Related content
The evolution of SOAR: From standalone to native ecosystem capability
To understand how SOAR functions in 2026, we must first recognize a fundamental industry shift: SOAR is no longer just a standalone solution. While dedicated platforms still exist for high-maturity environments, SOAR has largely evolved into a native capability embedded directly within next-gen SIEM and XDR platforms. SOAR tools are more commonly integrated with SIEM and XDR tools in a SOC environment. It sits above the enterprise security stack, coordinating disparate tools into a unified, high-speed defense system. Industry analysts also confirm that this convergence is an architectural necessity.
Gartner highlights in its Hype Cycle for Security Operations report that as the standalone SOAR market matures, its core value is being absorbed by broader security operations platforms to provide unified analyst experience.
How SOAR works: The modern architecture
Despite its shift towards integration, the mechanics of a SOAR engine still operate through three distinct functional layers. The layers of the SOAR engine work in parallel and follow a logical progression: orchestration connects tools, automation executes the logic, and response manages the final outcome .
Security orchestration: The integration layer
The security orchestration layer is the connective bridge of a modern SOC and relates to how the SOAR platform connects and coordinates hardware and software tools in an enterprise ecosystem.
In a typical environment, analyst monitor threats use a fragmented array of solutions like firewalls, threat intelligence feeds, and endpoint protection tools, that often come from different vendors and lack native integration. SIEM tools provide visibility into what's happening in each environment by correlating the security telemetry. The security orchestration function of SOAR brings them together to execute a response through APIs, prebuilt plugins, and custom integrations.
These unify the tools and provide a coherent system to execute a threat response. By providing a centralized hub, orchestration allows data to flow seamlessly between tools, ensuring that an analyst investigating a phishing email no longer has to manually copy-paste indicators between a secure email gateway and a threat intelligence platform.
Security automation: The execution layer
Security automation is the process of defining and implementing a predetermined course of action that executes automatically in response to specific security events or incidents. This layer replaces manual, repetitive work with programming efficiency through the use of playbooks.
Playbooks are digital process maps that outline the exact steps of standard security procedures for threat remediation and triaging. These playbooks can be:
- Fully automated: Handling low-level, high-volume tasks (like checking IP reputations) in milliseconds.
- Semi-automated: Executing the bulk of an investigation but pausing for a human-in-the-loop approval before taking a critical action like shutting down a server.
- Fully-manual: Guiding an analyst through a complex, non-linear investigation with a checklist of best practices.
Together, orchestration and automation layers proactively reduce alert fatigue, and enable the SOC team to focus on high-priority incidents that require human analysis and intervention.
Once SOAR receives an alert on a potential brute-force attack, it triggers a playbook that executes the below automated workflow to mitigate the threat in real-time. Here's how a typical brute force investigation playbook works:
- Reputation check: Automatically queries threat intelligence feeds to check the reputation of the source IP address.
- Correlation: Verifies the logs to confirm multiple failed login attempts from the same IP or targeted user within a specific timeframe.
- Process analysis: Checks the reputation of the specific process that attempted the logon to identify known malicious tools.
- Risk scoring: Validates the current risk scores for the host and the user to see if this fits a pattern of compromised behavior.
- IP blocking: If the source IP is determined to be malicious, automatically updates firewall or EDR rules to block the IP.
- Process termination: If the logon process itself is flagged as malicious, the playbook instantly terminates and quarantines the file.
- Privilege assessment: Checks whether the targeted user account holds administrative privileges.
- If the user is an administrator: Escalates the incident severity to High or Critical and alerts the SOC lead immediately.
- If the user is a standard user: Proceeds with account containment.
- Account containment: Disables the user account to prevent further access.
- Session management: Terminates active sessions associated with the affected user.
- Credential security: In Active Directory environments, expires the user’s password to force a reset upon their return.
- Threat hunting: Triggers a Microsoft Defender (or equivalent EDR) scan on the host to check for other hidden malicious processes.
- Host isolation: If additional malicious processes are discovered during the scan, the playbook terminates those processes and isolates the host from the network to prevent lateral movement.
Security response: The management layer
The security response layer is the command and control center where orchestration and automation culminate in action. Once a threat is identified and the automated steps are executed, the response layer provides the framework for final resolution and documentation.
