What is credential access in MITRE ATT&CK?
Credential access is a tactic in the MITRE ATT&CK framework (TA0006) that describes the techniques adversaries use to steal account credentials such as passwords, password hashes, authentication tokens, and Kerberos tickets. Stolen credentials let attackers impersonate legitimate users, escalate privileges, and traverse the network without triggering the kind of alerts that malware execution or exploit-based lateral movement would. This is why credential access is arguably the most dangerous post-compromise tactic in the entire ATT&CK matrix.
The 2025 Verizon Data Breach Investigations Report found that stolen credentials were involved in 44.7% of all confirmed breaches, more than any other attack action. IBM's 2024 Cost of a Data Breach Report reported that breaches caused by stolen or compromised credentials took an average of 292 days to identify and contain, the longest lifecycle of any initial attack vector. The reason is simple: when attackers use valid credentials, they look like authorized users, and traditional perimeter-based defenses cannot distinguish them from legitimate activity.
Credential access is the bridge between initial access (TA0001) and the attacker's ultimate objectives. An adversary who gains a single low-privilege foothold can dump credentials from memory, crack password hashes offline, forge Kerberos tickets, or relay NTLM authentication to escalate to domain administrator privileges (TA0004), often within hours. Groups like FIN7, APT29 (Cozy Bear), and Scattered Spider routinely chain credential access techniques to achieve full Active Directory compromise before the security team detects the initial breach.
Key insight: Credential access is the tactic where attacker dwell time compounds. Each stolen credential unlocks new systems, which yield more credentials, which unlock more systems. A single undetected Mimikatz execution on a domain-joined workstation can cascade into full domain compromise within 24 hours. Investing in credential access detection breaks this escalation chain at its most vulnerable point.
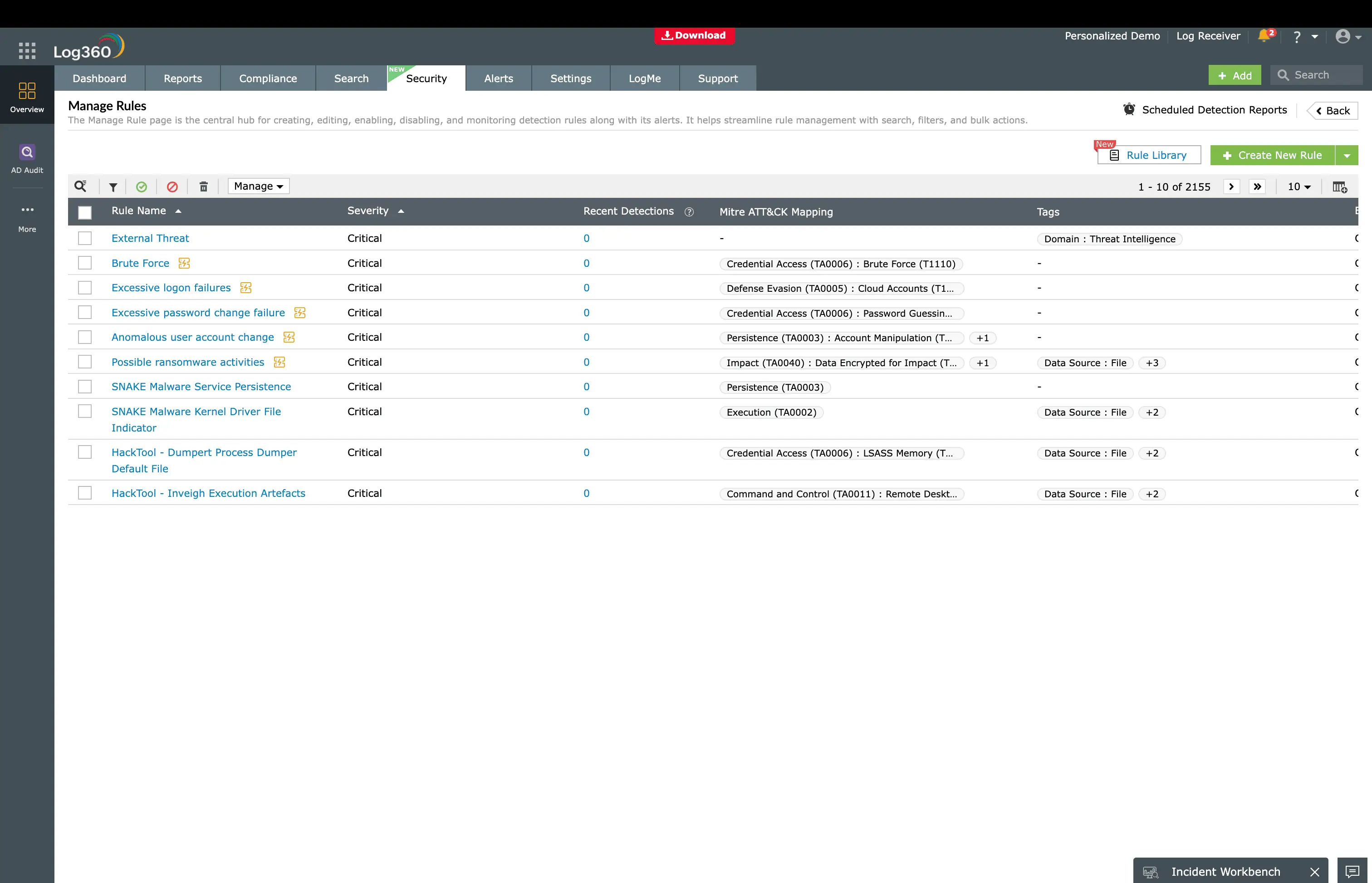
This guide covers the credential access techniques that matter most for detection: OS Credential Dumping, Brute Force, Steal or Forge Kerberos Tickets, and Adversary-in-the-Middle, maps each to specific SIEM detection rules, walks through real-world attack scenarios from 2024-2025 incidents, and shows how to build a comprehensive detection and response strategy using ManageEngine Log360 and its 219 prebuilt detection rules for credential access.
Why credential access is critical to detect early
Credential access sits at a pivotal point in the attack lifecycle. Before credential access, the attacker may only control a single compromised endpoint with limited privileges. After successful credential access, the attacker can:
- Move laterally across the entire network: Stolen domain credentials grant access to file servers, databases, other workstations, and domain controllers. This enables lateral movement (TA0008) at scale without exploiting any vulnerability.
- Escalate to domain administrator: Techniques like DCSync and Kerberoasting can extract domain admin credentials or forge tickets that grant domain admin access, achieving privilege escalation (TA0004).
- Persist indefinitely: Golden Tickets forged with the KRBTGT hash grant access for as long as the ticket is valid (default 10 hours, but attackers set them for years). Even a full password reset across the organization won't revoke a Golden Ticket. Only a KRBTGT password rotation will.
