What are SOAR tools?
Security orchestration, automation, and response (SOAR) tools, are software platforms designed to help security operations centers (SOCs) teams to integrate disparate security tools, automate repetitive tasks, and streamline their incident response workflows.
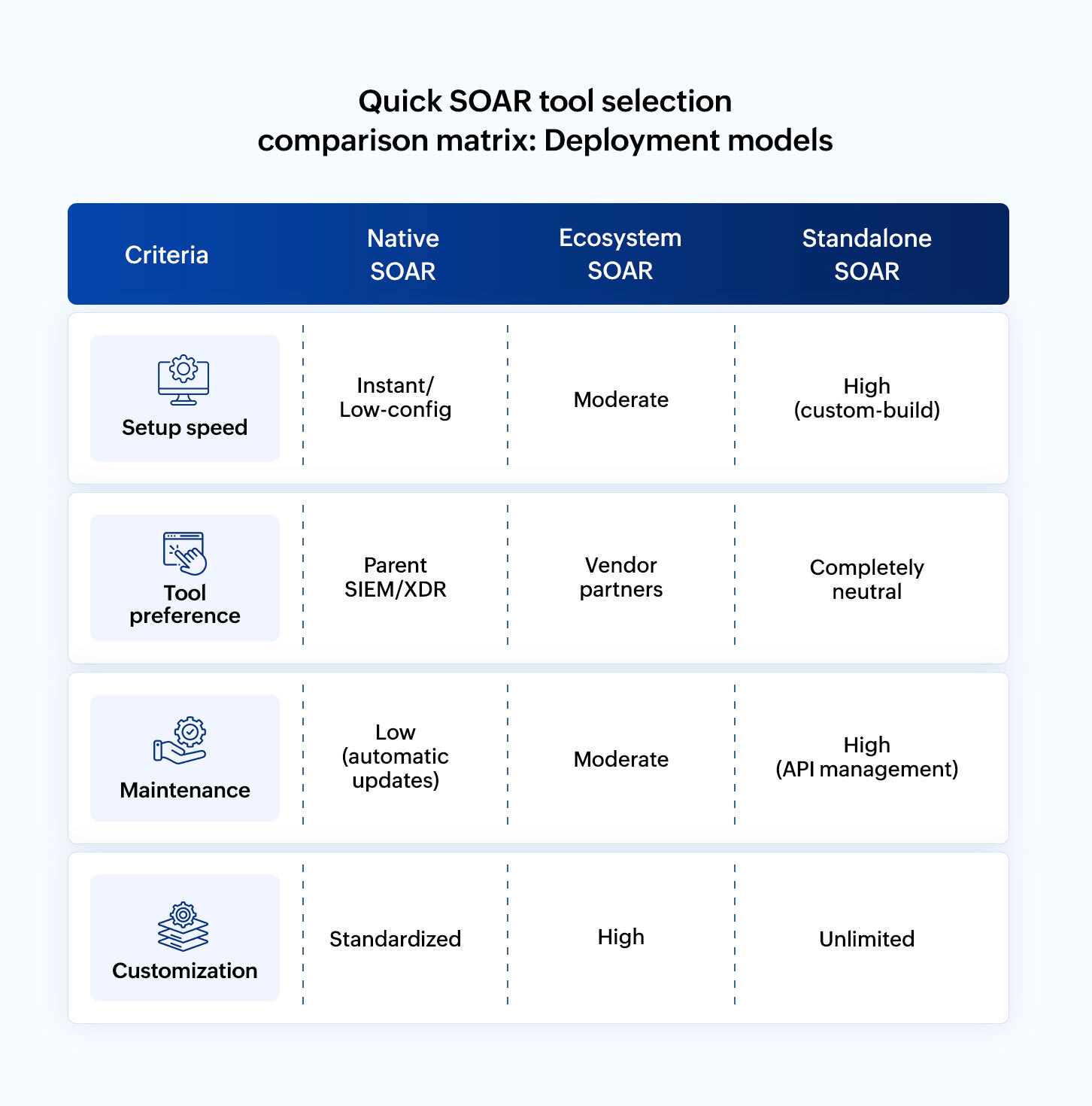
SOAR tools deployment models:
The SOAR market has matured into three distinct deployments models. Choosing between them depends on whether you prioritize integration speed, vendor ecosystem, synergy, or unlimited customization.
