- Home
- SIEM use cases
- Rogue Device Evasion
How to track rogue device evasion attempts
In this page
Understanding the threat
Attackers often compromise legitimate endpoints and then disable monitoring or MDM agents to avoid detection. Once the device is hidden from inventory systems, it effectively becomes invisible to IT teams—yet it still has valid access to internal resources. These rogue devices are then used to move laterally, harvest credentials, or exfiltrate data without raising immediate suspicion.
Detecting this evasion requires correlating device inventory changes with performance anomalies, authentication logs, and software activity. Identifying when a previously managed endpoint suddenly disappears or exhibits unexpected network behavior is key to preventing stealthy persistence.
Category:
- External threat
Relevant MITRE ATT&CK tactics and techniques:
Tactics:
TA0005 – Defense Evasion, TA0008 – Lateral Movement, TA0009 – Collection
Techniques:
T1562 – Impair Defenses, T1027 – Obfuscated Files or Information, T1078 – Valid Accounts
Compliance mapping:
- CMMC MP.L1-3.8.3: Supports monitoring and control of endpoint inventory and media handling by surfacing devices that have been deregistered or stopped reporting.
- NIST PE-3 (Physical Access): Helps detect devices that have been tampered with or removed from management visibility—supporting controls for physical and logical access monitoring.
- CIS 1.2 (IG1): Enables asset inventory and tracking practices required by CIS, by correlating enrollment/he
The hunt: Real-life threats
APT29 campaign: Attackers disabled endpoint management agents to keep compromised hosts from receiving security patches or detection updates, maintaining long-term stealth.