- Exfiltrate data silently: With legitimate credentials, attackers can access sensitive data, databases, and cloud services as if they were authorized, making exfiltration indistinguishable from normal business activity.
The credential access attack chain
Understanding how credential access fits within a broader attack is essential for building detection depth. Here is the typical progression:
| Stage | ATT&CK tactic | What happens | Credential access role |
|---|---|---|---|
| 1 | Initial Access (TA0001) | Attacker gains entry via phishing, exploitation, or stolen credentials | May use previously stolen credentials to enter |
| 2 | Execution (TA0002) | Attacker runs code on the compromised system | Loads credential theft tools (Mimikatz, Rubeus) |
| 3 | Credential Access (TA0006) | Attacker harvests credentials from memory, AD, or network protocols | Core credential theft occurs here |
| 4 | Privilege Escalation (TA0004) | Attacker uses stolen credentials to gain higher access | Stolen admin hashes enable privilege escalation |
| 5 | Lateral Movement (TA0008) | Attacker moves to other systems | Uses stolen credentials for pass-the-hash, RDP, SMB |
| 6 | Impact (TA0040) | Ransomware deployment, data exfiltration | Domain admin credentials enable environment-wide impact |
CrowdStrike's 2025 Global Threat Report noted that the average breakout time, from initial compromise to lateral movement, is now 62 minutes. Credential access is almost always the enabler of this rapid progression. Attack groups like Scattered Spider have achieved full Active Directory takeover in under 4 hours using credential access techniques alone, without deploying any traditional malware.
Note: Credential access detection is not just about catching the credential theft itself. It's about building a detection envelope that covers the entire chain, from the tool execution (Mimikatz, Rubeus, Hashcat) to the behavioral anomaly (unusual Kerberos requests, LSASS access) to the downstream impact (pass-the-hash logons, Golden Ticket usage). Log360 provides detection rules at every layer of this chain.
Credential access techniques in MITRE ATT&CK
MITRE ATT&CK catalogs 17 techniques under credential access. Four of these account for the vast majority of real-world credential theft incidents and represent the strongest detection opportunities for SIEM-based monitoring. Log360 provides 30 targeted detection rules across these four high-impact techniques, plus 189 additional rules for broader credential anomaly detection.
| Technique ID | Technique name | What it targets | Log360 rules | Real-world prevalence |
|---|---|---|---|---|
| T1003 | OS Credential Dumping | LSASS memory, SAM hive, NTDS.dit, LSA secrets, DCSync | 16 | Present in 80%+ of ransomware incidents (Mandiant) |
| T1110 | Brute Force | Password guessing, password spraying, credential stuffing | 5 | Top cloud attack vector per Microsoft Digital Defense Report |
| T1558 | Steal or Forge Kerberos Tickets | Service account passwords via Kerberoasting, TGTs via Golden Tickets | 6 | Used by APT29, FIN7, Wizard Spider (Mandiant, CrowdStrike) |
| T1557 | Adversary-in-the-Middle | NTLM relay, PetitPotam coercion, AD CS abuse | 3 | PetitPotam remains a top Active Directory attack vector |
Understanding the credential landscape
To detect credential access effectively, security teams need to understand what attackers are targeting and where credentials live in the environment:
Credentials in memory (LSASS)
Windows stores plaintext passwords, NTLM hashes, and Kerberos tickets in the LSASS process memory. Tools like Mimikatz extract these directly. This is the most common credential theft target because it requires only local admin privileges and yields immediately usable credentials.
Credentials in Active Directory (NTDS.dit)
The AD database (NTDS.dit) contains password hashes for every domain account. Attackers extract it via volume shadow copies, Ntdsutil, or DCSync replication requests. A single NTDS.dit file compromises every account in the domain.
Credentials in network protocols (Kerberos, NTLM)
Kerberos tickets and NTLM challenge-response exchanges traverse the network. Kerberoasting extracts service account tickets for offline cracking. NTLM relay forwards authentication to other services. Both exploit protocol design, not vulnerabilities.
Credentials in configuration (SAM, LSA, registry)
The SAM database stores local account hashes. LSA secrets in the registry contain service account passwords and VPN credentials. These are lower-value targets than LSASS or NTDS.dit but still enable lateral movement to other systems.
ManageEngine Log360 for credential access detection
Log360 ships with 219 prebuilt detection rules mapped to MITRE ATT&CK Credential Access (TA0006). Detect Mimikatz, DCSync, Kerberoasting, brute-force attacks, and NTLM relay across Windows endpoints and Active Directory, with real-time alerts, UEBA behavioral analytics, and automated response.
How credential access attacks work: Real-world scenarios
These scenarios are drawn from publicly reported incidents in 2024-2025. Each illustrates how credential access techniques chain together in real attacks, and exactly where Log360's detection rules trigger to break the chain.
Scenario 1 - Mimikatz to Domain Admin in 3 hours (T1003)
Attack workflow
The attack
A threat actor gained initial access to a healthcare organization through a phishing email that delivered a malicious macro. Once the macro executed a PowerShell download cradle, the attacker established a Cobalt Strike beacon on the compromised workstation. Within 20 minutes, they executed Mimikatz with sekurlsa::logonpasswords to dump all credentials from LSASS memory, harvesting the NTLM hashes and plaintext passwords of three recently logged-in users, including an IT administrator.
Using the IT admin's NTLM hash in a pass-the-hash attack, the attacker moved laterally to a domain controller. There, they executed DCSync, a Mimikatz feature that mimics domain controller replication traffic to request the password hash for any domain account, including the KRBTGT service account. With the KRBTGT hash, the attacker could forge Golden Tickets granting unlimited domain access.
What it looks like in logs
- Windows Event ID 4688: Process creation showing mimikatz.exe (or renamed binary with known command-line arguments like sekurlsa, lsadump, kerberos::golden).
- Windows Event ID 4656/4663: Object access audit showing a non-LSASS process requesting read access to lsass.exe, the signature of credential dumping.
- Windows Event ID 4624 (Type 9): NewCredentials logon type, created when pass-the-hash is used. The logon ID will differ from the user's interactive session.
- AD Replication Event (Event ID 4662): DCSync generates AD replication requests from a non-domain-controller machine account, specifically requesting the DS-Replication-Get-Changes-All extended right.
How Log360 detects this
Log360 provides multi-layer detection for this scenario:
- Mimikatz Detection (Critical): Catches known Mimikatz process names and command-line patterns at the moment of execution.
- LSASS Dump Keyword In CommandLine (Trouble): Detects obfuscated or renamed Mimikatz variants that still reference LSASS in their arguments.
- Active Directory Replication from Non Machine Account (Critical): Fires when a DCSync request originates from a non-domain-controller source, catching the credential harvesting at the AD level.
- Mimikatz DC Sync (Trouble): Specifically targets the DCSync technique using Mimikatz's lsadump::dcsync command pattern.
Even if the attacker renames Mimikatz and obfuscates command-line arguments, Log360's UEBA module detects the behavioral anomaly: a workstation initiating AD replication traffic is never normal behavior, regardless of the tool used.
