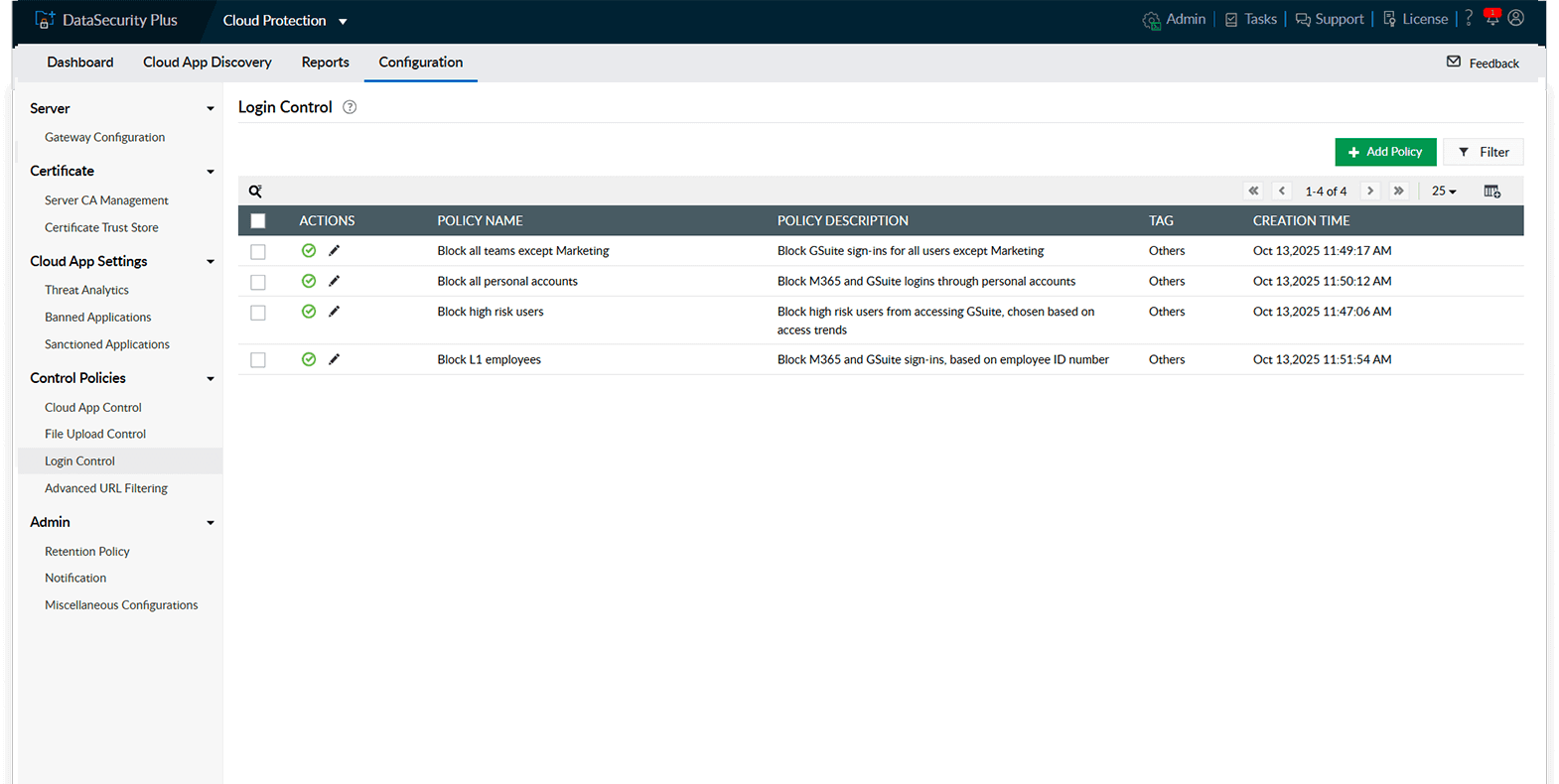
Strike the right balance between security and productivity by blocking risky logins without disrupting legitimate cloud app usage.
Restrict cloud app access to official accounts only and block personal account usage on the organizational network to reduce risk of data leakage.
