Related content
What is a playbook?
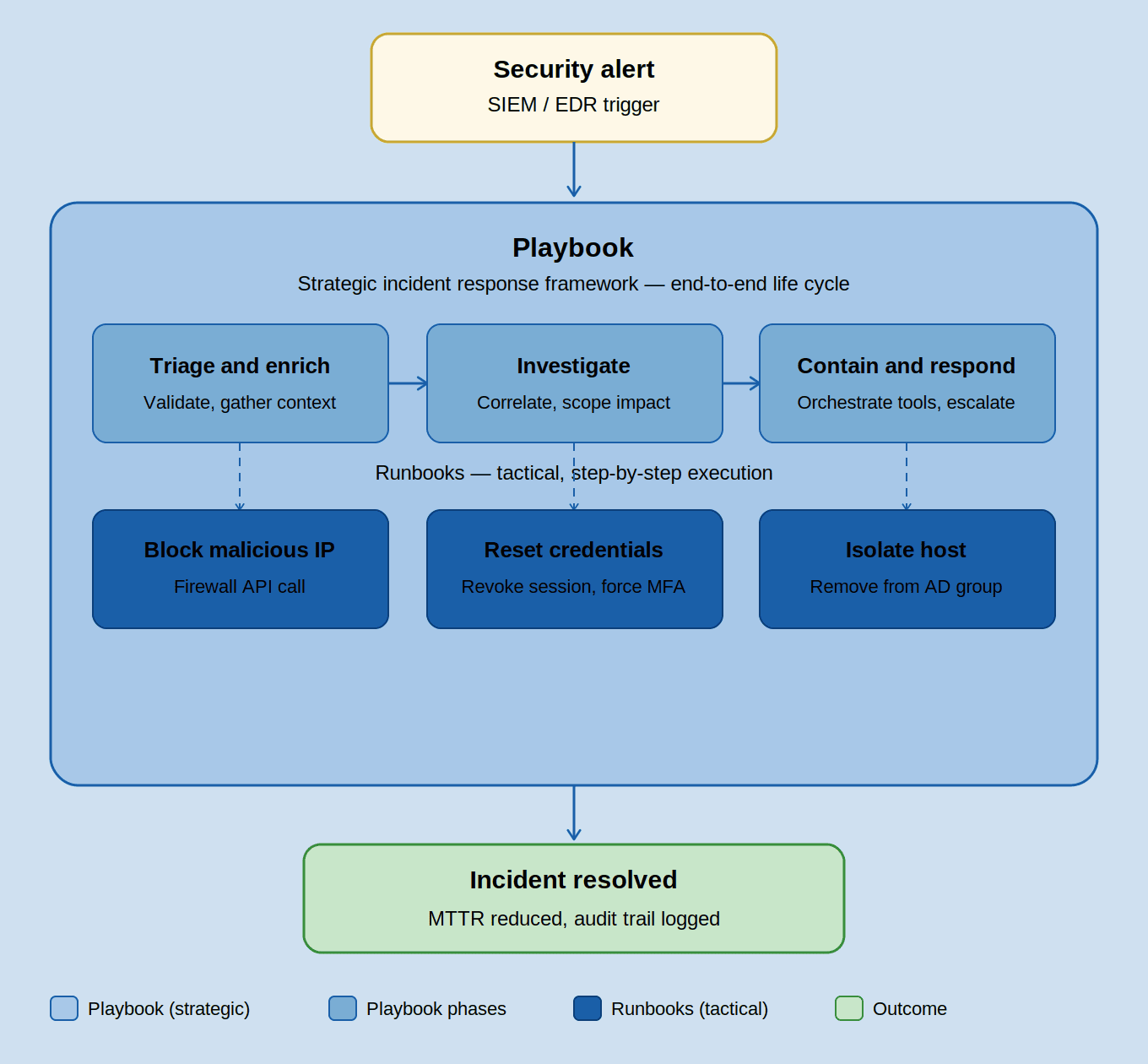
A playbook is a strategic set of actions and workflows that outline the response strategy against a threat from initial triage to final containment. It is an integral part of security orchestration, automation, and response (SOAR) platforms that automate incident response. SOAR playbooks provide end-to-end response for various categories of threats, such as ransomware and phishing.
How a playbook works: Once the SOAR platform receives an alert, it triggers an associated playbook. The playbook enriches the alert, gathers evidence, verifies the incident, and automates response workflows to neutralize the threat.
Why use a playbook: To ensure an orchestrated and automated response against threats while eliminating human errors in investigation and triage, and reducing the mean time to respond (MTTR).
What is a runbook?
