- Home
- SIEM
- Incident management
- Incident resolution process
Incident resolution in cybersecurity: Process, challenges, and best practices
In this page
- What is incident resolution?
- Incident resolution vs incident response
- Incident resolution in the security incident lifecycle
- Step-by-step incident resolution process
- Key challenges in incident resolution
- Incident resolution best practices
- How automation and SOAR improve incident resolution
- How Log360 streamlines incident resolution
What is incident resolution?
Incident resolution is the process of systematically addressing a security incident from detection through closure. It involves investigating the incident, containing the threat, eliminating the root cause, restoring affected systems, and documenting the actions taken.
An effective incident resolution process helps organizations minimize operational disruption, reduce security risk, and ensure incidents are handled in a consistent and auditable manner. It also enables security teams to learn from past incidents and improve their overall security posture.
About this explainer: A resilient SOC needs effective incident management. Explore our series on What is SIEM and SIEM tools to understand how SIEM streamlines threat response.
Incident resolution vs incident response
Although often used interchangeably, incident response and incident resolution serve different purposes in the security lifecycle.
Incident response focuses on immediate actions taken after an incident is detected. It aims to contain the threat, limit damage, and prevent further impact on systems and data. This phase involves validating alerts, identifying affected assets, isolating compromised systems, and applying short-term mitigation measures to stop the attack as quickly as possible.
Incident resolution extends beyond containment to address the full incident lifecycle. It includes root cause analysis, forensic investigation, remediation, system recovery, documentation, and post-incident review. With automation and SOAR-driven workflows, incident resolution ensures incidents are fully closed, handled consistently, and less likely to recur.
Understanding this distinction helps security teams identify where incident resolution fits within the broader security incident lifecycle.
Incident resolution in the security incident lifecycle
Incident resolution is a critical phase in the security incident lifecycle that ensures detected threats are fully investigated, mitigated, and prevented from recurring. Once an incident is identified, it moves through a series of stages detection, investigation, containment, eradication, recovery, and closure. Each stage is designed to minimize impact, restore normal operations, and strengthen organizational security.
Step-by-step incident resolution process
A structured incident resolution process helps organizations manage security incidents efficiently and consistently across the environment.
- Detection and alert validation
Security events are detected through logs, alerts, or continuous monitoring tools. Each alert is validated to filter out false positives and ensure that threats are prioritized for further action.
- Investigation and analysis
The incident is analyzed to understand its scope, severity, and root cause. This step involves identifying affected systems, users, data, and the attack vectors involved.
- Containment
Immediate actions are taken to isolate affected systems or accounts and prevent the threat from spreading across the network or impacting additional assets.
- Eradication
The underlying cause of the incident, such as malware, misconfigurations, or unauthorized access, is removed to ensure the threat is completely eliminated from the environment.
- Recovery
Affected systems and services are restored to normal operation and closely monitored to confirm they are secure, stable, and functioning as expected.
- Closure and documentation
The incident is formally closed with detailed documentation covering the actions taken, impact analysis, and lessons learned to improve future incident handling.
Key challenges in incident resolution
Organizations face several challenges when resolving security incidents. Understanding these challenges helps security teams develop more effective strategies and improve overall incident handling.
Alert fatigue and volume overload: Security teams often receive hundreds or thousands of alerts daily. Identifying critical threats among false positives consumes significant time and resources, which can slow response and increase the risk of overlooking genuine incidents.
Complex and evolving attack methods: Attackers continuously develop new tactics, techniques, and procedures. Advanced persistent threats, zero-day exploits, and sophisticated social engineering attacks make incident resolution more complex and time-consuming.
Fragmented security tools: Organizations often rely on multiple, disparate security tools that do not integrate well. This creates visibility gaps and requires manual correlation of data, slowing investigations and increasing the likelihood of missing critical connections.
Balancing speed with thoroughness: Security teams must quickly restore services while ensuring complete threat eradication. Rushing recovery can leave vulnerabilities or persistent threats, while overly cautious approaches extend downtime and impact business operations.
Compliance and legal requirements: Meeting regulatory obligations during incident resolution adds additional complexity. Organizations must preserve evidence, comply with notification deadlines, and maintain proper documentation while actively mitigating threats.
Resolve incidents faster with Log360
Eliminate manual triage and delayed response by automating alert enrichment, containment, and remediation with built-in SOAR playbooks.
Incident resolution best practices
Following established best practices helps organizations improve incident resolution outcomes and reduce mean time to resolution.
1. Develop and maintain incident resolution playbooks:
Create detailed playbooks for common incident scenarios such as malware attacks, data breaches, denial-of-service attacks, and insider threats. Playbooks should outline step-by-step actions, escalation paths, and decision points, and be reviewed regularly to address evolving threats.