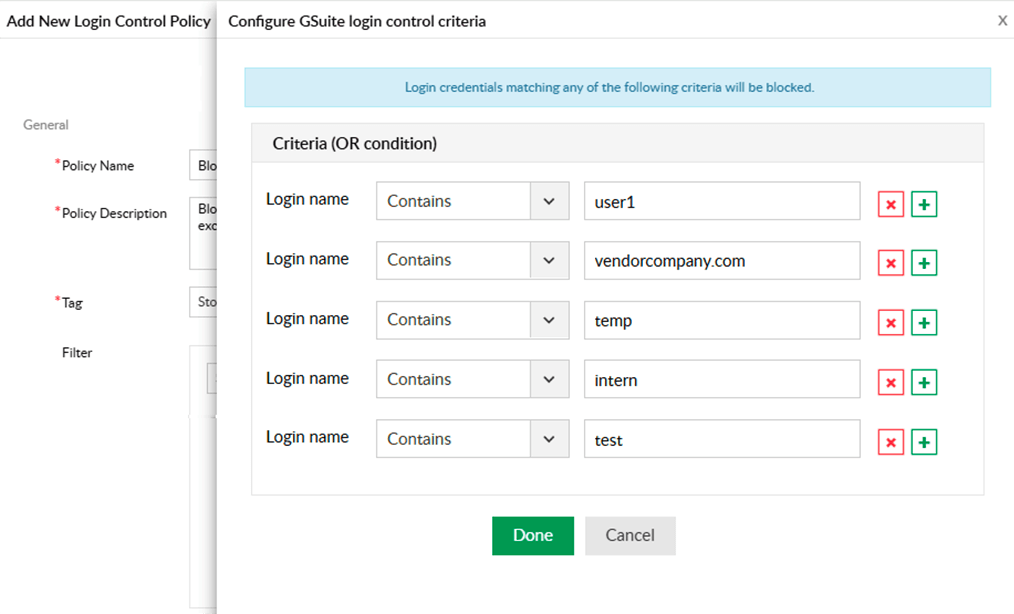
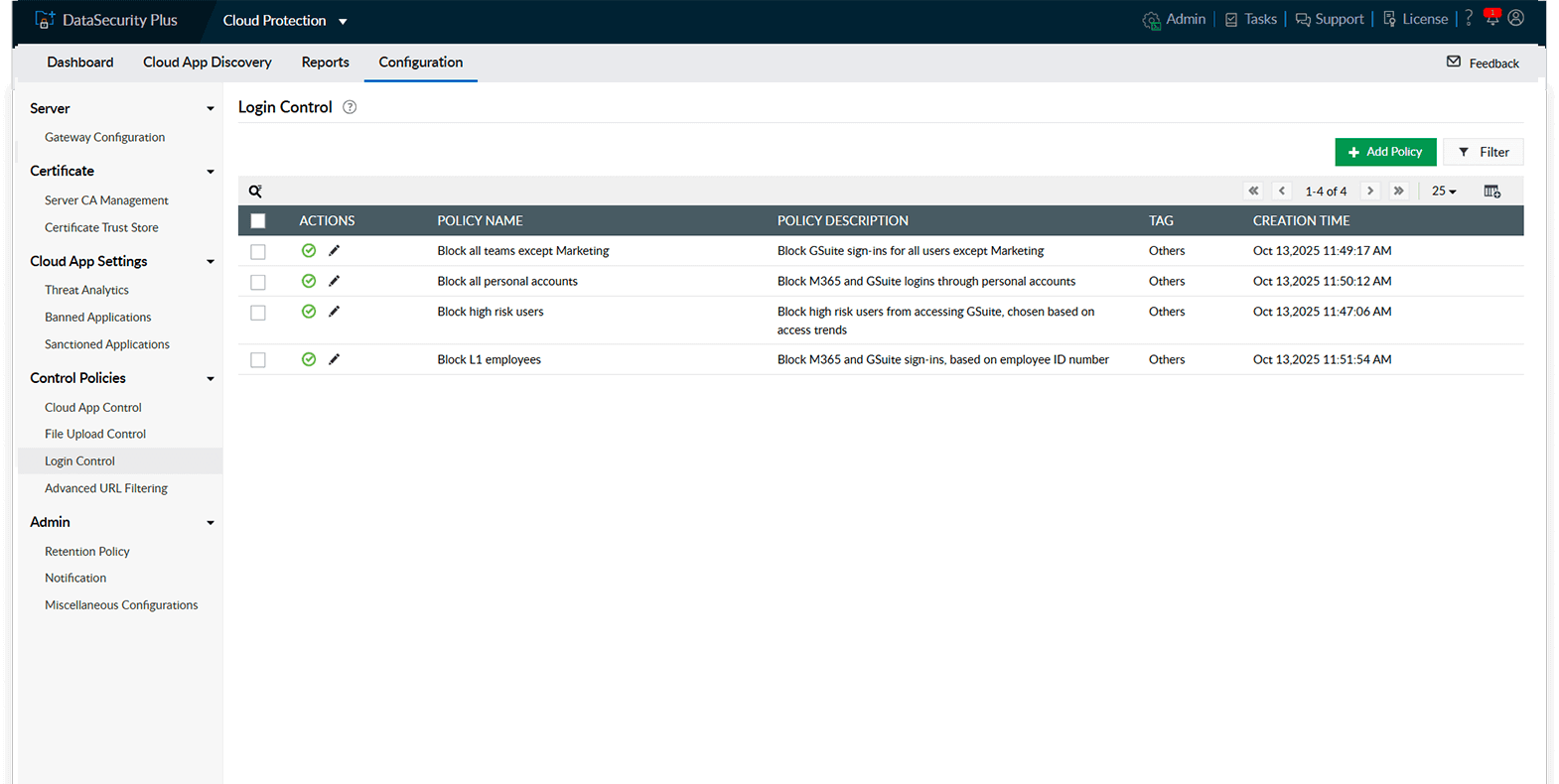
Use dynamic login control rules based on role, department, hierarchy, and other signals to control access granularly.
