Related content
In the current cybersecurity landscape, choosing between extended detection and response (XDR) and security information and event management (SIEM) isn't just a technical choice, but a strategic decision that should be based on your SOC needs. This page compares XDR and SIEM frameworks and implementation strategies to help you choose the right path for your SOC.
XDR vs. SIEM
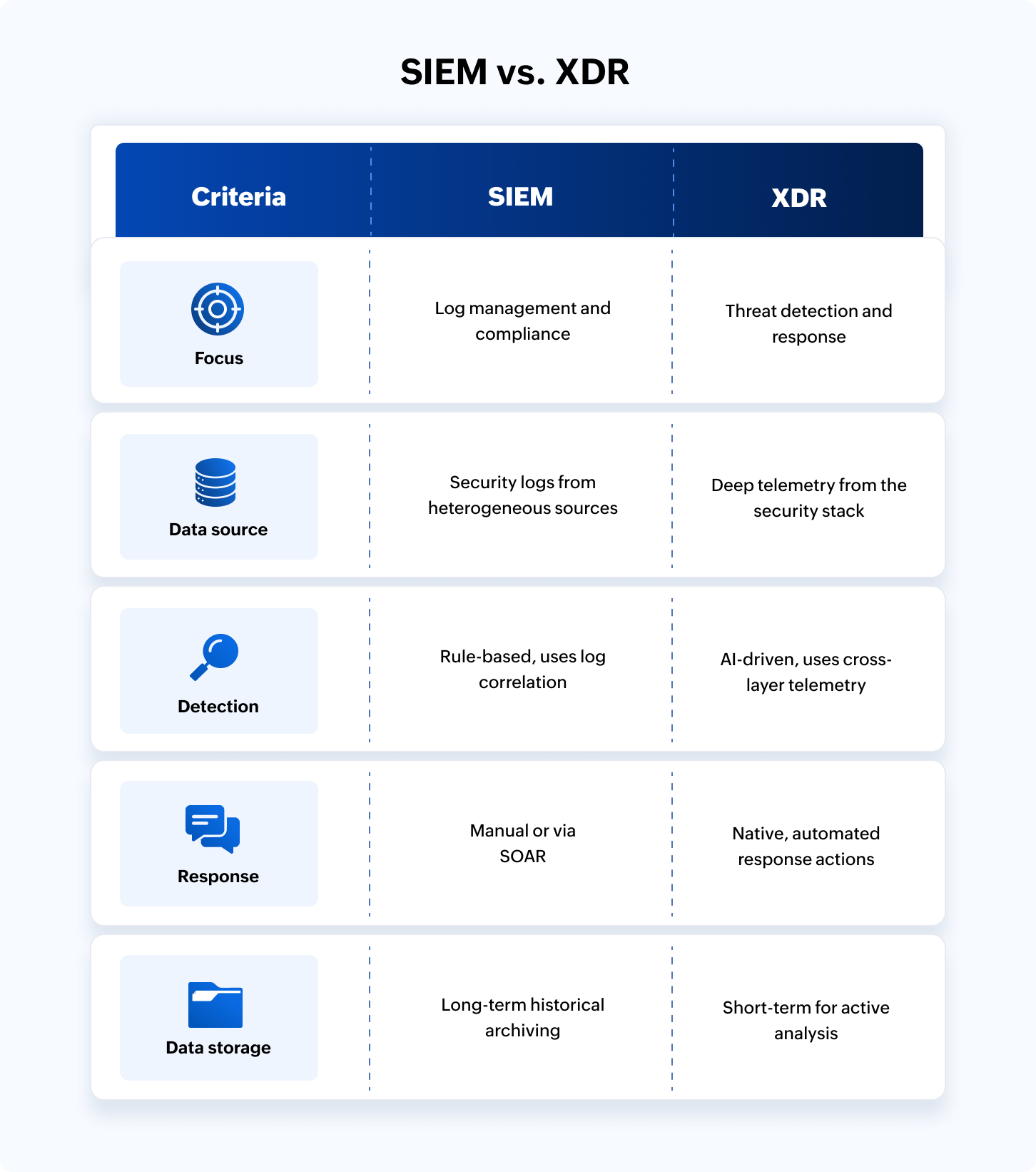
In today's threat landscape, the choice between SIEM and XDR depends on your security objective: visibility vs. velocity.
