The biggest threat to an organization's security is not from outsiders, but from trusted insiders, primarily employees. Disgruntled employees who leave the organization might steal confidential business data either to take revenge on the organization, or to sell it in the black market for financial gain. There are several ways a malicious insider can sneak data out of the corporate network. But the most common ones are:
- External devices: The growing popularity of Bring Your Own Device (BYOD) has led to a sharp increase in data theft via personal devices. A survey conducted by Crowd Research Partners found that one in five companies experience a data breach due to BYOD policies.
- Email: Business-critical files are leaked outside the organization as email attachments.
ManageEngine's DataSecurity Plus functions as data leak prevention software that helps prevent employees from stealing data via a USB device or email.
Steps to prevent data theft via USB devices:
DataSecurity Plus prevents data theft by implementing preventive policies that can block unwarranted data transfers. This copy protection software helps identify and block critical files from being copied to USB devices. It also helps educate users about the company's policies when they try to copy a file, using system prompts.
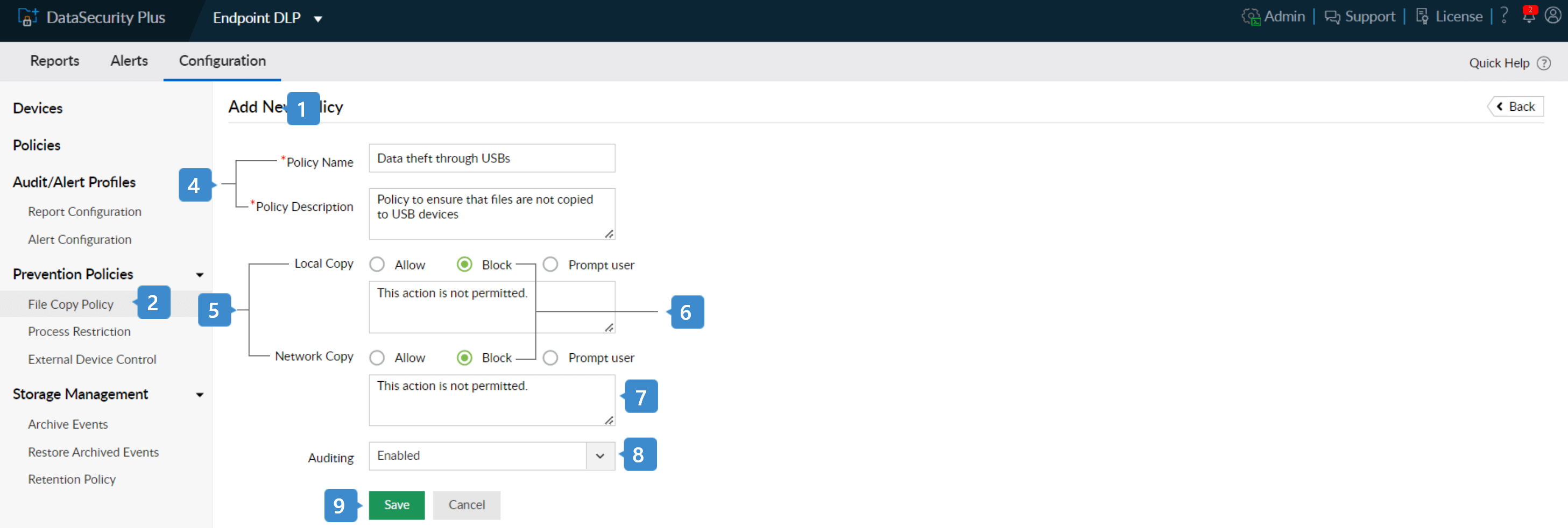
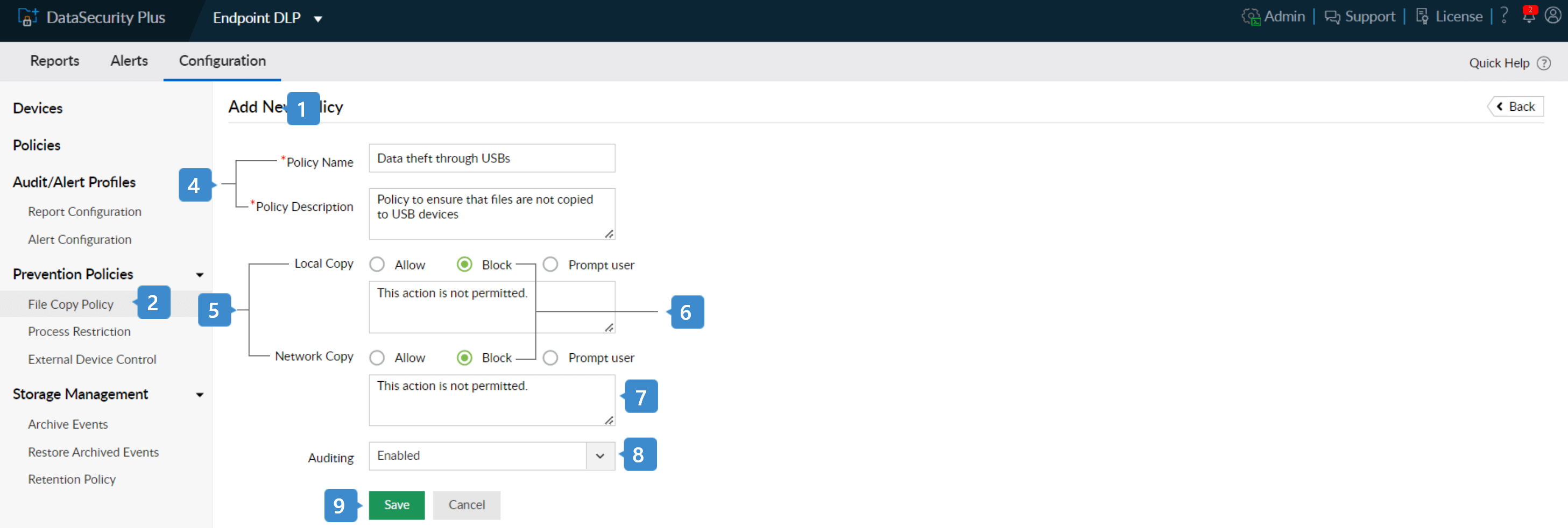
- Select Endpoint DLP from the application drop-down and go to Configuration.
- Choose File Copy Policy from the Prevention Policies drop-down menu.
- Click the + Create File Copy policy in the top-right corner.
- In the Add New Policy page that opens, provide a suitable policy name and brief description.
- Choose the type of response suitable for Local Copy and Network copy files.