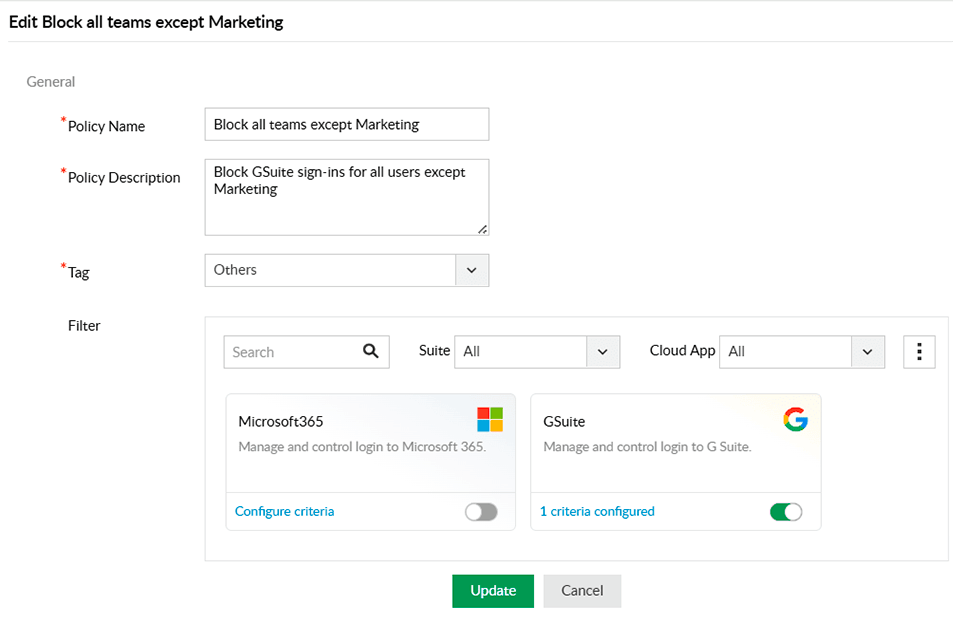
Only allow teams with clear business needs to sign in to Microsoft Office 365, Google Workspace, etc. while blocking other teams.
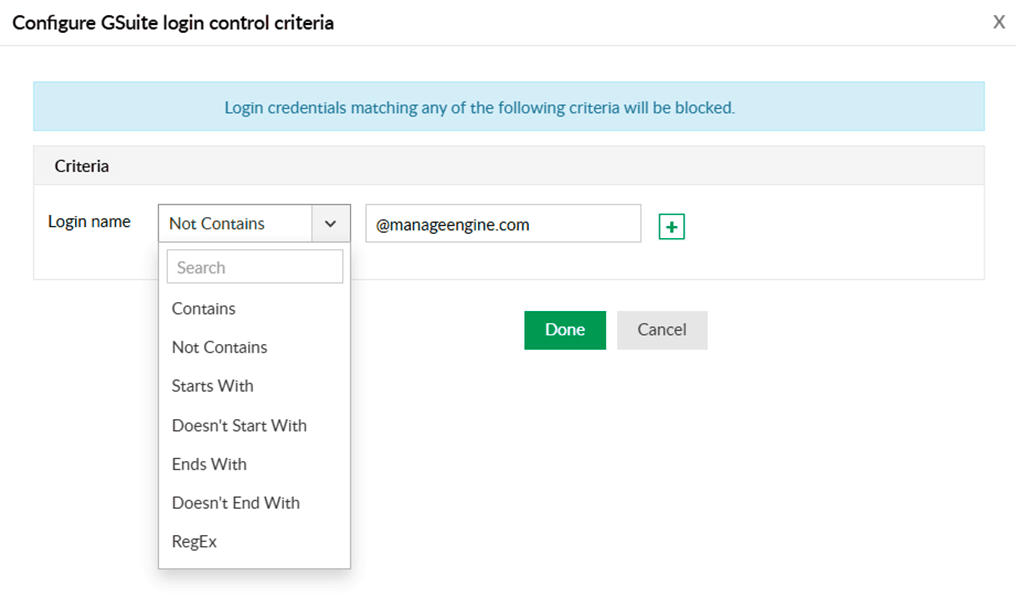
Allow logins to Google Workspace only through corporate accounts and block any attempt to access them using personal IDs to prevent data leaks and misuse.