Scenario 2 - Kerberoasting a Service Account (T1558)
Attack workflow
The attack
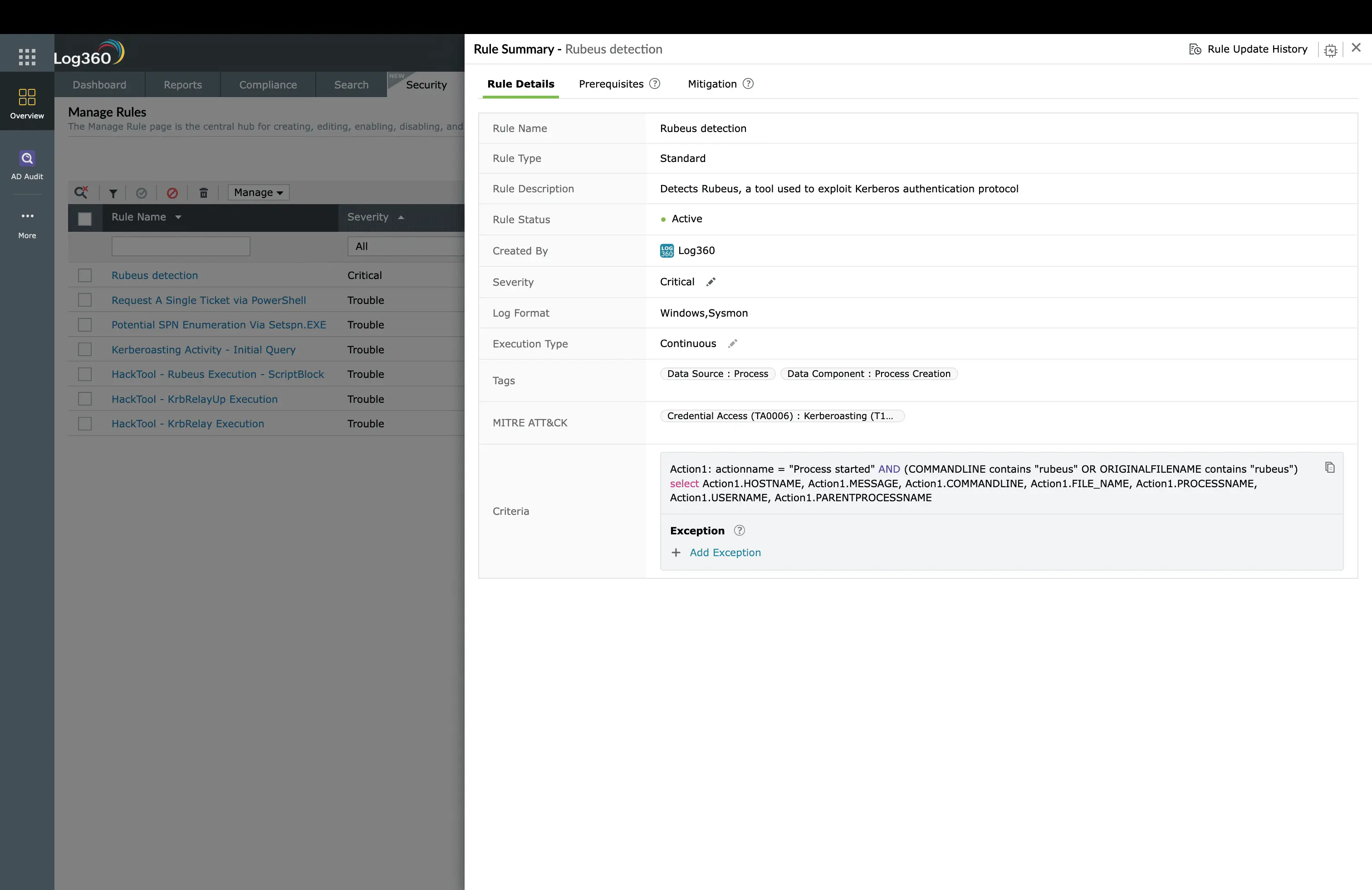
A member of the FIN7 threat group, having compromised a financial services organization, used Rubeus (a C# Kerberos abuse toolkit) to perform a Kerberoasting attack. The attacker first enumerated all accounts with Service Principal Names (SPNs) using setspn -T domain -Q */*, identifying 23 service accounts, including one used by a SQL Server instance running with domain admin privileges.
The attacker then requested Kerberos TGS (Ticket Granting Service) tickets for each SPN-enabled account. Because Kerberos TGS tickets are encrypted with the target service account's password hash, the attacker exported these tickets and cracked them offline using Hashcat with a GPU cluster. The SQL Server service account, which had a 12-character password that hadn't been rotated in 3 years, was cracked in under 8 hours.
What it looks like in logs
- Windows Event ID 4688: setspn.exe executed with enumeration parameters, followed by Rubeus execution.
- Windows Event ID 4769: A burst of Kerberos TGS requests from a single workstation for multiple different service accounts, especially with RC4 encryption (0x17), a strong Kerberoasting indicator since modern environments should use AES.
- Windows Event ID 4688 (on attacker's system): Hashcat execution with Kerberos cracking modules.
How Log360 detects this
- Potential SPN Enumeration Via Setspn.EXE (Trouble): Catches the reconnaissance phase when the attacker inventories service accounts.
- Kerberoasting Activity. Initial Query (Trouble): Detects the characteristic pattern of rapid TGS requests for multiple services, especially with RC4 encryption downgrade.
