DNS anomaly detection with machine learning: How ManageEngine DDI Central stops threats before they start

Most breaches don't announce themselves; they whisper.
A subtly malformed DNS query here. A DHCP lease request that looks almost normal there. A client that suddenly requests a domain no one in your organization has ever heard of. By the time these whispers become alarms on a SIEM dashboard, attackers have often already moved laterally, exfiltrated data, or cemented persistence.
In traditional DNS, DHCP, and IPAM (DDI) setups, these signals are buried under millions of legitimate transactions. Security teams scroll through endless logs, hoping pattern recognition and caffeine will catch what signature-based tools missed. That model is broken and threat actors know it.
There's a popular saying: Fortune favors the brave. However, in networking fortune favors the foresighted. That's why we brought ML to the heart of ManageEngine DDI Central—to turn your DNS and DHCP infrastructure from a passive service layer into a predictive, self-learning and self-healing security shield.
This is adaptive defense for DDI. Your network learns, predicts, and stops attacks before they even start.
What is anomaly detection? How does ManageEngine DDI Central deploy it?
Proactive protection powered by ML—built to detect the covert patterns that hide real sophisticated threats. DDI Central transforms your DNS, DHCP, and IP infrastructure into a self-learning shield that analyzes patterns, predicts attacks, and stops them in real time.
Here's what that actually means in practice.
What it does
Anomaly detection in DDI Central is the continuous, ML-driven surveillance of every DNS query and DHCP transaction flowing through your network with one job: to surface the behaviors that shouldn't be happening.
It watches for the quiet outliers that signature-based tools miss. A client that suddenly queries a newly registered domain. A burst of lookups with algorithmically generated names. A subnet absorbing lease requests at unnatural rates. A DUID showing up on two hosts at once. These are the covert patterns that precede real breaches and they never trigger a traditional alert until it's too late.
DDI Central flags each one, scores it by severity, maps it to the responsible entity, and either contains it automatically or hands your team a forensic-ready case file. No log hunting, tool switching, or guesswork.
