- Free Edition
- Quick Links
- Active Directory Auditing
- Active Directory auditor
- Active Directory monitoring
- Account lockout analyzer
- Login monitoring software
- Active Directory change notifier
- User logon audit reports
- AD logon logoff tracker
- User logon failure auditing
- Login history tracking tool
- AD change auditor
- Insider threat detection software
- Permissions change auditing
- Entra ID reporting
- Privileged user monitoring
- User behavior analytics tool
- Active Directory security monitoring
- Group Policy auditing tool
- GPO change auditor
- Entra ID auditing
- Audit user account management
- OU change auditor
- Audit group membership changes
- Active Directory auditing and reporting tool
- GPO reporting tool
- Remote desktop monitoring software
- PowerShell logging and auditing
- Azure password protection auditing
- Azure sign-in risk detection
- File Server Auditing
- Windows Server Auditing
- Employee Tracking
- Workstations Auditing
- Compliance Auditing
- Other features
- SIEM Integration
- Windows DNS - Schema Auditing
- Windows security event log monitoring
- SIEM audit solution
- Schedule Active Directory change reports
- Reports from Archived Data
- Aggregated summary reports
- AD new/old attribute changes
- Audit trail
- Audit Active Directory LAPS
- Scheduled Reports & Alerts
- Account lockout examiner
- Industry
- Documents
- Success Stories
- Related Products
- Log360 (On-Premise | Cloud) Comprehensive SIEM and UEBA
- ADManager Plus Active Directory Management & Reporting
- EventLog Analyzer Real-time Log Analysis & Reporting
- ADSelfService Plus Identity security with MFA, SSO, and SSPR
- DataSecurity Plus File server auditing & data discovery
- Exchange Reporter Plus Exchange Server Auditing & Reporting
- M365 Manager Plus Microsoft 365 Management & Reporting Tool
- RecoveryManager Plus Enterprise backup and recovery tool
- SharePoint Manager Plus SharePoint Reporting and Auditing
- AD360 Integrated Identity & Access Management
- AD Free Tools Active Directory FREE Tools
Windows Event ID 4624 – Successful logon
Introduction
Event ID 4624 (viewed in Windows Event Viewer) documents every successful attempt at logging on to a local computer. This event is generated on the computer that was accessed, in other words, where the logon session was created. A related event, Event ID 4625 documents failed logon attempts.
Event 4624 applies to the following operating systems: Windows Server 2008 R2 and Windows 7, Windows Server 2012 R2 and Windows 8.1, and Windows Server 2016 and Windows 10. Corresponding events in Windows Server 2003 and earlier included both 528 and 540 for successful logons.
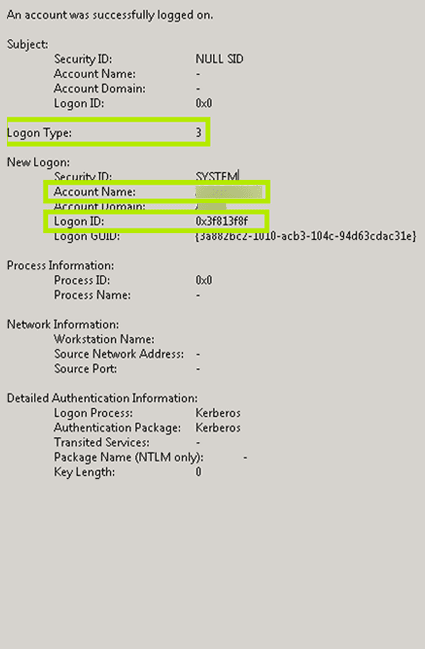
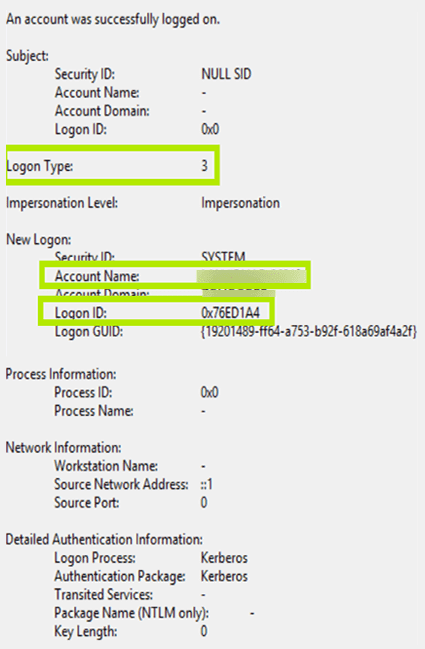
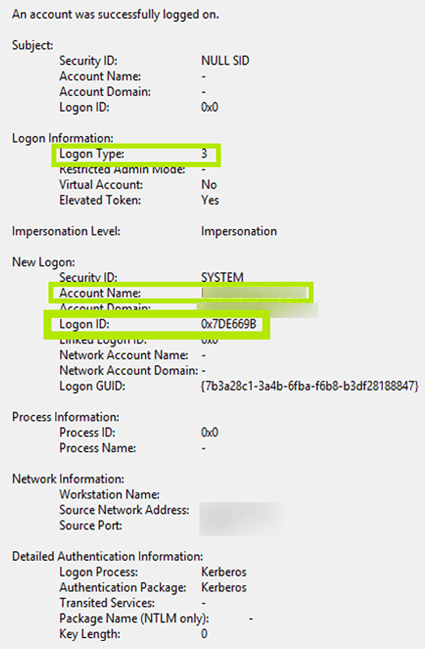
Event ID 4624 looks a little different across Windows Server 2008, 2012, and 2016. Highlighted in the screenshots below are the important fields across each of these versions.