Native SOAR:
In this deployment model, SOAR tools are embedded directly within another primary security platform, most commonly a SIEM or XDR.
- How it works: Your automation engine and detection logs are connected.There's no API bridge to build between your SIEM/XDR and SOAR because they share the same database and user interface.
- The advantage: Since it's preintegrated, you can activate playbooks in minutes rather than week.
- The trade-off: Vendor lock-in. Native SOARs are often optimized for their parent company's tools and might have less flexibility when connecting to rare, third-party apps.
Ecosystem SOAR:
This refers to a platform designed by major vendor to act as the security operating for their entire product family and broad network of approved partners.
- How it works: It is built to leverage a specific security fabric. While it can connect to anything, it works best when orchestrating a specific ecosystem (e.g., your firewall, EDR, and mail gateway are all from the same partner network).
- The advantage: Deep orchestration. These tools offer active integrations that go beyond reading logs—they can perform deep configuration changes across the vendor's entire ecosystem with high reliability.
- The trade-off: High complexity. These platforms often require dedicated engineers to maintain the connective tissue between ecosystem components.
Standalone SOAR:
A pure-play automation platform that doesn't belong to any SIEM or firewall vendor. It is a neutral third party.
- How it works: It is a blank canvas designed to connect to any tool with an API. It treats every security tool (Microsoft, CrowdStrike, Google, etc.) as an equal node in its workflow.
- The advantage: You can swap out your SIEM or EDR tomorrow, and your SOAR logic stays exactly the same. They are usually no-code leaders, allowing for the most creative and custom automations.
- The trade-off: Blank canvas syndrome. You have to build almost everything yourself. It doesn't know how to investigate a threat until you teach it.
Related content
The SOAR ecosystem: Building a high-velocity security fabric
A SOAR tool is not a silo; it is the connective tissue of your entire security stack.The modern security operations ecosystem is defined by three critical layers:
- The signal layer (SIEM, EDR & XDR): This is the central hub where detection happens. Standalone SOAR tools take the high-fidelity alert from these systems as input. However, in 2026, the market is maturing into a converged architecture where SOAR is built as a native capability in these systems reducing the API latency.
- The intelligent layer (TIP & enrichment): Modern SOARs automatically query the threat intelligent platforms (TIPs) for data enrichment and expedite the investigations with accuracy. When a suspicious IP is detected, the SOAR automatically checks the reputation on VirusTotal and enriches the alert with the data before IT teams ever see it.
- The action layer: This is where the SOAR executes the commands across your infrastructure. It could be forcing password resets or revoking sessions in identity infrastructure like Okta or AD, isolating endpoints from network via EDR, automatically blacklisting malicious IP in your firewall, and more.
As modern enterprises are moving away from volume-based to decision-based staffing, especially in the security operations department where there's a shortage of skills, SOAR redefines how SOC operates with lean staffing.
| Role | Focus | How SOAR redefines SOC |
|---|---|---|
| Tier 1: The validator | Validates AI-enriched cases; handles high-level exceptions | SOAR automates most of their clicks, turning them into reviewers rather than hunters. |
| Tier 2: Incident designer | Complex investigations, lateral movement analysis, and containment strategy. | Uses SOAR to orchestrate complex responses across multiple cloud and on-premises environments. |
| Tier 3: Detection engineer | Proactive threat hunting and playbook engineering. | They don't just hunt threats; they build the logic that the SOAR uses to automate future detections. |
| SOC Manager | Resource allocation, ROI reporting, and vendor management. | Relies on SOAR metrics (MTTR reduction, hours saved) to justify the security budget. |
Top SOAR tools
Selecting the right SOAR solution has a direct impact on how efficiently security teams operate and how effectively incidents are handled. The market includes a wide range of options, from standalone SOAR platforms to SOAR capabilities built into broader security ecosystems.