How it does it
Under the hood, the engine runs three loops in parallel:
1. Behavioral baselining
ML models observe your environment's normal rhythms—query volumes, domain diversity, lease patterns, and client-to-subnet relationships—and build a living baseline of what normal looks like for your network. Not just a generic benchmark.
2. Deviation scoring
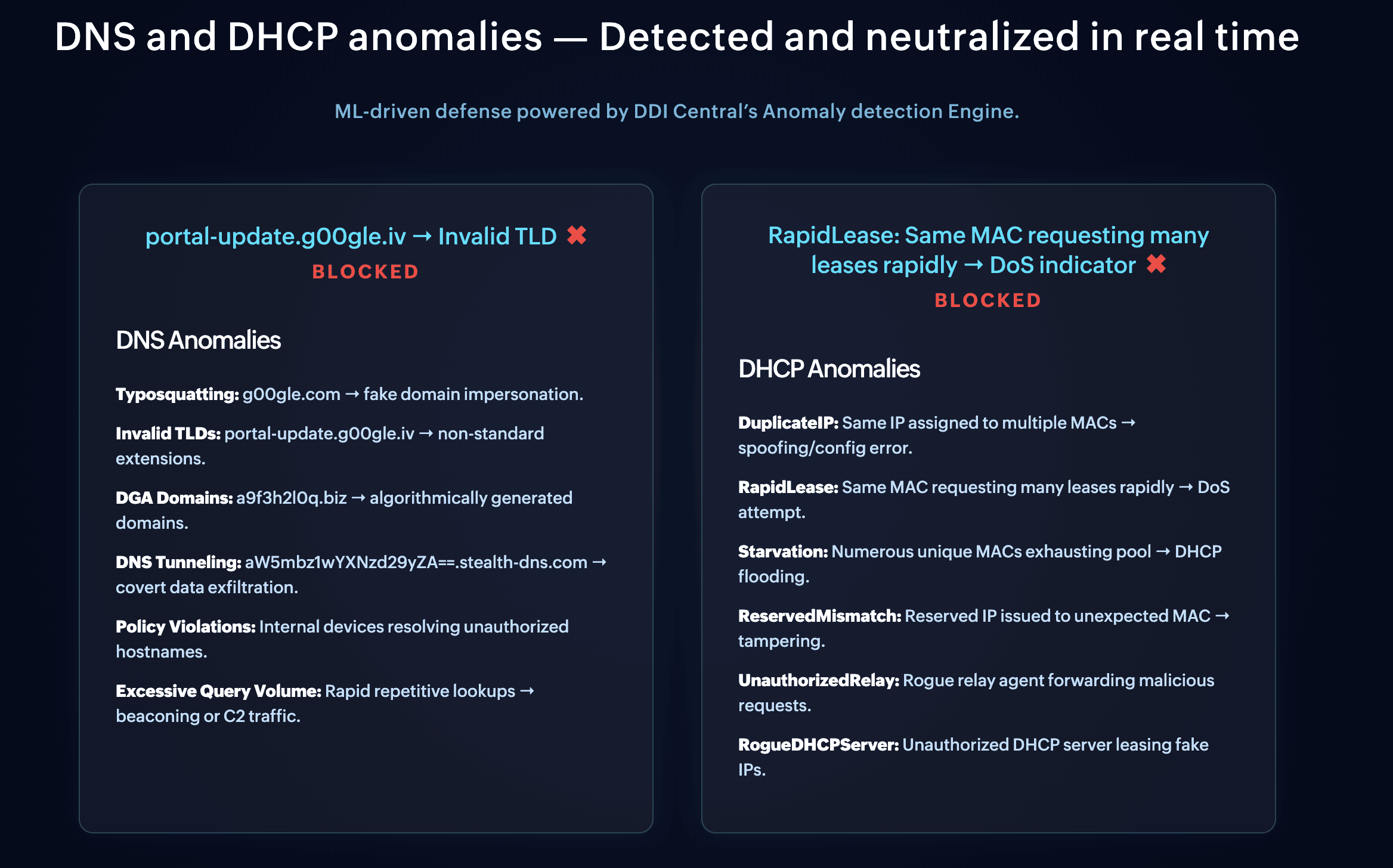
Every incoming DNS and DHCP event is measured against that baseline in real time. Deviations are scored on severity and classified by anomaly type, including: Domain Generation Algorithm (DGA) activity, DNS tunneling, subnet starvation, duplicate identifiers, enumeration waves, query-type abuse, and more.
3. Adaptive response
When an anomaly crosses your configured severity threshold, DDI Central takes containment action automatically by using DNS ACLs on Linux, client subnet isolation on Windows, or DHCP MAC-level quarantine. All of it is surfaced through the Insights dashboard and built-in anomaly reports, so your team reviews, validates, and releases entities on their own pace—not the attacker's.
The loop never stops tightening. Every validated anomaly feeds back into the baseline, making the engine sharper at catching weak signals and quieter on false positives with every cycle.
Why it does it
Unfortunately, the traditional detection model was built for a threat landscape that no longer exists.
Signature-based tools catch what's already been seen and cataloged. Threat feeds catch what's already been reported. Both are reactive by design, meanwhile sophisticated attackers know exactly how to operate in the gap between first seen and first published. That gap is where DGAs generate domains no feed has indexed yet, where tunneling exfiltrates data through queries no rule was written for, where starvation attacks unfold in subnets no one is watching.
DDI Central’s Anomaly Detection Engine closes that gap by shifting detection from known-bad lookups to abnormal behavior, helping catch threats on the day they emerge—not the day they receive a CVE. Since DNS and DHCP are the first infrastructure layers every attacker must eventually touch, anomaly detection at the DDI layer gives you the earliest possible warning the rest of your security stack has to work with.
