Related content
While the scope of SIEM and SOAR vary widely, in today's security landscape, combining SIEM and SOAR creates a unified security ecosystem that bridges the gap between detection and response. This article helps you understand the differences between the two platforms and the benefits of integrating them.
SOAR vs. SIEM
The ultimate difference between SOAR and SIEM tools lie in their purpose. This can be better understood the Gartner® definitions.
Gartner defines SOAR as technologies that enable organizations to collect inputs monitored by the security operations team. It also emphasizes that these inputs such as alerts from SIEM and other security tools allow SOAR to define, prioritize, and drive standardized incident response activities.
According to Gartner, SIEM is a technology that supports threat detection, compliance and security incident management. It also establishes that SIEM tools operate through the collection and analysis (both near real time and historical) of security events, as well as a wide variety of other event and contextual data sources.
Ultimately, while these tools serve different purposes, they must work in tandem to achieve comprehensive threat detection, investigation, and response.
What is SIEM?
What is SOAR?
SOAR, also known as security orchestration, automation, and response is a cyber security platform that orchestrates various security tools for the automation of response workflows to contain and mitigate security incidents.
How SOAR works: Ingest alerts from tools like SIEM and XDR to trigger playbooks or response workflows to neutralize threats. Its operational workflow can be summarized as follows:
Alert ingestion → Alert triage → Evidence management → Incident response → Forensic analysis.
Why use SOAR: To accelerate incident response and reduce MTTR by automating low-priority tasks, and allowing analysts to execute predefined workflows.
What is SIEM?
SIEM is a cybersecurity tool that collects and analyzes security data from various log sources to detect threats and generate alerts. These alerts typically serve as the input for SOAR platforms to coordinate and trigger response workflows.
How SIEM works: Aggregates logs from heterogeneous sources to carry out cross-layer correlation for threat detection and alerting. Its operational workflow can be summarized as follows:
Log collection → Event correlation → Threat detection → Alert generation.
Why use SIEM: For advanced threat detection and generation of high-fidelity alerts, in addition to log management and compliance.
Related content
Core capabilities of modern SOAR and SIEM
SIEM capabilities
| Rule-based detection | ML-based alerting | AI-powered investigation |
|---|---|---|
| These are the foundational logic sets that define what constitutes a security event. Modern platforms provide frequently updated, out-of-the-box rule sets for diverse environments (cloud, on-premises, and hybrid) for effective threat hunting and attack detection. | Unlike traditional SIEM that triggers an alert every time a simple baseline is hit, smart thresholds use ML to adjust limits dynamically based on historical patterns. This prevents alert fatigue and reduces the noise in the SOC. | Leveraging GenAI, SIEM tools can now transform hundreds of technical log entries into a concise, human-readable narrative. This allows analysts to immediately grasp the impact of a complex incident without manually piecing together individual raw logs. |
SOAR capabilities
| Automated workflow orchestration | Context-aware execution | Playbook management |
|---|---|---|
| Modern playbooks are powered by a visual orchestration engine that allow teams to design complex response logic such as cross-verifying threat intelligence or isolating a host using a drag-and-drop interface that requires no manual scripting. | SOAR systems categorize playbooks based on their specific trigger source to ensure the response is tailored to the data provided. Further subplaybooks can be nested as a subsequence within larger workflows for modular efficiency. | New-gen SOAR tools allow administrators to clone, validate, and monitor playbooks throughout their entire operational life with a detailed execution history that tracks performance trends and success rates to ensure the automation is performing as expected. |
SOAR vs SIEM - Which is right for you?
When to choose SIEM: Choose SIEM when you need centralized visibility and long-term data retention. It is essential for meeting compliance requirements, performing forensic investigations, and detecting complex threats hidden across disparate network logs.
When to choose SOAR: Choose SOAR when your team is overwhelmed by repetitive tasks and slow response times. It is ideal for automating alert triage, orchestrating disconnected security tools, and reducing the MTTR.
Key differences between SIEM and SOAR
SIEM and SOAR are two different platforms that differ in their architecture, working, functions, and more. Let's understand their differences based on the following categories.