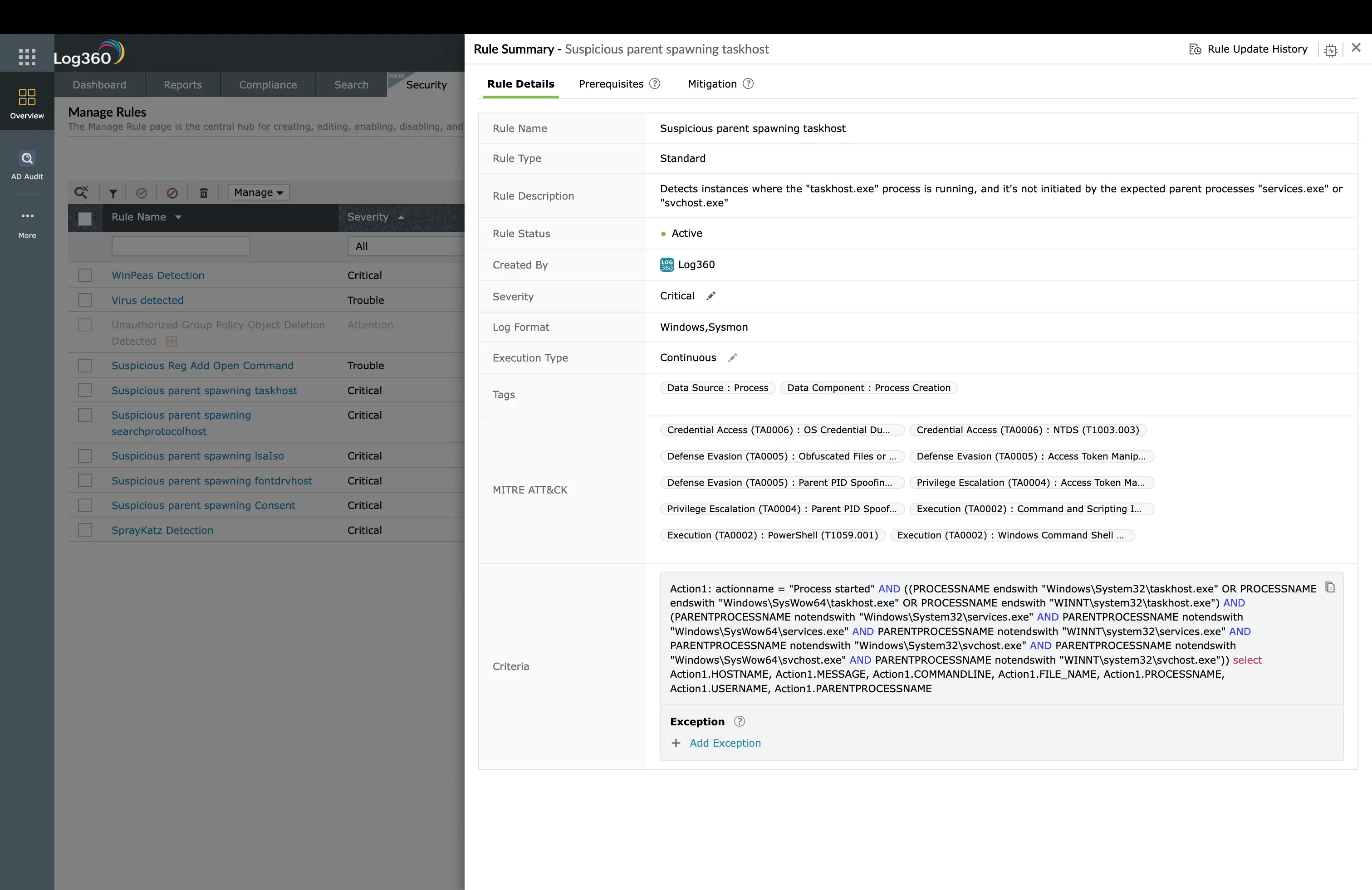
- Rubeus detection (Critical): Identifies Rubeus execution by process name and command-line signatures.
- Hashcat detection (Critical): Catches the offline cracking phase if the attacker runs Hashcat within the environment.
Scenario 3 - PetitPotam NTLM Relay to AD CS (T1557)
Attack workflow
The attack
An attacker exploited the PetitPotam vulnerability to coerce a domain controller into authenticating to a machine under the attacker's control via NTLM. The attacker relayed this NTLM authentication to the organization's Active Directory Certificate Services (AD CS) enrollment endpoint, requesting a certificate on behalf of the domain controller. With this certificate, the attacker could impersonate the domain controller to request a TGT for any account, achieving full domain compromise without ever cracking a password. This attack chain, first disclosed by security researcher Gilles Lionel (topotam), remains one of the most potent Active Directory attack paths.
What it looks like in logs
- Windows Event ID 4688: Execution of PetitPotam exploit tool or equivalent EfsRpcOpenFileRaw calls.
- Windows Event (Printer Spooler): Suspicious NTLM authentication requests originating from or targeting the print spooler service on domain controllers.
- AD CS Audit Logs: Certificate enrollment requests from unexpected sources, a domain controller requesting a certificate via a non-standard enrollment agent.
How Log360 detects this
- Petitpotam detection (Critical): Catches PetitPotam exploit execution based on process behavior and known tool signatures.
- Suspicious NTLM Authentication on the Printer Spooler Service (Trouble): Detects the NTLM coercion pattern targeting the print spooler, which is the classic PetitPotam relay path.
- HackTool. ADCSPwn Execution (Trouble): Specifically catches the AD CS exploitation phase where the relayed authentication is used to request a certificate.
Detection depth: PetitPotam illustrates why credential access detection cannot rely on a single rule. Log360's correlation engine links the PetitPotam coercion event, the NTLM relay, and the suspicious certificate enrollment into a single incident timeline, giving SOC analysts the full attack narrative in one view rather than three disconnected alerts.
Detecting credential access by log source
Credential access attacks primarily target Windows endpoints and Active Directory infrastructure. Unlike initial access, which spans cloud and network logs, credential access detection concentrates on four key log sources, each requiring specific audit policies to be effective.
Windows Security Event Logs
Windows generates the majority of credential access signals. Critical Event IDs include:
- Event ID 4688: Process creation. Catches known credential theft tools (Mimikatz, Rubeus, Hashcat, Hydra, Kerbrute) and suspicious command-line patterns.
- Event ID 4656/4663: Object access. Detects LSASS memory access by unauthorized processes, the core indicator of credential dumping.
- Event ID 4624/4625: Logon success/failure, reveals brute-force patterns, pass-the-hash (logon type 9), and impossible travel scenarios.
- Event ID 4769: Kerberos service ticket operations. Detects Kerberoasting via unusual TGS request patterns and RC4 encryption downgrades.
Active Directory Replication & Authentication Logs
AD-specific events are essential for detecting DCSync, NTDS.dit extraction, and Kerberos abuse:
- Event ID 4662: Directory service access, shows DS-Replication-Get-Changes-All requests from non-DC accounts (DCSync indicator).
- NTDS.dit creation events: File creation or modification of NTDS.dit outside of normal backup operations.
- Ntdsutil execution: Command-line utility used legitimately for AD maintenance but frequently abused to create snapshots of the AD database.
- DPAPI key extraction: Domain backup key extraction events indicating credential theft at the domain level.
Microsoft 365 (Entra ID) Logs
Cloud credential access targets Microsoft 365 and Microsoft Entra ID (previously Azure AD) authentication flows:
- Sign-in logs: Failed authentication patterns indicating password spraying (T1110.003), where many accounts tested with the same password.
- MFA challenge events: Repeated MFA failures or MFA fatigue attacks (T1621), where adversaries bombing users with push notifications until they accept.
- Token theft indicators: Session token replay from new IP addresses or device profiles.
SQL Server Authentication Logs
SQL Server credentials are high-value targets for data exfiltration:
- Failed login events: Brute-force attempts against SQL authentication accounts.
- Disabled account connections: Attempts to authenticate with disabled SQL accounts, a strong indicator of credential stuffing or persistence.
- Password change anomalies: Unexpected SQL account password modifications outside of change management windows.