This layer focuses on case management and remediation. It aggregates enriched data and forensic evidence, allowing multiple analysts to collaborate on a single incident in real time. Key functions include:
- Containment: Automatically or manually isolating infected endpoints or revoking compromised user credentials.
- Post-incident analysis: Generating immutable audit logs and reports to ensure compliance with regulations like the GDPR or SOC2.
- Continuous improvement: Using incident data to refine playbooks, ensuring the SOC becomes faster and more accurate with every threat it neutralizes.
SOAR working mechanism
A SOAR tool involves the following set of mechanisms for effective incident response and remediation.
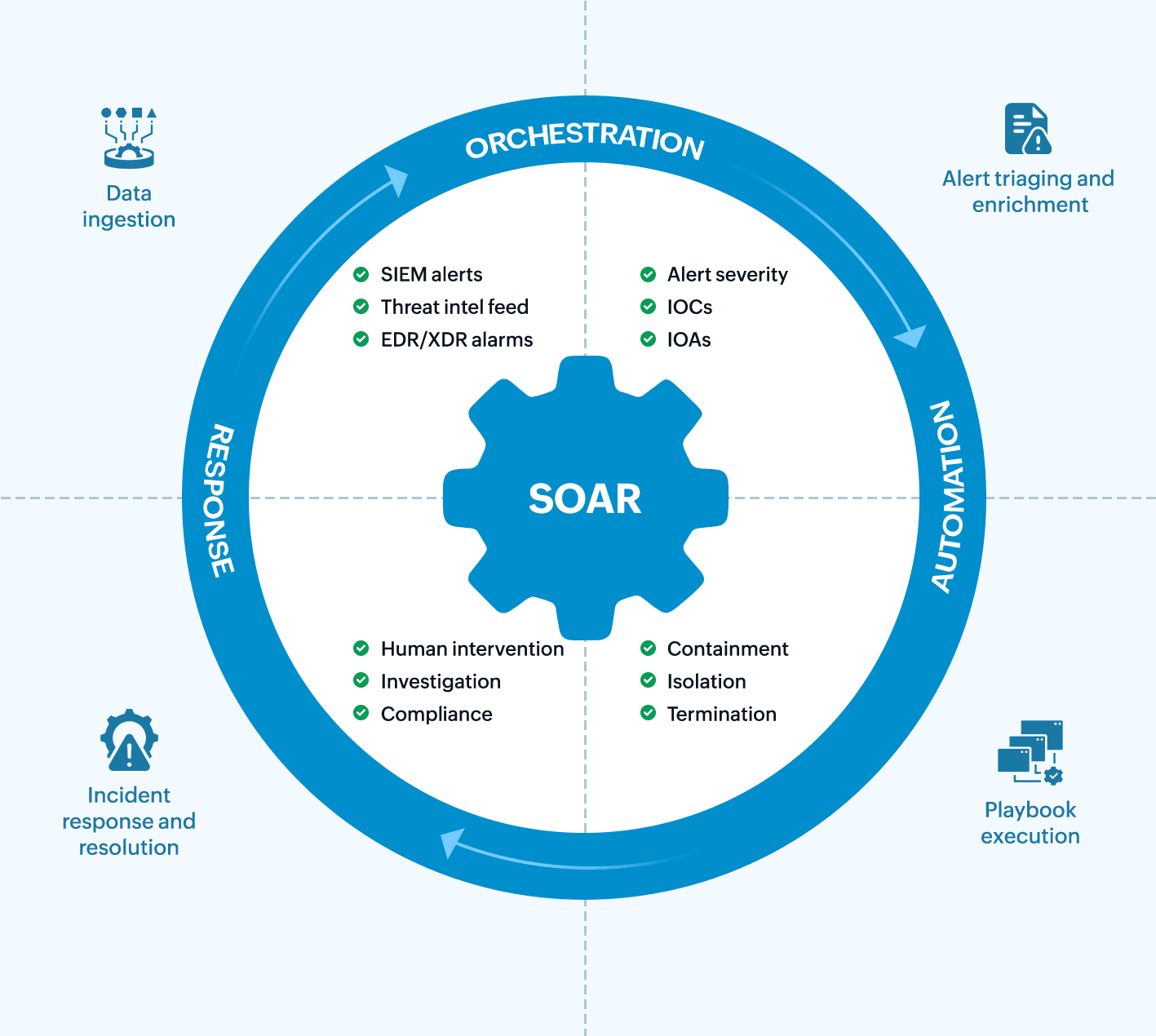
1. Data ingestion
This is the initial stage where the SOAR platform collects raw security data and alerts from various sources. The SOAR software uses APIs and connectors to pull or receive alerts from the security infrastructure which include SIEM tools, EDR or XDR solutions, threat intel feeds, firewalls and intrusion detection and prevention systems. This step aggregates disparate alerts and detections into the central SOAR security solution.