1. Scope of SIEM and SOAR
The primary scope of SIEM is to provide comprehensive visibility into network events and security incidents in real-time. To achieve this, it offers unified dashboards, granular reports, high-fidelity alerts, and detailed audit trails for specific events or attacks as they occur.
On the contrary, the scope of SOAR extends to comprehensive incident response at machine speed. It leverages predefined workflows and playbooks that execute automatically upon the detection of an attack, bridging the gap between detection and remediation.
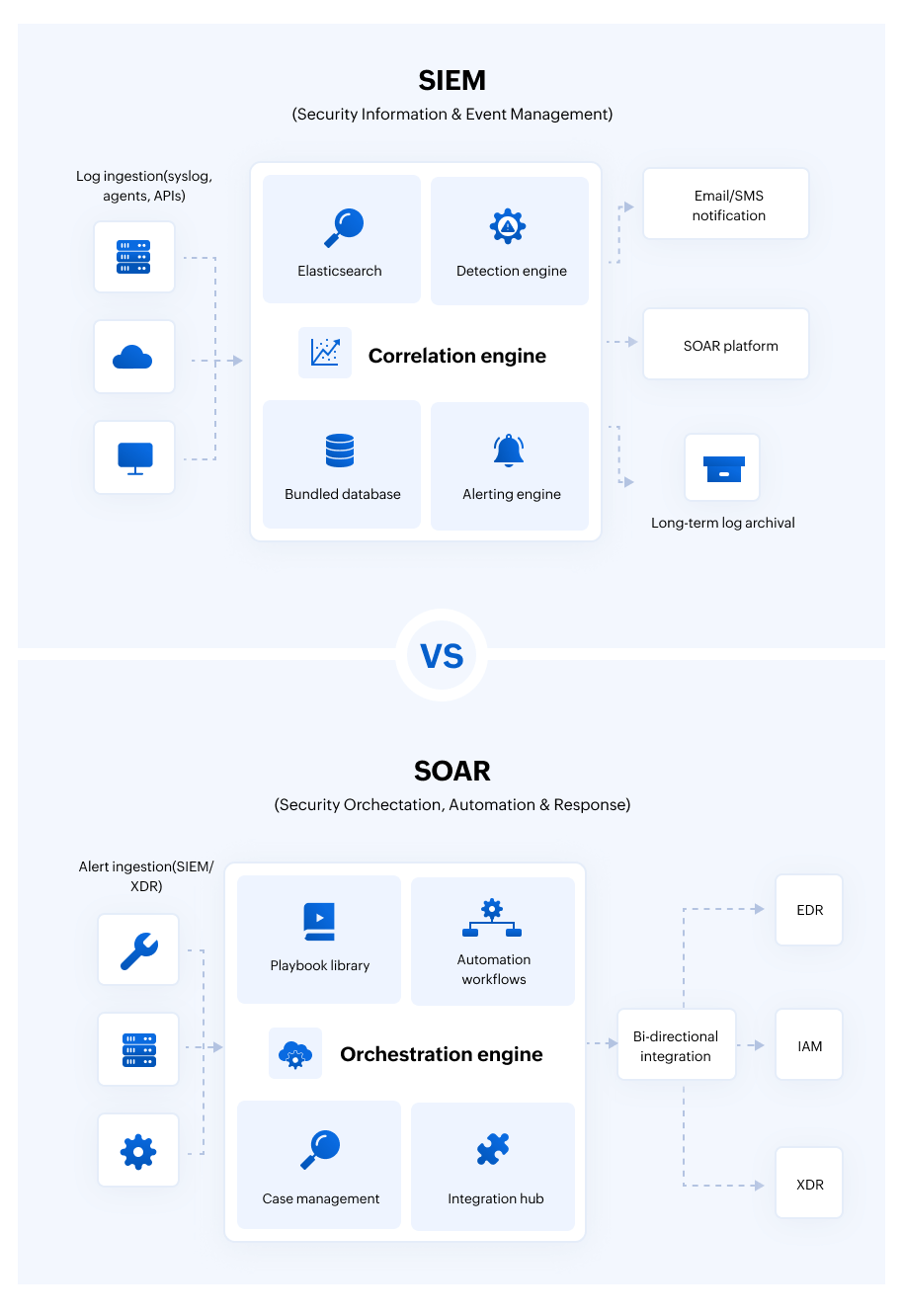
2. Architectural differences between SIEM and SOAR
SIEM: A SIEM tool primarily consists of a log management module, a detection engine, an alerting engine, and a database for long-term log retention and archival.