SIEM is a centralized data hub that excels at long-term log retention, complex compliance reporting (e.g., HIPAA, GDPR), and broad correlation across every corner of the network. It offers a historical data lake for deep forensic investigations and analysis.
XDR is an automated response tool that integrates deeply into specific security layers like endpoints, email, and cloud to correlate telemetry and neutralize threats in real time. It trades the broad, exhaustive logging of a SIEM for specialized, AI-driven speed and lower operational overhead.
What is XDR?
XDR is a unified security incident detection and response platform that automatically collects and correlates security data from across the network to detect threats and respond to them in near-real time. The primary advantage of XDR is the automated response. XDR doesn't just tell you there's a threat; it automatically executes a response to contain it.
How XDR works: Breaks down security silos by ingesting telemetry from endpoints, email, cloud, and network traffic into a unified console for better threat detection and response execution.
Why use XDR: To significantly reduce the mean time to respond (MTTR) by automating actions and playbooks.
What is SIEM?
SIEM is an SOC's single source of truth. It collects, parses, normalizes, and centrally aggregates log data from firewalls, servers, applications, cloud sources, endpoints, and even physical security devices to provide real-time security monitoring, threat detection, and long-term compliance reporting.
How SIEM works: Ingests massive amounts of data and processes it for threat detection, investigation, and compliance reporting. Modern SIEMs have evolved and now natively include AI-driven UEBA to reduce alert fatigue and SOAR for quicker threat response.
Why use SIEM: It's the gold standard for regulatory compliance and provides the historical data needed for visibility and post-breach investigations.
Related content
Core capabilities of XDR and SIEM
SIEM capabilities
| Centralized log monitoring | Real-time threat detection | Compliance reporting |
|---|---|---|
| SIEM acts as a universal log aggregator that ingests, parses, and normalizes data from hundreds of disparate sources into a standardized format. This centralization provides holistic security visibility across the network. | Using a powerful correlation and detection engine with predefined detection rules, SIEM identifies known signature-based attack patterns in real time. These detections serve as potential evidence during investigations. | SIEM automates audit-ready reporting for regulatory audits like HIPAA, the GDPR, and the PCI DSS. It generates prebuilt reports and maintains long-term, tamper-proof archives of all log data to ensure compliance. |
XDR capabilities
| Cross-layer correlation | Behavioral profiling | Detection and response |
|---|---|---|
| Unlike traditional tools that analyze log data in isolation, XDR correlates and associates raw telemetry across endpoints, networks, email, and cloud workloads to identify indicators of attack (IoAs) that lead to the attack kill chain. | Rather than relying on simple static rules, XDR uses machine learning to identify dynamic baselines that differentiate normal activity from malicious ones. This greatly helps in identifying zero-day threats and living off the land (LOTL) attacks. | Using AI-driven analytics, XDR identifies complex, multi-stage attack chains in real time. Its response is equally powerful, offering automated one-click remediation or rolling back unauthorized changes to neutralize threats at machine speed before they escalate. |
XDR vs. SIEM: Which platform is right for your SOC in 2026?
Choose XDR: If you need automated and integrated threat detection across endpoints, network, and cloud workloads with a smaller and more agile team.
Choose SIEM: If you are a large enterprise requiring comprehensive log management, historical data lakes, and strict regulatory controls (e.g., GDPR, HIPAA, NIS2, NIST) across your entire IT stack.
Key differences between XDR and SIEM tools
While both SIEM and XDR aim to detect and neutralize threats, the core difference lies in their operational philosophy: SIEM supports an enterprise-wide data strategy focused on visibility and compliance, while XDR supports a threat-centric detection and response strategy focused on speed and automation.
1. Data source: Telemetry vs. logs
XDR: Ingestion is high-fidelity, pulling deep, raw telemetry data, such as process command lines, API calls, and kernel-level events, from native sensors in the security stack. While it provides depth, it's often walled. Native XDR platforms such as Microsoft Defender and Palo Alto Cortex struggle with legacy systems or proprietary applications.
SIEM: Excels at collecting and normalizing logs from disparate sources including HRMS applications, ERPs (SAP), industrial IoT, in-house applications, and cloud workloads. This makes SIEM the ideal choice for organizations with complex, heterogeneous infrastructures and non-standard architectures.
