What is Kerberoasting and why it targets every organization
Steal or Forge Kerberos Tickets (T1558) is one of the most impactful credential access techniques because it requires no special privileges and produces offline-crackable material. Any authenticated domain user can request a Kerberos service ticket (TGS) for any account with a Service Principal Name (SPN). The ticket is encrypted with the service account's password hash, meaning the attacker can extract it and crack it offline without generating additional network traffic or authentication failures.
The most common variant, Kerberoasting (T1558.003), targets service accounts that run SQL Server, IIS, Exchange, and similar services. These accounts frequently have weak passwords, excessive privileges, and passwords that have not been changed in years. The CrowdStrike 2025 Global Threat Report identified Kerberoasting as one of the top five post-compromise techniques observed globally.
Groups like FIN7 and Scattered Spider use Kerberoasting routinely after gaining initial access. The technique is dangerous precisely because it is quiet: the TGS request is a normal Kerberos operation that blends with legitimate traffic. Detection requires monitoring encryption type downgrades (RC4 instead of AES), unusual request volumes, and known tool signatures.
Key insight: Kerberoasting does not trigger authentication failures or account lockouts. The service ticket request is technically valid. This makes it invisible to traditional brute force detection rules and is why dedicated Kerberos monitoring rules in Log360 are essential.
Kerberos ticket attacks at a glance: Impact, scope, and risk
| Attribute | Detail |
|---|---|
| MITRE ID | T1558 |
| Tactic | Credential Access (TA0006) |
| Severity | High |
| Affected Platforms | Windows, Active Directory |
| Common Tools | Rubeus, Impacket GetUserSPNs, PowerView, setspn.exe |
| Detection Difficulty | Moderate (tool detection easy; pure protocol abuse harder) |
| Log360 Coverage | 6 built-in correlation rules |
| Key Log Sources | Windows Security Events (4769, 4688), Kerberos Ticket Logs |
| Sub-techniques | T1558.003 (Kerberoasting), T1558.001 (Golden Ticket), T1558.002 (Silver Ticket) |
How Kerberoasting works: SPN enumeration to offline cracking walkthrough
A typical Kerberoasting attack unfolds in four stages.
Stage 1 - SPN Enumeration
The attacker, using any domain user account, enumerates all accounts with Service Principal Names. They run setspn -T domain -Q */* or use PowerView's Get-DomainSPNTicket to identify service accounts. This is a legitimate LDAP query that does not require elevated privileges and blends with normal directory lookups.
What this looks like in logs
Process: C:\Windows\System32\setspn.exe
Arguments: -T contoso.local -Q */*
Account: regular_user
(A standard domain user running SPN queries targets all services)
Stage 2 - TGS Ticket Request and Extraction
For each service account discovered, the attacker requests a Kerberos TGS ticket using tools like Rubeus (Rubeus.exe kerberoast) or Impacket's GetUserSPNs. Critically, the attacker forces RC4 encryption (0x17) in the request because RC4-encrypted tickets are dramatically faster to crack than AES-encrypted tickets. The domain controller honors this request because RC4 is still enabled in most environments for backward compatibility.
What this looks like in logs
Account: regular_user
Service Name: MSSQLSvc/sqlserver01.contoso.local:1433
Ticket Encryption Type: 0x17 (RC4-HMAC)
Client Address: 10.0.30.55
(Same account requesting tickets for 15+ services in 30 seconds)
Stage 3 - Offline Password Cracking
The attacker exports the encrypted tickets and runs Hashcat or John the Ripper offline. With modern GPU hardware, RC4-encrypted Kerberos tickets can be cracked at billions of attempts per second. A 10-character password falls in minutes. This stage happens entirely outside the target network, generating zero additional logs or alerts.
Stage 4 - Service Account Abuse
With the cracked service account password, the attacker authenticates as the service account and accesses everything the account can reach. SQL Server service accounts often have database admin rights. IIS service accounts may have access to file shares with sensitive data. If the service account has domain admin privileges (a common misconfiguration), the attacker achieves full domain compromise.
Real-world attack: FIN7 kerberoasting campaign (2024)
FIN7, a financially motivated threat group, used Kerberoasting extensively in attacks against retail and hospitality organizations throughout 2024. After gaining initial access through phishing, FIN7 operators deployed Rubeus to enumerate SPNs and extract TGS tickets for service accounts across the compromised domains.