ManageEngine Log360
ManageEngine Log360 is a unified SIEM solution with native SOAR capabilities powered by the Zoho Qntrl Circuit orchestration engine. This built-in engine delivers comprehensive security orchestration, automation, and response within a single console, eliminating the need for a separate SOAR platform or complex integrations.
With support for both on-premises and cloud deployment, Log360 offers a cost-effective, rapid-deployment model and significantly lower total cost of ownership than managing standalone SIEM and SOAR products. It is especially suited for organizations that want centralized automation, streamlined operations, and faster mean time to respond (MTTR) without added complexity or expense.
Highlights of Log360:
- Unified SIEM–SOAR architecture: Combines threat detection, investigation, and automated response in a single platform, eliminating data silos and reducing integration overhead.
- Prebuilt playbooks and customizable workflows: Enables faster time-to-value with ready-to-use automation for common incident scenarios, while allowing customization to match organizational response processes
- Bidirectional integrations with security tools: Supports automated actions across firewalls, EDR solutions, Active Directory, cloud services, and ticketing systems directly from investigation workflows.
- Low-code workflow builder: The visual, low-code playbook builder in Log360 supports branching conditions for decision logic, parallel execution for simultaneous tasks, wait states for controlled delays, and batch processing for grouped operations, allowing multi-step sequences to run efficiently and complete investigations faster.
- Integrated case management and incident tracking: Helps teams manage alerts, investigations, and response actions within a unified incident life cycle.
- Automatic data enrichment during investigation: Playbooks pull context automatically by checking VirusTotal to obtain reputation scores for IPs, URLs, and file hashes. They retrieve UEBA risk scores to evaluate behavioral anomalies for users and hosts. Also, they perform user, group, role, and privilege checks to assess access levels and exposure. In addition, they detect anomalies in devices, autonomous system numbers (ASN), and geographic locations by comparing current activity with historical patterns. Finally, they cross-reference prior alert history from Log360 to identify correlated signals from identity and endpoint logs.
- Cost-effective and scalable licensing: Delivers enterprise-grade SOAR capabilities without the high cost typically associated with standalone SOAR platforms. Ideal for organizations seeking integrated threat detection and response, centralized automation, and streamlined security operations without managing multiple vendor platforms.
Palo Alto Networks Cortex XSOAR
Palo Alto Networks Cortex XSOAR is a comprehensive SOAR platform recognized for its extensive integration marketplace, sophisticated playbook engine, and strong threat intelligence capabilities. It supports complex automation scenarios and is backed by a mature ecosystem of prebuilt integrations and community-contributed content. Cortex XSOAR's architecture allows organizations to orchestrate workflows across hundreds of security tools, delivering coordinated response and deep incident context.
Considerations:
Palo Alto Networks Cortex XSOAR offers powerful automation but often introduces considerable complexity. Teams commonly face steep learning curves in playbook development, along with ongoing maintenance demands. Although the integration marketplace is broad, deeper customization typically requires advanced Python skills. Its pricing can escalate as automation volume grows, and many organizations note that the platform is resource-intensive, requiring strong infrastructure and dedicated engineering support for smooth performance.
Splunk SOAR (formerly Phantom)
Splunk SOAR is a mature automation platform recognized for its visual playbook editor, strong case management, and seamless integration with Splunk’s security ecosystem. It supports both attended and unattended automation, giving SOCs flexibility across operational models. The platform benefits from an active community contributing playbooks and apps, and it excels in data-driven automation by using Splunk’s analytics depth to power context-aware response actions.
Considerations:
Users often cite high total cost of ownership, particularly when deployed alongside Splunk SIEM. The platform requires significant expertise for advanced playbook development, and some organizations report that integrations outside the Splunk ecosystem may require additional configuration effort. Licensing complexity and per-action pricing models can make cost forecasting challenging as automation adoption grows. Organizations should carefully evaluate total implementation costs, including professional services, ongoing maintenance, and infrastructure requirements.