Essential Windows audit policies for credential access detection
Out-of-the-box Windows audit configurations are insufficient for credential access detection. You need to enable advanced audit policies. Here are the critical settings:
| Audit policy category | Subcategory | What it enables |
|---|---|---|
| Account Logon | Audit Kerberos Service Ticket Operations | Event ID 4769, essential for Kerberoasting detection |
| Account Logon | Audit Kerberos Authentication Service | Event ID 4771. Kerberos pre-authentication failures (brute-force detection) |
| Detailed Tracking | Audit Process Creation | Event ID 4688, catches credential theft tool execution |
| Object Access | Audit Kernel Object | Event ID 4656/4663. LSASS memory access by non-system processes |
| DS Access | Audit Directory Service Access | Event ID 4662. DCSync replication request detection |
| Logon/Logoff | Audit Logon | Event ID 4624/4625, pass-the-hash and brute-force detection |
Note: Enable command-line logging for Event ID 4688 by setting "Include command line in process creation events" in Group Policy (Computer Configuration → Administrative Templates → System → Audit Process Creation). Without command-line data, Log360's Mimikatz, Rubeus, and Hashcat detection rules cannot match on tool-specific arguments.
How to detect and investigate credential access with Log360
Log360's credential access detection operates at three levels: tool-signature rules that catch known attack tools, behavioral rules that detect credential theft techniques regardless of tooling, and UEBA anomaly detection that surfaces novel credential abuse patterns. Together, these create a layered detection architecture that catches credential theft even when attackers use custom or obfuscated tools.
Detecting OS credential dumping (T1003)
OS credential dumping is the most dangerous credential access technique because a single successful execution yields credentials for multiple accounts, often including privileged accounts. Log360 provides 16 dedicated rules covering every major credential dumping vector.
Key detection rules
| Rule name | Severity | Platform | What it detects |
|---|---|---|---|
| Mimikatz Detection | Critical | Windows | Known Mimikatz process names and command-line arguments, the most widely used credential dumping tool |
| SprayKatz Detection | Critical | Windows | SprayKatz, a Python-based Mimikatz alternative that dumps credentials remotely via network protocols |
| SafetyKatz Detection | Critical | Windows | SafetyKatz, a .NET version of Mimikatz designed to run in memory and evade disk-based detection |
| Credential theft using Procdump or comsvcs | Critical | Windows | Use of Microsoft's Procdump or comsvcs.dll to dump LSASS memory, a "living off the land" technique that uses legitimate Microsoft tools |
| SAM SECURITY Hive Dump | Critical | Windows | Registry hive export targeting SAM and SECURITY hives, extracts local account password hashes |
| Active Directory Replication from Non Machine Account | Critical | AD | DCSync attack. AD replication request from a non-domain-controller account, used to extract any account's password hash |
| NTDS.DIT Created / By Uncommon Process | Attention/Trouble | AD | NTDS.dit database file created or accessed by a non-standard process, full domain credential extraction |
Investigation workflow for credential dumping alerts
- Confirm the process chain: When a Mimikatz or credential dumping alert fires, examine the full parent-child process tree. Legitimate security tools occasionally trigger false positives, but Mimikatz command-line arguments like sekurlsa::logonpasswords, lsadump::dcsync, or kerberos::golden are definitive indicators.
- Identify exposed credentials: Determine which accounts were logged in to the compromised host at the time of the dump. Check Windows Event ID 4624 logs for all active sessions, every one of those accounts must be treated as compromised.
- Check for lateral movement: After credential dumping, attackers immediately use stolen credentials. Search for Event ID 4624 (Type 3 or Type 9) logons from the compromised host to other systems. These pass-the-hash or pass-the-ticket events indicate the attacker is already moving laterally.
- Assess domain-level impact: If Active Directory Replication from Non Machine Account or Mimikatz DC Sync fired, the attacker may have the KRBTGT hash. This means Golden Ticket forgery is possible, and the entire domain must be considered compromised until the KRBTGT password is rotated twice.
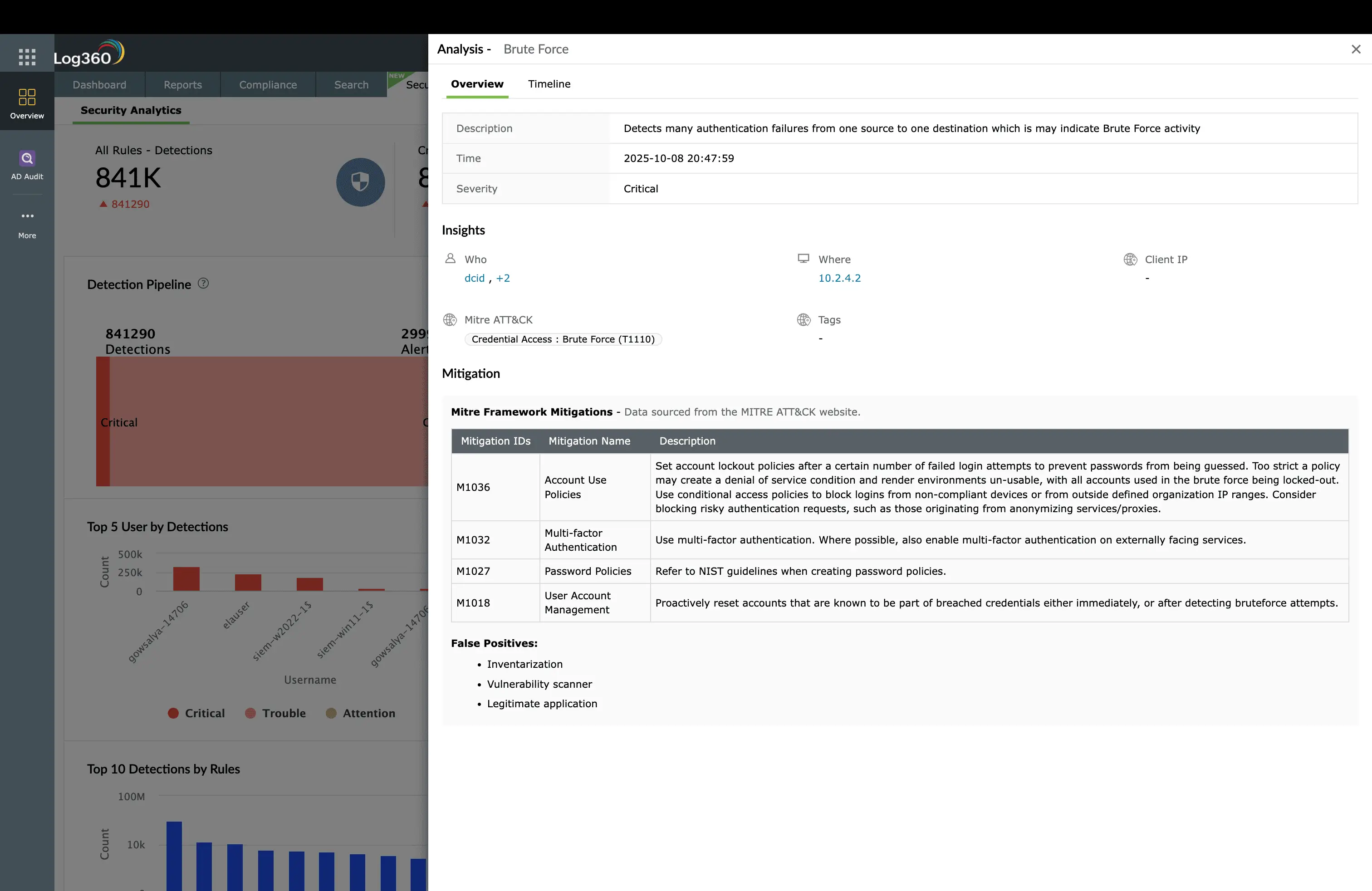
Detecting brute-force attacks (T1110)
Brute-force attacks generate the highest volume of credential access alerts but require careful tuning to separate real attacks from user mistakes. Log360's five brute-force rules combine tool-signature detection with pattern-based analysis.