In one documented incident, FIN7 identified a SQL Server service account with domain admin privileges and a password that had not been changed in over three years. The RC4-encrypted ticket was cracked offline in approximately 40 minutes. With domain admin access, the group deployed ransomware across the organization's entire infrastructure. The Mandiant M-Trends 2025 report highlighted this as a representative example of how Kerberoasting enables rapid escalation from low-privilege access to full domain compromise.
The attack could have been detected at multiple points, including the SPN enumeration, the burst of RC4 TGS requests, and the subsequent logon using the service account from an unexpected source. Log360's Kerberoasting detection rules would have flagged each of these indicators.
ManageEngine Log360 for Kerberos Attack Detection
Detect Kerberoasting, SPN enumeration, and ticket forging with 6 prebuilt rules. Protect your service accounts.
How to detect and investigate Kerberos ticket attacks with Log360
Log360 delivers detection for the full Kerberoasting lifecycle through its real-time correlation engine and Active Directory audit integration. The detection strategy covers three attack stages: SPN reconnaissance, ticket extraction, and post-exploitation.
Real-Time Detection
Detecting SPN enumeration
Kerberoasting begins with SPN enumeration, and Log360 catches this reconnaissance phase immediately. The Potential SPN Enumeration Via Setspn.EXE rule (Trouble, Windows) fires when process creation logs show setspn.exe executed with query parameters that enumerate all SPNs in the domain. While setspn.exe has legitimate administrative uses, running it with wildcard queries from a non-admin workstation is a strong indicator of Kerberoasting preparation.
Detecting Kerberoasting ticket requests
The core detection for Kerberoasting occurs at the ticket request stage. Log360's Kerberoasting Activity. Initial Query rule (Trouble, AD) detects the characteristic pattern of rapid TGS requests from a single account targeting multiple service accounts, especially when the requests specify RC4 encryption (type 0x17). This pattern is almost never seen in normal operations, where a user requests tickets only for the specific services they need to access.
Log360 also detects PowerShell-based Kerberoasting through the Request A Single Ticket via PowerShell rule (Trouble, AD), which fires when PowerShell cmdlets like Add-Type -AssemblyName System.IdentityModel and New-Object System.IdentityModel.Tokens.KerberosRequestorSecurityToken are used to request TGS tickets programmatically.
