The first step in tracking who deleted a file from your file servers is to enable auditing. Auditing allows you to tell Windows the specific set of changes you want to monitor so that only these events are recorded in the security log.
To enable auditing for object access-related events, follow the steps below:
A. Define the audit policies.
- 1 Run gpmc.msc (Group Policy Management Console).
- 2 Create a new GPO.
- 3 Click Edit and navigate to Computer Configuration > Policies > Windows Settings > Security Settings > Advanced Audit Policy Configuration > Audit Policies.Under Audit Policies, you'll find specific settings for Object Access.
Object Access:
- Audit File System > Define > Success and Failures.
- Audit Handle Manipulation > Define > Success and Failures.
- 4 To link the new GPO to your domain, right-click ‹your domain› ,Select Link an Existing GPO and choose the GPO that you created.
Note:By default, Windows updates Group Policy every 90 minutes; if you want the changes to be reflected immediately, you can force a background update of all Group Policy settings by executing the following command in the Windows Command Prompt: gpupdate /force
B. Define the system access control list (SACL).
- 1 Go to the file share, right-click and select Properties. Under the Security tab, navigate to Advanced > Auditing, and click Add.
- 2 This brings up another window where you'll make the following selections—Principal: Everyone; Type: All; Applies to: This folder, subfolders and files.
- 3 Then select Advanced Permissions: Delete subfolders and files, and Delete.
To view the events, open Event Viewer and navigate to Windows Logs › Security. Here you'll find details of all events that you've enabled auditing for. You can define the size of the security log here, and you can choose to overwrite older events so that recent events are recorded when the log is full.

Understanding event IDs associated with logon and logoff activity
-
Event ID 4663 — An Attempt Was Made To Access An Object
Event ID 4663 shows that a specific operation was performed on an object. The object could be a file system, kernel, registry object, or file system object on removable media or a device. Learn more
-
Event ID 4660 — An Object Was Deleted
Event ID 4660 is generated when an object is deleted. The object could be a file system, kernel, or registry object. This event does not contain the name of the deleted object. Learn more
Common identifiers required to tie these events together are matching Process IDs and Handle IDs on both event ID 4663 and 4660. This will help identify the object that was deleted from details in event 4663.
Limitations of native auditing tools
- There's no central repository for all change audit logs. File and folder activity logs are only recorded in the security log of individual computers (workstations or Windows servers).
- There's a size limit for Windows security logs, which can be an major issue for security.
- Windows doesn't offer event reporting, and with poor search filters, this makes root cause analysis a challenge.
- The lack of a robust real-time incident notification and threat response system is a severe limitation.
An easier way to detect who deleted a file from your file servers
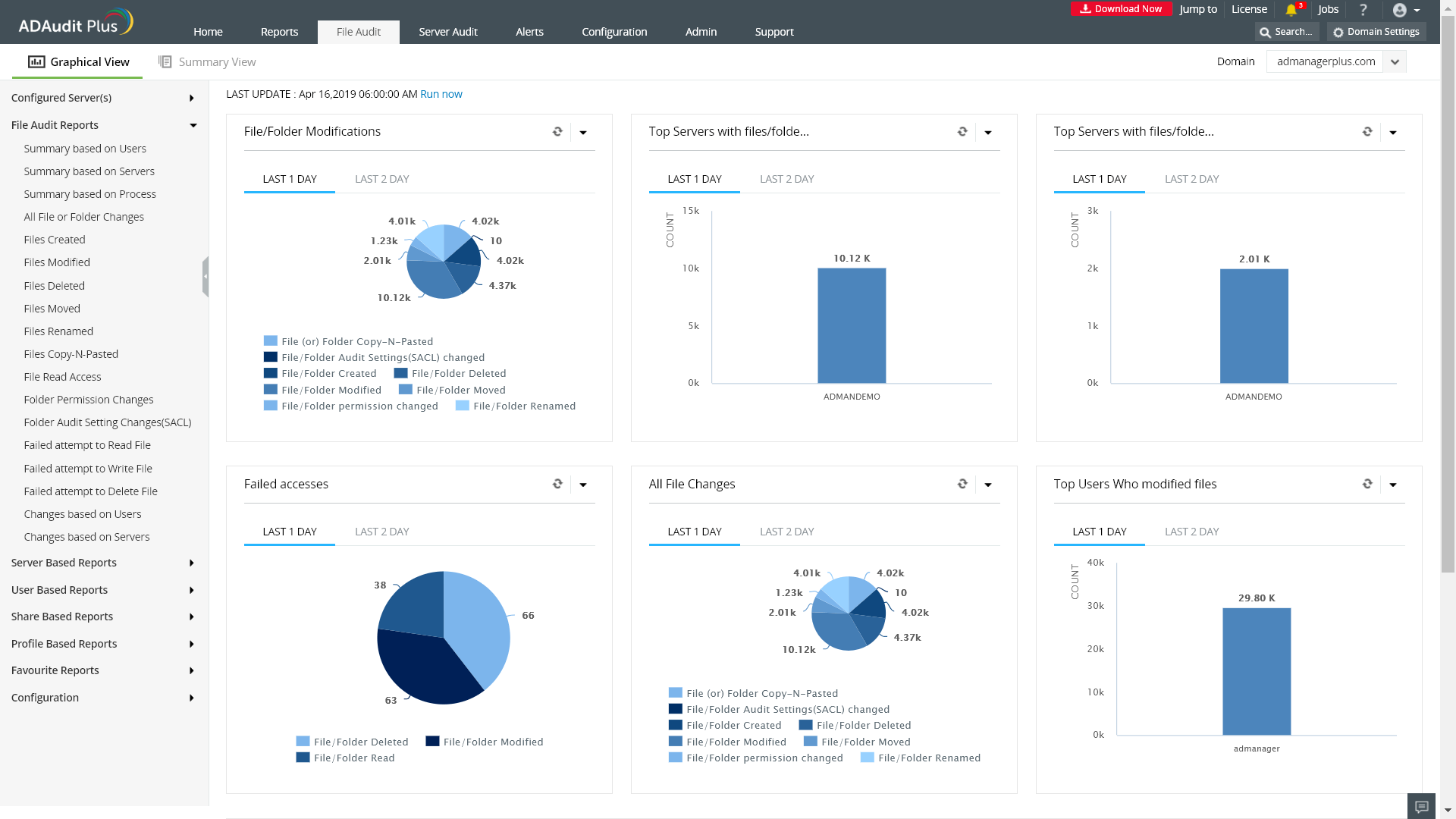
A tool like ADAudit Plus audits Windows file servers, failover clusters, NetApp, and EMC storage devices to document changes to files and folders. It also helps monitor system configurations, program files, and folder changes to ensure file integrity across your network.
With ADAudit Plus, you can instantly view reports on:
- Files read.
- File write actions.
- Files modified.
- Files created, deleted, moved, renamed, and copied and pasted.
- Permission changes.
- Failed access attempts, and more.
This information is provided on an easy-to-understand web interface that displays statistical information through charts, graphs, and a list view of canned and customized reports.