IBM Security QRadar SOAR (formerly Resilient)
IBM QRadar SOAR specializes in incident response orchestration with strong case management, regulatory compliance workflows, and mature threat intelligence integration. Users value its detailed audit trails, customizable incident forms, and support for complex approval workflows across global teams.The platform features a dynamic playbook designer, breach response management capabilities aligned with global privacy regulations.
Considerations:
Reviews frequently mention complexity in initial setup and configuration. The platform's user interface can feel dated compared to newer competitors, and advanced automation may require professional services engagement. Integration depth varies significantly across the vendor ecosystem, and organizations often supplement with custom API development for specialized tools.
The SaaS version of IBM QRadar SOAR was acquired by Palo Alto Networks and is now known as Palo Alto XSIAM. The standalone version remains available as an on-premises solution maintained by IBM.
Rapid7 InsightConnect
Rapid7 InsightConnect is known for its user-friendly interface, cloud-native design, and accessible automation builder. It suits teams that want fast deployment and simple workflow creation without heavy development effort. InsightConnect works seamlessly with the broader Rapid7 Insight Platform, including SIEM, vulnerability management, and offensive security tools. It also provides an extensive library of prebuilt workflows and a visual drag-and-drop playbook editor for quick automation.
Considerations:
While deployment is simple, InsightConnect’s advanced orchestration features are not as mature as those offered by enterprise-focused competitors. It works well for mid-sized teams but may fall short for large enterprises needing deep customization and scale. Its integration ecosystem is expanding but still narrower than long-established SOAR platforms. Teams should confirm that available integrations align with their specific security stack requirements.
Swimlane
Swimlane provides a low-code automation platform with strong visualization, flexible case management, and analyst-driven workflow design. Its Turbine engine delivers cloud-scale automation with broad integration support, allowing teams to build workflows without deep programming skills. Swimlane positions itself as an AI-enabled security automation platform that extends beyond traditional SOAR and unifies operations into a single system of record.
Considerations:
As a newer entrant in SOAR, some users mention that its integration library is still maturing and may require custom connector development for specialized tools. Organizations evaluating Swimlane should verify whether the available integrations support their security stack and factor in the resources needed to build custom automations. The platform suits teams that prioritize modern low-code automation, strong visualization features, and the flexibility to support use cases beyond traditional SOC operations.
Tines
Tines is a no-code automation platform gaining recognition for its intuitive workflow builder ("Stories"), modern user experience, and flexible pricing model. Security teams value its accessibility and the ability to automate workflows quickly without traditional development skills. The platform offers consumption-based pricing and is particularly popular among teams seeking automation agility without the overhead of traditional SOAR platforms.
Considerations:
Tines focuses primarily on workflow automation rather than comprehensive SOAR features like advanced case management or built-in threat intelligence. Organizations may need to supplement Tines with additional tools for complete incident response life cycle management. The platform is best suited for teams prioritizing automation agility over all-in-one SOAR functionality.
Microsoft Sentinel with Automation
Microsoft Sentinel includes native automation and orchestration capabilities through Azure Logic Apps and Playbooks , particularly effective for organizations invested in the Microsoft ecosystem. Its cloud-native architecture and integration with Microsoft 365 Defender provide coordinated response across Microsoft security tools.
Considerations:
While automation within the Microsoft ecosystem is streamlined, orchestrating third-party security tools often requires additional Azure Logic Apps expertise and can become complex. Pricing models based on Logic App executions can be difficult to forecast. Organizations with diverse, multi-vendor security stacks may find orchestration more challenging than dedicated SOAR platforms.Teams should carefully evaluate Logic Apps pricing and complexity when planning extensive automation beyond Microsoft's native ecosystem.
Siemplify (now Google Security Operations)
Siemplify, now part of Google Security Operations, is known for its visual case management, intuitive playbook builder, and strong analyst-focused design. It offers customizable investigation workflows and integrates tightly with Google Chronicle for unified detection and response, and is supported by Mandiant intelligence enrichment. The platform delivers cloud-scale automation backed by Google’s analytics and ML.
