When 16-year-old Koceilah Rekouche, aka Da Chronic, and his friends decided to trick AOL employees into revealing their personal information in 1994, little did they know that this type of attack, later named phishing, would eventually become one of the world's top cybersecurity threats in 2022.
In the summer of 1994, a hacker called Dave Lusby approached Rekouche because he had discovered a way to gain access to the credit card information of AOL users. Both of them invited other hackers to join their ring and started tricking AOL users. Thus began the world's very first phishing attack.
Their modus operandi was straightforward: Rekouche, Lusby, and a few others impersonated AOL employees and began to chat with new users in the New Member Lounge chat rooms. The new, vulnerable AOL subscribers were added automatically to these chat rooms during their first few logins.
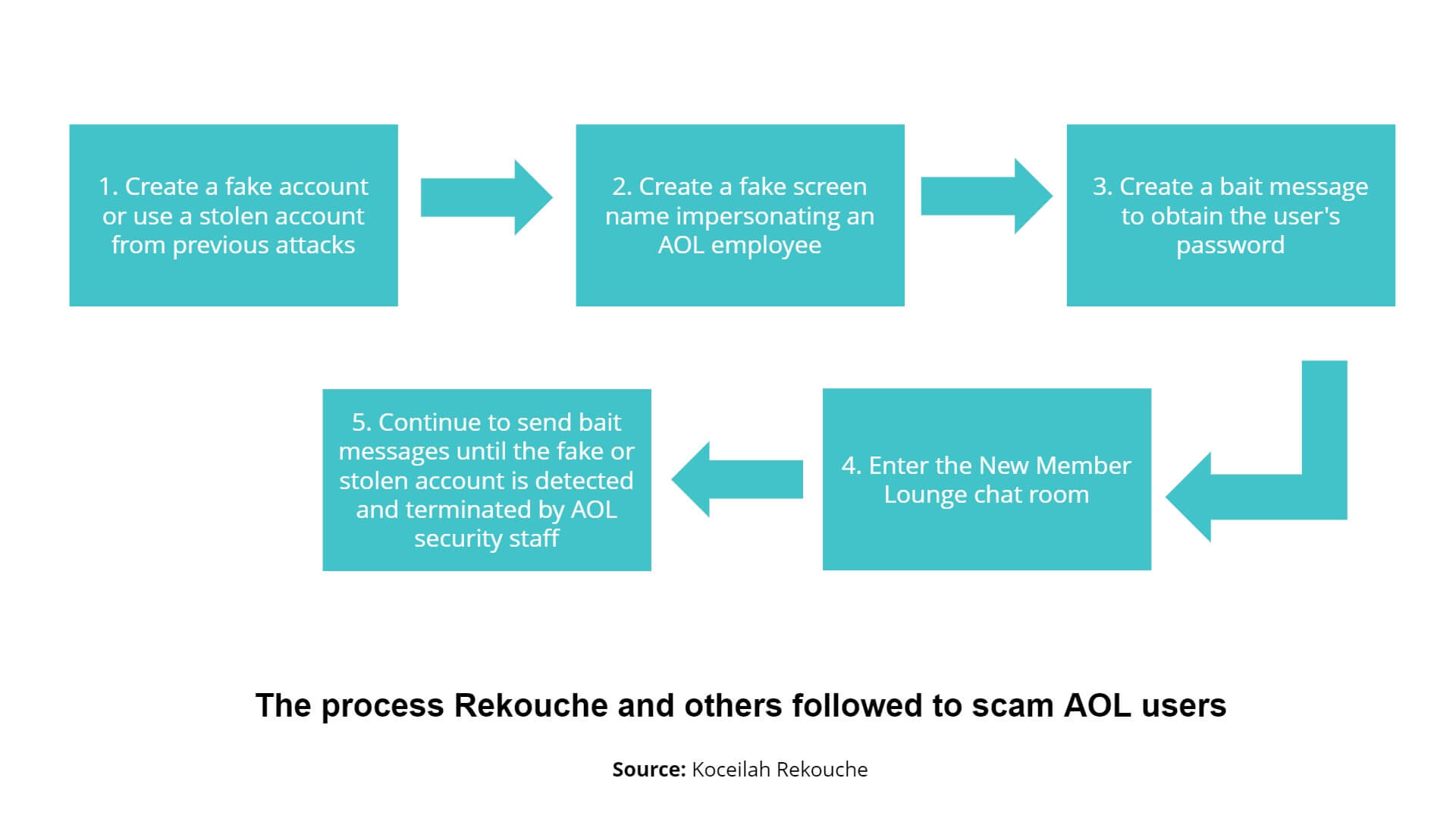
First, the hackers manually texted each of the members of the chat room using fake accounts they'd created with fake credit card information or stolen accounts they had obtained from previous attacks. If the hackers used fake accounts to communicate with other users, their operation was short-lived; AOL would log out and terminate these fake accounts within a few seconds. Stolen accounts were far more valuable since they were legitimate and they were later referred to as "phishes."