Control access to key cloud suites like Microsoft 365 and Google Workspace for users flagged due to past violations, suspicious behavior, or elevated data access risk.
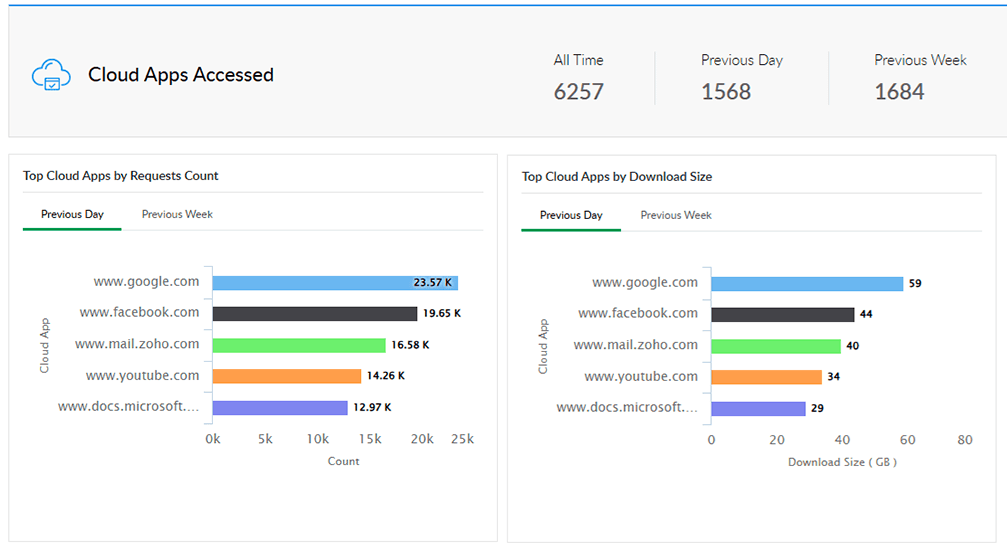
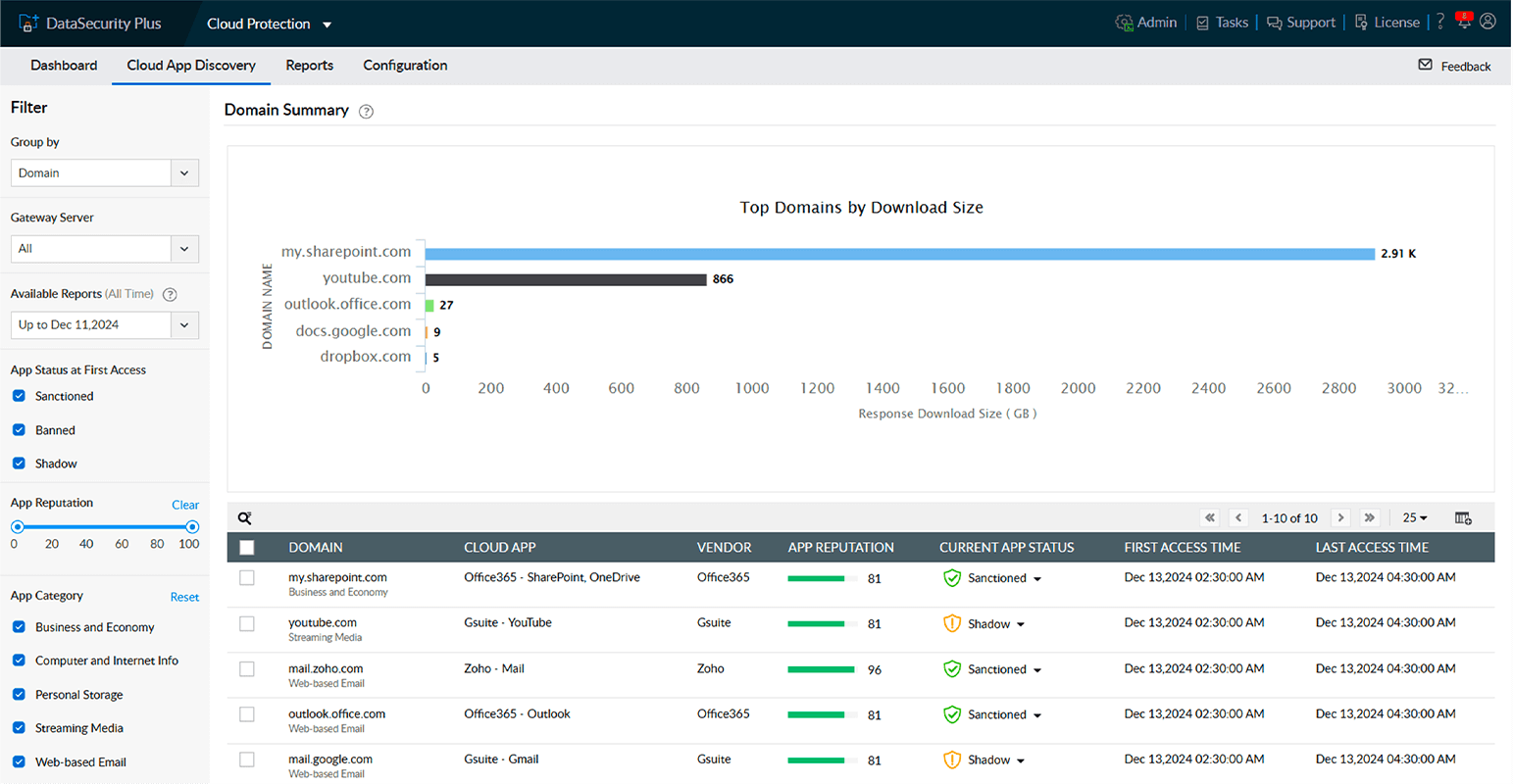
