How DDI Central's DNS security features help organizations build a stable, resilient DNS network

Most security investments focus on the perimeter, like firewalls, endpoint agents, and SIEM alerts. Yet one of the most abused channels in enterprise attacks barely gets a second look: DNS. Before malware is executed, before data is exfiltrated, and before a lateral movement attempt begins, DNS is involved. Attackers use it to find footholds, establish command-and-control (C2) channels, and quietly map internal infrastructure.
Yet protecting DNS isn't just about blocking threats. A misconfigured, invalidated, or unencrypted DNS layer is a liability on its own, even without an active attacker. Spoofed responses, unauthorized zone transfers, amplification attacks, or a resolver that simply doesn't know where to start: Any one of these can silently erode the reliability of your entire network.
So what does it actually take to build a DNS layer your organization can depend on—one that's secure, trustworthy, and resilient under pressure?
DDI Central answers that question across eight tightly integrated security features. Together, they don't just harden DNS. They transform it into a verified, encrypted, and policy-enforcing foundation that your network can stand on.
1. Controlling the gate: ACLs and TSIG
Security starts with a simple question: Who should be talking to your DNS server in the first place? Without a clear answer enforced at the infrastructure level, your DNS is open to abuse, such as unauthorized queries, rogue zone transfers, and unauthenticated dynamic updates.
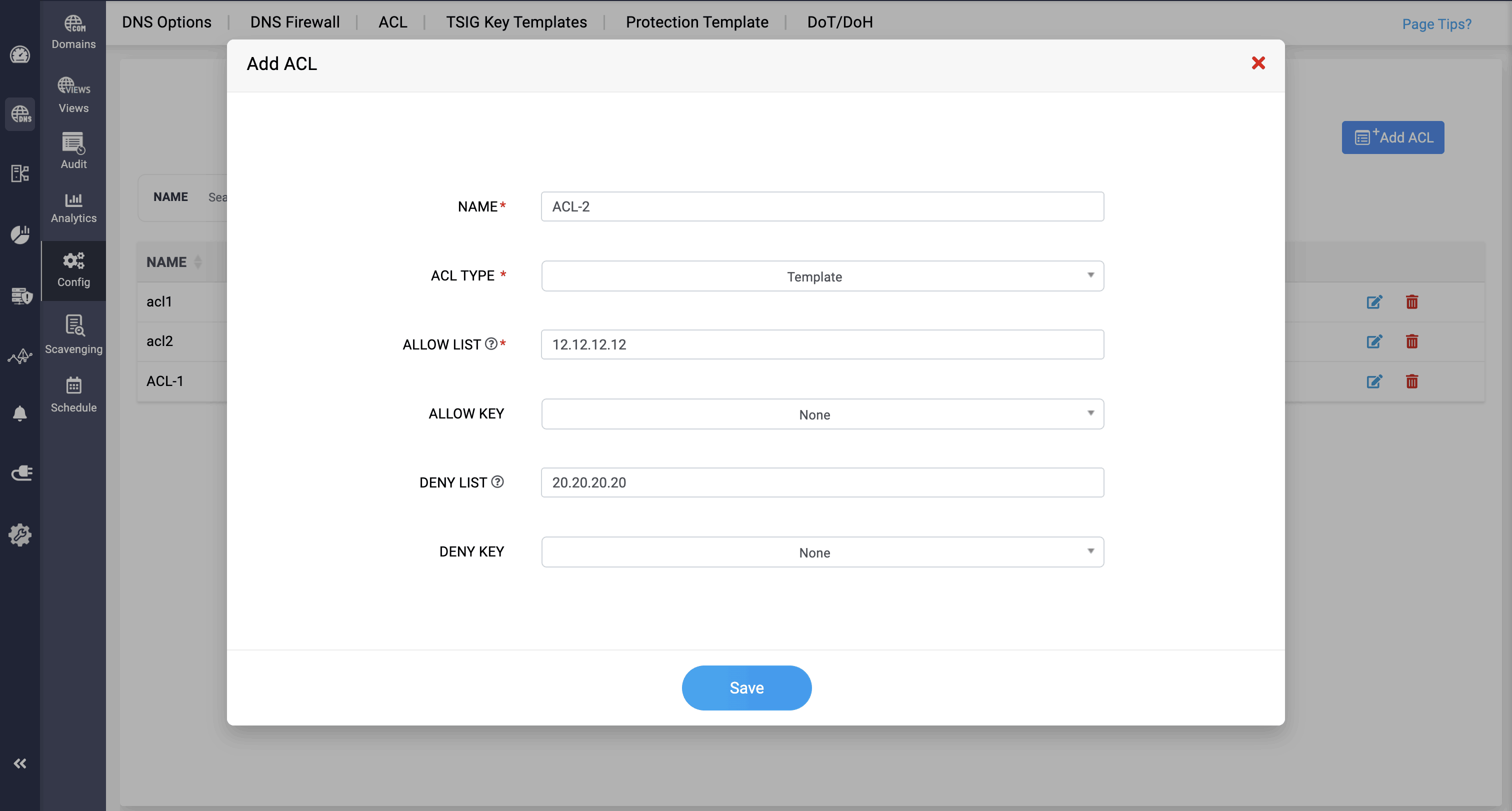
DDI Central's access control lists (ACLs) let admins define precisely which clients, subnets, or servers can query DNS, receive zone data, or submit dynamic updates. Rules can be applied globally at the cluster level, scoped to specific zones or views, or layered across both.