Considerations:
Following Google's acquisition, some customers have expressed uncertainty about the product roadmap and integration strategy. Organizations should evaluate Google's long-term vision for the platform and how it aligns with their security architecture plans. Integration availability outside Google Cloud may require additional consideration.
FortiSOAR
Fortinet FortiSOAR is a SOAR platform built for SOCs that need scalable, playbook-driven automation. It provides a visual workflow editor for handling phishing analysis, malware containment, vulnerability response, and other recurring incidents. The platform includes extensive prebuilt connectors across firewalls, EDR tools, SIEM platforms, and threat intelligence sources, supported by strong case management, audit trails, and collaboration features.
Considerations:
FortiSOAR is a powerful platform that can be complex to deploy and manage, requiring significant expertise and resources for full implementation. It is a premium-priced enterprise solution best suited for large organizations with dedicated SOC teams and Fortinet infrastructure. Organizations should evaluate whether the platform's capabilities justify the investment and implementation commitment.
For more detailed, real-world reviews and ratings of SOAR tools, visit user review platforms like Gartner Peer Insights or Capterra.
Critical 2026 SOAR tool selection questions for vendors
- Does your SOAR tool offer explainable AI? Can it show step-by-step log of why it decided to isolate an executive's laptop?
- Is it bidirectional? Can it change the firewall rule or does it just alert me to do it?
- What is the maintenance-value-ratio? How many hours a week will my tier-3 analyst spend just keeping your playbooks from breaking?
Selecting the right SOAR tool: 2026 strategy guide
Modern enterprises who look to automate their security operations are experiencing automation debt, the hidden cost of maintaining complex scripts and outdated playbooks. If you are looking to deploy or replace your existing SOAR tools or automation integration with your SIEM/XDR, look for the below five pillars to evaluate your next platform:
1. Architectural fit: Standalone vs. unified
- Unified SIEM-SOAR: Best for enterprises looking to reduce the tools sprawl. SIEM solutions with native SOAR capabilities offer built-in orchestration, meaning your detection logs and response actions share a common data model. This eliminates the need to build complex API bridges for orchestration which significantly lowers the total cost of ownership (TCO).
- Best-of-breed standalone SOAR tools: Ideal for massive, multi-vendor environments that require a neutral orchestration hub to connect dozens of legacy and cloud systems. These offer the highest level of customization but require a dedicated engineering team.
The choice: Choose unified SIEM-SOAR tools if you want to reduce tool sprawl and operational overhead, need the fastest ROI with minimal configuration. Alternatively, if you have a massive and heterogeneous environment and dedicated team to manage complex integrations, go for a standalone SOAR tool.
2. Operational maturity: Static playbooks vs. Agentic AI
- Traditional static playbooks: These follow a rigid if-then logic. They are great for predictable tasks such as if an IP is found malicious, block the traffic from that IP, but break when an attacker changes tactics.
- Agentic AI-driven playbooks: SOAR tools with agentic AI support use autonomous agents to reason through an investigation and take necessary steps. Instead of following a predrawn map, the agents understand the goal and autonomously queries the EDR, identity logs, and threat intel to provide a verdict.
The choice: If your SOC is suffering from alert fatigue, prioritize agentic AI. If you need to automate complex business processes, stick with traditional static playbooks. Choose SOAR tool that has both these capabilities and enable agentic AI when you need.
3. Staffing and skillset match: Low-code vs full-scripting
Automation is only as good as the person building the playbooks. Depending on the maturity of your SOC and staffing, choose one of the below options:
- No-code/low-code: These are SOAR tools with visual drag-and-drop canvases. They empower tier 1 analysts to build automations without knowing Python, preventing a bottleneck at engineering level.
- Full-scripting (example: Splunk SOAR): These SOAR tools allow for deep Python customization. These legacy SOAR tools are essential for unique enterprise workflow that require complex data transformation.
