Direct Inward Dialing: +1 408 916 9892
ADAudit Plus is real-time, web-based Windows Active Directory change reporting software that audits, tracks and reports on Windows (Active Directory, workstations logon/logoff, file servers and servers), NetApp filers and EMC servers to help meet the most-needed security, audit and compliance demands. Track authorized/unauthorized AD management changes, access of users, GPO, groups, computer and OU. Also, track every file and folder modifications, access and permissions changes with 200+ detailed event-specific reports and instant emails alerts. These reports can be exported into XLS, HTML, PDF and CSV formats to assist in interpretation and computer forensics.
You can configure these reports to be automatically generated and emailed to you at specified intervals. You can also export these reports to a format of your choice. Here is how you can track activities of privileged users using ADAudit Plus:
Login to ADAudit Plus → Go to the Reports tab → Under Account Management → Navigate to Administrative User Actions.
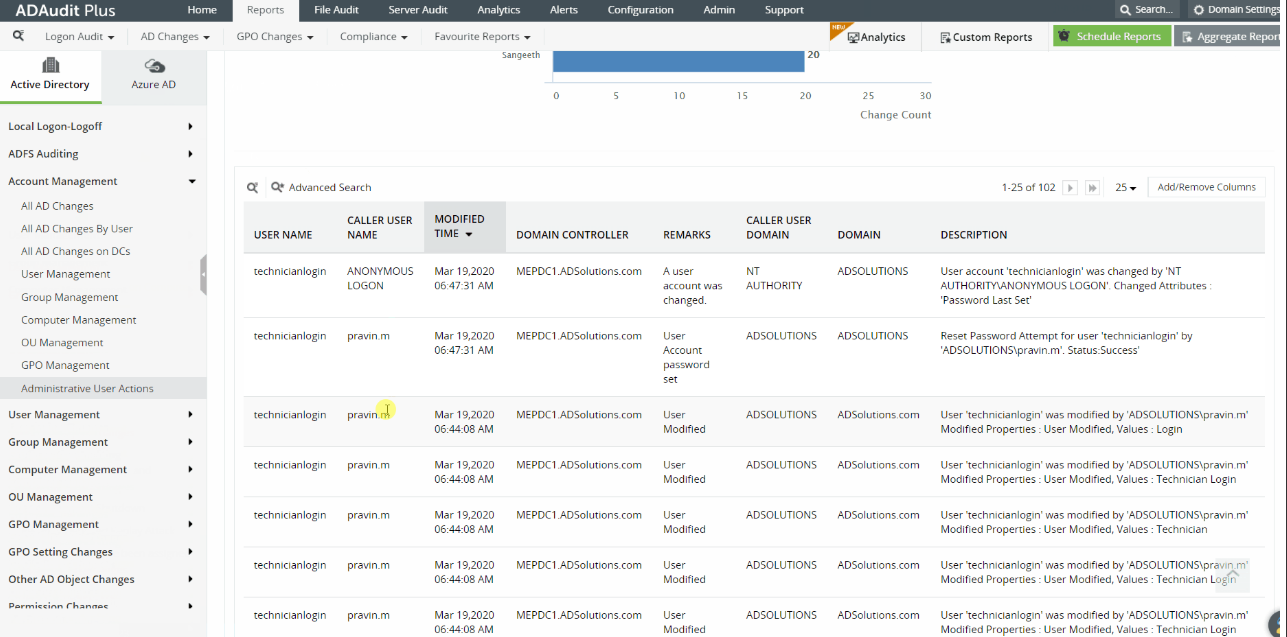
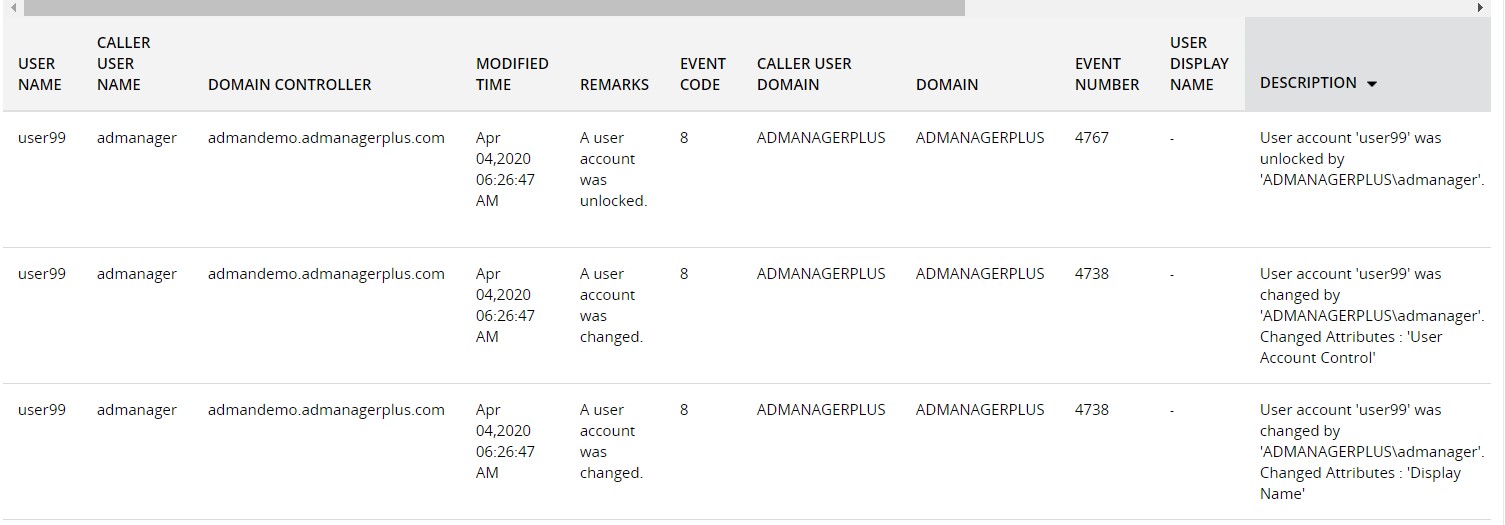
With this report, you can track the activities of your privileged users. This in turn will let you monitor any significant changes happening in your domain.
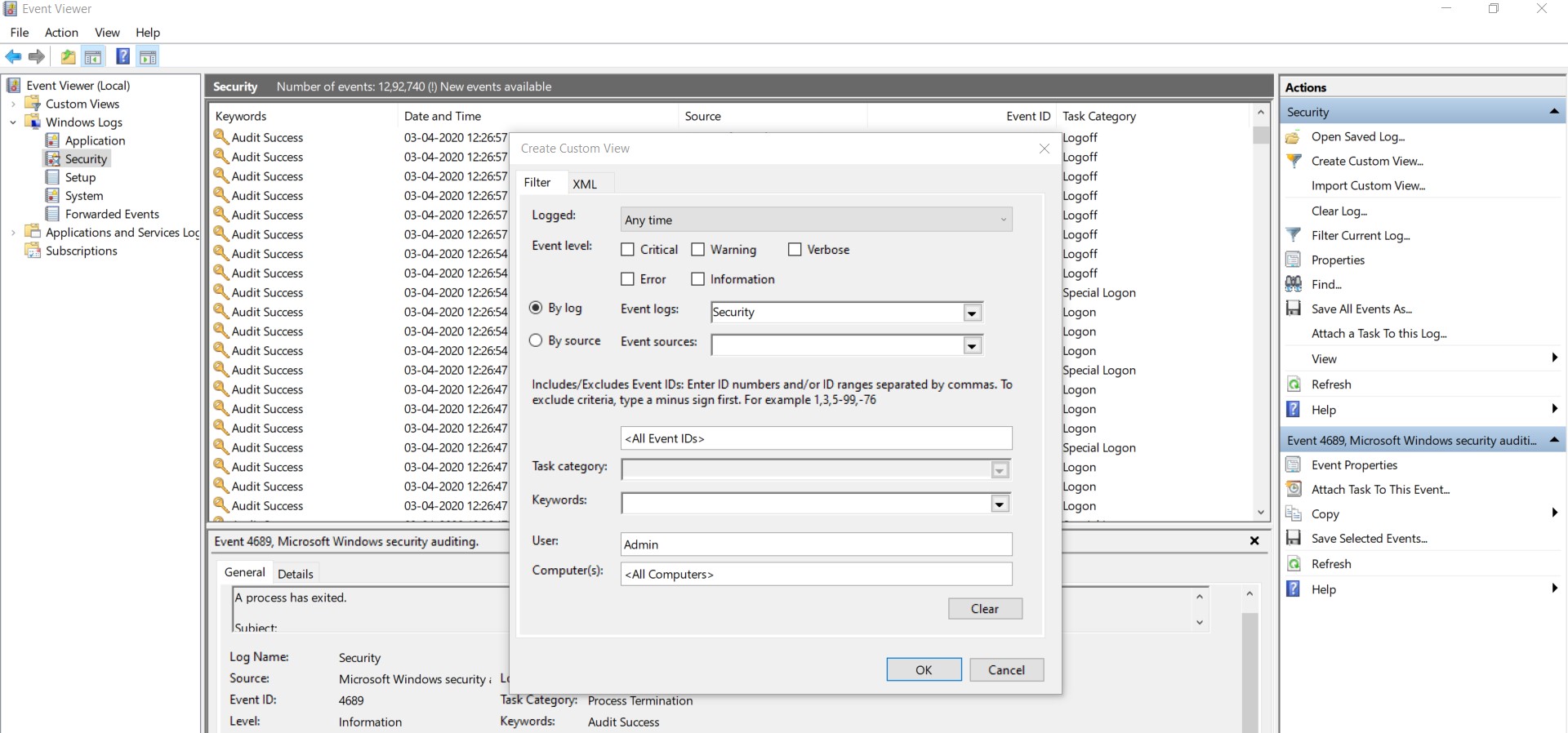
With native auditing, here is how you can track activities of privileged users:
You can list all privileged users by using Active Directory Users and Computers and Group Policy Management Console.
To discover other privileged user accounts you may also have to run customized scripts. For instance, every member of any administrative group is a privileged user.
Launch Server Manager in your Windows Server instance.