Pegasus spyware incidents: Mobile devices were compromised and subsequently removed from MDM visibility to sustain surveillance and avoid remote wipes or policy enforcement.
Scenario explanation:
An enterprise’s MDM dashboard reports a sudden drop in the number of enrolled endpoints. Soon after, the SOC notices authentication attempts from unregistered devices using valid credentials.
Investigation reveals that an attacker:
- Disabled MDM and inventory agents on compromised endpoints.
- Used these endpoints to access internal systems through a VPN and shared drives.
- Installed unauthorized software and performed repeated update attempts to mask their activity.
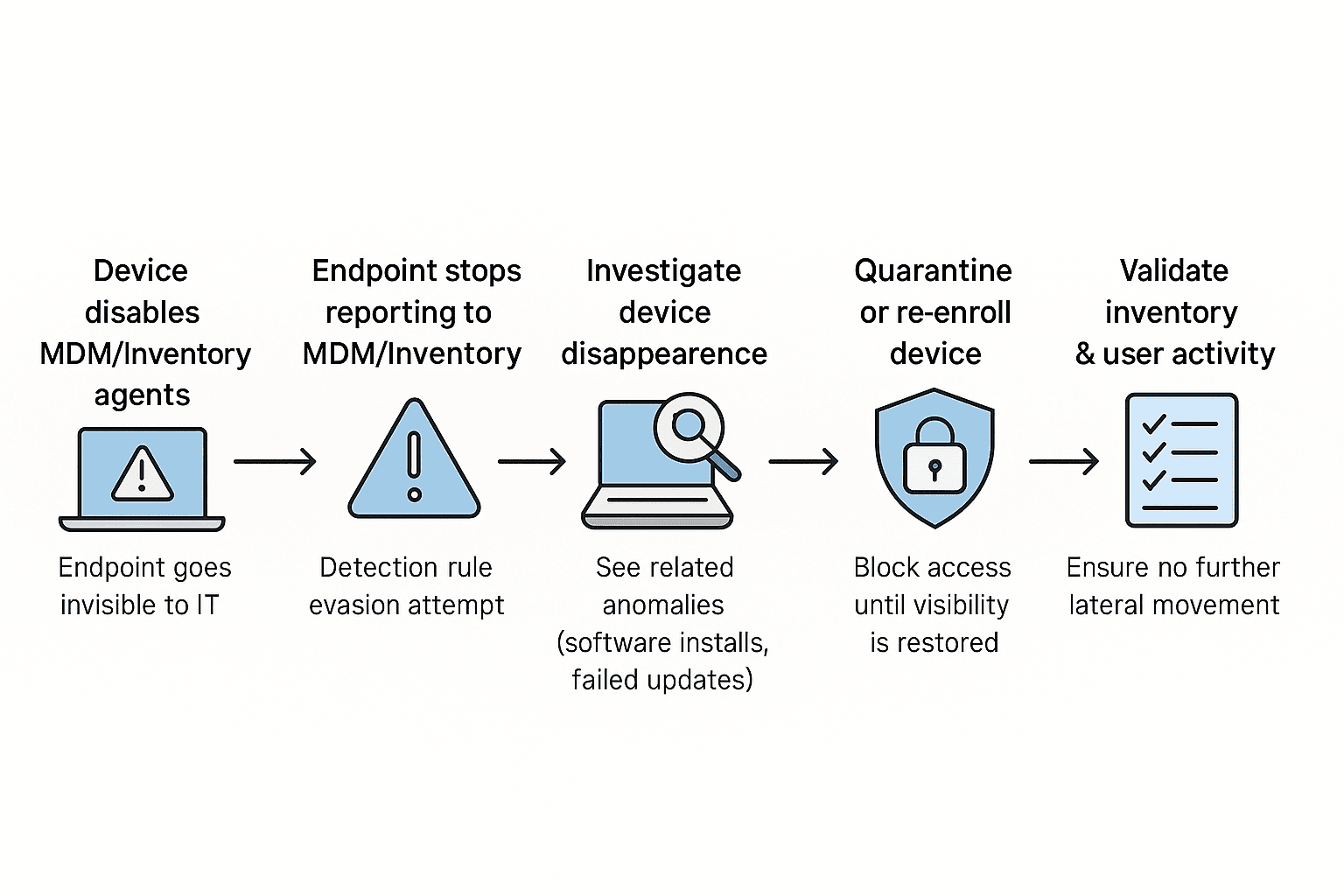
Scenario infographic:
Why this happens:
- Attackers tamper with MDM agents or registry entries to avoid device tracking.
- There is a missing correlation between MDM logs, inventory data, and authentication activity.
- Device performance anomalies are often not linked to security evasion.
What can go wrong:
- Compromised devices operate outside IT visibility.
- Lateral movement occurs undetected through legitimate credentials.
- Data theft or malware spread from invisible assets.
Prerequisites:
- Ensure MDM and EMM logs (enrollment, de-enrollment, agent status) are forwarded to Log360.
- Ensure device inventory and asset visibility events are collected from the endpoint or asset management system.
- Ensure authentication events from VPN, Active Directory, Azure AD, and other access systems are ingested into Log360.
How to detect rogue device evasion attempts using Log360
1. Identify evasion indicators
Monitor MDM and inventory logs to detect endpoints that suddenly stop reporting or deregister themselves. Detection rules such as Security Evasion – MDM help flag these events instantly.