2. Automate response workflows: Automating routine tasks such as isolating compromised endpoints, blocking malicious IP addresses, or disabling affected user accounts accelerates containment and reduces manual effort. Automation ensures consistent execution while allowing security teams to focus on investigation and remediation.
3. Define clear roles and responsibilities: Assign specific roles within the incident management team, including investigation, containment, communication, and escalation. Clear ownership reduces confusion during critical incidents and improves coordination across teams.
4. Prioritize incidents based on risk and impact: Implement a structured prioritization framework that considers threat severity, asset criticality, and business impact. This ensures high-risk incidents receive immediate attention while lower-priority events are handled efficiently.
5. Ensure centralized logging and monitoring: Centrally collect logs from critical systems and monitor them continuously. Comprehensive visibility is essential for accurate investigation, forensic analysis, and understanding the full scope of an incident.
6. Conduct regular incident response exercises: Perform tabletop exercises and simulated attack scenarios to test incident resolution processes. Regular practice helps identify gaps, improve team readiness, and refine playbooks based on real-world conditions.
7. Enrich alerts with threat intelligence: Integrate threat intelligence to enrich security events with information on known attacker tactics, techniques, and indicators of compromise. Contextual insights enable faster and more accurate resolution decisions.
8. Document incidents thoroughly: Maintain detailed records of incident timelines, actions taken, and outcomes. Proper documentation supports compliance, audit requirements, and continuous improvement of incident handling processes.
9. Perform post-incident reviews: Conduct structured reviews after major incidents to identify areas for improvement and strengthen future response capabilities.
10. Enable cross-team collaboration: Effective incident resolution requires coordination between security, IT operations, legal, and business teams. Predefined communication workflows ensure smoother collaboration during incidents.
How automation and SOAR improve incident resolution
As security environments become more complex, relying on manual processes to resolve incidents is no longer effective. Automation and SOAR help organizations respond to incidents faster, reduce operational overhead, and ensure consistent handling across the incident lifecycle.
SOAR enables predefined response workflows to be automatically triggered when a security incident is detected. These workflows can perform immediate containment actions such as isolating compromised endpoints, blocking malicious IP addresses, disabling affected user accounts, collecting forensic data, and creating incident tickets in ITSM tools. This ensures that critical response steps begin instantly, limiting the spread and impact of threats.
Automation also enhances alert triage and investigation by enriching incidents with contextual data from threat intelligence feeds and historical security events. Standardized playbooks enforced through SOAR ensure incidents are resolved consistently, reduce manual error, and support audit and compliance requirements.
By standardizing response through playbooks, SOAR cuts MTTR and alert fatigue while ensuring audit-ready incident handling.
How Log360 streamlines incident resolution
ManageEngine Log360 is a unified SIEM solution with built-in SOAR capabilities that enables security teams to resolve incidents from a single platform. Log360 natively integrates orchestration, automation, and response into the incident resolution workflow eliminating the need for separate SOAR tools. By combining centralized log management, real-time threat detection, and automated response, Log360 enables organizations to move from alert to resolution faster.
From alerts to automated remediation:
Centralized incident visibility: Log360 ingests and correlates logs from diverse sources, including leading EDR platforms like CrowdStrike Falcon (via Event Streams for detections, audits, user activity, and more), Microsoft Defender, and Bitdefender, providing unified visibility across endpoint, network, identity, and cloud telemetry.Track all incidents from malware alerts, phishing attempts, anomalous logins, and data exfiltration in a single dashboard without switching between SIEMs, endpoints, and network tools.