Note:
- Local Copy: File copy actions that take place on the local system or any external storage device connected to it.
- Network Copy: Files copy actions that take place within the network.
- Choose the Block response to prevent all files from being copied to USB devices.
- Enter a custom message to be displayed to the user, in the textbox shown below.
- By default, Enabled option will be chosen from the Auditing drop-down to audit all the file copy events, using the policy.
- Click Save to create the prevention policy.
Note: Go to Policies in the left pane, and add the newly created file copy prevention profile to the existing Data Leak Prevention policy.
Steps to apply prevention policy to all workstations:
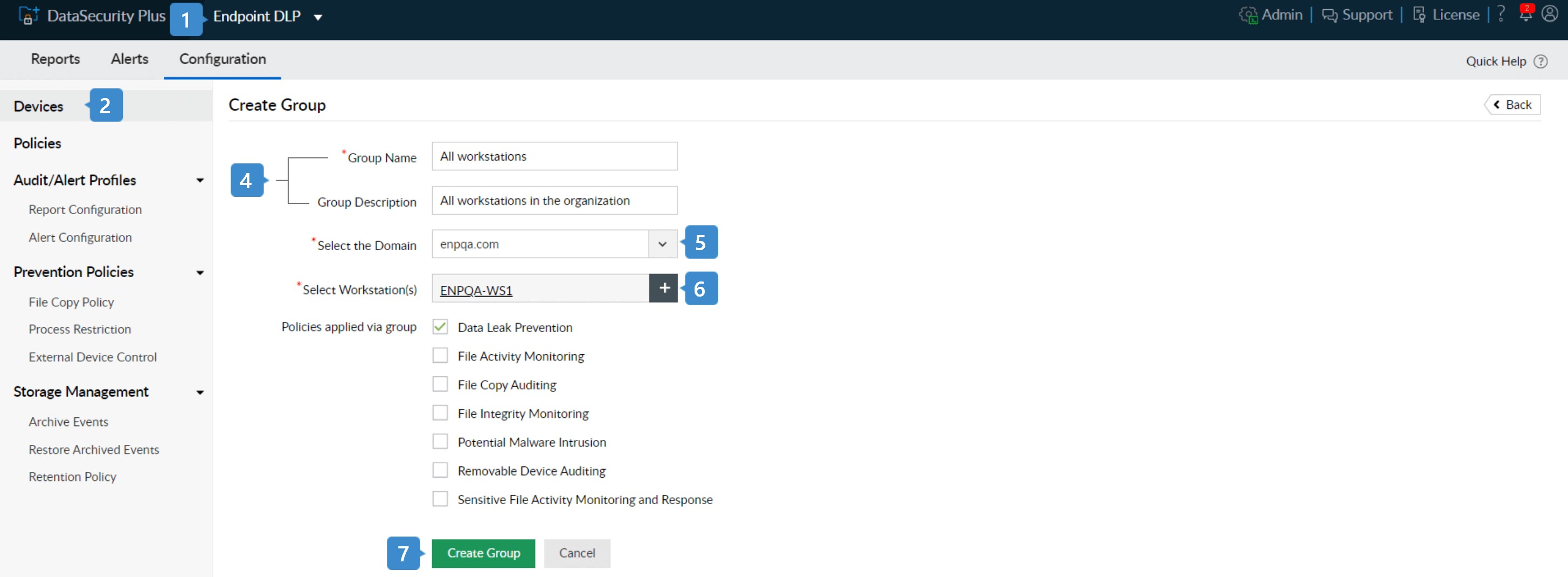
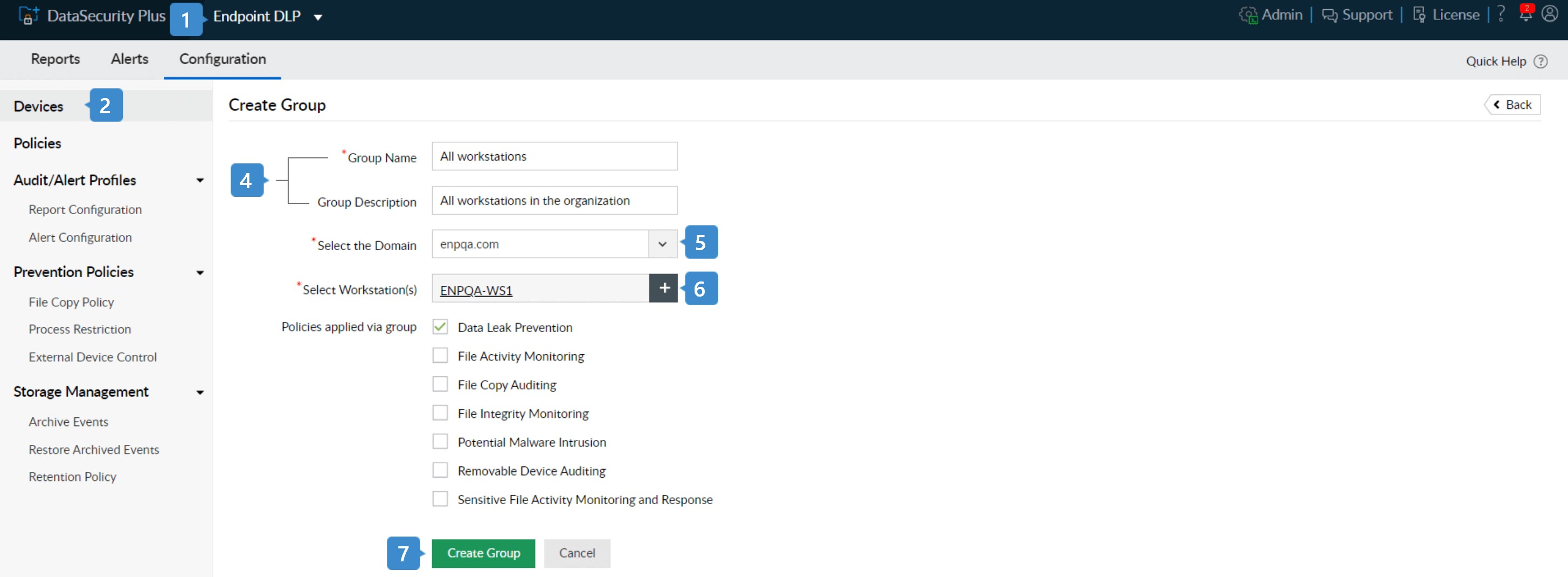
- Select Endpoint DLP from the application drop-down.