2. Investigate in the Incident Workbench
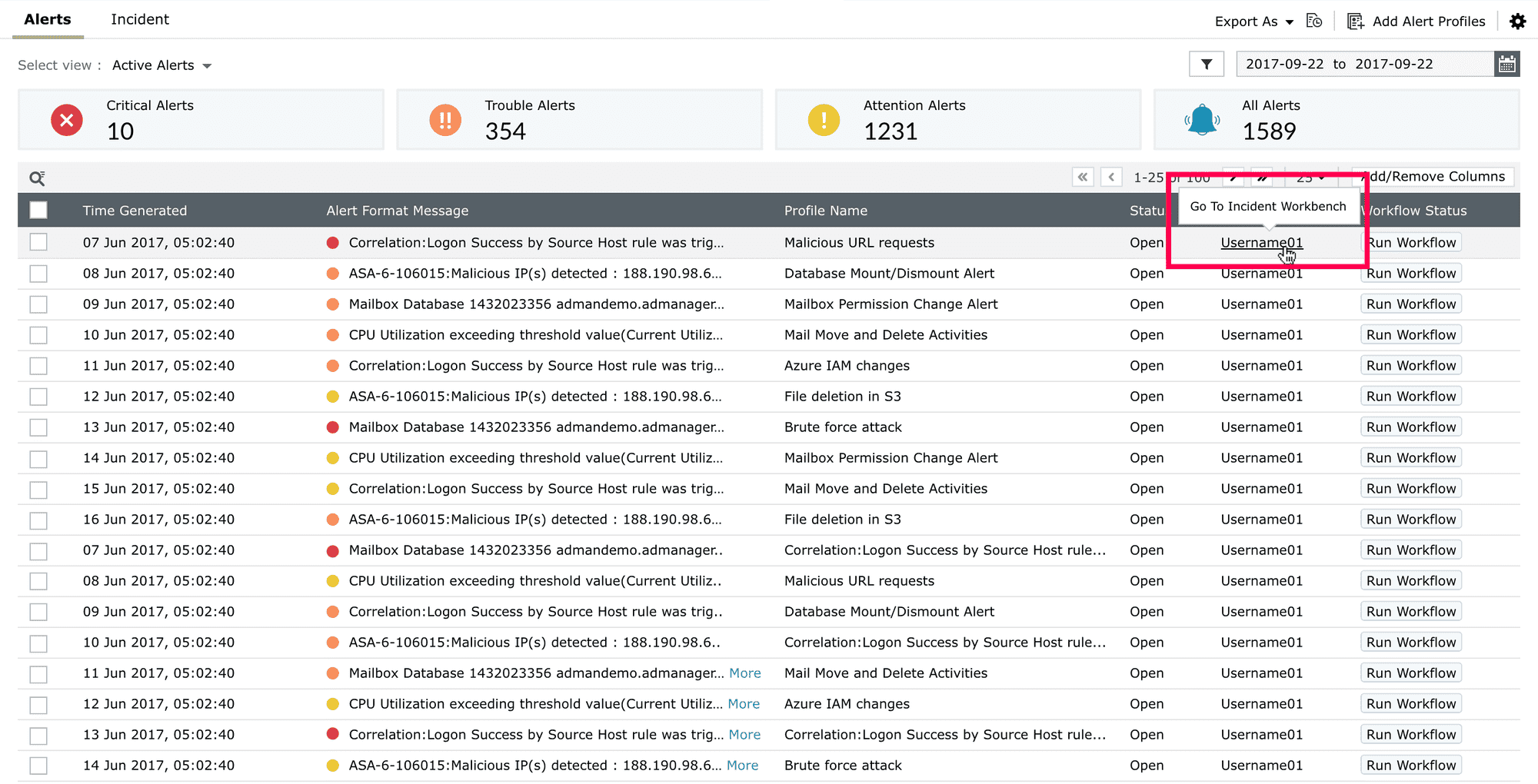
Open the Incident Workbench from alerts or reports to trace when and how the device went rogue. Correlate device disappearance with concurrent anomalies—like unauthorized software installations or failed updates to confirm compromise.