Key detection rules
| Rule name | Severity | Platform | What it detects |
|---|---|---|---|
| Hashcat detection | Critical | Windows | Hashcat, the world's most popular password recovery tool, used to crack password hashes offline |
| Kerbrute detection | Critical | Windows | Kerbrute, a tool for brute-forcing Kerberos pre-authentication, bypassing account lockout policies |
| Hydra detection | Critical | Windows | Hydra, a parallelized network logon cracker supporting 50+ protocols (SSH, RDP, HTTP, SMB) |
| Notable account lockouts | Critical | Windows | Multiple accounts locked out in a short time window, indicates password spraying or automated brute-force attack |
| Suspicious Connection to Remote Account | Attention | AD | Unusual remote authentication patterns that deviate from established baselines |
Investigation workflow for brute-force alerts
- Analyze the pattern: Brute-force attacks have distinct patterns. Password guessing (T1110.001) targets a single account with many passwords. Password spraying (T1110.003) targets many accounts with one password. Check Windows Event ID 4625 (failed logon) to determine which pattern is occurring.
- Check source IP reputation: If the brute-force attack originates from external IPs, check against threat intelligence feeds integrated in Log360. Internal brute-force activity (from a compromised host) is more concerning, it indicates the attacker is already inside.
- Determine if any account was compromised: Look for a sequence of Event ID 4625 (failures) followed by Event ID 4624 (success) from the same source. This "fail-then-succeed" pattern confirms the brute force was successful.
- Assess the blast radius: For password spraying, the attacker likely had a username list. Check if any accounts in the targeted list have elevated privileges, domain admins, service accounts, or admin-tier users.
Detecting Kerberos ticket attacks (T1558)
Kerberos-based credential access is particularly dangerous because it exploits protocol design, not vulnerabilities. Any domain user can request TGS tickets for any SPN-enabled service, which means Kerberoasting requires no elevated privileges at all. Detection relies on identifying abnormal Kerberos request patterns.
Key detection rules
| Rule name | Severity | Platform | What it detects |
|---|---|---|---|
| Rubeus activity detected | Critical | Windows | Rubeus, a C# Kerberos manipulation toolkit used for Kerberoasting, ticket forging, and constrained/unconstrained delegation abuse |
| Kerberoasting initial activity detected | Trouble | AD | Burst of TGS requests targeting multiple service accounts, especially using RC4 encryption, the signature Kerberoasting pattern |
| SPN enumeration via setspn.exe detected | Trouble | Windows | Reconnaissance: attacker enumerating all SPN-enabled service accounts before launching Kerberoasting |
| PowerShell Kerberos ticket request detected | Trouble | AD | PowerShell-based Kerberos ticket request, a fileless Kerberoasting variant that doesn't require external tools |
| KrbRelayUp execution detected | Trouble | Windows | KrbRelayUp, a tool that combines Kerberos relay with local privilege escalation, converting any domain user to local admin |
| Suspicious outbound Kerberos connection | Trouble | Windows | Kerberos traffic to non-standard destinations, indicates Kerberos relay or ticket exportation to attacker infrastructure |
Investigation workflow for Kerberos attacks
- Identify targeted service accounts: When Kerberoasting is detected, determine which SPNs were requested. Check the SPN-enabled accounts for weak passwords, excessive privileges, and password age. Service accounts running as domain admin with old passwords are the highest-risk targets.
- Check for encryption downgrades: Review Event ID 4769 for the encryption type. Requests using RC4 (0x17) in an environment that supports AES are a strong Kerberoasting indicator. Modern environments should enforce AES-256 (0x12) for all Kerberos operations.
- Assess offline cracking risk: Even if you detect the Kerberoasting, the attacker may have already exported the tickets. The passwords of all requested service accounts should be rotated immediately, even if you catch the attack in progress.
- Look for subsequent credential use: If any service account passwords were cracked, search for new logon events using those service accounts from unexpected sources. This indicates the attacker is leveraging the cracked credentials.
Explore ManageEngine Log360's MITRE ATT&CK coverage across all 14 tactics
Log360 maps 2,000+ detection rules across all 14 MITRE ATT&CK Enterprise tactics, with the deepest coverage in the techniques that matter most. See how Log360's correlation engine connects credential access detections to lateral movement, privilege escalation, and impact alerts, giving your SOC the full attack narrative.
Proactive threat hunting for credential access
Rule-based detection catches known credential theft tools and patterns. But sophisticated attackers customize tools, use living-off-the-land binaries (LOLBins), and develop novel techniques that bypass signatures. Proactive threat hunting closes this gap. Here are four hunting hypotheses focused on credential access.
Hunt 1 - Undetected LSASS Access
Search for any process accessing LSASS memory that isn't a known legitimate accessor.
- What to search: Event ID 4656/4663 where the object is lsass.exe and the requesting process is NOT svchost.exe, csrss.exe, MsMpEng.exe (Defender), or your endpoint security agent. Any other process touching LSASS is suspicious.
- Why it works: Even when attackers use custom tools or reflective DLL injection, the LSASS access event is still generated. This hunt catches credential dumping regardless of the tool used.
- Where to search in Log360: Use Log360's log search to query Windows Security logs for Event IDs 4656/4663 with target process name containing "lsass".
Hunt 2 - Shadow Copy and NTDS.dit Extraction
Attackers who can't (or won't) use DCSync often resort to extracting the NTDS.dit database via volume shadow copies.
- What to search: Execution of vssadmin.exe, wmic shadowcopy, or diskshadow.exe on domain controllers, followed by file copy operations targeting ntds.dit, SYSTEM, or SECURITY registry hive files.
- Why it works: There are very few legitimate reasons to create shadow copies on domain controllers outside of backup windows. This hunt has a very low false-positive rate.