Event 4624 (Windows 2008)
Event 4624 (Windows 2012)
Event 4624 (Windows 2016)
Description of Event Fields
The important information that can be derived from Event 4624 includes:
- Logon Type: This field reveals the kind of logon that occurred. In other words, it points out how the user logged on. There are a total of nine different types of logons, the most common logon types are: logon type 2 (interactive) and logon type 3 (network). Any logon type other than 5 (which denotes a service startup) is a red flag.
- New Logon: This section reveals the Account Name of the user for whom the new logon was created and the Logon ID, a hexadecimal value that helps correlate this event with other events.
Other information that can be obtained from Event 4624:
Logon Type Description Type 2 Interactive logon
Occurs when a user logs on using a computer's local keyboard and screen.
Type 3 Network logon
Occurs when a user accesses remote file shares or printers. Also, most logons to Internet Information Services (IIS) are classified as network logons (except for IIS logons which are logged as logon type 8).
Type 4 Batch logon
Occurs during scheduled tasks, i.e. when the Windows Scheduler service starts a scheduled task.
Type 5 Service logon
Occurs when services and service accounts log on to start a service.
Type 7 Unlock logon
Occurs when a user unlocks their Windows machine.
Type 8 NetworkClearText logon
Occurs when a user logs on over a network and the password is sent in clear text. Most often indicates a logon to IIS using "basic authentication."
Type 9 NewCredentials logon
Occurs when a user runs an application using the RunAs command and specifies the /netonly switch.
Type 10 RemoteInteractive logon
Occurs when a user logs on to their computer using RDP-based applications like Terminal Services, Remote Desktop, or Remote Assistance.
Type 11 CachedInteractive logon
Occurs when a user logs on to their computer using network credentials that were stored locally on the computer (i.e. the domain controller was not contacted to verify the credentials).
- The Subject section reveals the account on the local system (not the user) that requested the logon.
- The Impersonation Level section reveals the extent to which a process in the logon session can impersonate a client. Impersonation Levels determine the operations a server can perform in the client's context.
- The Process Information section reveals details surrounding the process that attempted the logon.
- The Network Information section reveals where the user was when they logged on. If the logon was initiated from the same computer, this information will either be blank or reflect the local computer's workstation name and source network address.
- The Authentication Information reveals information about the authentication package used for logon.
Reasons for monitoring successful logons
Security
To prevent privilege abuse, organizations need to be vigilant about what actions privileged users are performing, starting with logons.
To detect abnormal and potentially malicious activity, like a logon from an inactive or restricted account, users logging on outside of normal working hours, concurrent logons to many resources, etc.
Operational
To get information on user activity like user attendance, peak logon times, etc.
Compliance
To comply with regulatory mandates precise information surrounding successful logons is necessary.
The need for a third-party tool
In a typical IT environment, the number of events with ID 4624 (successful logons) can run into the thousands per day. However, all these successful logon events are not important; even the important events are useless in isolation, without any connection established with other events.
For example, while Event 4624 is generated when an account logs on and Event 4647 is generated when an account logs off, neither of these events reveal the duration of the logon session. To find the logon duration, you have to correlate Event 4624 with the corresponding Event 4647 using the Logon ID.
Thus, event analysis and correlation needs to be done. Native tools and PowerShell scripts demand expertise and time when employed to this end, and so a third-party tool is truly indispensable.
Applying machine learning, ADAudit Plus creates a baseline of normal activities specific to each user and only notifies security personnel when there is a deviation from this norm.
For example, a user who consistently accesses a critical server outside of business hours wouldn't trigger a false positive alert because that behavior is typical for that user. On the other hand, ADAudit Plus would instantly alert security teams when that same user accesses that server during a time they've never accessed it before, even though the access falls within business hours.