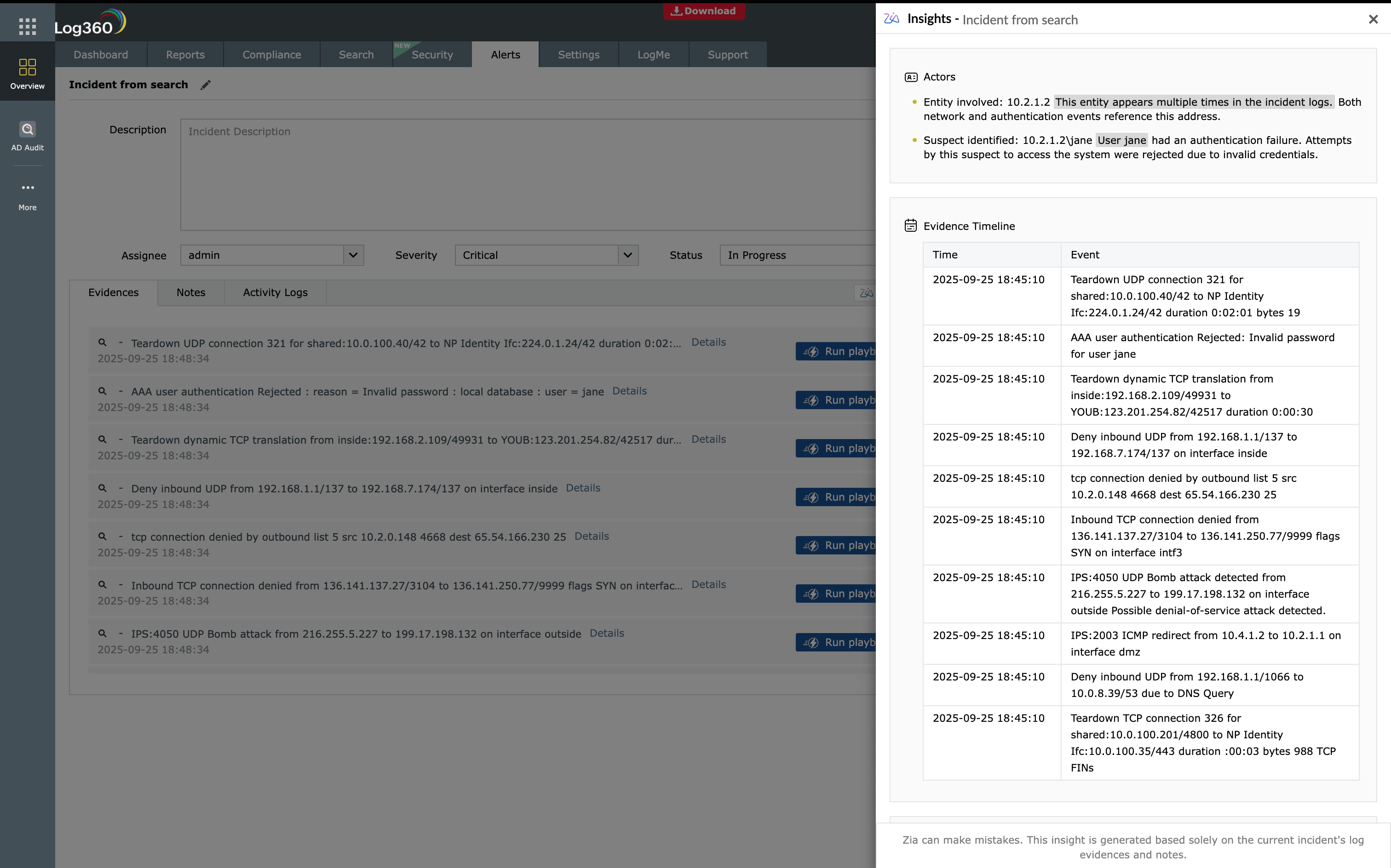
Automated enrichment and validation: Log360 Playbooks automatically gather context for incidents, including threat intelligence, user activity, asset information, and historical behavior. This eliminates repetitive manual checks.
Instant filtering and prioritization: Log360 Cross-check indicators against known attack patterns, malicious IPs, and file reputations to confirm threats quickly.
Real-time remediation: Execute actions such as isolating endpoints, disabling compromised accounts, blocking IPs, or quarantining files directly from Log360. Playbooks orchestrate these steps automatically, reducing the mean time to resolution (MTTR) from hours to minutes.
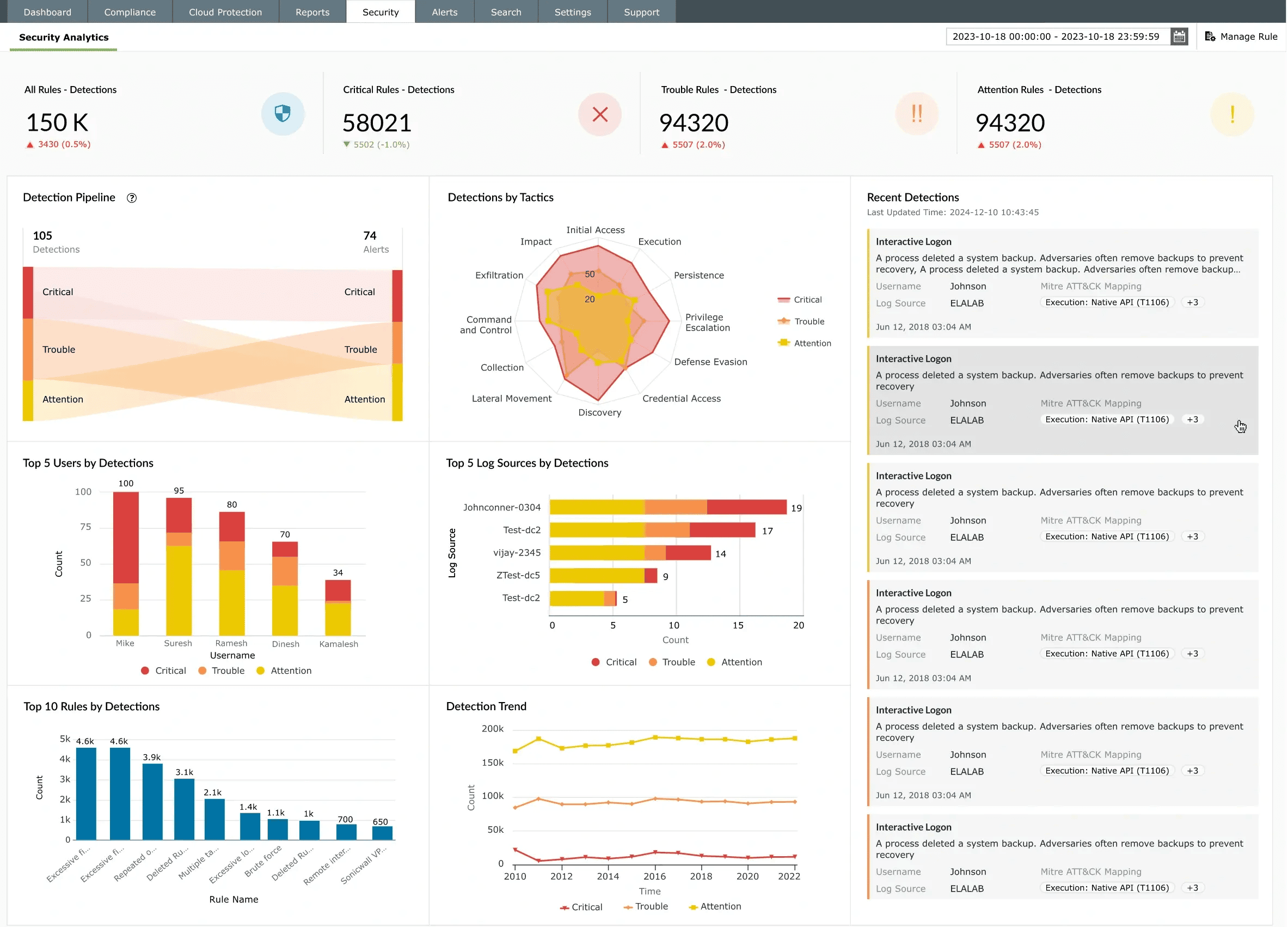
Automated incident resolution with Playbooks
At the core of Log360’s incident resolution capability are Playbooks, which transform manual, reactive processes into proactive, repeatable, and automated workflows.
Go beyond basic incident handling
- Instant search and filtering: Locate incidents quickly using criteria like user, device, alert type, or severity, eliminating manual correlation.
- Real-time investigation: Analyze incidents as they occur, with contextual insights attached to every event.
- Suspicious activity detection: Identify repeated failed logins, privilege abuses, unusual access patterns, or configuration changes to detect threats early.
- Compliance-ready reporting: Playbooks and incident logs are automatically documented, mapped to standards like PCI DSS, HIPAA, GDPR, and SOX, simplifying audits.
By combining SIEM and native SOAR capabilities in a single platform, Log360 enables organizations to resolve incidents faster, reduce operational overhead, and continuously improve their security posture.
FAQs
1. What is incident resolution in cybersecurity?
Incident resolution in cybersecurity refers to the structured process of investigating, containing, eliminating, and recovering from a security incident. It ensures that threats are fully addressed, affected systems are restored, and preventive measures are implemented to reduce the risk of recurrence.