A runbook is a documented set of steps an analyst follows to complete a specific task during incident response. In a runbook, an analyst works through each step by hand. For example, when a suspicious login is flagged, the analyst opens the identity management console, locates the account, disables it, then copies the user's details into a ticket and notifies the team. Every action requires human input, making response time dependent on analyst availability.
How a runbook works: It functions as a tactical how-to manual, detailing specific technical actions such as revoking a user session token via CLI or removing a host from an Active Directory group.
Why use a runbook: To automate routine tasks, such as system maintenance, configurations, and low-level responses to certain alerts.
Runbook vs. playbook
The table below differentiates a playbook and a runbook based on various criteria.
| Feature | Playbook | Runbook |
|---|---|---|
| Focus | To provide a comprehensive strategy for managing the entire life cycle of an incident. | To provide step-by-step technical instructions for completing discrete tasks with precision. |
| Scope | Playbooks cover the entire incident management process, including preparation, detection, internal communication, external notification, legal compliance, and the final forensic analysis. | A runbook focuses on specific tasks such as resetting a specific user's credentials, isolating a compromised workstation, or updating firewall rules to block a malicious IP address. |
| Working | Involves initial alert triage, enrichment, and final response execution. It utilizes conditional statements or if-then logic to determine outcomes such as response actions, escalations to executives, or notifications to relevant stakeholders. Playbooks include human-in-the-loop decision gates for high-severity incidents. | Uses linear, sequential logic to guide an analyst through a technical process or automate a specific task. It ensures that the actions are carried out in a specific sequence, one after the other. |
| Automation | Enables automated orchestration, defining how different security tools and analysts should interact across the security stack to resolve a complex security event effectively. | Can automate low-level repetitive tasks or guide analysts through routine technical procedures with minimal manual effort, depending on the automation maturity of the SOC. |
| Compliance | Ensures adherence to regulatory mandates such as the GDPR or HIPAA by documenting the timeline of the incident and collecting relevant attack evidence. | Ensures technical integrity and auditability but does not directly support compliance. |
| Flexibility | Playbooks can be updated according to the security needs of the business based on the evolving threat landscape. | Updated through formal change management to ensure consistency, prevent ad-hoc deviations, and maintain auditability across the SOC. |
| Impact on MTTR | Aims to drastically reduce MTTR through security automation and orchestration, minimizing attacker dwell time and ensuring rapid remediation. | Does not directly impact MTTR but enables analysts to automate routine repetitive actions, allowing them to focus on high priority incidents. |
When to use a playbook or a runbook
Playbook: For strategic incident response
Use a playbook when you need a high-level strategic framework to orchestrate an entire incident response life cycle. It keeps technical teams, legal counsel, and executives aligned during complex threats. It serves as the response engine when specific threats such as ransomware are confirmed and requires a coordinated, multi-departmental response. Further, it also helps you ensure compliance by following a standardized, auditable process to meet industry certifications or legal evidence-handling requirements.
Runbook: For tactical task execution
Use a runbook when you need technical instructions or workflows to perform a specific, repeatable task with absolute precision, minimizing the risk of human error and maximizing operational speed. Runbooks help perform standard actions such as resetting a compromised user’s password, revoking an API key, or blocking a malicious domain immediately using the relevant tool and without searching for the correct command-line syntax. It also serves as a blueprint for transitioning from a manual SOC to an automated SOAR-powered security team.
Explore ManageEngine Log360's SIEM and SOAR capabilities with a personalized walk-through.
Frequently asked questions
What is the difference between a playbook and a runbook?
A playbook governs the end-to-end incident response life cycle from detection to recovery by orchestrating and automating the the security stack, enabling the SOC to reduce the MTTR. A runbook, by contrast, provides the specific commands or tool-based actions needed to execute the playbook’s requirements, enabling the SOC to automate routine repetitive tasks and focus on high-priority incidents.
What is a runbook?
A runbook is a standard set of instructions or workflows that outlines the steps required to complete a specific task within an incident response plan. The primary advantage of a runbook is operational consistency because it removes the guesswork for analysts by providing the specific commands, scripts, or tool-based actions needed to neutralize a threat.
Can a runbook and playbook be used together?
Yes, they work best as a pair. The playbook governs the overall response strategy, while runbooks execute the individual technical steps within it. When a threat is detected, the playbook decides what needs to happen; the runbooks handle precisely how each action gets done.
What is the difference between a playbook and an SOP?
A standard operating procedure (SOP) is a fixed document for routine, repeatable tasks performed the same way every time. A playbook is dynamic, using conditional logic to adapt responses based on the threat scenario. SOPs prioritize procedural consistency; playbooks prioritize strategic, context-aware decision-making during active security incidents.
- What is a playbook?
- What is a runbook?
- Runbook vs. playbook
- When to use a playbook or a runbook