That's the shift: reactive to predictive. From chasing signatures to reading behavior. From finding out after to knowing before.
Pillar 1 — The insights dashboard: Your complete anomaly landscape at a glance
Every good investigation starts with orientation. Before you can act, you need to see the full shape of the threat landscape inside your environment. The Insights dashboard was engineered to give you exactly that—the entire pulse of anomalies, mapped, ranked, and made meaningful.
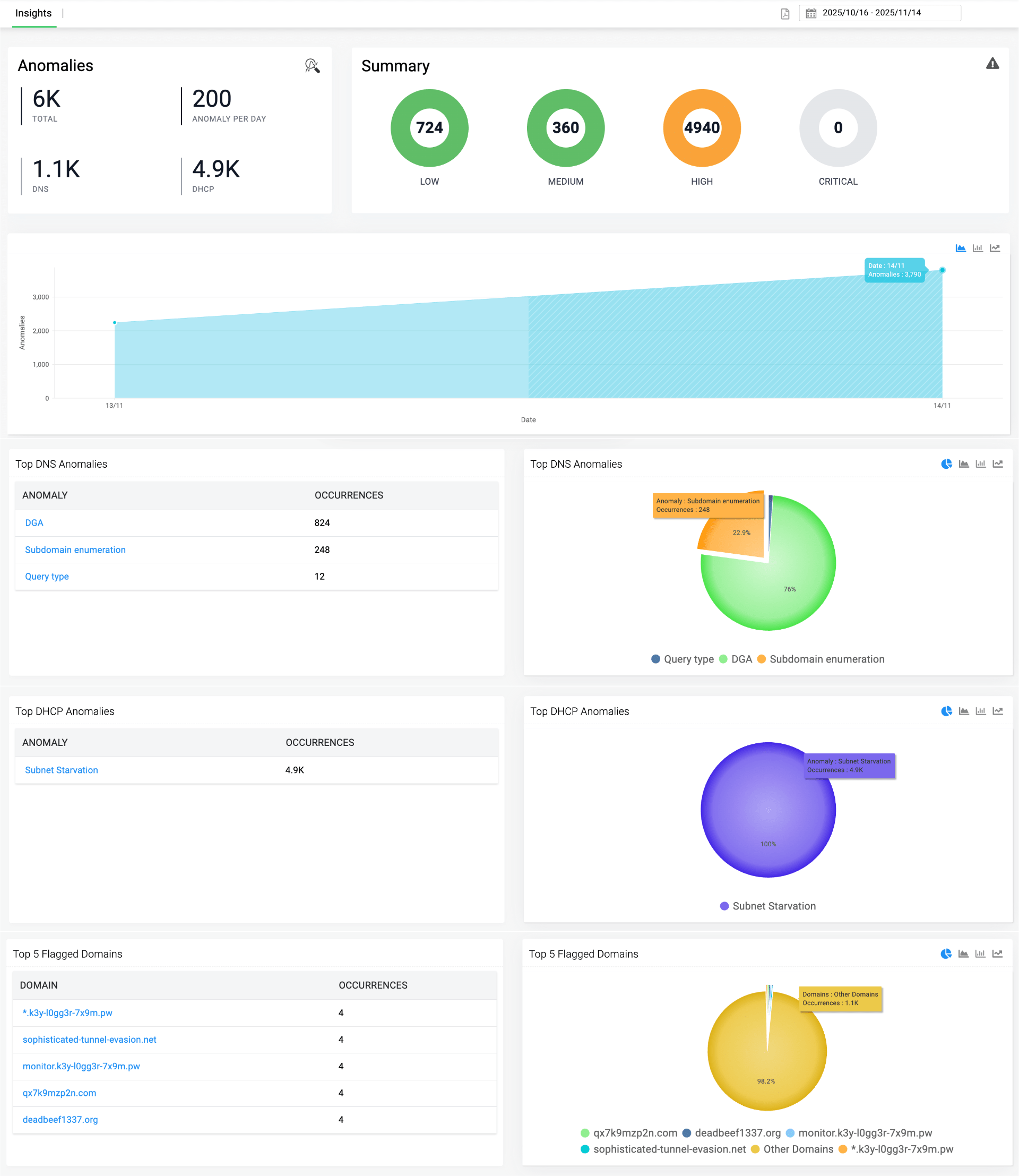
It opens with an executive-grade view of your organization's risk posture. You can instantly quantify the true volume and weight of DNS and DHCP anomalies across every site, without ever sifting through logs.
Stratified risk visibility: Anomalies are automatically bucketed into low, medium, high, and critical tiers by the engine. You see where risk concentrates in a single glance, so triage becomes a matter of reading severity and not interpreting it.
Time-series risk tracking: A rolling anomaly curve reveals whether threats are spiking, flattening, or dropping. It's your early indicator of creeping instability, letting you predict breakpoints before they happen rather than reconstruct them afterwards.
Evidence-driven threat hunting: The dashboard pinpoints dominant DNS threat categories, reconnaissance, DNS tunneling, DGA activity, and surfaces them as executive-ready insights. No protocol analyst required to interpret what's happening.
DHCP pressure-point visualization: DHCP anomalies rarely get the attention they deserve, yet they're often the earliest sign of a starvation attack, rogue device, or identity-spoofing attempt. The dashboard shows which DHCP category occupies the largest footprint and lets you drill into affected entities, timestamps, and conflict patterns with a single click.
Flagged domain forensics: A ranked view of the domains driving most DNS anomalies. Click into any one and you uncover risk patterns, client activity, triggering behaviors, and forensic cues; the full evidence trail needed for rapid validation.
Pillar 2 — Network risk snapshot: Emerging threat signals in real time
If the Insights dashboard tells you the shape of your risk, the Network Risk Snapshot tells you the story behind it. It's designed for the moment you've spotted something suspicious and need to understand who, what, and where quickly.
