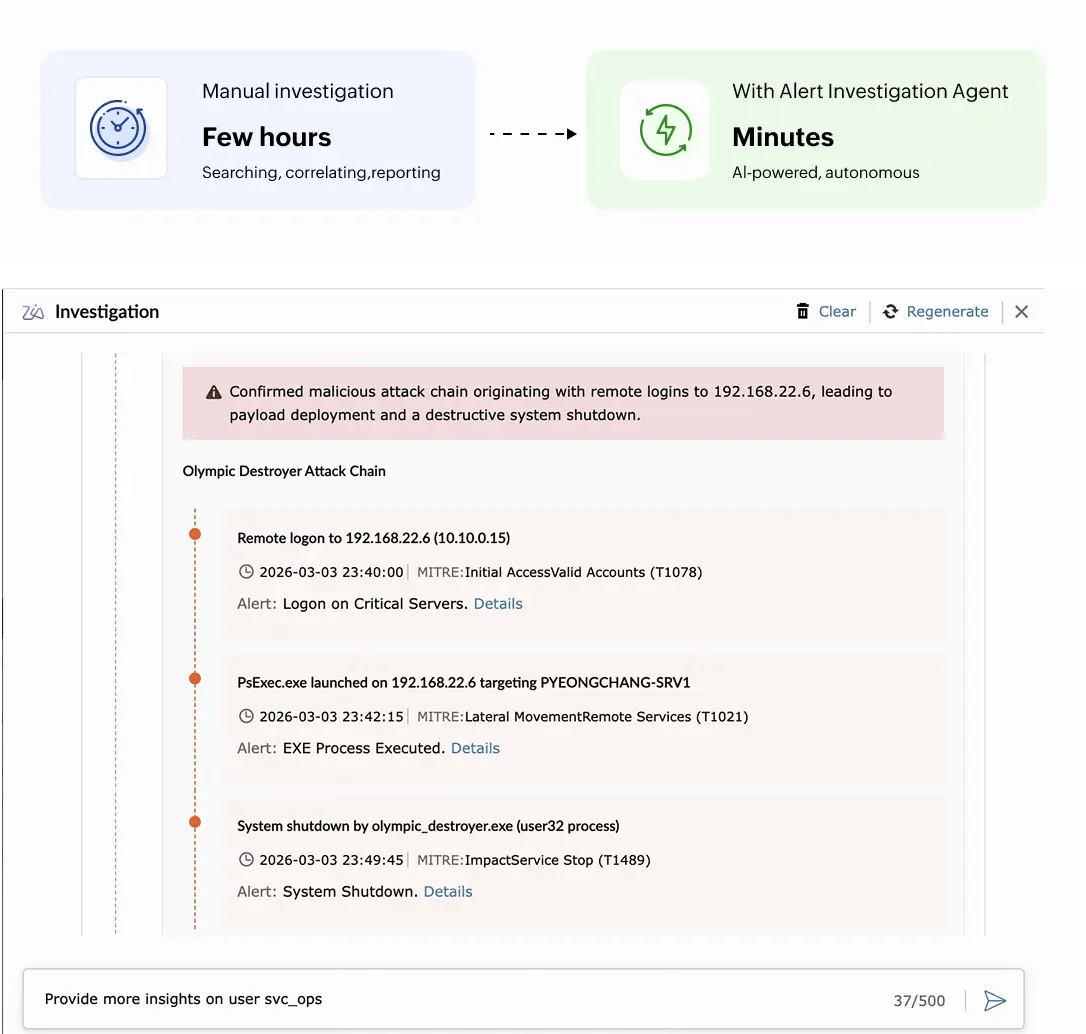
Security analysts sort through hundreds of alerts daily. Each one demands context: Which entities are involved? Are there related alerts? What does the log trail reveal? Manually piecing this together takes time, and most alerts never get a thorough investigation.
Log360 Zia Alert Investigation Agent changes this. It takes your selected alert and runs a full, multi-step investigation automatically. It identifies entities, checks threat intelligence, finds related alerts and logs, and builds a timeline of events. The result is a structured investigation report, complete with MITRE ATT&CK mapping and clear next steps—delivered in minutes instead of hours.
When you initiate the Alert Investigation Agent on any alert, the agent uses LLM-driven reasoning to determine which actions to take based on the alert type and available data. It works through a defined set of investigation steps, with the sequence and depth tailored to each alert.