Under Manage, select Group Policy Management and launch the Group Policy Management console.
Navigate to Forest → Domain → Your domain → Domain Controllers.
Create a new GPO and link it to the domain containing the user object, or edit any existing GPO that is linked to the domain to open the Group Policy Management Editor.
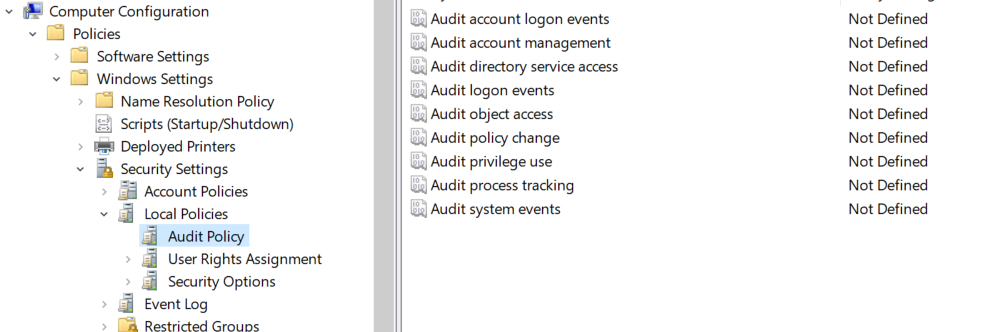
Navigate to omputer Configuration → Windows Settings → Security Settings → Local Policies → Audit Policy.
The Audit Policy lists all of its sub-policies in the right panel, as shown in Figure 1.
Select the policies you want to enable for both its successful and failure events. In the event of multiple failures, the organisation can initiate security protocol, if necessary.
Click Apply and OK to close Properties window.
Launch Server Manager in your Windows Server instance.
