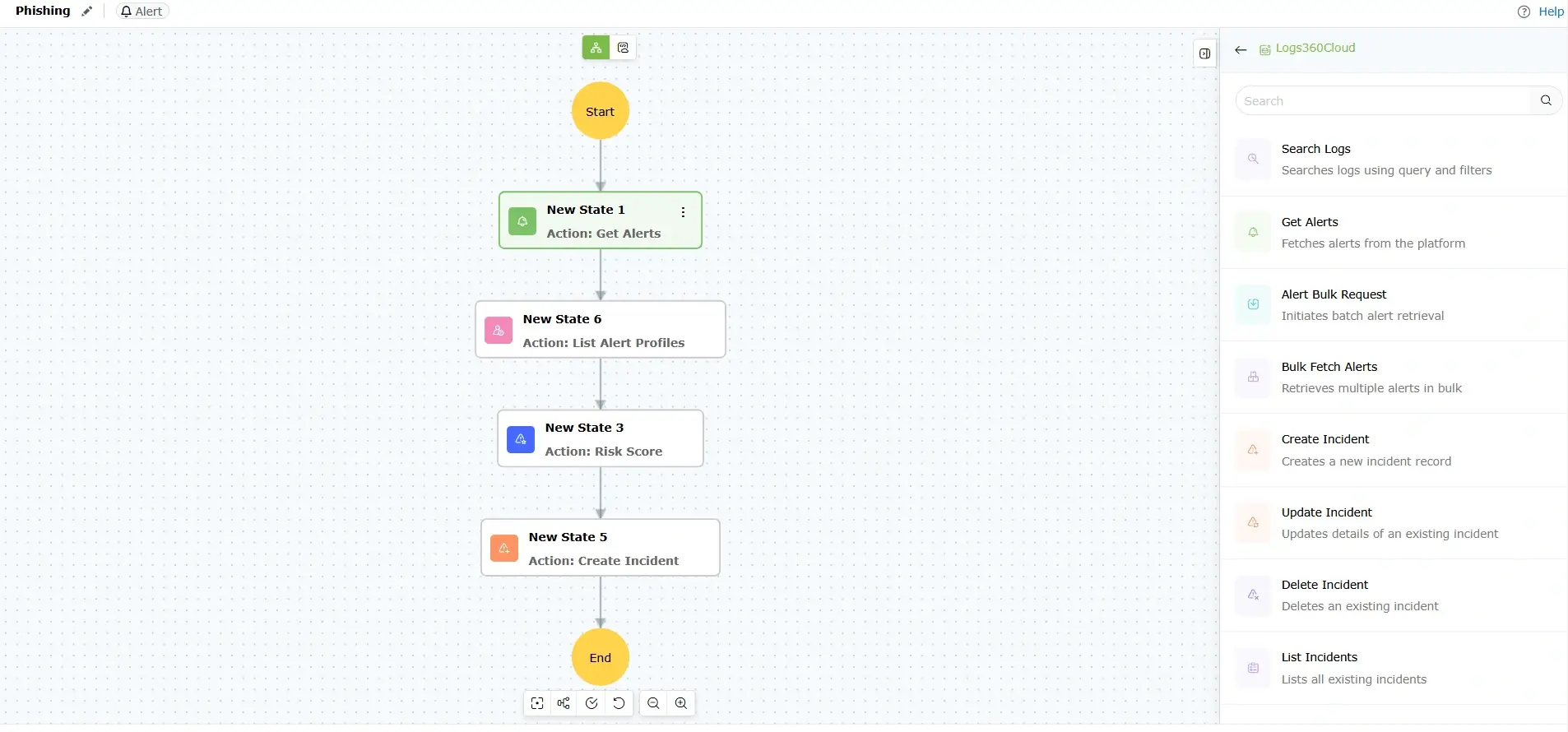
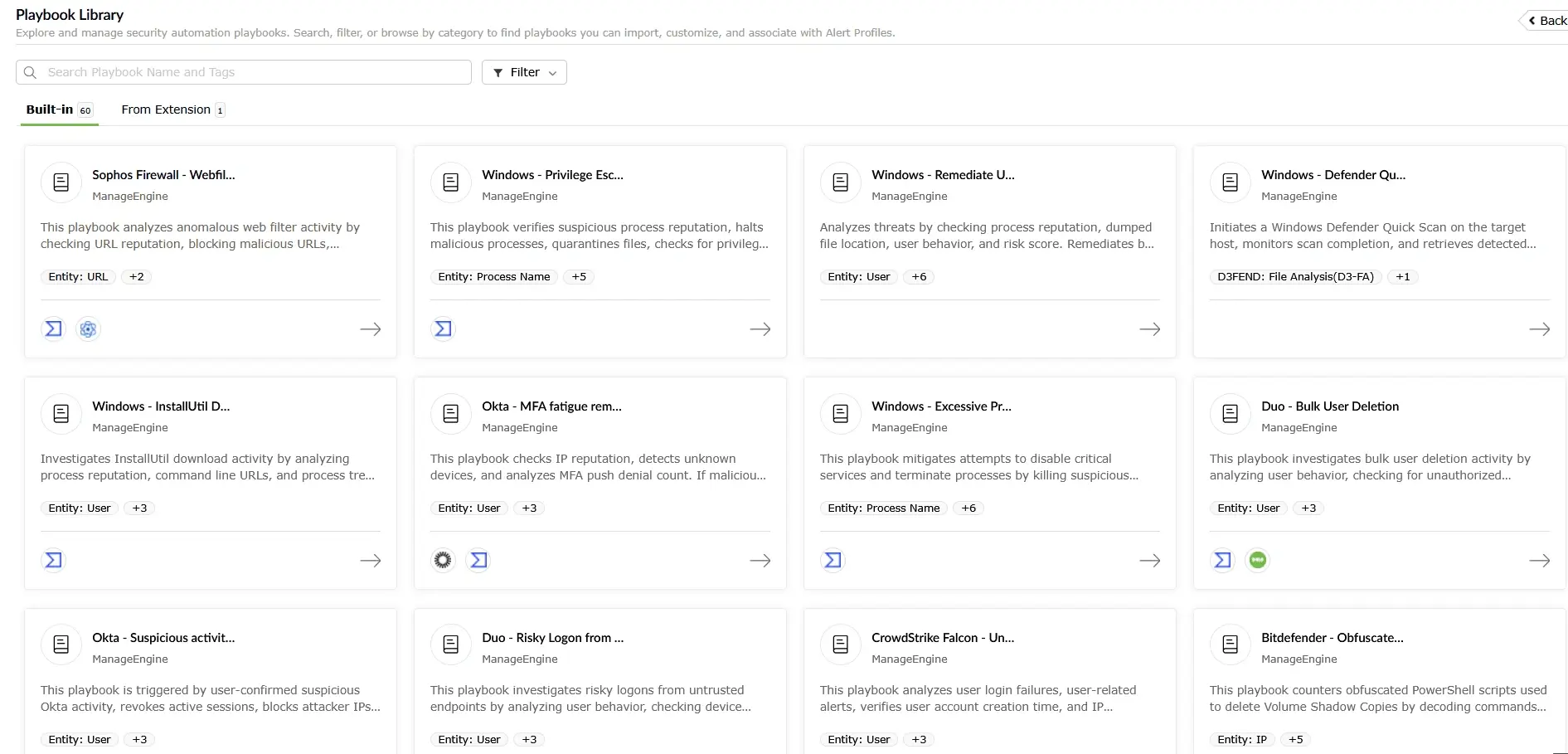
Security orchestration, automation, and response (SOAR) is a security tool that enables organizations to orchestrate multiple tools that automate incident response against security threats and incidents. It allows teams to automate low-level responses to security events, streamline incident response, and improve overall operational efficiency—thereby reducing MTTR.