ACL templates make this scalable. Define a policy once and apply it everywhere. Whether you're working in DDI Central's simplified allow and deny interface or in full ISC BIND format for complex environments, ACLs ensure that your DNS server only responds to traffic it's supposed to.
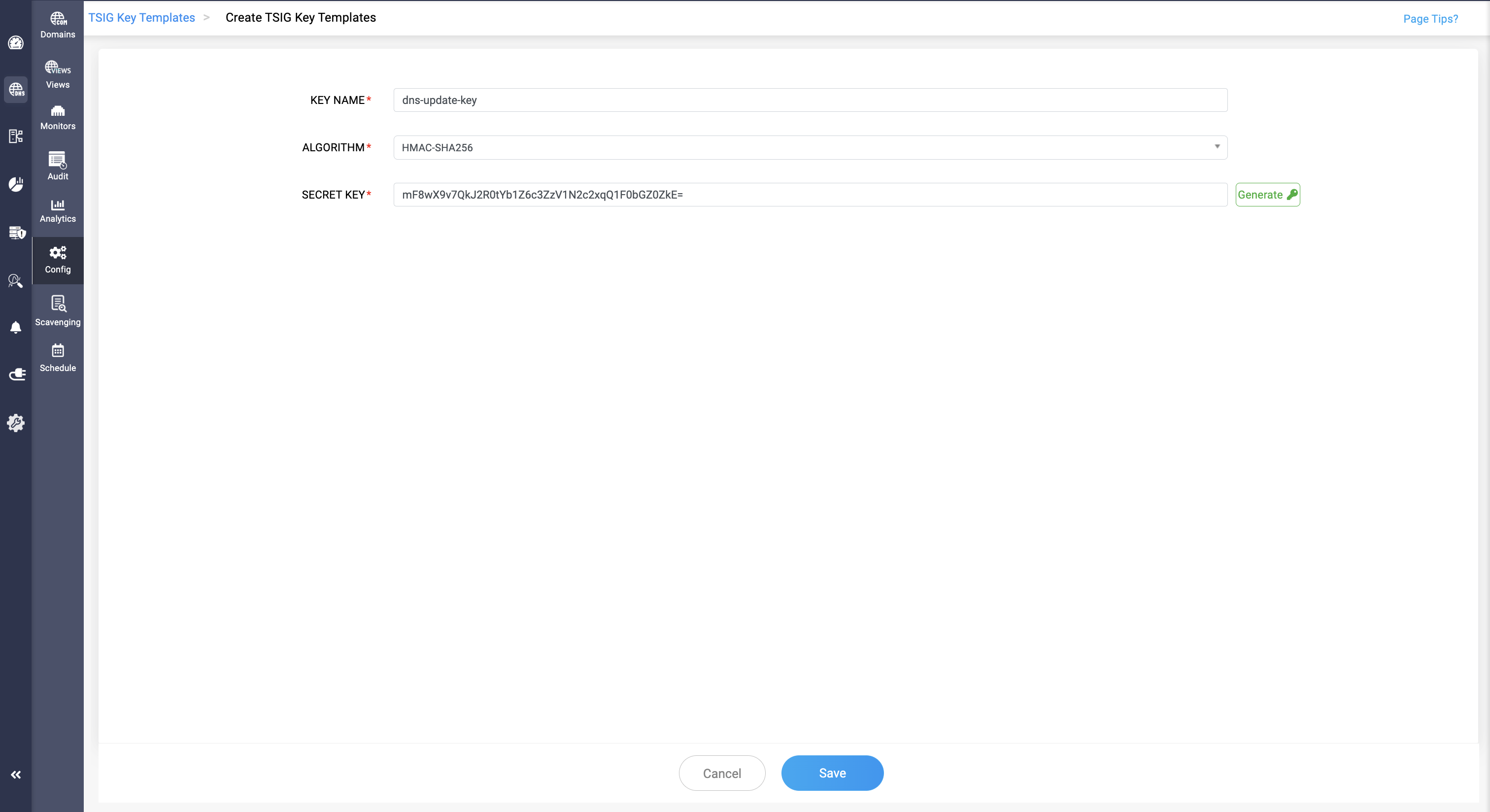
Standard DNS has no native mechanism for verifying the identity of the server sending data. That gap is what Transaction Signature (TSIG) closes. Using shared secret keys and HMAC cryptography (with algorithm options ranging from SHA-1 to SHA-512), TSIG signs every DNS transaction between servers.