2. Detection logic: IoC vs. IoA
XDR: Most XDR platforms prioritize behavioral detection over static rules. They leverage AI- and ML-based detection to identify active IoAs in the security stack rather than static indicators of compromise (IoCs). This allows XDR to better detect zero-day exploits and LOTL attacks that don't trigger traditional rule-based alerts. XDR platforms are now designed to eliminate alert fatigue—a top challenge with most SIEM implementations. They use AI to automatically stitch related security signals into a single, high-fidelity incident.
SIEM: Next-gen SIEM solutions rely on a high-precision correlation engine that processes logs against a library of prebuilt detection rules. These rules are often based on the MITRE ATT&CK® framework and help analysts detect IoCs at various stages of the attack kill chain. They also include ML-based behavioral analytics to identify slow attacks, advanced persistent threats, and subtle behavioral anomalies to detect threats early.
3. Incident response and automation: Native XDR vs. SIEM + SOAR
While both security platforms promise lower MTTR, their execution differs in terms of operational scope and integration depth.
Native XDR: Solutions like Microsoft Defender and Palo Alto Networks Cortex XDR are designed as closed-loop systems. They have in-depth automation because the platform owns the underlying sensors that collect data and execute responses. For example, if Microsoft Defender detects a malicious process linked to an email, it can natively kill the file, revoke the user's OAuth tokens, and quarantine the email across the entire M365 tenant instantly, without any third-party API calls. However, it's scope is strictly limited to Microsoft's ecosystem; it cannot natively reach to isolate an device on a different endpoint agent or block a port on a firewall that doesn't integrate with it.
SIEM: For enterprises with a heterogeneous stack, a SIEM solution with built-in SOAR capabilities is the standard for cross-vendor response implementation. For example, ManageEngine Log360 can coordinate a response that starts with a Fortinet firewall alert, triggers a scan in a third-party vulnerability manager, and then automatically blocks a compromised user in Active Directory. While this process requires managing API handshakes, it allows enterprises to automate security across their entire infrastructure, regardless of the vendors in their stack.
4. Forensics and retention: Long term vs. real time
XDR: Often known as the hunter's tool, XDR typically stores high-volume, performance-driven telemetry for a shorter window, ranging from 30 to 90 days. While XDR is engineered for rapid root cause analysis and immediate threat hunting, its limited retention period makes it less suitable for long-term compliance or investigating incidents that occurred in the past.
SIEM: SIEM tools are built for search at scale. They offer long-term, tamper-proof retention of audit logs required for multi-year compliance requirements. This helps in extensive forensic analysis and identification of root causes for complex and slow attacks.
Strategic implementation: Advantages and limitations of XDR and SIEM
XDR vs. SIEM is a choice between response speed and data governance. Below is the strategic breakdown of how these tools perform in real-world enterprise environments.
XDR implementation
XDR is designed for rapid, automated threat containment. It's the ideal choice for enterprises prioritizing MTTR with lean staffing.
| Advantages of XDR | Limitations of XDR |
|---|---|
|
|
SIEM implementation
SIEM serves as the central hub for your data. It's the strategic choice for compliance-heavy industries and enterprises with diverse technology stacks.
| Advantages of SIEM | Limitations of SIEM |
|---|---|
|
|
XDR vs. SIEM decision matrix
| Organization type | Strategic priority | Recommended solution |
|---|---|---|
| SME with a small IT or SOC team | Speed and automation | XDR |
| Bank, healthcare, or government agency | Compliance and governance | SIEM |
| Uses a multi-vendor stack | Interoperability (orchestration) | SIEM + SOAR |
| Uses a single platform | Ecosystem depth | Native XDR |
Trending in 2026: The hybrid SOC
Most mature enterprises no longer choose between SIEM or XDR. They implement an XDR tool for their front-line automated defense and feed high-fidelity alerts into a SIEM tool with native SOAR for global orchestration and long-term compliance. This creates a model that captures the speed of XDR with the governance of SIEM.
ManageEngine Log360: The ultimate bridge for your SOC
Log360 provides the agility of an XDR with the enterprise-wide authority of a SIEM. It's designed to scale with your organization—whether you stay in a single ecosystem or expand into a heterogeneous environment.