Track which cloud apps are being accessed the most, analyze usage patterns, and spot risky activity before it becomes a breach.
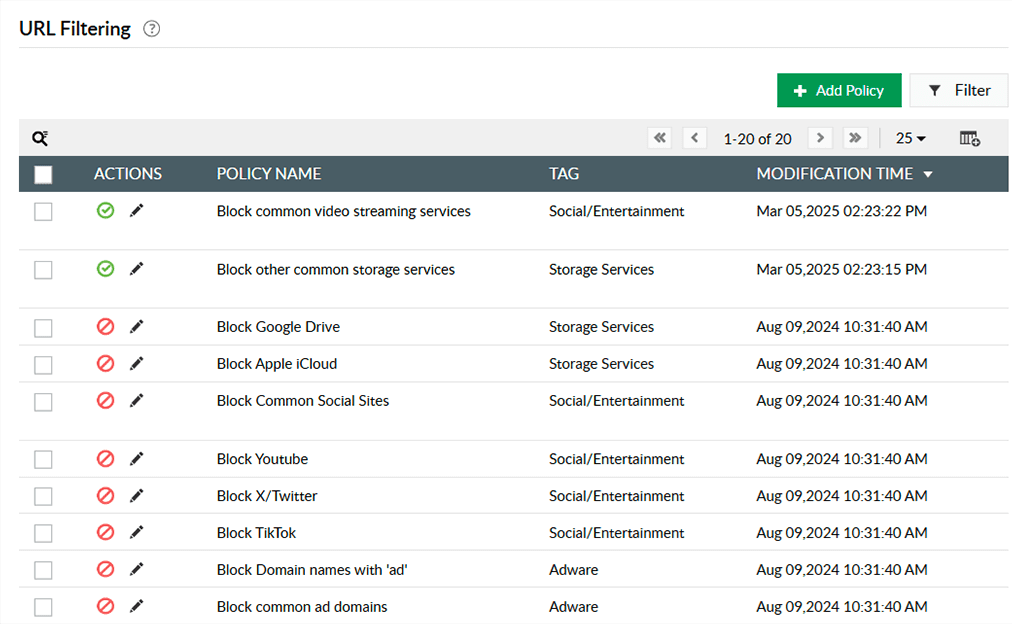
Create granular access control policies to block unwarranted access attempts—whether they are unauthorized, malicious, or unproductive.