- Navigate to Configuration > Devices to open the Configured Workstation(s) page.
Note: To add new workstations, click on the + Add Workstations button and follow the steps in this
page.
- Select the Configured Groups tab and click the + Create Group button located at the top-right corner.
- Provide a suitable Group Name and Group Description.
- Select the appropriate domain from the drop-down.
- Click the + in the Select workstation(s) field, and select all the workstations.
- Now, select Data Leak Prevention under Policies applied via group and click Save.
The file copy prevention policy is now applied to all the workstations in the group. This ensures that no files can be copied to USB sticks, eliminating the possibility of data theft via external storage devices.
DataSecurity Plus also audits all the file copy actions by employees, which gives the organization's IT security team, insights about its users who might be carrying out excessive or suspicious data transfer activities.
Steps to prevent data theft via email:
In organizations where the use of external devices is restricted, the next most common way to steal data is via email. Users can send sensitive data as email attachments to themselves, or to an accomplice outside the organization.
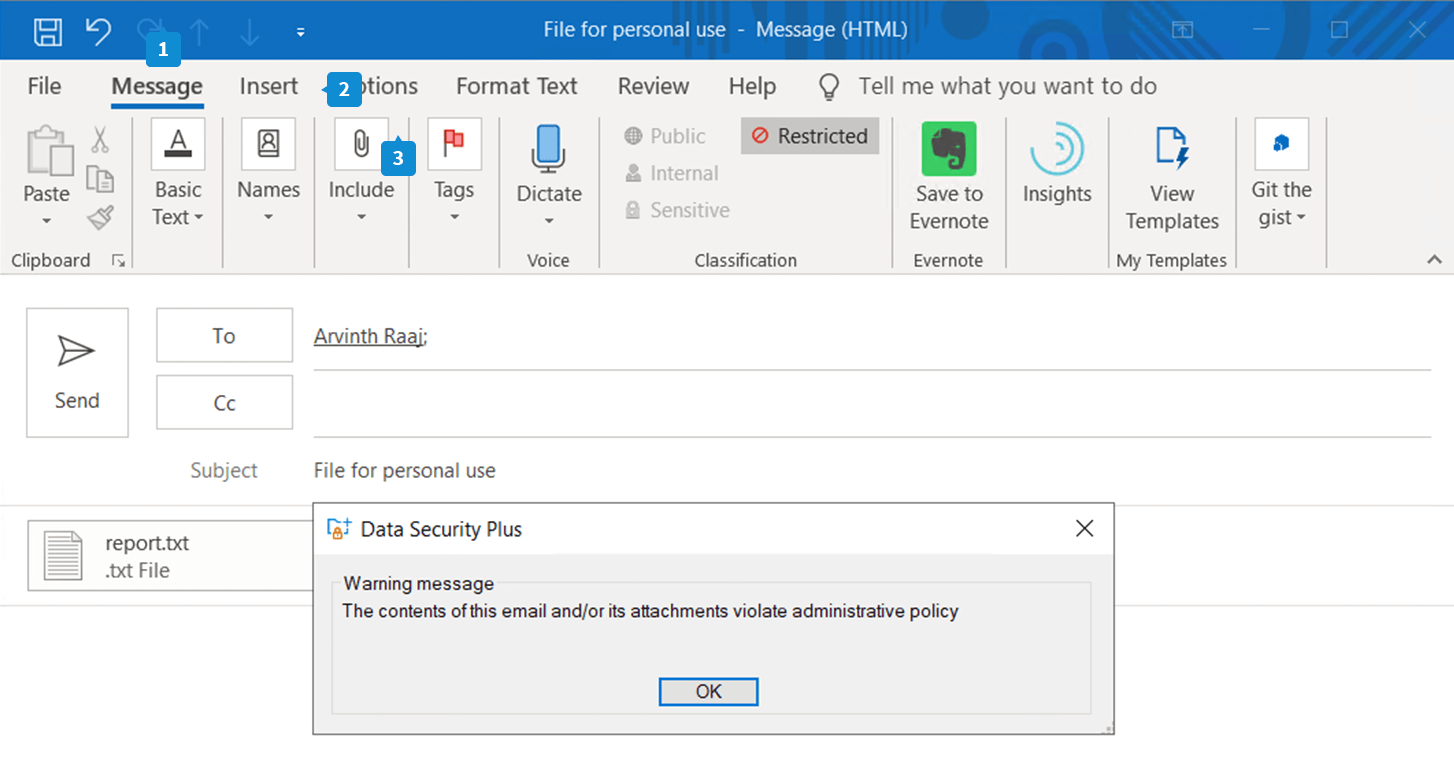
DataSecurity Plus enables you to alert and block files from being sent via email (Outlook) by implementing attachment protection.