- Log360 rules that support this hunt: Shadow Copies Creation Using OS Utilities (Trouble) and Ntdsutil Abuse (Trouble) catch the most common extraction methods. Hunt for variants that bypass these rules.
Hunt 3 - Kerberos Anomalies Beyond Kerberoasting
Advanced attackers forge Kerberos tickets rather than cracking them. This requires detecting anomalies in Kerberos behavior.
- What to search: Kerberos TGT requests (Event ID 4768) where the encryption type is RC4 when the account supports AES. Golden Ticket usage where the ticket lifetime exceeds the domain's MaxTicketAge policy. Silver Ticket indicators where a TGS is presented without a preceding TGT request.
- Why it works: Forged tickets often have non-standard attributes, unusual lifetimes, mismatched encryption types, or missing parent requests. These statistical anomalies are difficult for attackers to eliminate.
- Where to search in Log360: Query Kerberos events and correlate with Log360's UEBA module, which builds baselines for normal Kerberos patterns per user and entity.
Hunt 4 - Credential Exposure in Cloud Environments
Cloud credential theft leaves different traces than on-premises attacks.
- What to search: OAuth token grant events from unusual applications. Service principal creation events followed by immediate resource access. API key usage from IP addresses that have never been seen before for that user.
- Why it works: Attackers who steal cloud tokens or API keys often use them from their own infrastructure. The IP-to-identity mismatch is a strong hunting signal.
- Where to search in Log360: Use Log360's cloud security monitoring to review M365 and AWS authentication patterns for anomalies.
How to respond to and remediate credential access attacks
When a credential access alert is confirmed as a true positive, the response urgency depends on what was stolen. A single user's password being brute-forced requires account-level remediation. A Mimikatz execution followed by DCSync requires domain-level incident response. Here are graduated response procedures for each scenario.
Immediate containment (first 30 minutes)
- Isolate the compromised host: The machine where credential theft occurred is the priority containment target. Log360's automated response can trigger network isolation via integration with ManageEngine Endpoint Central, executing containment scripts within seconds of a Critical alert.
- Disable compromised accounts: Every account that was active on the compromised system at the time of the credential dump must be disabled immediately. Log360's SOAR workflow can automate account disabling in Active Directory when Mimikatz or credential dumping rules fire.
- Block attacker network indicators: If the credential theft involved network communication (C2 beacons, NTLM relay), block the identified IPs and domains at the firewall and proxy.
Technique-specific remediation
| Technique | Immediate actions | Long-term hardening |
|---|---|---|
| OS Credential Dumping (T1003) | Reset passwords for all exposed accounts. If DCSync occurred, reset KRBTGT twice (12+ hours apart). Revoke all Kerberos tickets by resetting KRBTGT. | Enable Windows Credential Guard to protect LSASS memory from user-mode access. Deploy LSA RunAsPPL to prevent unsigned DLLs from loading into LSASS. Implement tiered administration (Tier 0/1/2 model). |
| Brute Force (T1110) | Lock targeted accounts. Block source IPs. If any accounts were successfully compromised (fail-then-succeed pattern), reset passwords and revoke sessions. | Enforce NIST SP 800-63B password policies. Deploy MFA on all externally accessible services. Implement smart lockout policies that block attacker IPs without locking out legitimate users. |
| Kerberos Tickets (T1558) | Rotate passwords for all targeted service accounts immediately. Force AES-only Kerberos for cracked accounts. | Migrate service accounts to Group Managed Service Accounts (gMSAs) with automatic 30-day password rotation. Enforce AES-256 encryption domain-wide by disabling RC4. Minimize SPN-enabled accounts to only those that genuinely require them. |
| Adversary-in-the-Middle (T1557) | Patch the exploited coercion vulnerability (PetitPotam, PrinterBug). Disable NTLM on affected systems if possible. If AD CS was abused, revoke the issued certificate. | Disable NTLM where possible, use Kerberos exclusively. Disable the print spooler service on all domain controllers. Enable Extended Protection for Authentication (EPA) on all web-based AD CS enrollment endpoints. Audit AD CS templates for ESC1-ESC8 vulnerabilities. |
Log360 automated response capabilities
Log360 can execute critical response actions automatically when credential access rules fire, reducing mean time to respond from hours to seconds:
| Response action | Use case | How it works |
|---|---|---|
| Disable user account | Credential dumping alerts (T1003), brute force success (T1110) | Automatically disables AD accounts when Critical credential theft rules fire. Integrates with ADSelfService Plus for self-service recovery after verification. |
| Force password reset | Kerberoasting alerts (T1558) | Forces immediate password reset for service accounts targeted in Kerberoasting attacks. |
| Run custom containment script | Mimikatz/DCSync alerts (T1003) | Executes network isolation scripts on the compromised host via Endpoint Central integration. |
| Create ServiceDesk Plus ticket | All credential access alerts | Automatically creates an incident ticket with alert details, affected accounts, and mapped response playbook steps in ServiceDesk Plus. |
| Send escalation notification | Critical-severity alerts | Email/SMS notification to SOC analysts and security leadership within seconds of any Critical credential access detection. |
Other credential access techniques to monitor
Beyond the four core techniques, MITRE ATT&CK TA0006 includes additional credential access methods. While these have fewer prebuilt rules, they represent emerging attack vectors, particularly in cloud and hybrid environments. Log360's custom correlation rule builder and UEBA behavioral analytics can extend detection to these techniques.
| Technique | Description | Detection approach in Log360 |
|---|---|---|
| Credentials from Password Stores (T1555) | Extracting passwords from browser credential stores, password managers, or Windows Credential Manager | Monitor process access to browser credential databases (Login Data, cookies.sqlite). Custom rules for credential manager export commands. |
| Unsecured Credentials (T1552) | Finding passwords in files, scripts, registry, environment variables, or cloud metadata APIs | UEBA anomaly detection for unusual file access patterns. Custom rules for cloud instance metadata queries (169.254.169.254). |
| Modify Authentication Process (T1556) | Patching authentication DLLs, installing skeleton keys, or modifying PAM modules to capture credentials in transit | File integrity monitoring on authentication DLLs (msv1_0.dll, pam_*.so). AD monitoring for skeleton key indicators (single-password authentication anomaly). |
| Multi-Factor Authentication Request Generation (T1621) | MFA fatigue attacks, bombing users with push notifications until they approve one | Custom rules for repeated MFA push events for a single user within a short time window. UEBA behavioral deviation from normal MFA patterns. |
| Steal Web Session Cookie (T1539) | Extracting session cookies to hijack authenticated web sessions without knowing the password | Monitor for browser cookie database access by non-browser processes. Token replay detection via UEBA source-IP deviation. |
| Steal or Forge Authentication Certificates (T1649) | Exploiting AD CS misconfigurations (ESC1-ESC8) to issue certificates granting domain admin access | AD CS audit log monitoring for unusual certificate enrollment requests. Custom rules for ESC1 template abuse patterns. Integrates with ADCSPwn detection. |
Building a credential access detection strategy
Effective credential access detection is not about deploying rules and hoping for the best. It requires a deliberate strategy that covers multiple detection layers, accounts for attacker evasion, and aligns tool deployment with your environment's specific risk profile.
