- Home
- SIEM use cases
- Windows Registry evasion
Windows Registry evasion
In this page
Understanding the threat
Windows Registry evasion occurs when adversaries alter registry keys or values to hide malicious activity, disable defenses, or gain persistence on an endpoint. These modifications often impact security configurations, RDP settings, user privileges, or malware’s operational parameters. Since many registry paths are commonly modified by legitimate applications, attackers exploit this trust to blend in. Without dedicated monitoring, registry-based evasion can allow malware to persist undiscovered and weaken endpoint defenses.
Category
- Endpoint threat
Relevant MITRE ATT&CK mapping
- TA0005 Defense Evasion: T1112 Modify Registry
- TA0003 Persistence: T1547 Boot or Logon Autostart Execution
Relevant compliance mapping
- CMMC IR.L3-3.7.5
- NIST DE.AE-2 (Anomalous Events)
- CIS 8.8 (IG3)
Scenario
At a company, SOC analysts observed unusual authentication failures across multiple endpoints. Further investigation revealed that RestrictedAdminMode had been silently enabled through unauthorized registry edits. In addition, several RDP-related registry keys had been modified, allowing attackers to authenticate in ways that bypassed normal credential protections. Analysts also discovered registry entries consistent with Azorult malware, indicating that attackers had altered trust-related registry values to weaken security controls and establish persistence.
These changes went undetected initially because registry updates occur frequently in Windows environments and often appear legitimate. Without targeted monitoring, the attacker was able to maintain stealth, extract data, and manipulate system configurations.
What went wrong