Steps to block critical files from being sent as attachments in email:
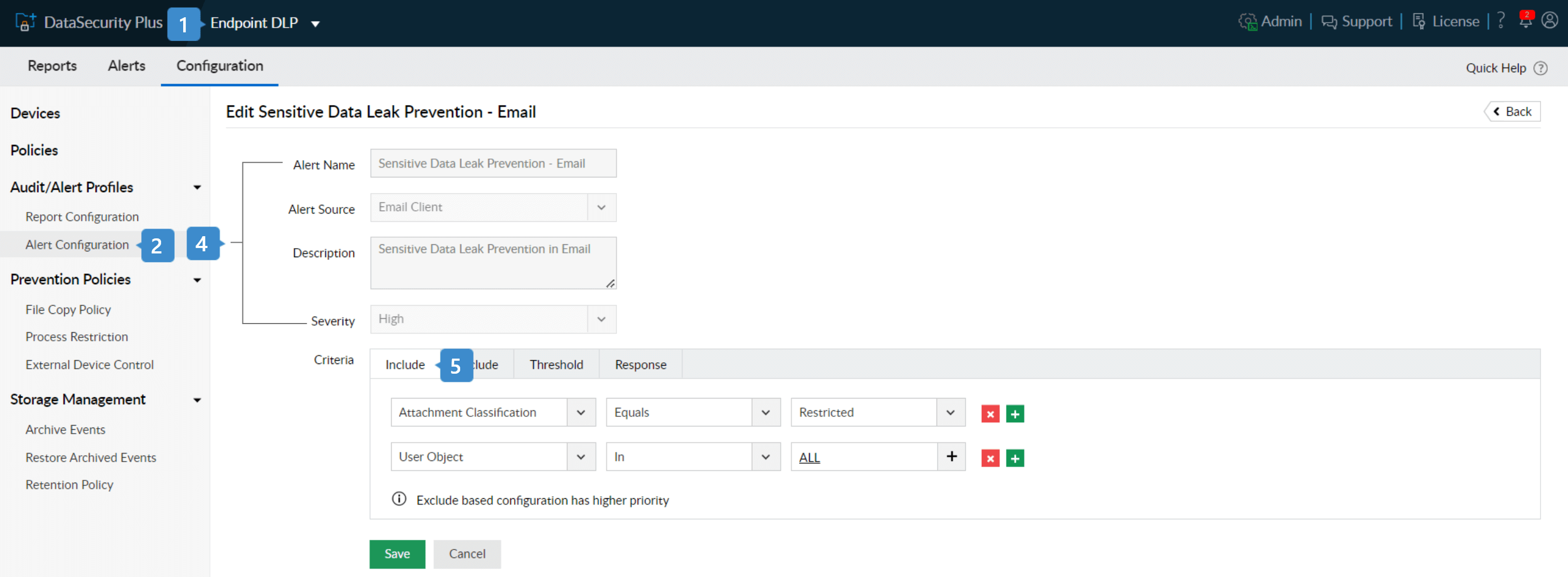
- Select Endpoint DLP from the application drop-down.
- Navigate to Configuration > Audit/ Alert Profiles > Alert Configuration and select Email Client.
- Click the Sensitive Data Leak Prevention - Email.
- Confirm that the Alert Name, Source, Description and Severity are configured.
- Under Criteria, choose the following menu options:
- Include:
- User Object: All
- Attachment Classification: Restricted
- Exclude:
Note:
- The attachment classification represents the sensitivity of the file, based on its content.