SOAR: A SOAR tool consists of an orchestration channel, automation templates or workflows, a playbook library, and an investigation console.
3. Working of SIEM and SOAR
The differences between SIEM and SOAR in their operations can be explained by extracting the various functional stages in a SOAR and SIEM tool. The below table helps you understand, the different layers and their functions.
| Working stages | SIEM | SOAR |
|---|---|---|
| Stage 1: Ingestion | Ingests raw logs, flows, and telemetry via Syslog, agents, or APIs. | Ingests high-fidelity alerts from SIEM, EDR, or XDR tools using APIs. |
| Stage 2: Processing | Converts raw data into a standard format as key-value pairs and indexes the data for search enablement and report generation. | Connects to third-party tools, threat intel data, and other analytical engines to create an orchestration channel and automation flow for data enrichment and cross tool response. |
| Stage 3: Detection/investigation | Runs predefined rules to find signature attack patterns or known IoCs and IoAs. Also leverages UEBA to identify abnormal behavior to flag anomalies, assign risk scores, and insider threats. | Triage alerts based on severity, evidence and risk scores of the users and entities involved and creates active cases that are assigned to analysts for investigation. |
| Stage 4: Alerting/response | Flags a specific event as suspicious and produces a prioritized notification that a security boundary has been breached or a policy has been violated. | Triggers automated, logic-based workflows to investigate the alert and execute containment actions, such as isolating impacted hosts or disabling compromised accounts. |
| Stage 5: Follow-up activity | Transmits or feeds the generated alerts to integrated platforms or SOAR tools to respond to the incident, and generates audit trails for compliance. | Generates detailed incident reports including process trees, workflows, and evidence for forensic analysis. |
Relationship between SIEM and SOAR - The synergy
Combining SIEM and SOAR creates a unified security ecosystem that bridges the gap between detection and response. The key benefits of integrating SIEM and SOAR include:
- Accelerated incident response: The integration allows the SIEM to pass high-fidelity alerts directly to SOAR playbooks. This automation eliminates manual triage, enabling the system to contain threats like ransomware at machine speed.
- Reduced alert fatigue: By using SOAR to automate the investigation of routine SIEM alerts, analysts shall automate manual investigation of low-priority noise. This ensures they can focus their expertise on high-priority, complex hunting tasks.
- Enriched threat intelligence: When SIEM detects an anomaly, SOAR automatically queries external threat feeds for context. This enrichment provides analysts with a complete investigative package before they even open a case.
- Unified tool orchestration: The synergy allows your security stack to act as a unit. A detection in the SIEM can trigger the SOAR to update firewall rules or isolate infected endpoints.
- Standardized compliance and documentation: While SIEM maintains long-term audit logs, SOAR captures every automated response step. Together, they provide a comprehensive, tamper-proof record of both the breach and the remediation.
Strategic implementation: Advantages and limitations of SIEM and SOAR
SIEM vs SOAR is a choice between detection and response. Below is the strategic breakdown of the advantages and limitations of implementing these tools.
SIEM implementation
SIEM excels at cross-layer correlation and detection. It is the strategic choice if your priority is compliance and log forensics.
| Advantages of SIEM | Limitations of SIEM |
|---|---|
|
|
SOAR implementation
SOAR excels at cross-layer response and remediation. It's standalone functionality is very much limited and always depends on detection tools like SIEM for inputs i.e., alerts.
| Advantages of SOAR | Limitations of SOAR |
|---|---|
|
|
SIEM vs. SOAR decision matrix: Choosing the best tool
How to choose the best SIEM and SOAR tools
Here are some critical capabilities that need to be considered while choosing SIEM and SOAR tools to maximum synergy and performance.
Full-fledged automation
When choosing SIEM and SOAR tools, automation must extend beyond simple remediation to handle data enrichment and high-fidelity threat escalation. Effective automation instantly gathers threat intelligence and correlates user context to ensure an alert is enriched and correctly prioritized for immediate action. Whereas proactive escalation ensures that critical threats bypass the noise and reach senior responders immediately. Thus full-fledged automation is a critical capability of SIEM and SOAR tools to ensure effective pre-investigation and swift incident response.