Under Manage, select Group Policy Management and launch the Group Policy Management console.
Navigate to Computer Configuration → Policies → Windows Settings → Security Settings → Advanced Audit Policy Configuration. Select Audit Policies.
Force audit policy subcategory settings to override audit policy category settings in Group Policy to make sure that basic auditing is disabled.
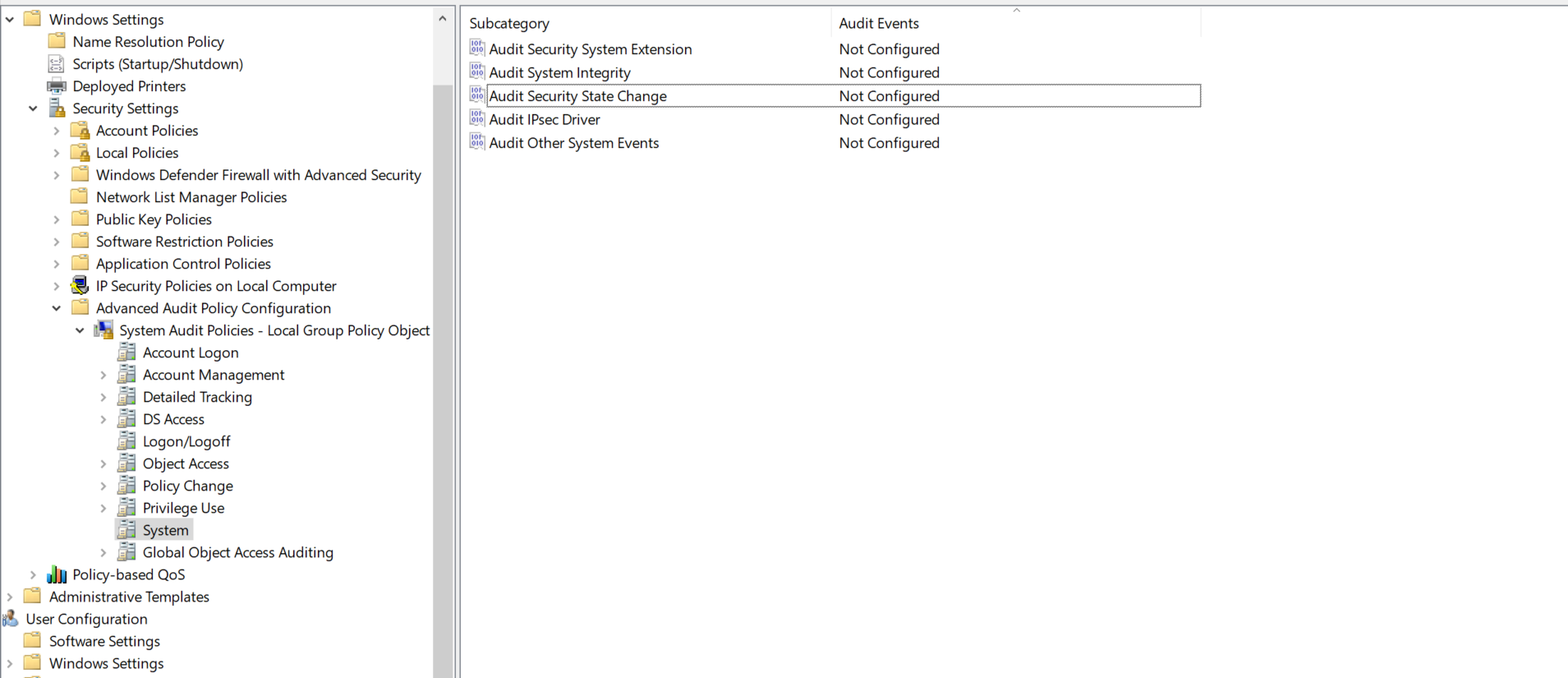
Decide on the policies you want to enable and select both Success and Failure options.
Native auditing becoming a little too much?
Simplify Active Directory auditing and reporting with ADAudit Plus.
Get Your Free Trial Fully functional 30-day trial