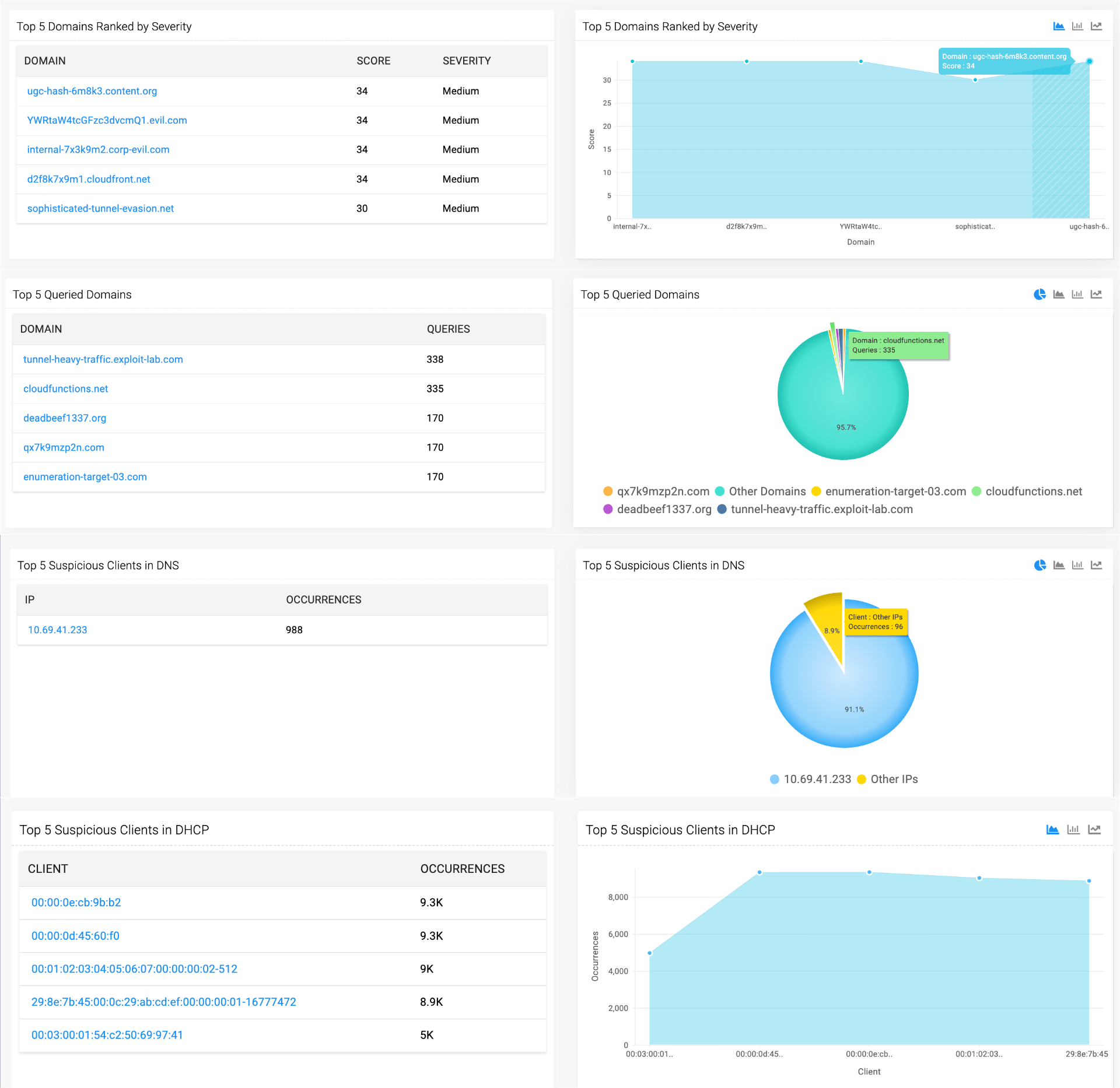
See why a domain was flagged, not just that it was: Every flagged domain comes with a severity score and context, revealing whether your risk is dominated by a handful of bad actors or spread evenly across the environment. Urgent validation becomes reading a ranked list, not reverse-engineering an alert.
See where your DNS traffic truly flows: A ranked snapshot of the highest-hit destinations reveals which suspicious domains are being hammered. Unexpected domains with high query counts are almost always one of three things: malware infections, misconfigurations, or shadow services running quietly on your network.
Identify the clients driving your DNS risk: Correlate why each endpoint triggered the anomaly load, enabling rapid confirmation of malware, misconfiguration, or insider misuse, which accelerates remediation workflows before small problems metastasize.
Track misbehaving clients through DHCP activity: Correlate each endpoint's anomaly trail with excessive leases, duplicate identifiers, or lease churn. You instantly see whether a host represents a persistent attack or a short-lived disturbance. A distinction that changes how you respond.
Pillar 3 — Built-in anomaly reports: Forensic depth without log scrubbing
Dashboards tell you what. Reports tell you why. DDI Central's built-in anomaly reports, split across DNS and DHCP, give your team the forensic depth needed to move from detection to confident action without ever opening a raw log file.