2. What are the steps in the incident resolution process?
The incident resolution process typically includes detection, investigation, containment, eradication, recovery, and closure with documentation. Following these steps helps organizations manage incidents consistently, minimize operational impact, and ensure complete threat remediation.
3. How is incident resolution different from incident response?
Incident response focuses on immediate actions to contain and mitigate a security threat, whereas incident resolution covers the entire lifecycle, including root cause analysis, system recovery, documentation, and continuous improvement after the incident is resolved.
4. How does automation improve incident resolution?
Automation improves incident resolution by reducing manual intervention, accelerating response actions, and ensuring consistent execution of remediation steps. Automated workflows and runbooks help security teams contain threats faster and reduce the overall mean time to resolve incidents.
5. How to improve incident resolution time?
Organizations can reduce incident resolution time by prioritizing critical alerts, automating repetitive tasks, standardizing response workflows, and ensuring clear ownership and escalation paths within the security operations team.
6. What should an incident response plan include?
An incident response plan should define roles and responsibilities, detection mechanisms, communication protocols, containment strategies, recovery procedures, and post-incident review processes. A well-documented plan ensures faster and more coordinated response.
7. How do you create an incident response plan?
To create an incident response plan:
- Identify critical assets and risks
- Define incident categories and severity levels
- Establish response procedures
- Assign roles and escalation paths
- Test the plan regularly through simulations
You can align your plan with industry standards like NIST SP 800-61 and implement it using incident management software.