Zone transfers are authenticated. Dynamic updates are verified. The risk of a rogue secondary server quietly siphoning your DNS zone data is eliminated. DDI Central stores TSIG key templates centrally, making it straightforward to apply consistent authentication across your entire DNS infrastructure.
2. Making DNS trustworthy: DNSSEC and encrypted transport
Controlling access is the first layer. The second is ensuring that the DNS data itself can be trusted, that responses haven't been tampered with in transit, and that the communication channel is private.
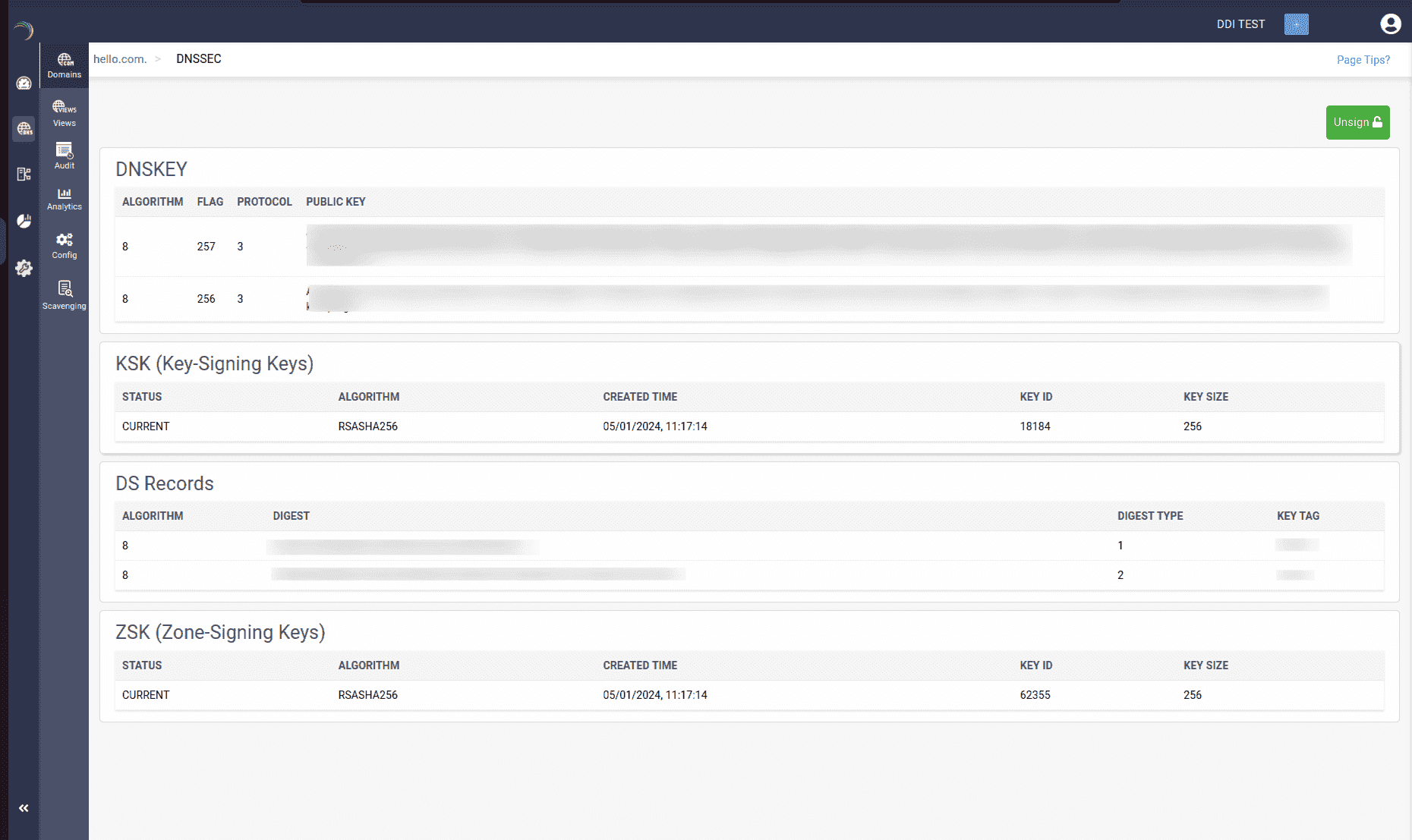
DNS cache poisoning is one of the oldest, most effective attacks in the book: intercepting a query, returning a forged response, and redirecting users to a malicious destination. DNSSEC makes this impossible by cryptographically signing DNS records at the zone level.
Every record set in a signed zone carries a digital signature. Resolvers configured to validate DNSSEC can verify that the response came from the legitimate zone owner and hasn't been modified. DDI Central makes this remarkably simple to deploy, so admins sign a zone with a single click, and the required DNSKEY and DS records are automatically generated. The chain of trust, from root to record, is established and maintained without manual key management overhead.