- If two files with different classifications are uploaded as attachments to the same email, then the most restrictive classification is applied.
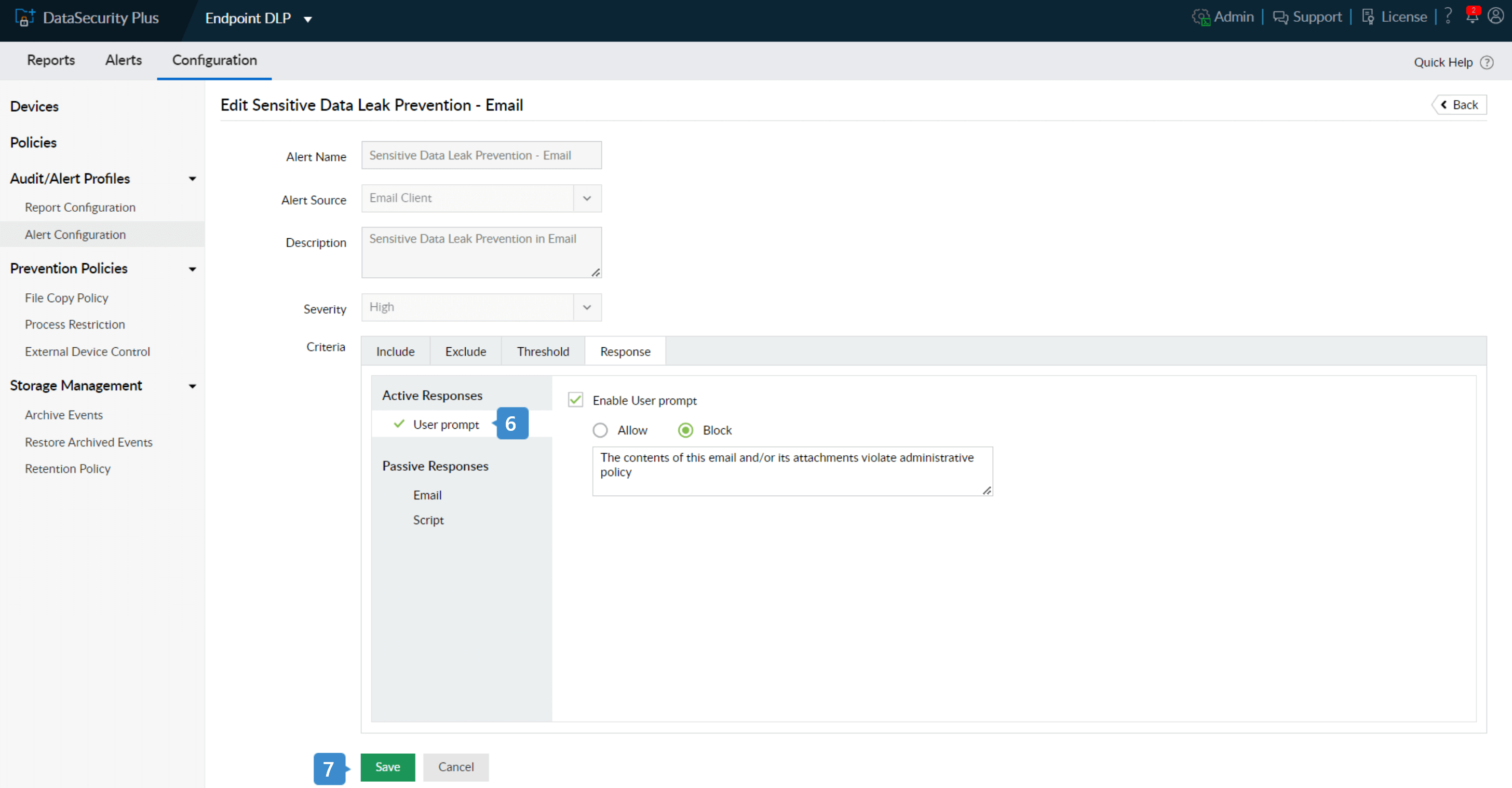
- Set the active response measure as shown below:
User Prompt: Enable User Prompt as Block to prevent the file from being sent, and enter a custom message to be displayed to the user.
- Click Save.
The classification is displayed in Outlook, as shown above.
You have now configured DataSecurity Plus to prevent data theft by employees through USB devices and email.