Bidirectional integration
Bidirectional integration creates a synchronized feedback loop between SIEM and SOAR platforms. While SIEM sends alerts to SOAR to trigger automation, SOAR sends status updates back to the SIEM. This helps SIEM manage alerts, identify false positives, and update the status of incidents. On the other hand, closing incidents on SIEM helps SOAR prevent double working on alerts. This ensures that both systems are synchronized to facilitate enhanced incident response. Thus it is important to choose tools that offer seamless bidirectional integration with open APIs and integrations.
Low-code customization
SIEM and SOAR tools with low-code customization empower analysts to quickly adapt playbooks and workflows to emerging threats. Low code platforms use a visual, drag-and-drop interface to build security workflows without deep programming knowledge. This approach bridges the skills gap, allowing SOC teams automate complex responses and maintain synchronized SIEM-SOAR environments without needing a dedicated software developer.
Vendor-agnostic flexibility
It is important to avoid vendor lock-in while choosing SIEM and SOAR tools because it greatly limits the capabilities of both platforms, resulting in tool sprawl. Thus choosing platforms that are vendor-agnostic and offer pre-built connectors for a wide range of EDR, firewalls, and email gateways, regardless of the manufacturer, can help streamline integration, collaboration, and strengthen the overall security stack.
Explore ManageEngine Log360's SIEM and SOAR capabilities with a personalized walkthrough.
Frequently asked questions
SIEM vs. SOAR: Which is right for my organization?
Choose SIEM if the priority is log centralization, compliance reporting, and real-time threat detection. Integrate it with SOAR if the security team is overwhelmed by alert volume and needs to automate repetitive response tasks.
What is the difference between SIEM and SOAR?
The primary between SIEM and SOAR is that SIEM focuses on threat detection and SOAR focuses on incident response. Here are some core differences:
| SIEM | SOAR |
|---|---|
| Aggregates, normalizes, and correlates logs from various sources for threat detection. | Orchestrates various detection and response tools to automate the incident response process. |
| Ingests logs from network devices and third-party integrations. | Ingests alerts generated by SIEM solutions or other security tools. |
| Focuses on MTTD, false positive reduction, and log source coverage. | Focuses on MTTR, automation ROI, and playbook success rate. |
Does SOAR need a SIEM?
Technically no, but practically yes. While SOAR can ingest data from various security tools, it most commonly relies on a SIEM tool to provide high-fidelity alerts. Without a SIEM, a SOAR platform lacks a centralized source of analyzed event data.
Can SIEM and SOAR be integrated?
Yes, SIEM and SOAR are highly complementary and almost always integrated in high-end security environments. While SIEM identifies a potential threat through log correlation, it sends an alert to the SOAR platform via API. The SOAR then triggers a preconfigured playbook to investigate or remediate that specific alert across various security tools.
How do SIEM and SOAR work together?
SIEM and SOAR work together as a detection and remediation pipeline. SIEM acts as the analytical layer, and SOAR acts as the response layer. While SIEM generates alerts, SOAR ingests the alerts to execute remediation workflows and playbooks. This combined function helps neutralize threats at machine speed, reducing MTTR.
Does XDR replace SIEM and SOAR?
No. While XDR integrates detection and response across security layers, it does not replace SIEM or SOAR. Most organizations use them together to create a multi-layered, robust defense strategy. SIEM remains essential for long-term log storage, complex correlation, and regulatory compliance.
Conversely, SOAR provides advanced orchestration and custom playbooks to manage complex workflows across your entire security ecosystem. On the other hand, XDR focuses on deep, cross-vector threat detection and rapid response for specific attack paths such as email, cloud, and endpoint.
- What is SOAR?
- What is SIEM?
- Core capabilities of modern SOAR and SIEM
- SOAR vs SIEM - Which is right for you?
- Key differences between SIEM and SOAR
- Relationship between SIEM and SOAR - The synergy
- Strategic implementation: Advantages and limitations of SIEM and SOAR
- SIEM vs. SOAR decision matrix: Choosing the best tool
- How to choose the best SIEM and SOAR tools
- Frequently asked questions