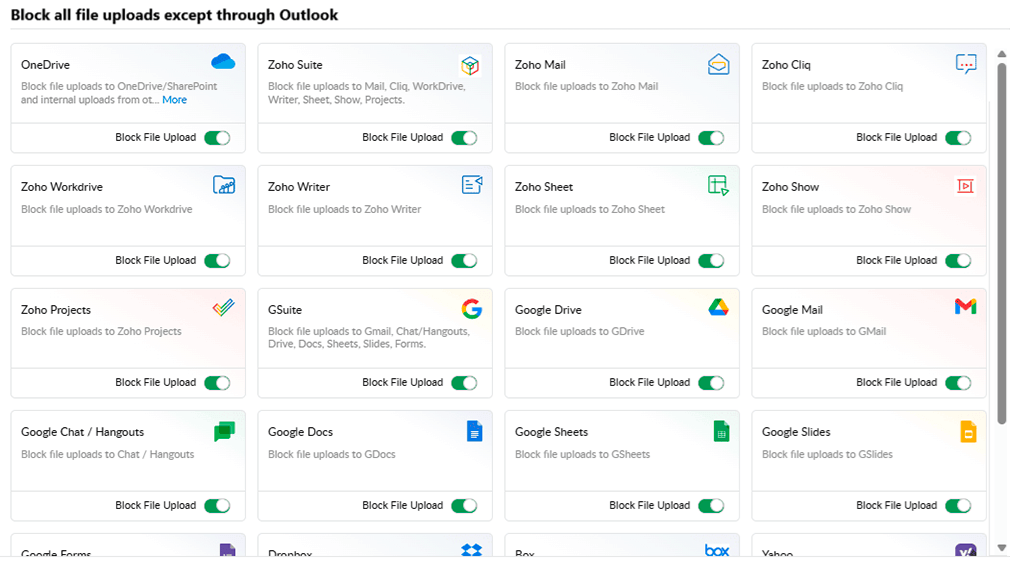
Apply strict data control policies to prevent file uploads and downloads to unauthorized cloud applications.
Secure cloud suite logins, know exactly who accessed what and when, analyze trends, and implement control measures to reduce security risks.
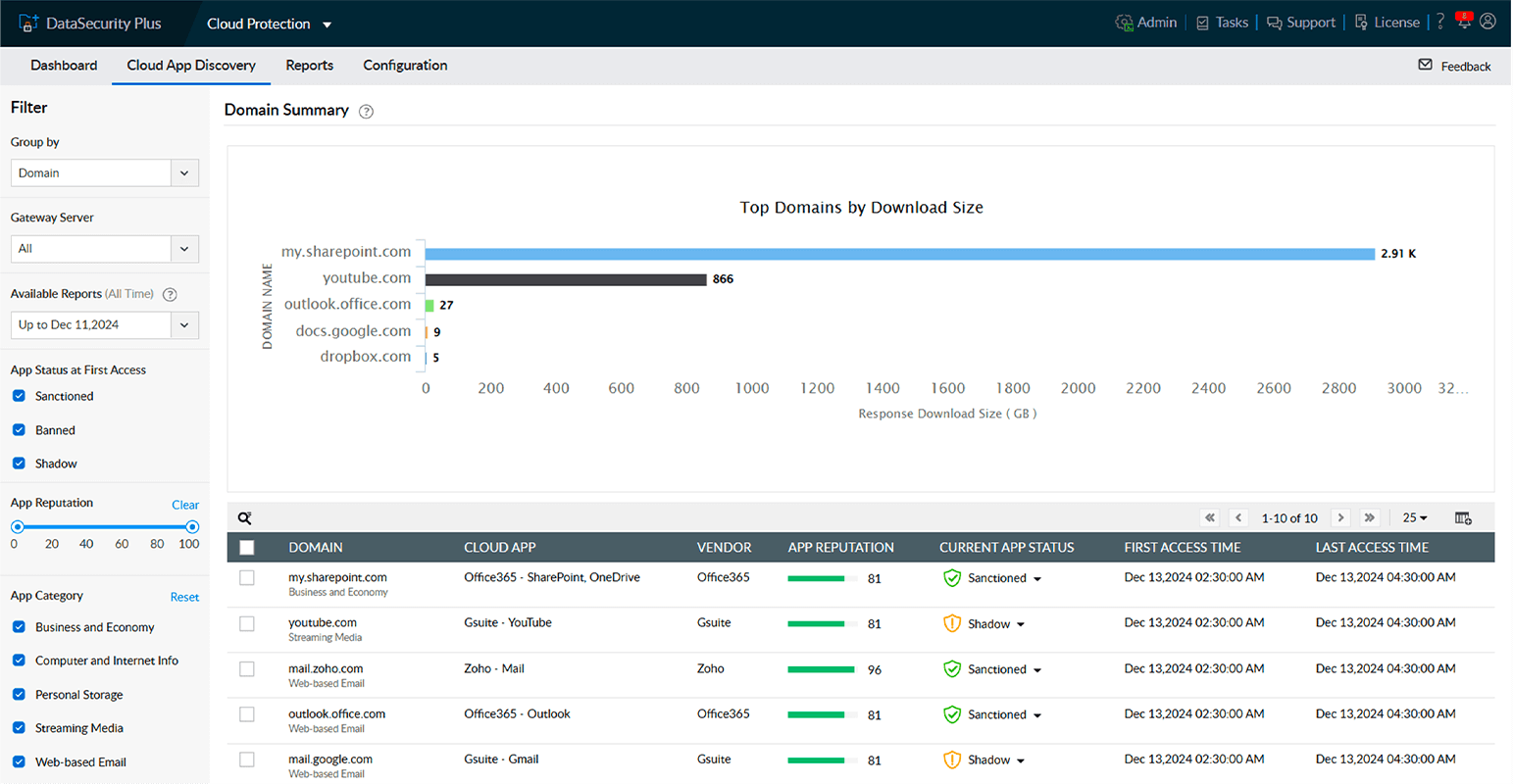
View top-accessed domains, app reputation, app status, and app usage times from a unified dashboard.