The choice: Choose no-code/low-code SOAR tools if your SOC is staffed by generalist analyst who need to build and fix their own workflows. Choose full-scripting SOAR tools if you have dedicated security devops team that has granular control over every line of automation code.
| If your SOC is | And your staffing is | Your best SOAR fit is |
|---|---|---|
| Lean/mid-market | 1-5 generatlist analyst | Unified SIEM with SOAR |
| Global enterprise | 24/7; Tiers 1-3 | Ecosystem SOAR |
| Agile/startups | Security engineers | No-code SOAR engines |
| Overwhelmed | Understaffed | Agentic AI-powered SOAR |
SOAR tool buying tip:
During your SOAR tool evaluation or POC, ask the vendor to show their best demo. Ask your Tier 1 analyst to build phishing triage playbook from scratch. If they can do it under two weeks without a consultant, the tool will likely to become a shelfware.
Ready to see how unified SIEM + SOAR simplifies your security operations? Schedule a SOAR demonstration with our experts
Selecting the right SOAR tool: Key features
Choosing the right SOAR tool is essential for scaling security operations and improving analyst efficiency. Leading analyst firms such as Gartner® recommend evaluating SOAR solutions based on core capabilities such as orchestration scope, automation depth, case management, and the breadth of integrations. These criteria provide a useful baseline for comparing platforms.
Beyond core features, successful adoption depends on practical considerations identified during deployment. These include how well the platform integrates with your existing security tools, how easily your team can build and maintain playbooks, and how closely the solution aligns with established incident response workflows. Organizations should also consider deployment flexibility (on-premises or cloud) and the role of AI-driven automation in improving decision-making and response accuracy.
To make a confident, future-proof choice, prioritize a SOAR tool that offers:
Intelligent automation engine
Advanced playbook capabilities with conditional logic, branching workflows, and context-aware decision-making to handle complex incident scenarios. AI-powered automation that learns from analyst actions and workflow optimizations is increasingly valuable.
Intuitive playbook development
Visual workflow builders and low-code or no-code interfaces that allow security analysts to create and modify playbooks without extensive programming knowledge, reducing reliance on development resources and accelerating automation adoption.
Robust case management
Comprehensive incident tracking, collaboration features, and audit trails that support investigation workflows, team coordination, and post-incident analysis. Customizable dashboards and reporting capabilities are essential for stakeholder communication.
Threat intelligence integration
Native support for ingesting, enriching, and acting on threat intelligence from multiple sources, enabling automated indicator lookups, contextual enrichment, and intelligence-driven response decisions.
Flexible deployment options
Support for on-premises, cloud, and hybrid deployment models that align with infrastructure strategy and data requirements, with scalability to support expanding automation adoption grows across your organization.
Prebuilt content library
Extensive collections of vendor-maintained playbooks, integration connectors, and use case templates that accelerate time-to-value and incorporate industry best practices for common incident scenarios.
Metrics and analytics
Built-in reporting that tracks automation effectiveness, MTTR reduction, analyst productivity, and workflow performance, helping teams demonstrate ROI and identify areas for optimization.
Ultimately, the best SOAR tools strike a balance between advanced automation and everyday usability, taking into account team skill levels, resource constraints, and operational priorities. Focusing on these capabilities helps organizations achieve immediate efficiency gains while building a scalable foundation for long-term security operations.
SOAR tool deployment: Critical risks you can't afford to miss
Implementing a SOAR tool can significantly improve security operations efficiency, but many organizations encounter predictable operational and technical challenges during deployment and adoption. Understanding these risks early helps teams plan more effectively and avoid underperforming SOAR implementations. Common challenges include:
1. Automating garbage processes
Automating poorly designed, inefficient, or unnecessary workflows simply accelerates bad processes. This creates more noise, wastes resources, and delivers little real value to the SOC.
Fix: First map and refine your existing incident response processes. Focus automation on high-impact, well-defined use cases only, such as alert enrichment or ticket creation, to build early wins and maintain trust.
