up real-time alerts for high-risk activity
Immediate notifications are critical to prevent lateral movement and data theft.
- Navigate to Alerts > Manage Profiles > Add Alert Profile or use built-in RDP abuse profiles from Settings > Marketplace > Installed Extensions > Windows.
- Select the correlation rules for RDP registry changes and anomalous login behavior.
- Configure notification channels (email, SMS, Teams, or ticketing system).
- Trigger alerts when:
- RDP is re-enabled without authorization
- Sensitive RDP security settings are altered
- Off-hours or remote logins occur from unusual sources.
- SOC teams can act immediately to isolate endpoints or accounts.
Step 6: Investigate and contain RDP abuse using incident timelines
Use Log360’s incident timeline to visualize RDP abuse events and track lateral movement.
- Open Correlation Results > Incident Timeline.
- Review:
- When the RDP registry change occurred
- Which account executed the change?
- Subsequent login sessions and IP/device details
- Containment actions may include:
- Disabling RDP on affected endpoints
- Resetting compromised credentials
- Blocking malicious IPs or devices
- Integrating with SOAR/EDR to isolate endpoints
- This process enables fast investigation, containment, and remediation before the attacker can cause further damage.
Next steps
- Investigate flagged accounts and endpoints thoroughly
Review all alerts triggered by RDP registry changes, off-hours logins, or unusual remote sessions to identify compromised accounts or endpoints.
- Validate changes with IT or change management teams
Cross-check whether the RDP-related modifications were authorized maintenance or configuration updates to rule out false positives.
- Take corrective actions immediately
Disable unauthorized RDP sessions, reset compromised credentials, revoke excessive privileges, or block affected accounts to prevent further abuse.
- Perform a root cause analysis
Identify how the attacker gained access phishing, credential theft, or insider misuse and implement measures to prevent recurrence.
- Optimize and strengthen monitoring
Fine-tune Log360 detection rules and UEBA thresholds, schedule periodic reports, and continuously audit registry changes to ensure early detection of any future RDP abuse attempts.


