CISOs should track certain metrics to gauge the efficiency of their SOC, and to see how effectively they've achieved their goals. Doing so can help them see how the security function has progressed in each of the metrics over time. Metrics will also help CISOs benchmark against industry standards and understand critical areas of improvement.
Let's now look at the 13 metrics that a CISO should track.
Incident rate: The incident rate indicates the number of security incidents that have occurred over a specific time period. CISOs should track incidents that were successfully mitigated and those that weren't. From this, they'll gain insights into how effective their security solution is and how frequently bad actors target their organization.
CISOs should track:
By tracking these on a regular basis, they'll get a fair idea of the number of possible breaches they can expect quarter-to-quarter.
This will undoubtedly help CISOs during budget meetings with the board. When incident rate trends are presented along with the findings of breach likelihood, cost, and risk, the board will understand the extent of threats aimed at their organization. They'll be more inclined to renew or increase their cybersecurity investment following the review of this crucial data.
Breach likelihood: Breach likelihood tells CISOs how likely they are to suffer a breach if the current attack trend continues. While incident rates are metrics measured after the fact, breach likelihood is a metric that denotes the possible number of security incidents that organizations are likely to face, taking into account their risks and the security controls in place.
To that effect, CISOs should consider the total number of incidents (both successful and failed breach attempts), and third-party risk assessment scores. They should also use the insights inferred from their UEBA solution (possessing peer group analysis and seasonality capabilities) to determine the organizational risk and department-wise risk. CISOs can then use predictive modeling and analytics to determine the likelihood of breaches and project how much it would cost the company if the predictions were to come true.
Cost per incident: Data breaches cost organizations their reputation and money. The average cost of a data breach is $4.35 million, according to IBM's Cost of a Data Breach Report 2022. By measuring the cost per incident (sometimes referred to as breach impact), CISOs can determine the true impact of breaches on business, and can compare and identify how much higher or lower their costs are when compared to industry standards.
Risk exposure: Risk exposure is the product of breach likelihood and breach impact.
Risk exposure = Breach likelihood * Breach impact
Tracking this helps CISOs strengthen their organizations' defenses against risks. CISOs can only secure their organization when they know what threats they're exposed to. Measuring risk exposure is a good way to calibrate the source and degree of threats. It also helps CISOs obtain budget approvals from the board to prevent these risks from becoming security incidents.
Severity level of breach: The severity of a breach indicates its magnitude and the level of its devastation. For every security breach, the CISO should track its severity. One way to do this is to use a scale of 1-5 (with "5" being the highest). The measure of breach severity can be qualitative or quantitative, depending upon constraints faced by the CISO. Tracking breach severity shows CISOs the true reflection of their security posture, because an organization with an effective security team and solution will have a minimal number of severe breaches.
Mean time to detect (MTTD): The MTTD tells CISOs how long it has taken their security team to detect a breach. Organizations should aim to minimize the MTTD because the faster the detection, the less time an attacker remains unchallenged in the network, and the quicker the threat mitigation.
Mean time to respond, recover, and resolve (MTTR): MTTR could mean any of the following depending on how an organization chooses to define the term. The CISO should be tracking all of them.
Mean time to patch (MTTP): The MTTP is also referred to as the vulnerability patch response time. This indicates how quickly the security team implements patches to software and applications in devices once they discover vulnerabilities. CISOs should ensure that there's minimal delay between a patch release and its implementation. To accomplish this, they should start by tracking the number of unpatched devices using vulnerability scanners.
Level of security maturity: CISOs need to know how prepared their security team is to defend against cyberattacks. They can test and assess their organization's security maturity with the help of proactive approaches such as pen testing (or ethical hacking), red teaming, and cyberwar gaming. Ethical hackers perform pen testing to identify security vulnerabilities in a system or an application, whereas in red teaming, a dedicated group of individuals, either in-house or outsourced, operate with the explicit permission of C-suite executives to infiltrate the organization.
On the other hand, facilitators (either CISOs or external war game experts), conduct cyberwar games to test and improve the incident response and security preparedness of an organization.
CISOs should determine which approach will best meet their organization's current needs and accommodate their future security requirements. They can then rate themselves as low, medium, or high based on the findings to identify their level of security maturity.
Alternatively, CISOs can use a cybersecurity framework such as the Essential Eight to identify where their organization's security maturity level lies. According to the Essential Eight Maturity Model, organizations can classify themselves into various maturity levels based on the risks posed by cyberattackers likely to attack them, and the techniques or trade craft used by them to carry out an attack. Figure 1 will give CISOs an idea as to how this model helps organizations identify their security maturity level.