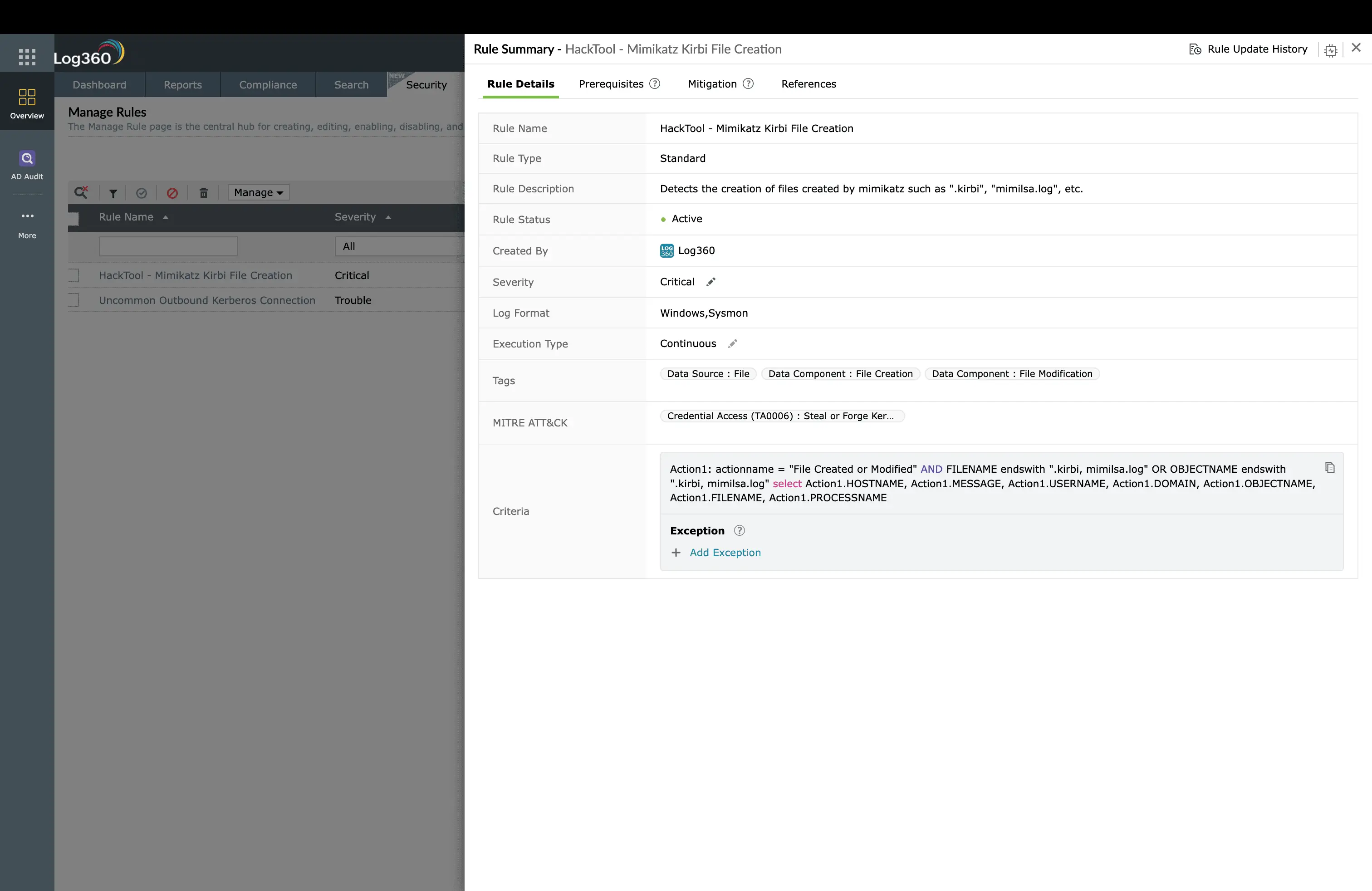
Detecting Rubeus and KrbRelayUp
The Rubeus detection rule (Critical, Windows) identifies the Rubeus toolkit by process name and command-line signatures. Rubeus is the most common Kerberos attack tool in active intrusions, supporting Kerberoasting, AS-REP roasting, ticket manipulation, and Kerberos relay attacks. The HackTool. KrbRelayUp Execution rule (Trouble, Windows) targets a newer attack variant that combines Kerberos relay with local privilege escalation.
For Kerberos traffic anomalies, the Uncommon Outbound Kerberos Connection rule (Trouble, Windows) flags Kerberos traffic directed to unexpected destinations, which may indicate ticket exfiltration or the use of external cracking services.
Behavioral Detection with UEBA
Log360's UEBA module builds baselines for each account's Kerberos activity, tracking which services each account normally requests tickets for, the typical request frequency, and the encryption types used. When an account that normally requests 2-3 TGS tickets per day suddenly requests tickets for 20 different service accounts within minutes, all with RC4 encryption, the UEBA anomaly score spikes and generates an alert.
Investigation workflow in Log360
- Identify targeted service accounts: Review the 4769 events to determine which service accounts had tickets requested. Prioritize investigation of service accounts with elevated privileges (domain admin, database admin).
- Check encryption type: RC4 (0x17) encryption in TGS requests is the strongest Kerberoasting indicator. If all requests use AES (0x12), it may be legitimate activity.
- Verify the requesting account: Verify whether the requesting user normally accesses these services by reviewing their UEBA historical baseline in Log360.
- Look for post-exploitation: Search for logon events (4624) using the targeted service accounts from unexpected sources. If a service account authenticates from a workstation instead of its designated server, it has likely been compromised.
- Check for follow-on attacks: Kerberoasting often precedes credential dumping (T1003) and lateral movement (TA0008). Cross-reference with alerts from those techniques.
Coverage gaps and custom rules
- RC4 TGS Request Anomaly: Flag any TGS request using encryption type 0x17 (RC4) in environments where AES-only Kerberos has been enforced. Any RC4 request after the policy change indicates either a misconfiguration or an active Kerberoasting attempt.