2. Alert triaging and enrichment
Once an alert is ingested, the system automatically begins to determine its legitimacy and gather the necessary context to arrive at the action plan. The system applies basic logic to filter out known false positives for triaging and then correlates external and internal data to add context to the IOCs found in the alert. It automatically queries threat intelligence services for reputation data on IP addresses, URLs, and file hashes and also audits internal logs to determine the user associated with an infected host or device.
3. Playbook execution
Based on the criteria and context gathered during the enrichment phase, the SOAR platform executes a defined, automated workflow using the response playbook. The playbook executes a sequence of actions across multiple security tools simultaneously to contain the incident.
For instance, if a malicious IP is confirmed, the playbook automatically blocks the IP on the firewall. Similarly, when a phishing email is confirmed, the playbook automatically searches mailboxes for the email and quarantines it to prevent attack propagation.
4. Incident management and resolution
This is the final stage, which involves both automated and manual actions to resolve the incident, document the workflow, and revive the systems to normal operations.
It involves generating a detailed incident report of all automated actions and evidence and updating the incident ticket with the resolution status.
SOAR use case framework: Real-world scenarios for orchestration, automation, and response
| SOAR architectural layer | Core functional goal | Real-life scenario | Operational impact (MTTR) |
|---|---|---|---|
| Security orchestration | The connector: Unifying the IT and security stack into a single ecosystem. | Contextual signal unification: A user logs in from an impossible travel location (for example, London then Tokyo in one hour). The engine orchestrates a check between Azure AD/Okta logs, HR systems (to see if the user is on vacation), and dark web feeds (to see if their password was recently leaked). | Eliminates data silos: Unifies identity, location, and threat intelligence into a single alert without manual lookup. |
| Security automation | The investigator: Executing logic-based playbooks to handle high-volume triage. | Automated identity verification: A playbook triggers an Adaptive MFA Challenge. If the user fails the MFA or if the risk score is too high, the playbook automatically scans the user's recent file access logs in SharePoint or OneDrive to check for bulk data downloads (data exfiltration). | Machine-speed triage: Replaces manual "did you log in?" emails with instant, programmatic verification and behavioral analysis. |
| Security response | The terminator: Managing the incident life cycle and final remediation actions. | Enforced zero-trust remediation: The engine executes a global kill-switch which terminates all active web sessions, disables the user account in Active Directory, and wipes the corporate email profile from the user’s mobile device via mobile device management. | Surgical containment: Stops an active breach in milliseconds, preventing lateral movement or a full-scale ransomware deployment. |
Benefits of security orchestration and automation
Here are some of the key benefits of leveraging a SOAR software for incident management.
Reduce MTTR and increase response accuracy
SOAR leverages automation to execute investigation and containment actions across multiple security tools simultaneously and instantly. This reduces the MTTD and MTTR, and minimizes the impact of breaches. It also eliminates human error in threat investigation, ensuring consistent response to every threat.
Optimizing analyst efficiency and productivity
SOAR automates triage, data enrichment, and containment for high-volume, low-severity alerts, effectively combating alert fatigue. This allows human analysts to focus their expertise on complex, high-priority threats, threat hunting, and playbook refinement, thereby increasing the SOC team's overall productivity.
Standardizing security processes
Playbooks enforce a consistent, organization-wide approach to handle specific threats, ensuring the same effective procedure is followed when an alert is triggered. This standardization supports compliance, simplifies training for new team members, and enables the security team to audit its response protocols for maximum effectiveness.