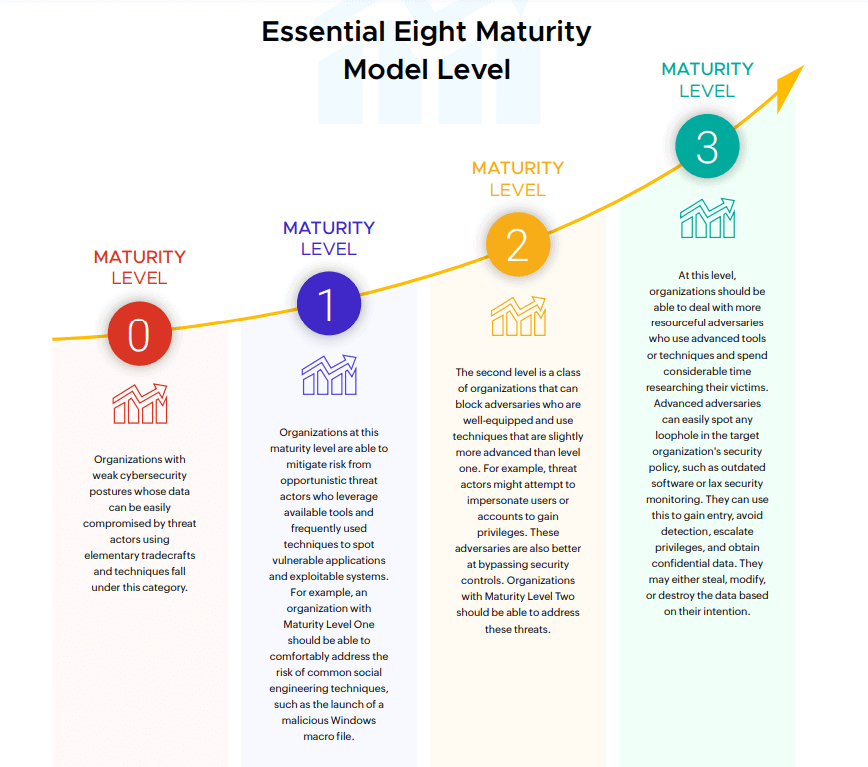 Figure 1: Essential Eight Maturity Model
Figure 1: Essential Eight Maturity Model
Percentage of users not using multi-factor authentication: Threat actors often use compromised credentials to gain entry into a network. Organizations which encourage the use of MFA are less likely to face an attack due to compromised credentials since attackers can no longer gain access with only the password.
CISOs should track users who aren't using MFA, and should ensure that they start adopting MFA as a part of their normal logon routine. This should be reflected when tracking this metric month-to-month. CISOs can look into their Active Directory to identify the MFA status of users.
Percentage of users not using MFA = (Number of users with MFA status as disabled/Total number of users in the organization) * 100
CISOs should work towards bringing down this percentage significantly.
Frequency of backup: In 2022, the average cost of a ransomware attack—not including the cost of the ransom itself—was $4.54 million. Ransomware attacks are terrifying because organizations might still not gain access to their original data as attackers could manipulate the data, or fail to give the decryption key even if organizations pay the ransom. It's imperative for organizations to have backups to verify the authenticity of their data. If a CISO ensures that the security team backs up the data frequently, then they might even get away without having to pay the ransom.
Percentage of watchlisted users: Watchlisted users refers to the riskiest users. For example, employees usually work within a specific timeframe, say, 9am to 6pm. But it is wise to add them as watchlisted users if they demonstrate work-related activity round the clock, or if they indicate increased activity outside their usual work hours. Similarly, it is wise to closely monitor users who are connected to many or key assets. CISOs also should be vigilant in tracking the number of watchlisted users as an unexplained increase indicates a potential insider attack.
Percentage of watchlisted users = (Total number of watchlisted users/Total number of users in the organization) * 100
Tracking this can help CISOs identify if there's a sizable difference in their riskiest users quarter-to-quarter.
Now you know the key metrics that CISOs should track. If you want to learn the criteria to measure the success of a CISO, read this blog. If you wish to learn about the potential cost savings from a SIEM investment, download this white paper.
You will receive regular updates on the latest news on cybersecurity.
© 2021 Zoho Corporation Pvt. Ltd. All rights reserved.