Zia Insights and the Alert Investigation Agent are designed to work together. When both are enabled, the system generates Insights first, giving you a quick contextual summary of the alert. From there, a single click on Start Investigation launches the full investigation workflow.
| Category | Zia Insights | Alert Investigation Agent |
|---|---|---|
| Purpose | Quick contextual summary of alerts, logs, and incidents | Deep investigation to uncover root cause and the entire attack chain. |
| Data Enrichment | MITRE TTPs mapping | Queries VirusTotal, Advanced Threat Analytics, and UEBA to assess risk for users, IPs, and domains. |
| Depth | Single-event analysis | Digs through related logs, alerts, and threat intelligence sources. |
| Availability | Logs, Alerts, and Incidents | Alerts only. |
| Interaction | Read-only | Interactive: pause, resume, select options, or ask questions in natural language. |
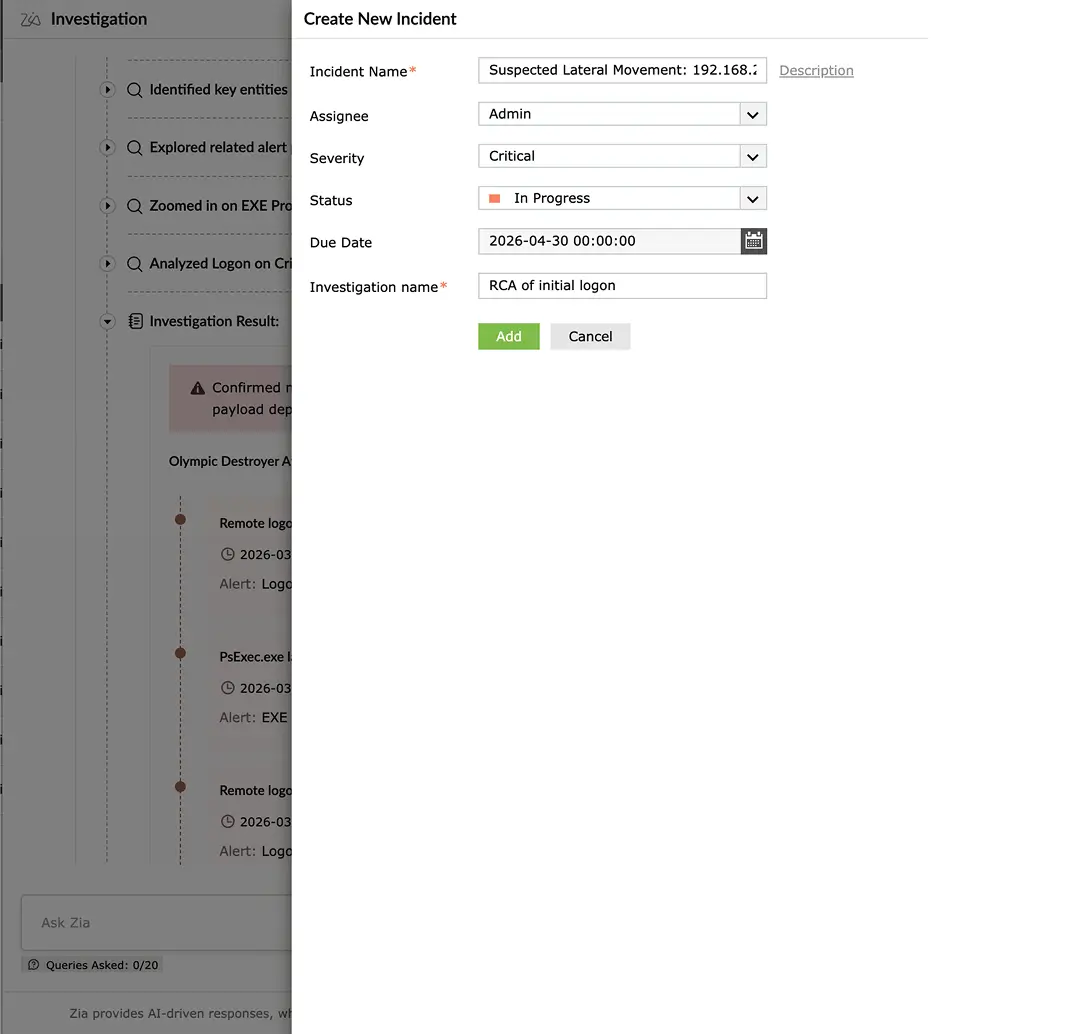
| Output | Summary, MITRE mapping, remediation suggestions | Full investigation report with entity risk, attack timeline, associated alerts and logs, immediate remediation actions, and future risk assessment. Option to export and add the investigation trail to incident. |
Move from manual to AI-driven investigations that surface the full story behind every alert.