The SOC did not have active registry auditing or alerting in place to detect unauthorized modifications. With many legitimate processes modifying registry values, harmful changes were overlooked. No alerting existed for trust record manipulation, RDP configuration tampering, or malware-linked registry entries, allowing the attacker to persist.
How Windows Registry evasion monitoring helps
Real-time registry monitoring exposes unauthorized changes to sensitive system keys, highlights tampering attempts, and detects registry patterns linked to known malware. This visibility helps analysts uncover stealthy persistence techniques and respond before attackers escalate privileges or compromise additional systems.
Real-world trends
- Modern malware families like Azorult increasingly use registry-based persistence to operate without leaving file-based artifacts.
- RDP-focused intrusions often involve registry manipulation to weaken security settings and facilitate credential-free lateral movement.
Detecting Windows Registry evasion
Prerequisites
- Enable registry auditing on all monitored Windows endpoints.
- Ensure registry modification logs are forwarded to Log360.
- Document approved system and application registry modifications for baseline reference.
- Enable the relevant Log360 detection rules for registry tampering.
How to detect Windows Registry evasion using Log360
Log360 provides real-time visibility into registry modifications, helping analysts detect unauthorized evasion techniques quickly. Here’s how:
a. Identify suspicious registry modifications
Log360 collects registry modification events and surfaces unusual updates to security keys, RDP settings, and persistence-related values. Analysts can review registry activity reports to identify unauthorized changes, unexpected value updates, or modifications occurring outside normal system behavior.