The growth of AOL's subscriber base and the hacker community led to an increase in the number of people involved in this "fishing" scheme. Rekouche then began to develop automated software to carry out his hacks, which he called AOHell. The term phishing is believed to have been popularized through this tool.
AOHell was designed to be used by both amateurs and professionals. Once inside a chat room, phishers could choose to capture either passwords or credit card information. AOHell had pre-engineered bait messages phishers could choose from to reach out to members as well as options to create completely new phishing messages. Once the software was released in a chat room, it would create a list of possible users and send the bait message for the chosen function to all of them.
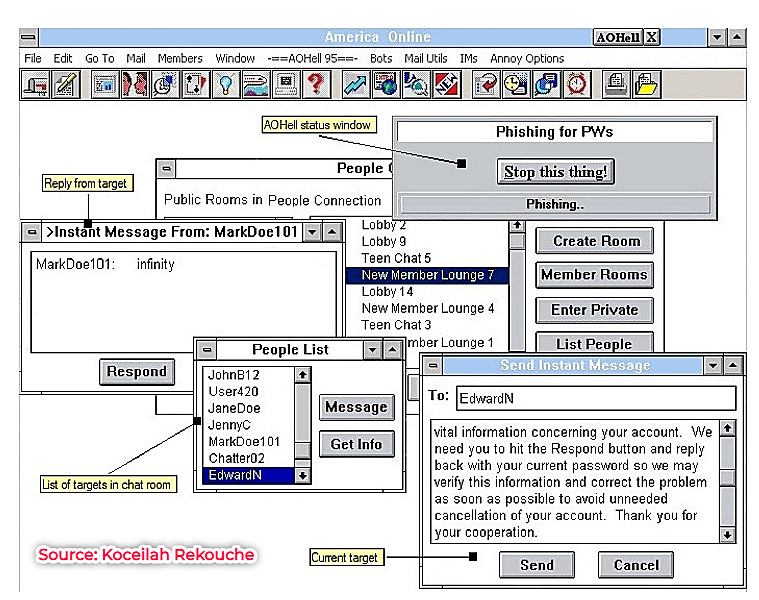
AOHell greatly increased the number of victims the hackers could bait. This process went on for a while, with the hackers remaining undetected because of two major reasons:
Keeping in mind that the attack happened nearly 30 years back, the hackers did not really face a huge risk of being caught by the police or facing repercussions for their actions since they used fake or stolen accounts to log in. Despite being a popular online platform, AOL did not use an automatic billing verification system and was dependent on the diligence of the employees overseeing the authentication process. Due to its lax monitoring system, the hackers were able to phish a lot of credit card information or credentials in one go.
Initially, AOL used external service providers like SprintNet to establish telephone-modem connectivity. SprintNet did not supply AOL with the telephone numbers of the users logging in to its website, which meant AOL could not identify users by their phone numbers. Later, even though AOL got its own modem network called AOLNet, it did not have the ability to obtain phone numbers either.
Rekouche stopped working on the AOHell software by September 1995, but by then several similar applications were being developed to hack into different communities on the internet. By the early 2000s, what had begun as an amateur hacking attempt by a couple of teenagers had led to sophisticated phishing attacks by self-trained cybercriminals.
Phishing, one of today's most common social engineering attacks, has been around for nearly 30 years. Tracing the origin of phishing helps you understand the human intentions and behavior behind this attack type and how attackers developed automated software to carry it out. This development ultimately led to the sophisticated phishing techniques cyberattackers use today.