SIEM vs. SOAR
The table differentiates SIEM and SOAR.
| Criteria | SIEM | SOAR |
|---|---|---|
| Focus | The primary goal of a SIEM tool is threat detection and analysis. | SOAR solutions focus on automation and response. |
| Core function | Aggregates, normalizes, and correlates massive volumes of log data to identify threats. | Automates the execution of incident response workflows across various security tools. |
| Input | Raw log data and security events from network devices and third-party integrations. | High-fidelity alerts generated by SIEM solutions or other security tools. |
| Output | High-fidelity alerts and security incidents. | Execution of a response workflow for incident containment. |
| Impact on time | Reduces MTTD by filtering noise and flagging threats. | Reduces MTTR by executing actions instantly. |
SOAR implementation challenges
While SOAR delivers significant benefits, SOC teams often encounter various bottlenecks during its implementation. Here are some common challenges faced during SOAR deployment:
Integration complexity
Connecting SOAR platforms with existing security tools can be technically tedious. Legacy systems might lack modern APIs, requiring custom connectors or middleware solutions to integrate with SOAR. It is crucial to verify the native integration support before selecting a SOAR solution.
Playbook development and maintenance
Creating effective playbooks requires deep understanding of both security operations and the organization's specific infrastructure. Playbooks also require ongoing maintenance as threats evolve and tools change. Therefore, SOC teams are supposed to allocate dedicated skilled personnel and resources for playbook governance and management.
Managing and organizing playbooks becomes challenging as threats evolve. Without proper documentation and version control, playbooks might be duplicated, which can result in overlapping actions. It is necessary to implement a playbook library with clear naming conventions and regular audits to prevent such issues.
False positive management
Automated responses to false positives can disrupt business operations and create unnecessary noise. This also impacts SOC efficiency and productivity. It is important to fine-tune alert thresholds and incorporating validation steps into playbooks before enabling fully automated responses.
Strategic SOAR buying guide: How to choose the right SOAR solution in 2026
In 2026, the value of a SOAR platform is measured by its automatability surface, the percentage of your security and IT stack it can actually control without manual intervention. Therefore, you should prefer a tool that focuses on intelligent-driven capability rather than just a library of static integration.
1. Integration and ecosystem compatibility
A SOAR tool's primary job is to orchestrate existing tools and, therefore, its ability to integrate with the current security stack is non-negotiable. The platform should provide out-of-the-box, bidirectional integration support for primary security tools such as SIEM, EDR/XDR, threat intelligence platforms, firewalls, and ticketing systems. It is also crucial for the tool to possess the API-first architecture because this enables a custom integration if the third-party tool does not have a native connector.
2. Playbook customization: Beyond static logic
Modern threats bypass rigid "if-then" rules. Your SOAR solution should provide dynamic playbooks that adapt in real time. Look for a SOAR solution that has:
- Prebuilt playbooks: The tool should include a rich library of prebuilt playbooks and connectors for common use cases such as phishing, malware, and vulnerability management.
- Low-code/no-code canvas: Apart from the playbook library, the platform should also feature an intuitive, visual drag-and-drop builder for creating, testing, and modifying workflows for tier-1 analysts. Look for a solution that provides a blueprint approach that treats incidents as multi-layered workflows rather than a simple linear flow chart.
- Reusable components: Look for nested playbooks that provide the ability to build a standard "isolate host" block once and reuse it across 50 different attack scenarios including phishing, malware, and unauthorized login.
- Versioning and rollback: Confirm that you can test a new version of a playbook in a sandbox before pushing it to live production.
- Human-in-the-loop (HITL) gates: Ensure you have the ability to pause a playbook during high-risk actions, like a server shutdown using, for example, an "Approve/Reject" button on a mobile app.
3. AI and agentic integration capabilities
The SOAR solution should provide AI-assisted investigation capabilities that include natural language queries and recursive reasoning to uncover root causes beyond static scripts. The AI-based triage should be able to prioritize alerts based on business context and historical patterns, not just severity scores. Also, AI agents can suggest or execute end-to-end responses by dynamically adapting playbooks to real-time threat evolution.
4. Case management and reporting
The tool should consolidate all ingested alerts, enriched data, and executed automated actions into a single, comprehensive incident case record. It should also include customizable dashboards that can display key performance indicators such as MTTD, MTTR, and overall alert volume reduction.