DNS anomaly reports
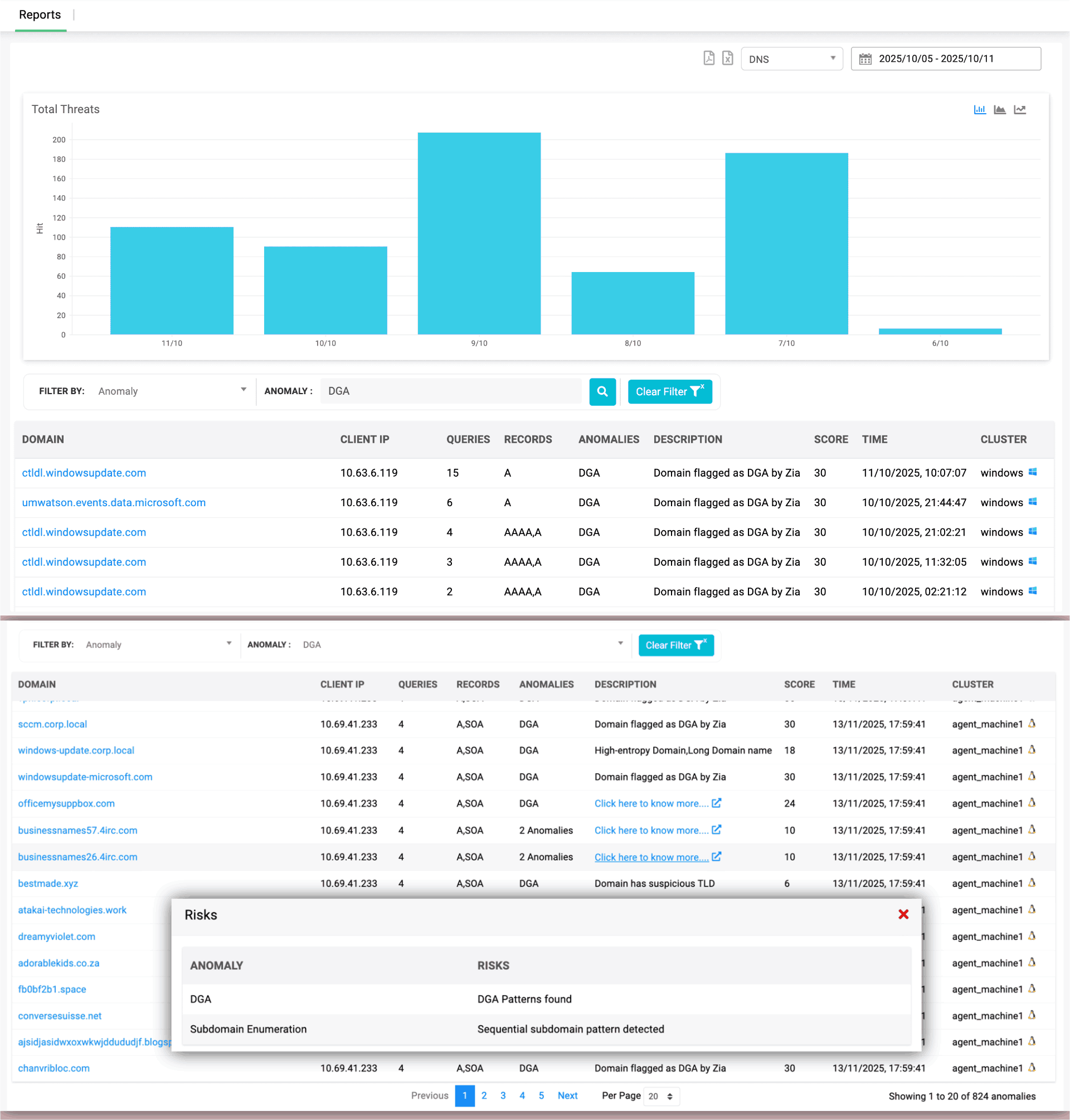
See the reasons, not just the flags. Every DGA or enumeration alert surfaces the exact risk indicators behind it—high entropy, long labels, suspicious Top Level Domains (TLDs), and sequential subdomains—so you understand why a domain was flagged.
Follow the trail from domain to endpoint: Trace anomalies back to the exact client IPs that queried suspicious domains, connecting DNS behavior directly to endpoint investigation.
Reconstruct the timeline in seconds: Query counts, record types, and timestamps reveal how often and when a suspicious domain was hit, giving you a clean timeline without stitching logs together.
Patterns, clusters, and clues in one feed: Link anomalies to source clusters to see which vantage point observed the behavior and whether the pattern was localized or distributed.
Point-and-click forensics: Pop-ups reveal risk reasons instantly, replacing raw packet combing with one-click evidence.