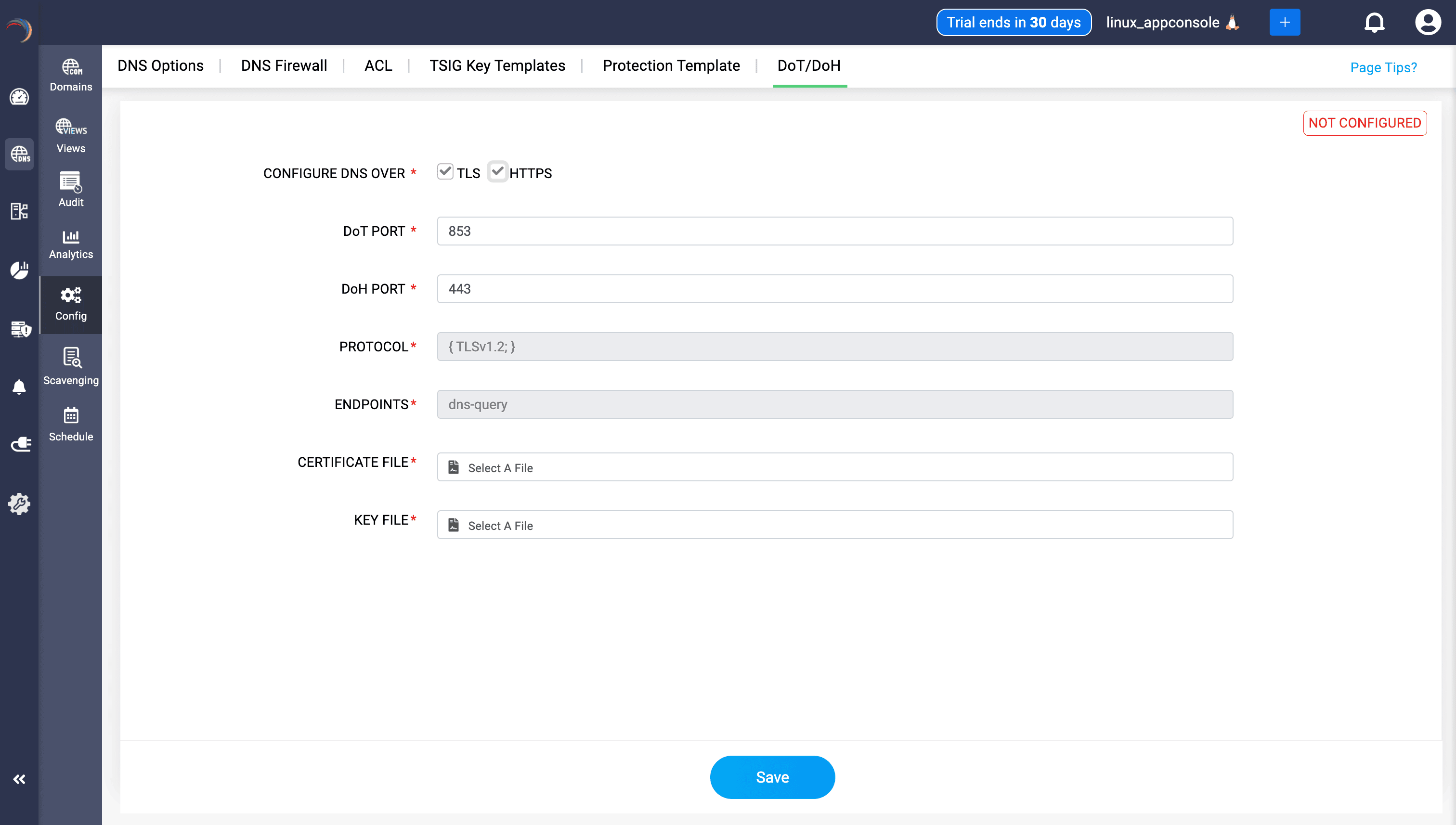
Even with DNSSEC validating the integrity of responses, traditional DNS queries still travel in plaintext. Anyone on the network path, like ISPs, on-path attackers, and surveillance systems, can read every domain your users resolve. That's both a privacy risk and security exposure.
DDI Central supports both DNS over TLS (DoT) and DNS over HTTPS (DoH), giving admins flexible, encrypted alternatives:
• DoT (port 853) encrypts DNS traffic using TLS, keeping it separate from web traffic. This is ideal for enterprise environments where DNS visibility and content filtering need to coexist.
• DoH (port 443) tunnels DNS inside HTTPS, making queries indistinguishable from regular web traffic. This is suited for privacy-sensitive or less controlled environments.
Configuration in DDI Central is UI-driven: Eenable DoT, DoH, or both; upload TLS certificates; set endpoints; and save. Once this is configured on the server side, enforcement can be pushed to all endpoints via endpoint control solutions, guaranteeing that every device in your network communicates with DNS over an encrypted channel.
3. Blocking threats at the DNS layer: DNS Firewall
With access controlled and data integrity assured, the next layer is active threat prevention. Not every attack involves a sophisticated exploit. Sometimes it's simply a user whose device queries a malicious domain, triggering a download, a callback, or a phishing page. DNS is the ideal place to stop it.