Phishing occurs when cybercriminals don fake identities to trick targets into revealing personally identifiable information (PII) or confidential data. Usually, the information sought is credit card data or login credentials. The most common medium for waging a phishing attack is email. SMS (smishing), social media platforms, spoofed websites, and most recently voice calls or audio messages (vishing) are also popular media phishers choose.
Over the past few decades since the AOL attack, phishers have evolved extensively. Today, phishing emails and websites are carefully crafted to mimic authentic ones, and much like the RaaS model, attackers have adopted Phishing as a Service (PhaaS) as a business run in underground forums. We will discuss this model in detail in Part 2.
For now, we will explore nine important types of phishing attacks.
Clone phishing: As the name suggests, clone phishing occurs when attackers replicate legitimate emails from trusted organizations and only change the link or attachment so that when users click it, ransomware or malware is installed. These emails are usually sent through a spoofed email address, and often the attack does not stop with simply installing the malware. The attackers go on to extract the contacts of the victim and target them as well.
Spear phishing: This is a more targeted attack where phishers spend time researching their targets to understand where they are from and their close circles and friends. They then pose as a known contact, reach out to the target, and try to trick them into revealing personal and financial information they can use for malicious reasons. The threat vectors used could be emails, messages on social media platforms, SMS, or even phone calls.
Whaling: In whaling attacks, phishers pose as a member of the senior management team in an organization (like the CEO). These attacks target not only employees but also key external parties who normally communicate with higher executives (i.e., the big whales). This attack method involves developing a fake website or email that aims to convince users to perform an action, usually making a payment. Since the email or request seems to have come from a trusted senior official, employees are more likely to go ahead with the action.
Smishing: With the advent of cell phones, the cyber world began to see an increase in smishing, a portmanteau of the words SMS and phishing. The attacker uses text messages as an attack vector, sending the victim a fraudulent link. For example, they could claim to be from a store offering a discount or from a bank. These kinds of attacks have increased in number because, according to Gartner, users are more likely to open and respond to text messages on their phones than emails.
Vishing: Similar to smishing, in a vishing (voice phishing) attack, the cybercriminal calls the target, pretends to be from a legitimate institution, and tries to convince them to reveal personal information. Usually, vishing attacks involve a combination of techniques, including smishing. Since most phone numbers have 10-15 digits depending on the location, criminals use phishing software to generate random numbers and determine their targets.
Pharming: Pharming is a type of phishing attack where criminals redirect targets to fake websites. Users are then asked to provide their login credentials or social security numbers or to carry out a financial transaction. Pharming can happen in two ways: by installing malicious software on a host computer (malware-based pharming) or by modifying the DNS table on a server (DNS cache poisoning). The latter is more difficult to detect and handle since the host computers themselves are not affected.
Angler or social media phishing: This is where attackers reach out to users on social media, pretending to be a friend or a customer service agent. Most angler attacks target the employees of financial institutions.
Man-in-the-middle attacks: A cybercriminal intercepts an interaction between a user and an application in this type of attack. The most common way to do this is through Wi-Fi hotspots; the attacker makes these public, and when users try to connect to them, the attacker infiltrates the connection. Then they decrypt the SSL traffic through HTTPS spoofing or tapping into SSL vulnerabilities.
Search engine phishing: Instead of resorting to phishing emails to redirect users to fake websites, criminals now get them indexed by search engines like Google to list them on the search results pages. These sites are made to look legitimate to persuade targets to visit them.
Both phishing and ransomware have been identified as important cyberthreats to watch out for in 2022. While phishing is used to convince targets to reveal confidential information, ransomware attacks are used to install malware in software systems to gain hold of data, block access, and demand a ransom in exchange.
Of the several ways ransomware attackers try to gain access to systems, phishing is currently their number one choice. The attack begins with the threat actor sending a phishing email containing a malicious link or attachment. When the user clicks it, the attacker gains access to the system and carries out the attack. The victim is usually unaware of the activity until they receive the ransom note.
Putting measures in place to curb and defend against phishing helps nip ransomware attacks in the bud. Part 2 of this "Phishing for information" series will examine the phishing attack techniques criminals resort to and how organizations can defend against them with an effective security management tool.
You will receive regular updates on the latest news on cybersecurity.
© 2021 Zoho Corporation Pvt. Ltd. All rights reserved.