DHCP anomaly reports
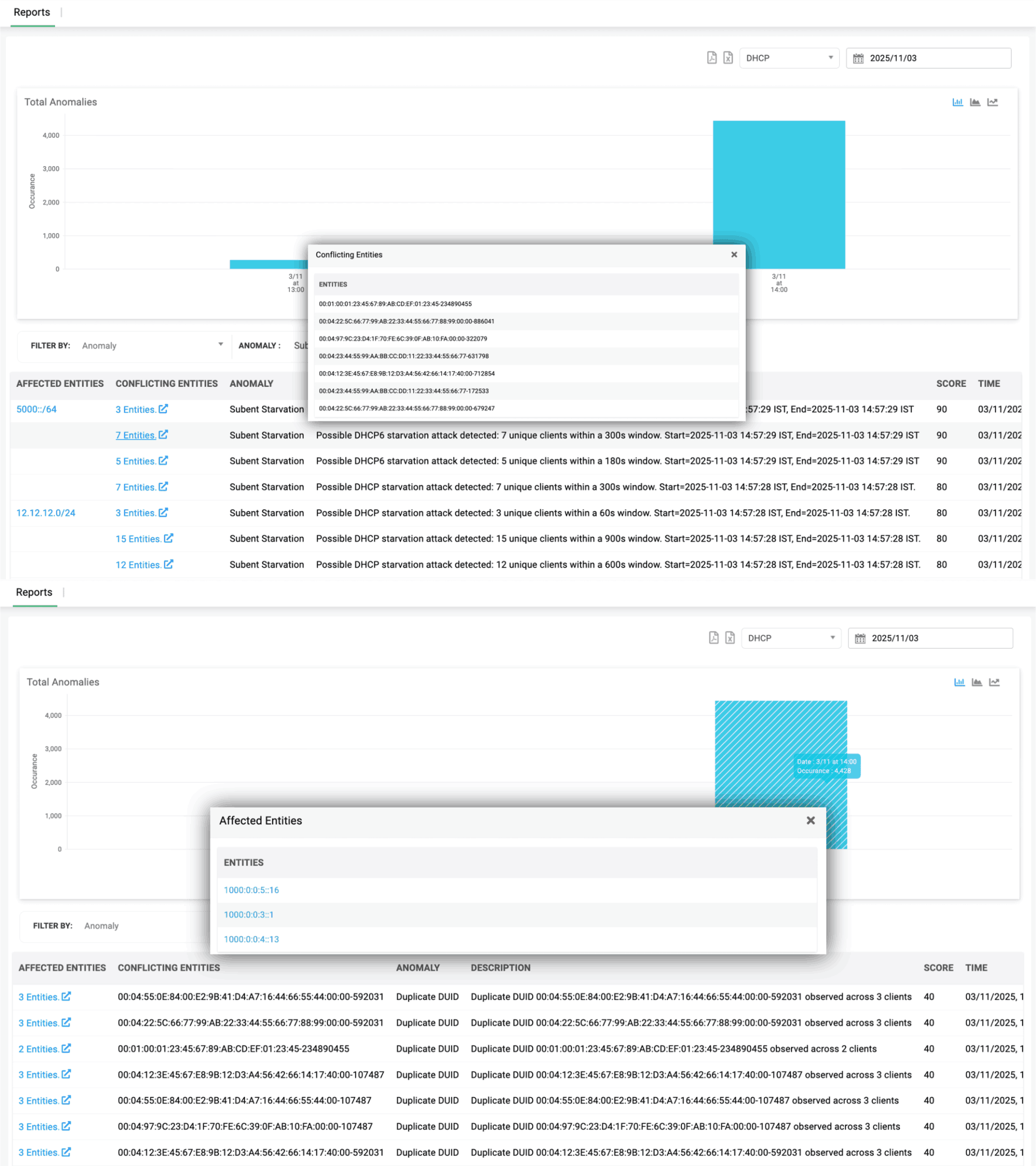
From a thousand events to the one you need: Drill down by risk score, DHCP type, cluster, anomaly type, or affected entity to locate the precise event you're hunting.
Trace instability to its true sources. Identify which clients triggered Duplicate DUIDs, Duplicate IAIDs, or subnet starvation; a definitive offender list for admins, a risk-origin view for CXOs.
Temporal clarity on demand: View anomalies tied to a specific day and hour to see when misbehavior peaked or stabilized, which is critical for post-incident reviews and trend analysis.
Context without screen-switching. Detection windows, unique client counts, and timestamps surface inline on every event. No tool pivoting. No copy-pasting MACs into spreadsheets.
Conflict-group clarity. Review groups of clients sharing identifiers, leases, or abnormal patterns and turning chaos into actionable leads. Drill into the exact MACs, DUIDs, or IPs involved to trace spoofing attempts and misconfigurations with zero guesswork.