How to choose SOAR solutions: 2026 evaluation criteria
| Capability pillar | The legacy question | The 2026 SOAR strategic evaluation question | Why it matters for your enterprise |
|---|---|---|---|
| Agility and change | Does it have a connector for my EDR? | How hard it is for me to switch this playbook to a new EDR provider next year? | Prevents vendor lock-in. A modern SOAR should allow you to integrate with different vendors and swap tools by updating a single connection object. |
| Automation barrier | Does it support Python for custom scripting? | Can a Tier-1 analyst modify this logic without waiting for a developer? | High-code SOARs create bottlenecks. No-code/low-code platforms democratize automation so your frontline t eam can pivot at the speed of the threat. |
| Intelligence gap | Does it integrate with threat intelligence feeds? | How does the AI handle a signal it has never seen before? | Static playbooks fail against zero-days. You need Agentic AI that can autonomously reason out, suggesting new investigation steps based on context rather than just following a preset script. |
| Execution reality | Can it automatically block an IP address? | What happens when the Firewall API is down during an active attack? | Reliability is everything. Your SOAR must have native retry logic and failover paths to ensure critical containment actions aren't lost to a transient network error. |
| Human synergy | Does it have an "Approve" button?" | Can our manager approve a high-risk action via mobile app in under 10 seconds? | Friction kills response time . Human-in-the-loop g ates must be seamless and mobile-native so that manager approval doesn't become a 30-minute delay. |
| Hidden costs | What is the annual licensing fee? | What is the total effort (hours) to maintain these playbooks over 12 months? | The hidden tax of SOAR is playbook drift. If you spend more time fixing broken automations than investigating threats, th e total cost of ownership i s too high. |
Explore ManageEngine Log360's SIEM and SOAR capabilities with a personalized walk-through.
Frequently asked questions
What is SOAR?
Security orchestration, automation, and response (SOAR) is a cybersecurity tech stack that integrates siloed security tools via API-centric orchestration to automate investigation and response. It transforms manual triage into machine-speed response, acting as the critical link between detection and remediation to minimize the mean time to respond (MTTR).
What is a playbook in SOAR?
A playbook is a predefined workflow that executes a structured sequence of response actions in response to security incidents and threats. It acts as the automation and response component of the SOAR platform that helps with neutralizing threats at machine speed, reducing the MTTR.
How does SOAR reduce alert fatigue?
SOAR reduces alert fatigue by automating the triage process by filtering out false positives and aggregating related events into a single case. By handling repetitive, low-level tasks via playbooks, it ensures analysts only focus on high-priority threats that require human intervention.
Can I use SOAR if I have tools from different vendors?
Yes. SOAR platforms are designed to be vendor-neutral. They use API integrations and prebuilt connectors to orchestrate workflows across diverse security stacks, allowing tools from different providers to communicate and work together seamlessly in a unified interface.
What is SOAR in cybersecurity?
In cybersecurity, SOAR stands for security orchestration, automation, and response. It is a cybersecurity solution that helps various security tools and platforms collaborate and automate processes that help respond to security incidents promptly. It helps security teams manage and respond to threats more efficiently, streamlining the entire incident response process.
What is security automation and response?
Security automation and response involves the execution and automation of predefined workflows in response to security incidents. It primarily aims to automate the response workflows with minimal human intervention. This speeds up processes like threat investigation and containment, allowing security teams to handle more incidents faster, thereby lowering the MTTR.
What is the difference between SIEM and SOAR?
The main difference between security information and event management (SIEM) and SOAR is that SIEM primarily focuses on log collection and analysis, whereas SOAR focuses on incident response. SIEM correlates security incidents to generate alerts that serve as the input for SOAR. SOAR ingests the alerts from SIEM and automates the actions needed to respond to the alert and remediates the threat.
What is the difference between security orchestration and security automation?
Security orchestration is the process of coordinating and managing multiple security tools in order to attain centralized security insights. Whereas, security automation focuses on making a single task or incident workflow run on its own with minimum or no human intervention to achieve swift and efficient incident response.
Can XDR and SIEM be used together?
Yes, XDR and SIEM can be used together in order to achieve comprehensive visibility. High-performance SOCs deploy XDR for granular telemetry correlation and incident response to neutralize threats, while utilizing SIEM as a centralized data lake for cross-vendor log aggregation, complex forensic auditing, and long-term regulatory compliance archival.
- The evolution of SOAR: From standalone to native ecosystem capability
- How SOAR works: The modern architecture
- SOAR use case framework: Real-world scenarios for orchestration, automation, and response
- Benefits of security orchestration and automation
- SIEM vs. SOAR
- SOAR implementation challenges
- Strategic SOAR buying guide: How to choose the right SOAR solution in 2026
- How to choose SOAR solutions: 2026 evaluation criteria
- Frequently asked questions