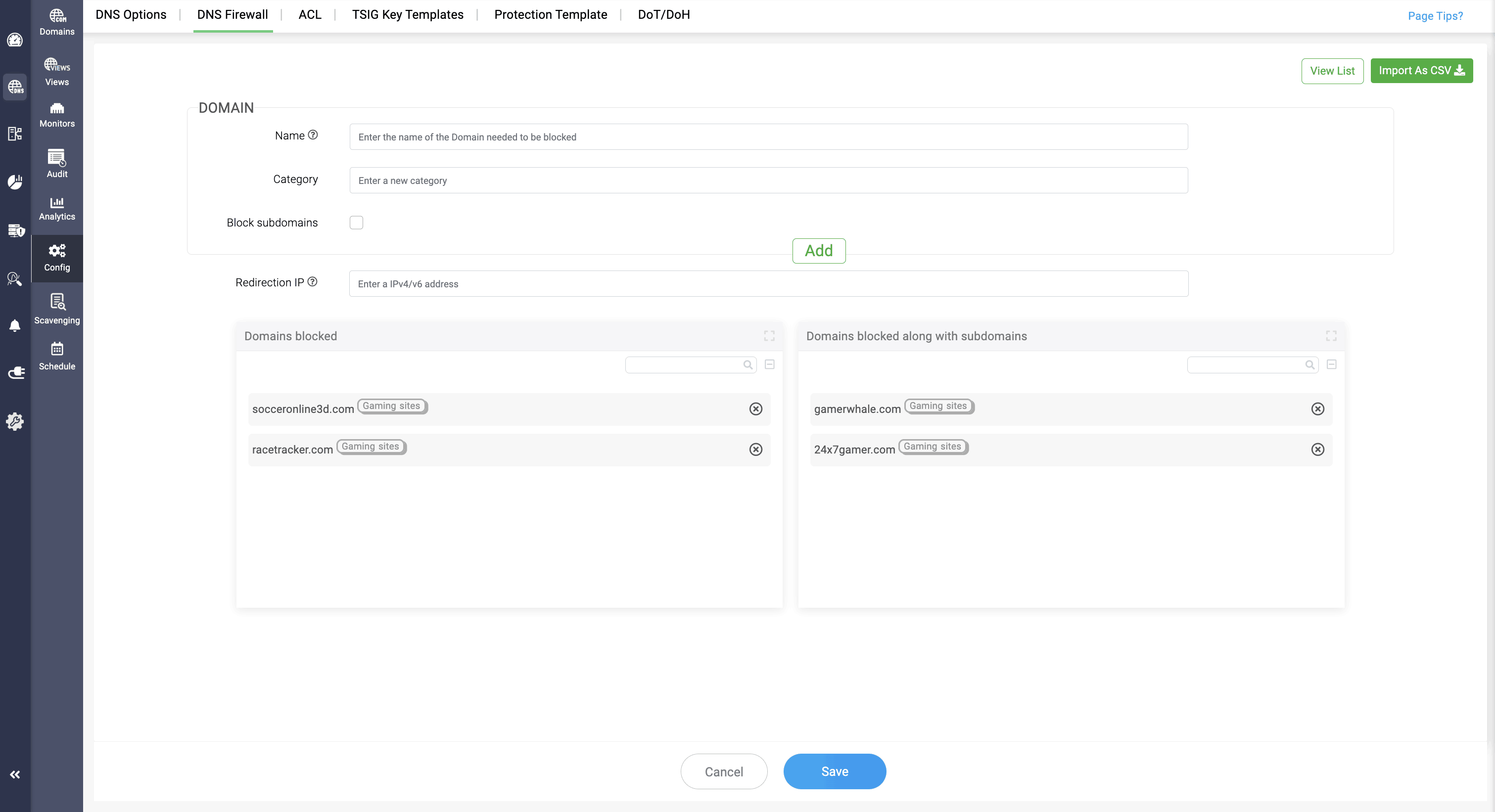
DDI Central's DNS Firewall intercepts outbound queries before they reach the internet and checks them against a configured blocklist. If a domain is flagged, the firewall prevents resolution and silently redirects the client to a safe IP address of your choosing—no error, no exposure, and no alert fatigue for the user.
Here's what makes DDI Central's implementation practical at the enterprise scale:
• Custom blocklists: Build and manage your own lists organized by categories, like malware, phishing, C2 infrastructure, adult content, or any classification that fits your policy.
• Third-party threat feeds: Pull in curated lists of known malicious domains from external security providers, keeping your blocklist current without manual curation.
• Subdomain coverage: Blocking a domain automatically covers all its subdomains, closing the gap that attackers exploit by rotating through subdomains of the same malicious root.
• Bulk importing via a CSV: Onboard large blocklists instantly without entering domains one by one.
The DNS Firewall turns your resolver into a policy enforcement point that quietly filters millions of queries a day, keeping users and devices away from known bad destinations without disrupting legitimate traffic.
4. Defending against volumetric attacks: RRL and Protection Templates
Even a well-secured DNS server can be brought to its knees by volume. DNS amplification attacks, NXDOMAIN floods, and recursive query abuse don't need to bypass your security controls; they just need to exhaust your resources. That's where traffic-layer defenses come in.