Step 1 - Map Your Credential Attack Surface
Before configuring detection rules, understand where credentials live in your environment and which are most valuable to attackers:
- Inventory privileged accounts: Domain admins, service accounts with SPN, accounts with DCSync rights, Microsoft Entra ID Global Admins, AWS IAM users with console access. These are the attackers' primary targets.
- Identify credential stores: LSASS on domain-joined workstations, NTDS.dit on domain controllers, Microsoft Entra ID token cache, AWS secrets in environment variables, SQL Server sa accounts. Each requires specific detection rules.
- Assess credential hygiene: Service accounts with passwords older than 90 days are prime Kerberoasting targets. Local admin passwords reused across workstations enable credential reuse. These hygiene issues directly inform which detection rules to prioritize.
Step 2 - Deploy Layered Detection
No single detection layer catches everything. Build defense in depth:
Layer 1: Tool-signature detection
Log360's Critical-severity rules (Mimikatz, Rubeus, Hashcat, Hydra, Kerbrute, Petitpotam) catch known attack tools with high confidence and minimal false positives. These should be set to immediate notification, any legitimate use of these tools in production should be vanishingly rare.
Layer 2: Behavioral detection
Log360's Trouble-severity rules (LSASS access anomalies, AD replication from non-DC, Kerberoasting patterns, SPN enumeration) detect credential theft techniques rather than specific tools. These catch attackers who use custom or obfuscated tools.
Layer 3: UEBA anomaly detection
Log360's UEBA module builds behavioral baselines for authentication patterns, login times, source IPs, Kerberos request volumes, service account usage. Deviations from baseline catch novel attacks that bypass both tool-signature and behavioral rules.
Layer 4: Proactive hunting
Scheduled threat hunting exercises, using the hypotheses in the previous section, catch credential access that all automated layers missed. Log360's search and forensics capabilities support complex hunting queries across historical logs.
Step 3 - Tune and Validate
Credential access detection generates false positives from legitimate IT activities, backup agents accessing LSASS, IT staff using lsadump tools for AD recovery, service accounts with legitimate SPN enumeration. Effective tuning:
- Allowlist known legitimate processes: Identify your backup agent, EDR agent, and AD management tools. Create exclusions for processes from specific paths with specific parent processes only, never blanket-exclude a process name.
- Validate with purple team exercises: Run controlled credential access attacks using the same tools (Mimikatz, Rubeus, Kerbrute) in a test environment to confirm Log360's rules fire as expected. Validate that renamed or obfuscated variants are still detected.
- Review alert fidelity monthly: Check the true-positive rate for each credential access rule. Rules below 80% true-positive rate need tuning. Rules that never fire may indicate a log collection gap.
Integration advantage: Log360's native integration with the ManageEngine IT management suite, including Endpoint Central for endpoint isolation, ServiceDesk Plus for incident ticketing, PAM360 for privileged access governance, and ADManager Plus for AD management, means credential access detection, investigation, and response happen in a unified workflow rather than across disconnected consoles.
Need to explore ManageEngine Log360? Schedule a personalized demo
Frequently asked questions
What is credential access in MITRE ATT&CK?
Credential access (TA0006) is a tactic in the MITRE ATT&CK framework that describes techniques adversaries use to steal credentials such as passwords, password hashes, authentication tokens, and Kerberos tickets. Attackers use stolen credentials to impersonate legitimate users, escalate privileges, and move laterally across the network. Credential access is involved in nearly half of all confirmed breaches according to the Verizon DBIR.
What are the most common credential access techniques?
The four most commonly observed credential access techniques are OS Credential Dumping (T1003) using tools like Mimikatz, Brute Force (T1110) including password spraying, Steal or Forge Kerberos Tickets (T1558) through Kerberoasting, and Adversary-in-the-Middle (T1557) using NTLM relay techniques. Log360 provides 30 targeted detection rules across these four techniques.
How do I detect Mimikatz in my environment?
Detect Mimikatz through multiple signals: process creation events (Event ID 4688) with known Mimikatz command-line arguments, LSASS memory access (Event ID 4656/4663) by unauthorized processes, suspicious service installations matching credential dumping tool patterns, and DCSync replication requests from non-domain-controller accounts. Log360 has dedicated Mimikatz Detection (Critical), Mimikatz DC Sync (Trouble), and LSASS Dump Keyword In CommandLine (Trouble) rules that automate this detection.
What is the difference between credential access and initial access?
Initial access (TA0001) describes how attackers gain their first entry into an environment, through phishing, exploitation, or previously stolen credentials. Credential access (TA0006) occurs after the attacker is already inside and focuses on stealing additional credentials to escalate privileges, move laterally, and maintain persistence. Detecting initial access stops the attacker at the door; detecting credential access stops them from gaining the keys to every room.
How many detection rules does Log360 have for credential access?
Log360 has 219 prebuilt detection rules mapped to the credential access tactic (TA0006), covering Windows, Active Directory, Microsoft 365, and SQL Server log sources. This includes 16 rules for OS Credential Dumping (T1003), 5 for Brute Force (T1110), 6 for Kerberos Ticket attacks (T1558), and 3 for Adversary-in-the-Middle (T1557), plus 189 additional rules for broader credential behavior anomalies. These are part of Log360's library of 2,000+ detection rules covering all 14 MITRE ATT&CK Enterprise tactics.
What log sources are critical for detecting credential access?
The most critical log sources are:
- Windows Security Event Logs. Event IDs 4624/4625 (logon), 4656/4663 (object access), 4688 (process creation with command line), 4769 (Kerberos ticket operations);
- Active Directory replication and authentication logs. Event ID 4662 for DCSync detection;
- Microsoft 365 Entra ID, sign-in and audit logs for cloud credential abuse; and (4) SQL Server authentication logs for database credential attacks. Log360 collects and correlates across all of these natively.
How do I prevent Kerberoasting attacks?
Prevent Kerberoasting by taking these steps:
- Rotating service account passwords every 30-60 days.
- Enforcing AES-only Kerberos encryption by disabling RC4 via Group Policy.
- Using Group Managed Service Accounts (gMSAs) with automatic password rotation instead of standard service accounts.
- Minimizing SPN-enabled accounts.
- Monitoring with Log360's Kerberoasting Activity rule to catch attacks in progress. Even with prevention controls, detection remains essential, attackers may find accounts that were missed during hardening.
- What is credential access in MITRE ATT&CK?
- Why credential access is critical to detect early
- Credential access techniques
- Real-world attack scenarios
- Detecting credential access by log source
- How to detect and investigate with Log360
- Proactive threat hunting
- How to respond and remediate
- Other credential access techniques
- Building a detection strategy
- Frequently asked questions