b. Enable prebuilt detection rules and alert profiles
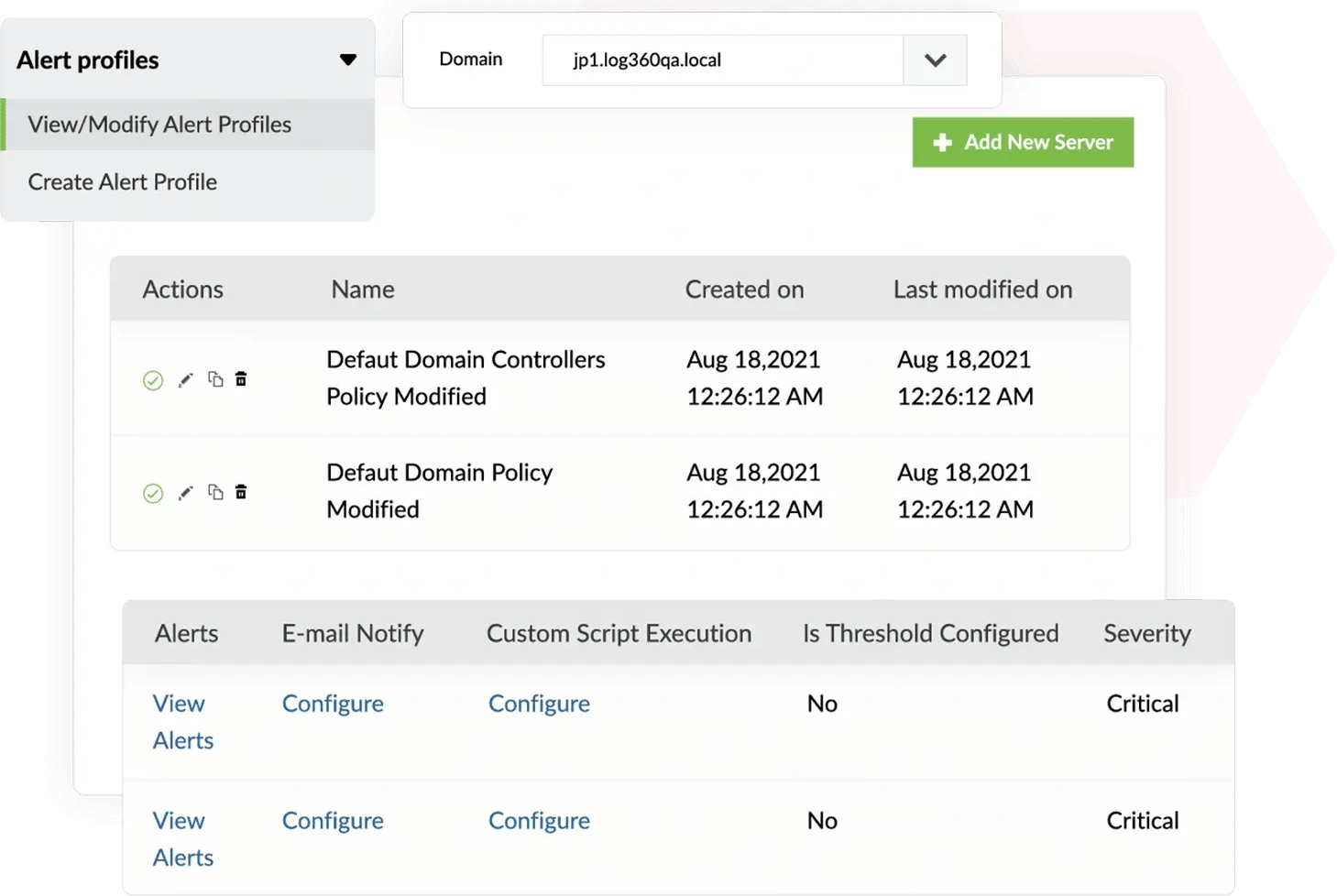
Enable alert profiles for the following detection rules to detect registry-based evasion techniques:
- Windows Registry Trust Record Modification
- Potential Tampering With RDP Related Registry Keys
- Registry Entries For Azorult Malware
- RestrictedAdminMode Registry Value Tampering
These rules highlight registry behaviors associated with stealthy persistence, defense weakening, or malware configuration.
c. Access the Incident Workbench to analyze timeline and registry activity context
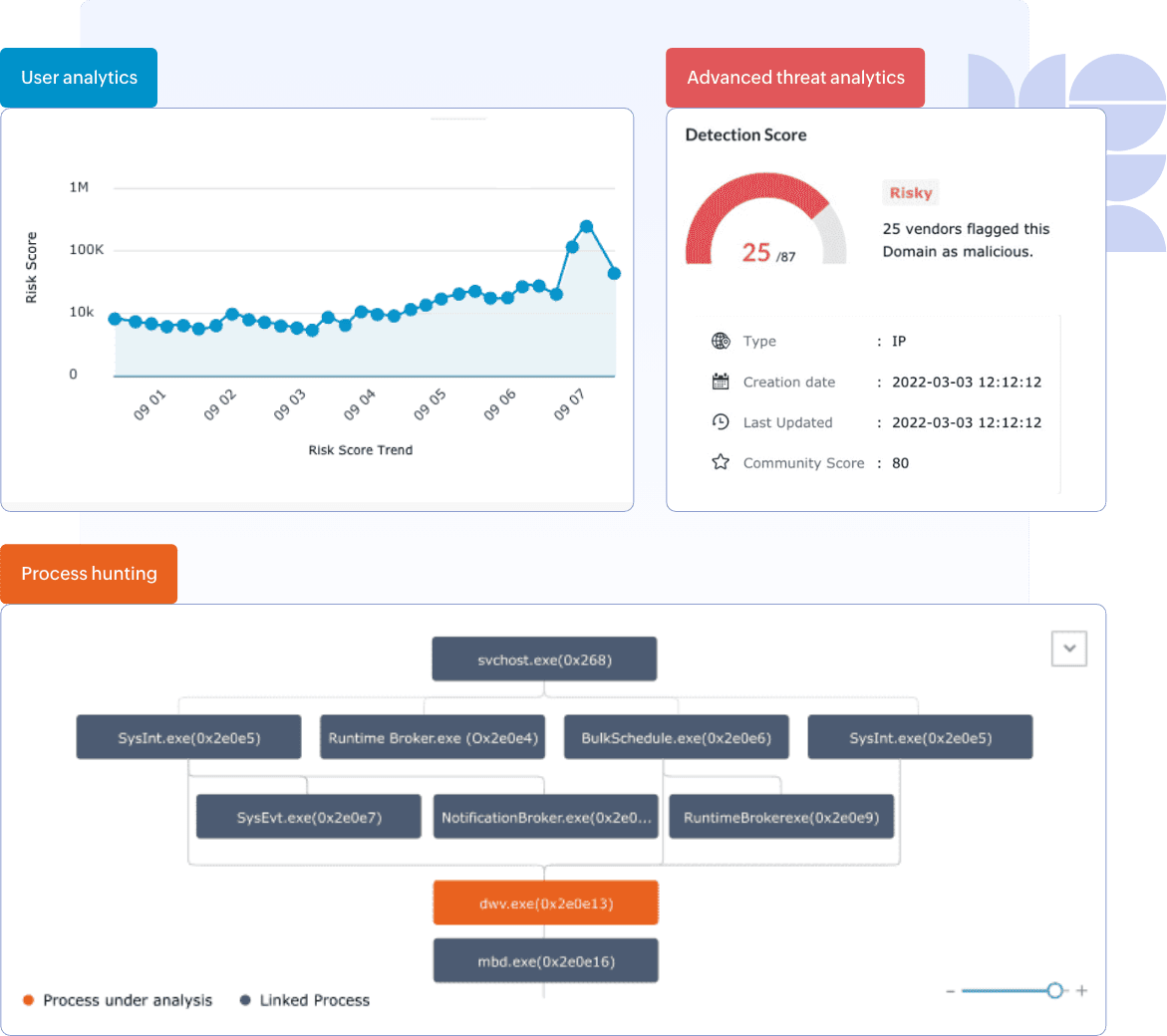
Use the Incident Workbench to review the sequence of registry edits, view related processes, and inspect user activity at the time of modification. The timeline helps analysts understand how and when the attack progressed, while the Process Hunting Tree provides additional context around suspicious executions.
d. Raise incidents and assign analysts
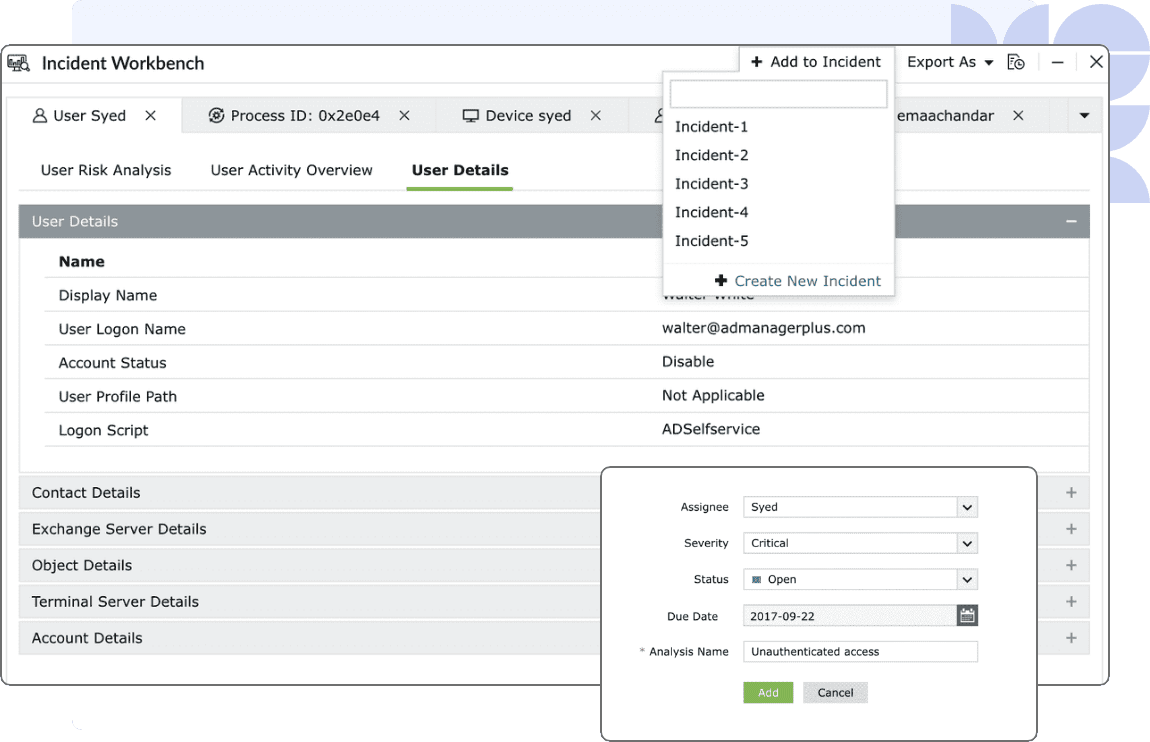
Convert suspicious registry events into incidents within the Workbench. Assign them to analysts for validation, investigation, and remediation, ensuring the evasion technique is contained and any malicious registry keys are reverted.
Next steps
- Define critical registry paths and values that require continuous monitoring.
- Configure registry tampering alert profiles in Log360 to surface unauthorized changes immediately.
- Conduct periodic reviews of registry activity patterns to identify consistent misuse or evasion attempts.
- Update incident response procedures to include steps for validating, reversing, and documenting unauthorized registry changes.