- For single-vendor ecosystems: If your organization is heavily invested in a single stack (e.g., Microsoft 365 or AWS), Log360 provides deep and native integration. It audits Active Directory changes, Microsoft Exchange, and Microsoft Entra ID with granular precision, delivering the same instant response and depth as a native XDR but with superior long-term forensic retention.
- For heterogeneous environments: Most modern enterprises are accidental hybrids, running a mix of legacy on-premises servers, multi-cloud platforms (e.g., AWS, Azure, GCP), and diverse security tools from different vendors. Log360 normalizes data from over 750 sources out-of-the-box, breaking down silos to provide a single, unified solution.
Explore ManageEngine Log360's SIEM and SOAR capabilities with a personalized walkthrough.
Frequently asked questions
What is the difference between XDR and SIEM?
SIEM focuses on centralized log management, long-term data retention, and compliance reporting across the entire enterprise. XDR is a more specialized on correlating telemetry from endpoints, networks, and cloud environments to provide faster automated detection and response.
| Feature | SIEM | XDR |
|---|---|---|
| Scope | Collects log data from sources across the network for threat detection, compliance, and long-term storage. | Focuses deeply on endpoints, email, and cloud to find and stop active attacks. |
| Detection | Identifies patterns across disparate logs using event correlation to trigger alerts. | Correlates telemetry from integrated tools to provide a unified story of an incident. |
| Response | Mostly passive and only generates alerts, whereas response requires a separate tool like SOAR. | Has built-in automation to kill malicious processes or isolate infected hosts instantly. |
What is the difference between XDR, SIEM, and SOAR?
SIEM aggregates and analyzes logs to detect events whereas SOAR provides the orchestration and playbooks to automate responses to those events. XDR unifies these capabilities, combining cross-layer detection with built-in SOAR-like automated response actions in a single, integrated platform.
Can XDR and SIEM be used together?
Yes, XDR and SIEM can be used together in order to achieve comprehensive visibility. High-performance SOCs deploy XDR for granular telemetry correlation and incident response to neutralize threats, while utilizing SIEM as a centralized data lake for cross-vendor log aggregation, complex forensic auditing, and long-term regulatory compliance archival.
SIEM vs. XDR: Which should I choose?
Choose SIEM if you need centralized logging for compliance and broad visibility across the entire enterprise, including legacy systems. Choose XDR if you prioritize deep, automated detection and response across specific vectors like endpoints and cloud.
Which solution is better for a small SOC team?
XDR is generally better for small teams. It offers out-of-the-box integration, high-fidelity alerts, and automated response capabilities that reduce manual triaging. While SIEM is powerful, it often requires significant engineering resources to tune rules and manage data ingestion, which can quickly overwhelm a lean team focused on immediate incident response.
Is open XDR the same as a SIEM with SOAR?
Not exactly, though they overlap. Open XDR focuses on unifying telemetry from various third-party security tools into a single detection engine. A SIEM with SOAR collects all logs (security and non-security) and uses playbooks to automate workflows. Open XDR is more about integrated threat detection, while SIEM with SOAR is a broader platform for data management and orchestration.
Does XDR help with regulatory compliance?
XDR helps, but it isn't a total solution. It provides the audit trails and incident reporting required by frameworks like the GDPR or HIPAA. However, many regulations require long-term log retention (often years), which is a core SIEM strength. While XDR proves you can detect breaches, you’ll likely still need a SIEM for comprehensive compliance archiving.
Is XDR replacing SIEM?
Not entirely. While XDR is replacing SIEM for active threat detection and response due to its superior speed, SIEM remains essential for broad compliance, deep forensic history, and non-security log auditing. Many modern organizations now use both as complementary solutions.
- What is XDR?
- What is SIEM?
- Core capabilities of XDR and SIEM
- XDR vs. SIEM: Which platform is right for your SOC in 2026?
- Key differences between XDR and SIEM tools
- Strategic implementation: Advantages and limitations of XDR and SIEM
- XDR vs. SIEM decision matrix
- Trending in 2026: The hybrid SOC
- ManageEngine Log360: The ultimate bridge for your SOC
- Why Log360 wins in 2026
- Frequently asked questions