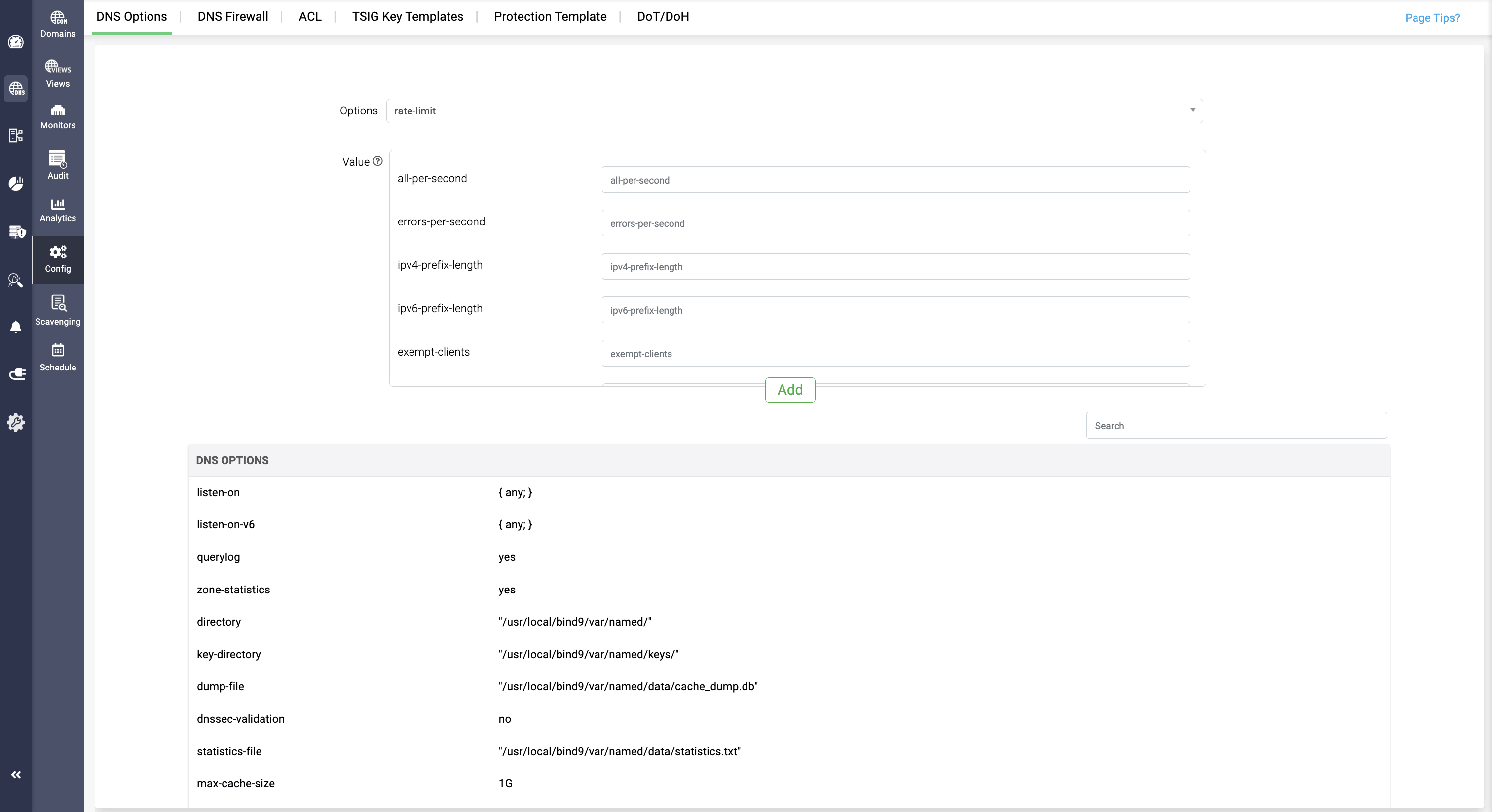
Response Rate Limiting (RRL) limits the rate at which DNS responses are sent to any given client or subnet. When DDI Central detects an abnormal volume of identical requests (a hallmark of amplification attacks), it begins throttling responses, cutting off the flood before it can overwhelm your infrastructure or be weaponized against a third party.
The controls are granular: Admins can set per-second limits for total responses, NXDOMAIN replies, NODATA replies, error responses, and referrals independently. The slip parameter adds intelligence to throttling; instead of dropping excess requests silently, DDI Central can return truncated responses that push clients to TCP, a channel that's far more resource-intensive for attackers to sustain. Trusted subnets can be exempted, and a log-only mode lets admins test configurations safely before enforcing them.