2. The playbook maintenance tax
Sophisticated playbooks often break due to API changes, tool upgrades, evolving threats, or expired credentials. This creates a heavy ongoing maintenance burden that consumes analyst time and reduces overall automation benefits.
Fix: Select platforms with agentic AI features or no-code/low-code builders that adapt more easily to changes. Assign dedicated ownership for playbooks, conduct quarterly reviews, and build robust error handling, logging, and alerting into every workflow from the start.
3. Over-automation and loss of trust
Pushing too much automation too quickly, especially on high-risk actions without safeguards, can lead to false positives, unintended disruptions, or missed edge cases. When analysts lose confidence, they bypass the system entirely, defeating the purpose of SOAR.
Fix: Use a phased rollout, begin with attended or hybrid automation that requires human approval for critical decisions. Closely monitor results, refine based on real incidents, and gradually move to fully unattended automation only after proven reliability.
4. The integration depth trap
Many SOAR connectors provide read-only data access but lack true bidirectional response actions, such as isolating endpoints, revoking sessions, or updating firewall rules. This limits actual orchestration and forces manual steps during incidents.
Fix: During proof-of-concept testing, validate full response capabilities, not just data ingestion. Confirm API depth, rate limits, and performance under realistic load. Prioritize tools with deep, production-proven integrations for your specific security stack.
Addressing these risks early helps avoid common deployment failures and maximizes the return on your SOAR investment.
Ready to deploy SOAR the right way?
Explore ManageEngine Log360's unified SOAR capabilities. Schedule a personalized demo with our experts today.
Frequently asked questions
What are SOAR tools?
Security orchestration, automation, and response (SOAR) tools are platforms that help security teams coordinate, automate, and standardize incident response workflows across multiple security technologies. Acting as a centralized automation hub, SOAR tools connect disparate security tools, execute predefined playbooks, and orchestrate response actions, reducing manual effort and accelerating threat remediation.
What is the primary focus of SOAR tools?
The primary focus is to automate routine actions, orchestrate multi-step responses, and centralize security workflows. SOAR tools help teams enrich alerts, triage faster, and handle threats with consistency.
What are the key differences between SIEM and SOAR tools?
SIEM tools focus on detecting and analyzing security events through log collection, correlation, and analytics to identify incidents that require investigation. SOAR tools focus on orchestrating and automating incident response, managing the actions taken after threats are detected. Many modern security platforms combine SIEM and SOAR capabilities, enabling streamlined workflows from detection through investigation and automated response.
How does SOAR integrate with other security tools?
SOAR integrates through APIs and connectors. It links SIEM, EDR, IAM systems, firewalls, cloud services, ticketing platforms, and threat intelligence feeds. This allows automated enrichment and coordinated containment or remediation actions across the environment.
What are cloud-based SOAR solutions?
Cloud-based SOAR platforms run as SaaS services. They offer the same automation and orchestration capabilities as on-premises tools but provide faster deployment, automatic updates, and elastic scalability.
What are the key benefits of deploying a SOAR tool?
SOAR tools lower MTTR through automation, improve analyst productivity by removing repetitive tasks, and ensure consistent incident handling with standardized playbooks. They reduce human error, support scalable alert management, and provide clear, auditable response records for compliance.
What capabilities should enterprises look for in a SOAR tool?
Enterprises should look for broad integrations, easy playbook creation, strong case management, built-in enrichment from threat intelligence, flexible deployment models, prebuilt content, detailed reporting, and reliable vendor support.
Which SOAR tool delivers the fastest ROI?
SOAR tools with prebuilt playbooks, low-code workflow builders, and wide integration support deliver faster ROI. Unified SIEM-SOAR platforms typically reduce deployment time and show value faster by minimizing integration overhead and lowering operational costs.
- SOAR tools deployment models:
- The SOAR ecosystem: Building a high-velocity security fabric
- Critical 2026 SOAR tool selection questions for vendors
- Selecting the right SOAR tool: 2026 strategy guide
- Selecting the right SOAR tool: Key features
- SOAR tool deployment: Critical risks you can't afford to miss
- Frequently asked questions