Tailor login control policies for different users, departments, and risk levels to align with your organization's acceptable usage policy.
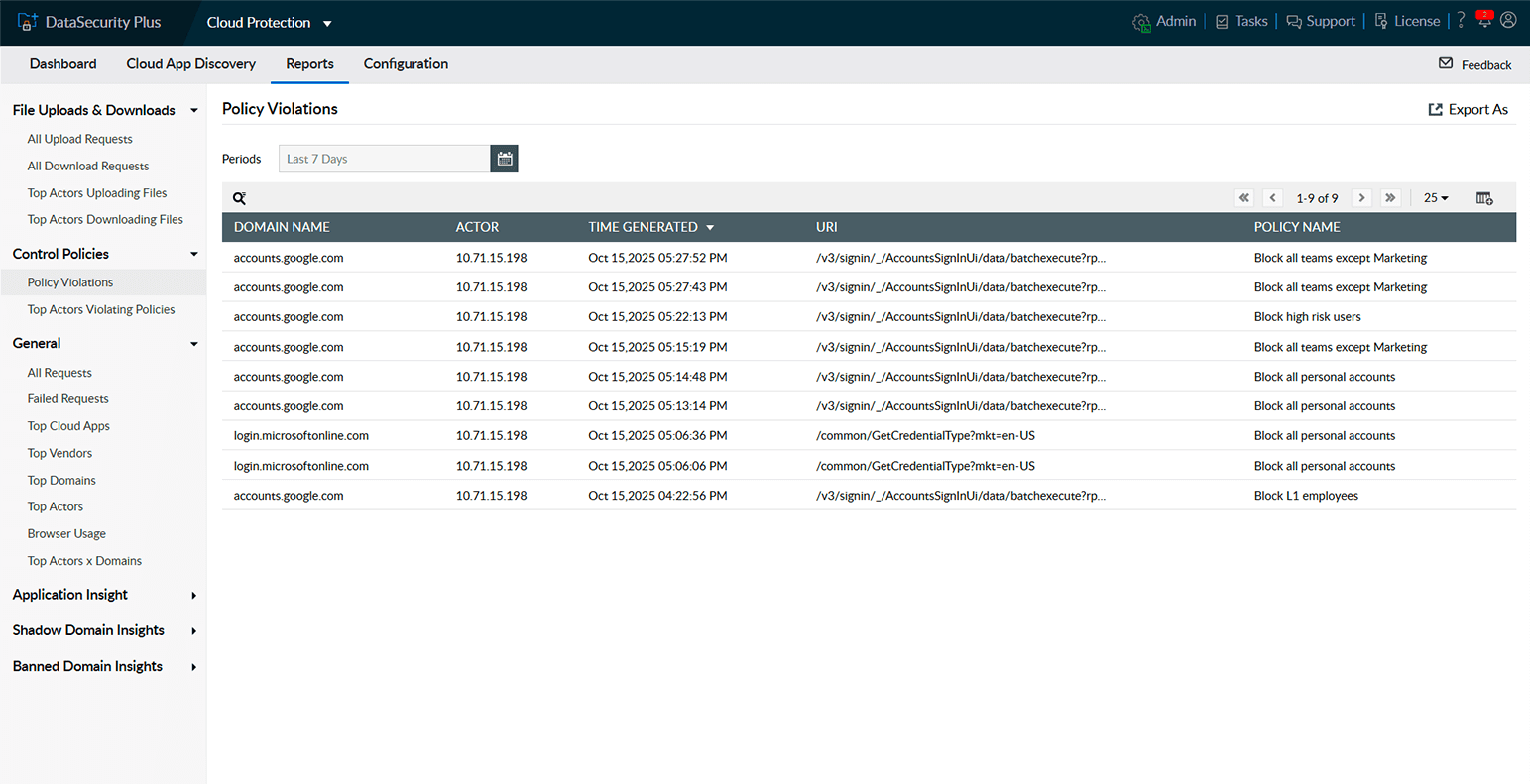
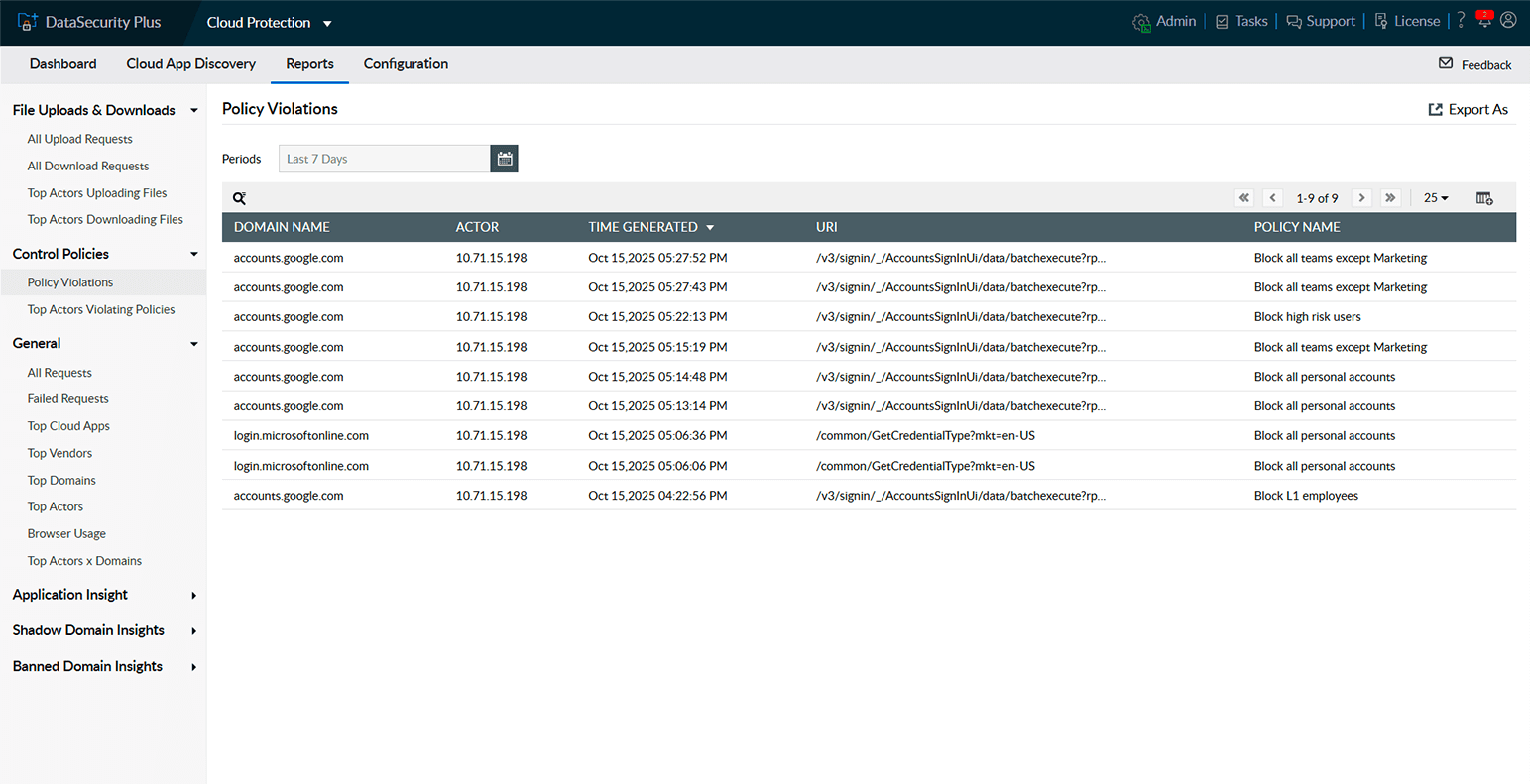
Demonstrate access governance and policy enforcement with in-depth reports, covering different aspects of cloud data security.
Track all policy violations, including who tried to log in, upload, or download files from unauthorized domains ensuring accountability.
Monitor and restrict file uploads to unauthorized external cloud applications and websites.
Stop data leakage through email by blocking outgoing emails containing sensitive file attachments.
Analyze user access to detect unusual patterns and stop insider risks before they escalate into breaches.
Track file uploads and downloads to monitor data movement and take action on unauthorized transfers instantly.