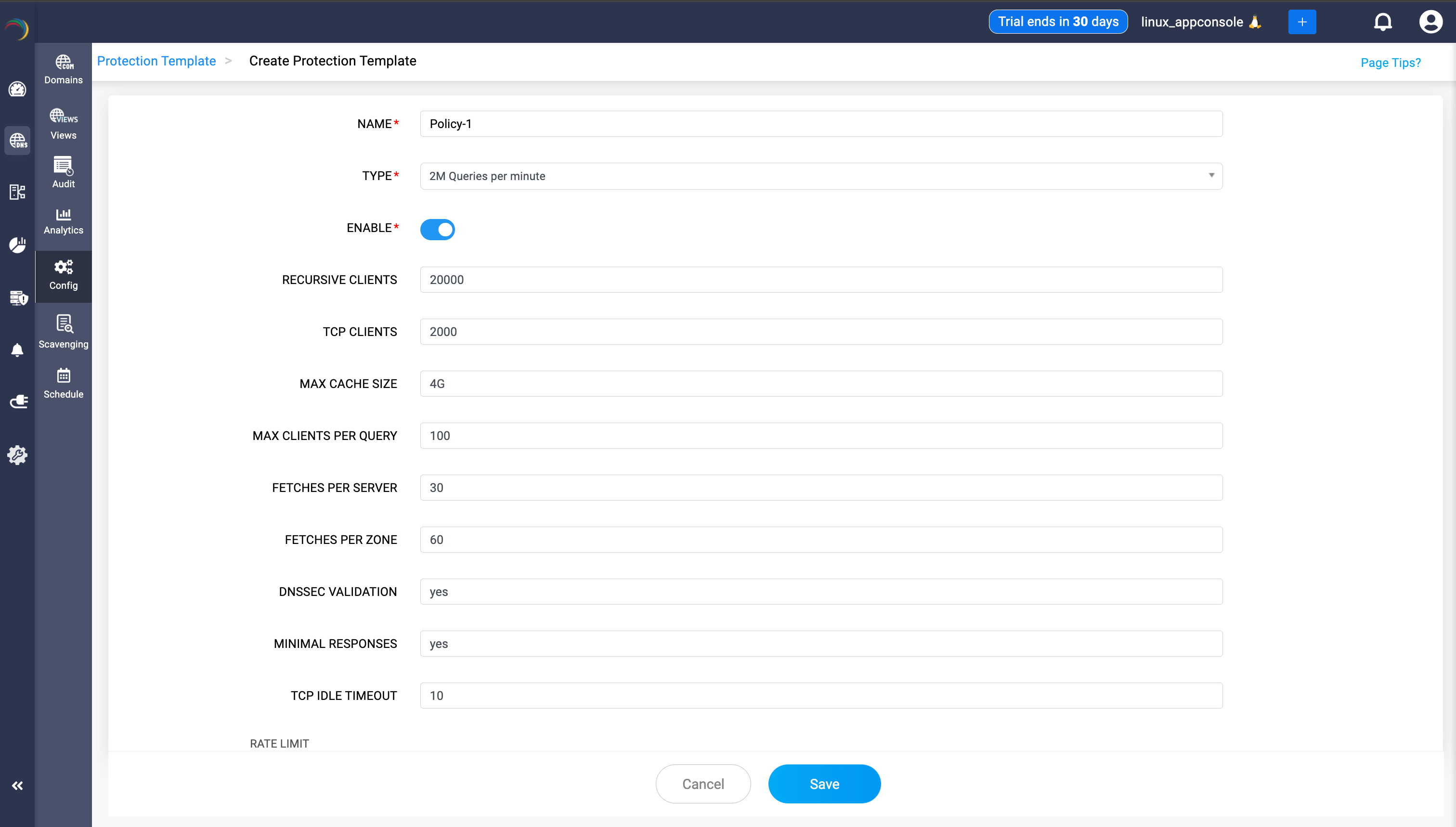
Configuring rate limits server by server is error-prone and hard to audit. Protection Templates solve this by letting admins codify their DNS security posture into reusable, policy-driven profiles that can be applied across every server in a cluster.
Each template consolidates the full range of server-level controls into a single configuration:
• Query rate presets (50,000, one million, two million, or five million queries per minute) for environments of any size, with a Custom option for precise tuning
• Resource limits for recursive clients, TCP connections, concurrent fetches per server and zone, and the cache size, preventing resource exhaustion from misconfigured or abusive clients
• An integrated DNSSEC validation toggle and a minimal response mode, reducing data leakage risk while maintaining performance
One template is consistently applied—no configuration drift, no gaps, and no manual audits required.