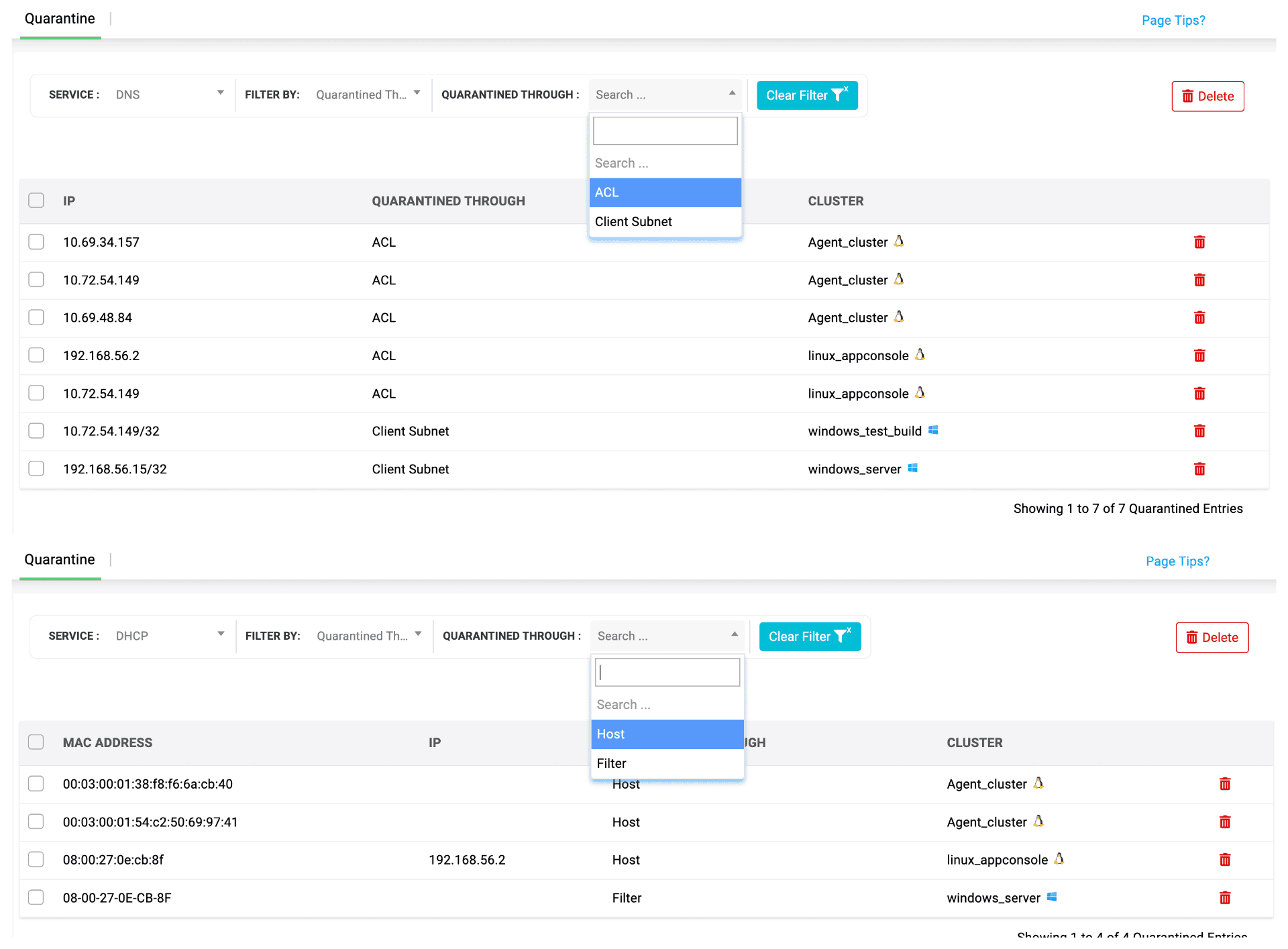
Pillar 4 — Anomaly detection and response: Your zero-touch quarantine command center
Detection without response is just expensive observation. The fourth pillar closes the loop—where DDI Central's adaptive intelligence translates into measurable defensive outcomes.