- Service Account Authentication from Unexpected Source: Alert when a service account authenticates from a host other than its designated server, indicating the password was compromised and is being used by an attacker.
How to remediate and prevent Kerberos ticket attacks
Immediate containment
- Rotate targeted service account passwords: Any service account whose TGS ticket was requested during the Kerberoasting attack must have its password changed immediately, using a 25+ character randomly generated password.
- Disable the requesting account: If the account that performed the Kerberoasting is not a known admin performing a legitimate audit, disable it through Log360's automated response.
- Check for compromised service accounts: Search for logon events using the targeted service accounts from unexpected source hosts or IP addresses.
Root cause remediation
- Enforce AES-only Kerberos: Disable RC4 encryption across the domain (CIS Benchmark recommendation). This forces the domain controller to issue AES-encrypted tickets, which are orders of magnitude harder to crack.
- Migrate to Group Managed Service Accounts (gMSAs): gMSAs use automatically rotated, 240-character passwords managed by Active Directory. They eliminate the weak-password risk entirely.
- Audit and reduce SPN-enabled accounts: Review all accounts with SPNs. Remove SPNs from accounts that no longer need them. Reduce the privileges of remaining service accounts to the minimum required.
Long-term hardening
- Tiered service account model: Classify service accounts by privilege level and apply appropriate password length, rotation, and monitoring requirements to each tier.
- Monitor for AS-REP roasting: A related technique (T1558.004) targets accounts with Kerberos pre-authentication disabled. Audit all accounts and ensure pre-authentication is enabled.
- Regular Kerberos health checks: Schedule quarterly reviews of SPN assignments, encryption types in use, and service account password ages.
Log360 automated response configuration
- Disable requesting account: Enable for Rubeus detection and Kerberoasting Activity rules
- Force service account password reset: Trigger for any Critical-severity Kerberos rule
- Create ServiceDesk Plus ticket. Auto-create incident with full Kerberos event details
- Email/SMS notification: Alert the identity management team when Kerberoasting is detected
Need to explore ManageEngine Log360? Schedule a personalized demo
Kerberos ticket attacks: Frequently Asked Questions
What is Kerberoasting in MITRE ATT&CK?
Kerberoasting is a sub-technique (T1558.003) where an attacker requests Kerberos service tickets for accounts with Service Principal Names (SPNs) and then cracks them offline to recover the service account password. It is effective because any authenticated domain user can request these tickets, and service accounts often have weak, rarely-rotated passwords. See the full credential access guide.
How does Log360 detect Kerberoasting?
Log360 detects Kerberoasting through 6 prebuilt correlation rules covering the full attack lifecycle: SPN enumeration via setspn.exe, initial Kerberos TGS request patterns, Rubeus execution, PowerShell-based ticket requests, KrbRelayUp attacks, and unusual outbound Kerberos connections. UEBA behavioral baselines flag accounts requesting tickets for services they have never accessed.
What Windows Event IDs indicate Kerberoasting?
Event ID 4769 (Kerberos Service Ticket Request) is the primary indicator. Look for bursts of TGS requests from a single account targeting multiple service accounts, especially with RC4 encryption type (0x17) instead of AES (0x12). Event ID 4688 shows Rubeus, setspn.exe, or PowerShell execution related to the attack. Forward all Kerberos events to Log360.
How do I prevent Kerberoasting attacks?
Use Group Managed Service Accounts (gMSAs) with automatically rotated, complex passwords. Enforce AES-only Kerberos encryption by disabling RC4. Limit SPN-enabled accounts to only those that genuinely require them. Set service account passwords to 25+ characters. Monitor with Log360 UEBA for unusual TGS request patterns.
What is the difference between Kerberoasting and Golden Ticket attacks?
Kerberoasting steals service account passwords by cracking TGS tickets offline. Golden Ticket attacks use a stolen KRBTGT hash to forge unlimited TGT tickets granting access to anything in the domain. Kerberoasting requires only a standard domain user account; Golden Tickets require the KRBTGT hash, typically obtained through DCSync (T1003.006). Kerberoasting is the entry point; Golden Tickets are the endgame.
- What is Kerberoasting?
- Impact, Scope, and Risk
- How Kerberoasting works
- Use cases
- Detect and investigate with Log360
- Remediation and prevention
- Frequently Asked Questions