3. Respond and contain
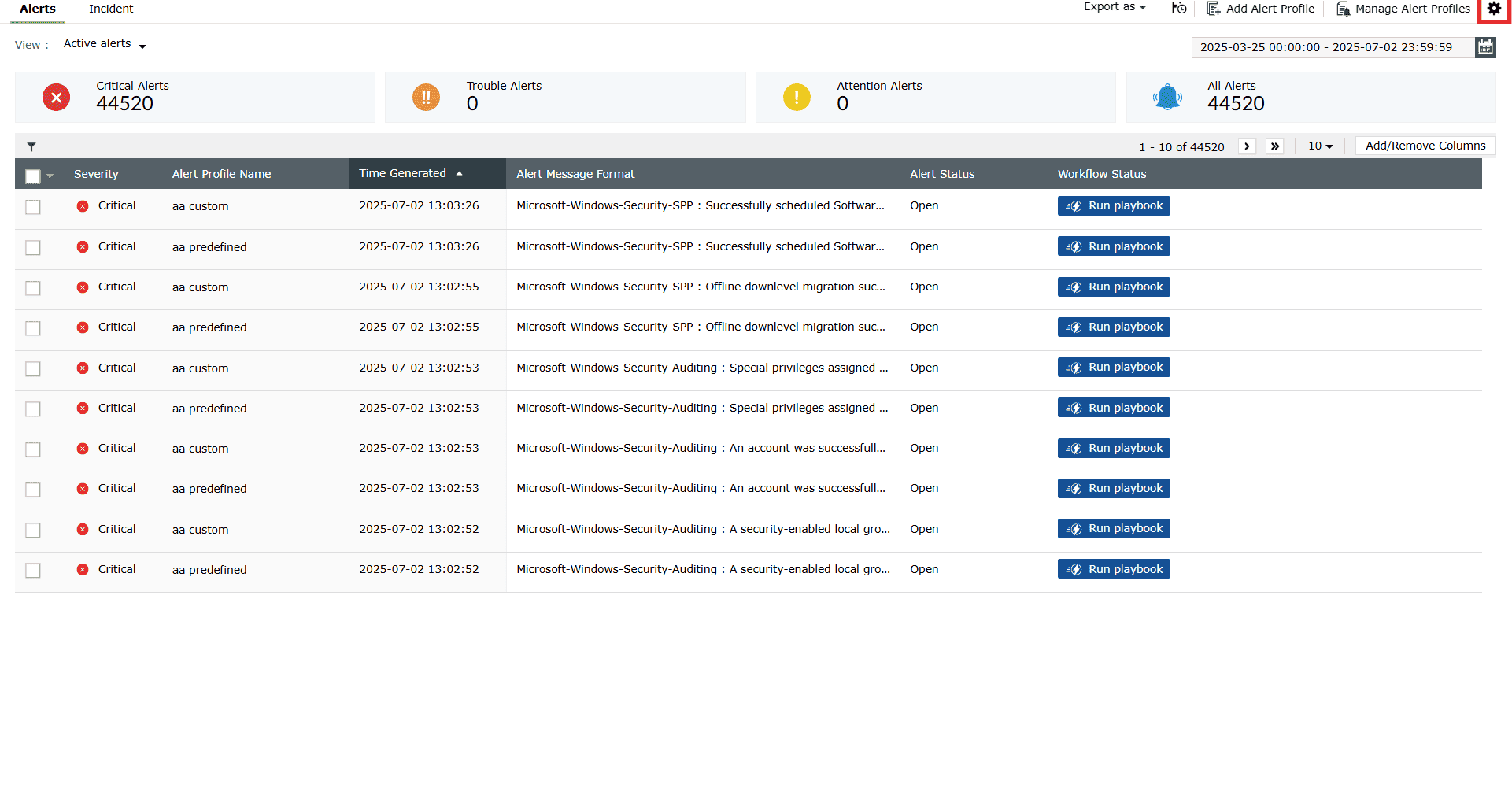
Trigger automated alerts to notify IT teams when evasion is detected. Quarantine or re-enroll rogue endpoints immediately to restore visibility and prevent further access.
Next steps:
- Establish device reporting thresholds: Flag endpoints missing from inventory or MDM check-ins beyond set intervals.
- Integrate MDM and authentication monitoring: Correlate device logs with user activities to uncover rogue access patterns.
- Automate quarantine workflows: Ensure compromised or hidden devices are isolated quickly.
- Review inventory regularly: Periodically validate device lists to identify anomalies and ensure consistent coverage.