Automatic containment
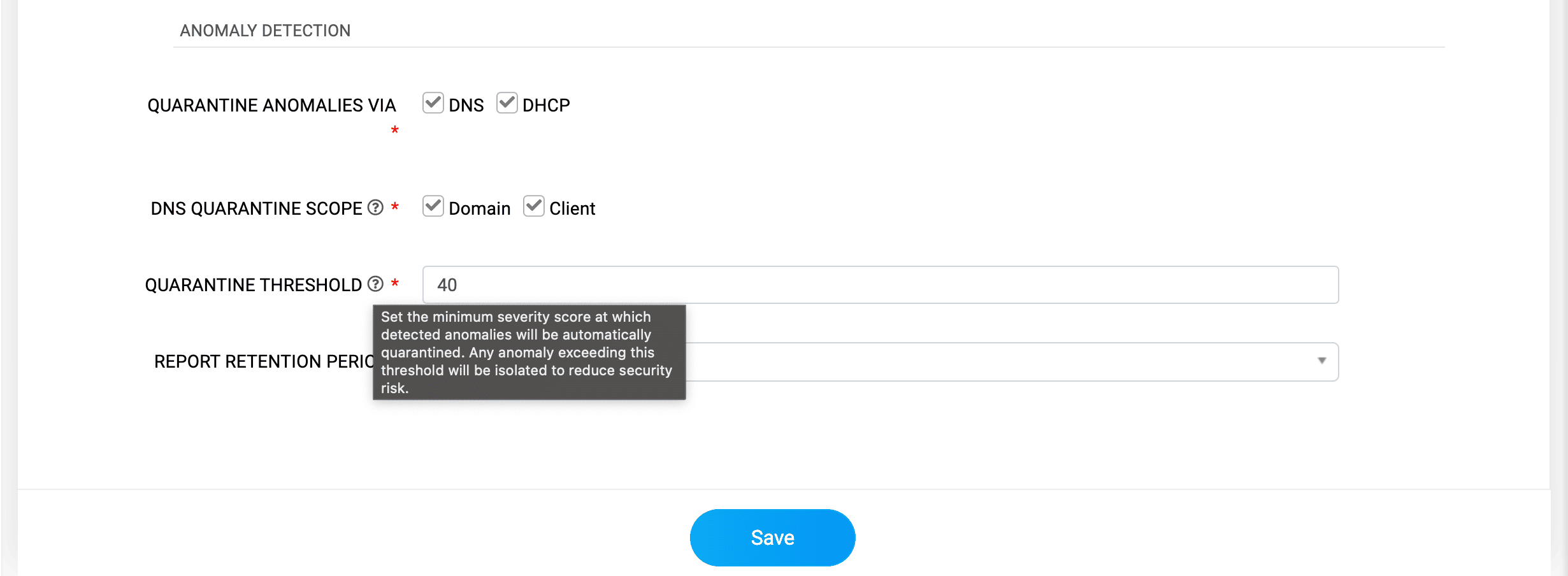
Zero-touch containment. The moment an anomaly crosses your severity threshold, DDI Central blocks the threat entity by using DNS ACLs on Linux and client subnet-based isolation on Windows to cut off compromised devices from making further queries. Malware spread stops at the earliest possible stage.
Contain on your terms: Choose the quarantine method that fits your environment—DNS-level blocking, DHCP MAC isolation, or a combined mode—for precision containment aligned to your architecture and security policy.
Review what was stopped, on your own pace. All quarantined domains and clients are held in a dedicated zone where your team can validate impact, filter by score or cluster, and follow the evidence—without live threats still in play.
Focused investigation
Containment buys you time. Investigation uses it well.
Your threshold. Your rules: Customize risk score thresholds for DNS and DHCP so auto-quarantine triggers only at the severity your operational risk appetite calls for.
One view. All blocked threat paths: Every domain ACL block and every MAC-level DHCP quarantine consolidated into a single table, a complete picture of what was intercepted.
Reclaim what's clean.Keep out what isn't: Decide which hosts can rejoin after remediation and which should stay blocked. Clean recovery without reinfection risk.
No panic. No packet diving: The system quarantines automatically and surfaces only what needs your attention, from a unified console where you can drill down and release entries by cluster, IP, or method.
Why DDI Central's anomaly detection engine matters: The compounding advantages of adaptive DDI security
Step back from the individual features, and a larger pattern emerges. What the DDI Central anomaly detection engine really delivers is time. The one resource every security team is starved for and time compounds.
Auto-triage and auto-containment let teams investigate without rushing to respond.
Detection-to-validation in one flow eliminates tool-switching, log-hunting, and fragmented diagnosis.
Behavioral scoring surfaces risky communication long before a threat feed or signature can recognize it.
Zero-delay visibility into emerging DGA storms, starvation trends, query anomalies, and enumeration waves as they form, not after.
Flexible visualization (pie, area, bar, line) adapts to investigation needs and data density.
Investigation-ready metadata on every event with each anomaly links back to its service scope (zone, subnet, host), accelerating the move from detection to validation.
Faster validation, smaller blast radius: Context-rich verification in seconds shrinks exposure windows.
ML-driven continuous learning tightens baselines over time, reducing noise and exposing true weak signals earlier.
The bottom line: Foresight is the new perimeter
The perimeter-based model of security is dead. What's replaced it isn't a new fence —it's a new mindset. The modern defense isn't built on walls; it's built on foresight. On knowing, before anyone else does, that something subtle is off.
DNS and DHCP aren't just plumbing. They're the first layer that every attacker—from commodity malware to nation-state operators must eventually touch. That makes your DDI infrastructure the most valuable, underutilized early-warning system in your environment.
With ManageEngine DDI Central, we've turned that system on. Detect early. Respond instantly. Outpace new, sophisticated threats with DDI Central's adaptive intelligence. Your network is already seeing the first signs. The only question is whether you're seeing them with it.
Ready to turn your DDI into a self-learning shield? Explore ManageEngine DDI Central and see how adaptive defense changes the economics of network security.