5. Starting from a trusted foundation: Root Hint
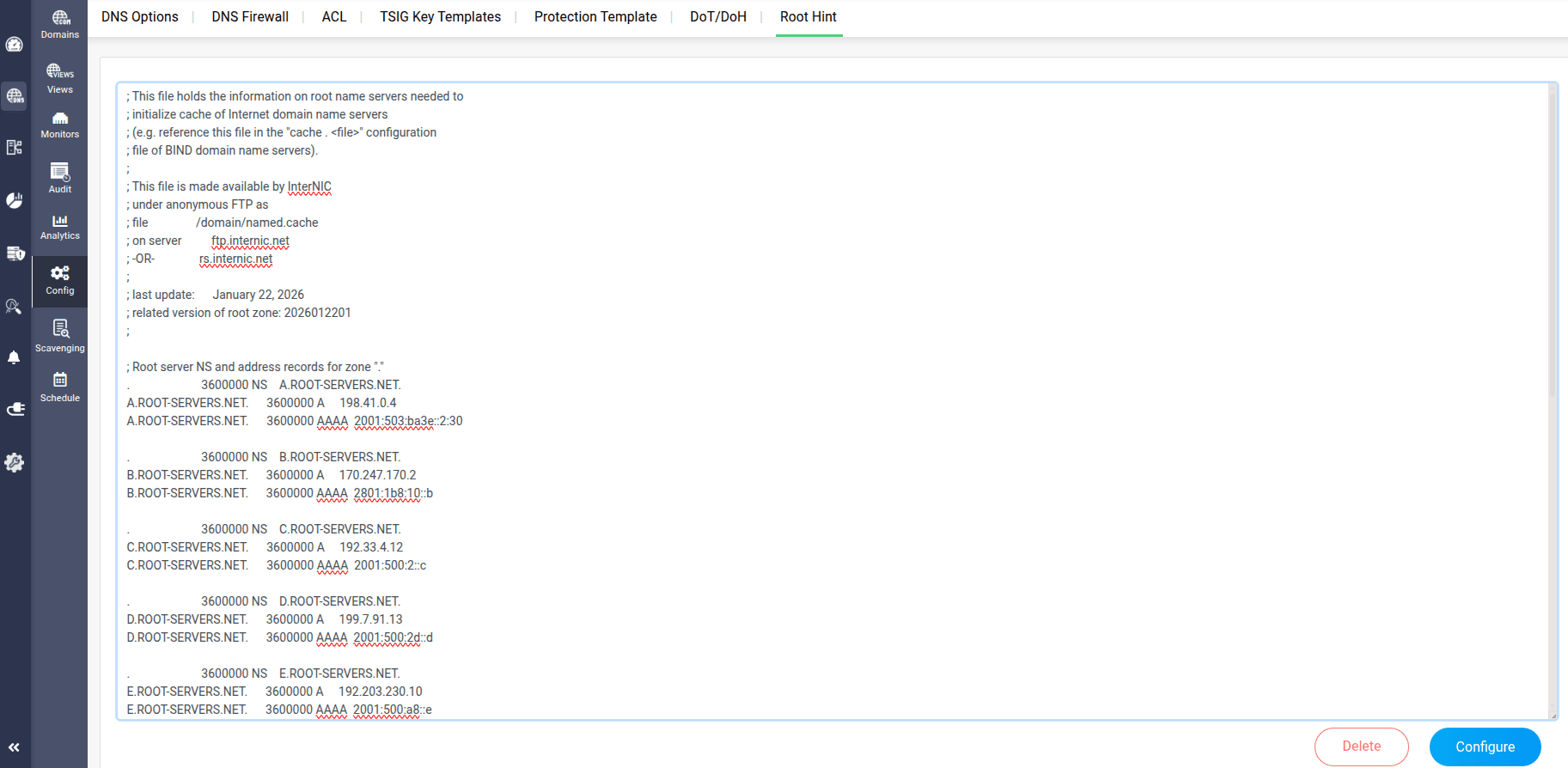
Every DNS resolution chain starts somewhere. For resolvers that don't already know the answer, that starting point is the root: the authoritative source that points queries toward the right top-level domain servers. If your resolver's root hint file is outdated or misconfigured, resolution can fail silently or be directed toward unintended destinations.
DDI Central's Root Hint feature gives admins direct visibility and control over this foundational configuration. The Root Hint template, containing the domain names and IP addresses of all root name servers, can be viewed, edited, and pushed to every DNS server in the organization from a single interface—one click to configure it and organization-wide consistency guaranteed.
It's a small feature with an outsized impact on reliability. Plus, because Root Hint configuration is restricted to users with the Admin role, changes to this foundational setting are always deliberate and authorized.
DNS security is infrastructure security
Every one of these features addresses a real, documented attack vector or operational risk. Together, they form a layered defense that covers the full threat surface of a DNS environment:
ACLs and TSIG lock down who can interact with DNS and verify every server-to-server transaction.
DNSSEC and encrypted transport ensure data integrity and query privacy from end to end.
DNS Firewall keeps users and devices away from known malicious destinations.
RRL and Protection Templates defend against volumetric abuse and enforce a consistent policy at scale.
Root Hint ensures that the entire resolution chain starts from a verified, trusted foundation.
Most organizations treat DNS as plumbing: something that just works, until it doesn't. DDI Central treats it like what it actually is: a critical control plane that deserves the same rigorous security posture as any other part of your network.
When DNS is secure, your entire network is more secure. When DNS fails, or gets compromised, everything built on top of it is at risk.
Ready to see it in action?
Start your free, 30-day trial or request a personalized demo and experience a DNS layer built to withstand the demands of modern enterprise networks.