Direct Inward Dialing: +1 408 916 9892
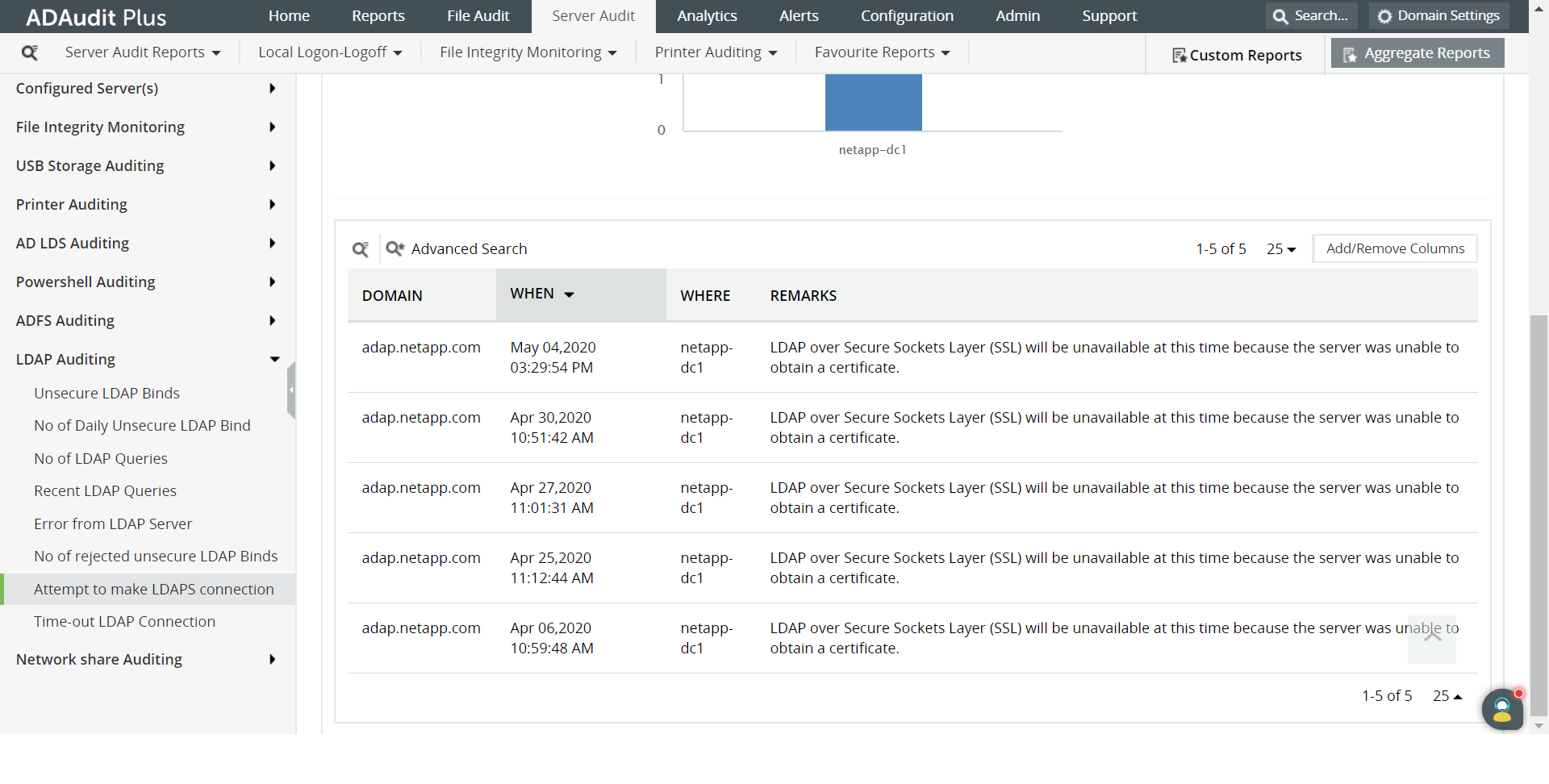
Login to ADAudit Plus web console as an administrator.
Navigate to the Server Audit tab and from the LDAP Auditing section in the left pane, select the Attempt to make LDAP connection report.
In the top right corner, select the Domain from the drop-down list and click Generate.
Select Export As to export the report in any of the preferred formats (CSV, PDF, HTML, CSVDE and XLSX).
Open Group policy management console.Create a new GPO and edit it -> Computer configuration -> Policies -> Windows Settings -> Security Settings -> Local Policies -> Audit Policy:
Audit Account Management -> Check the box for Success
Audit Directory Service Access -> Check the box for Success
Click Apply.
Navigate to Security Settings Level ->
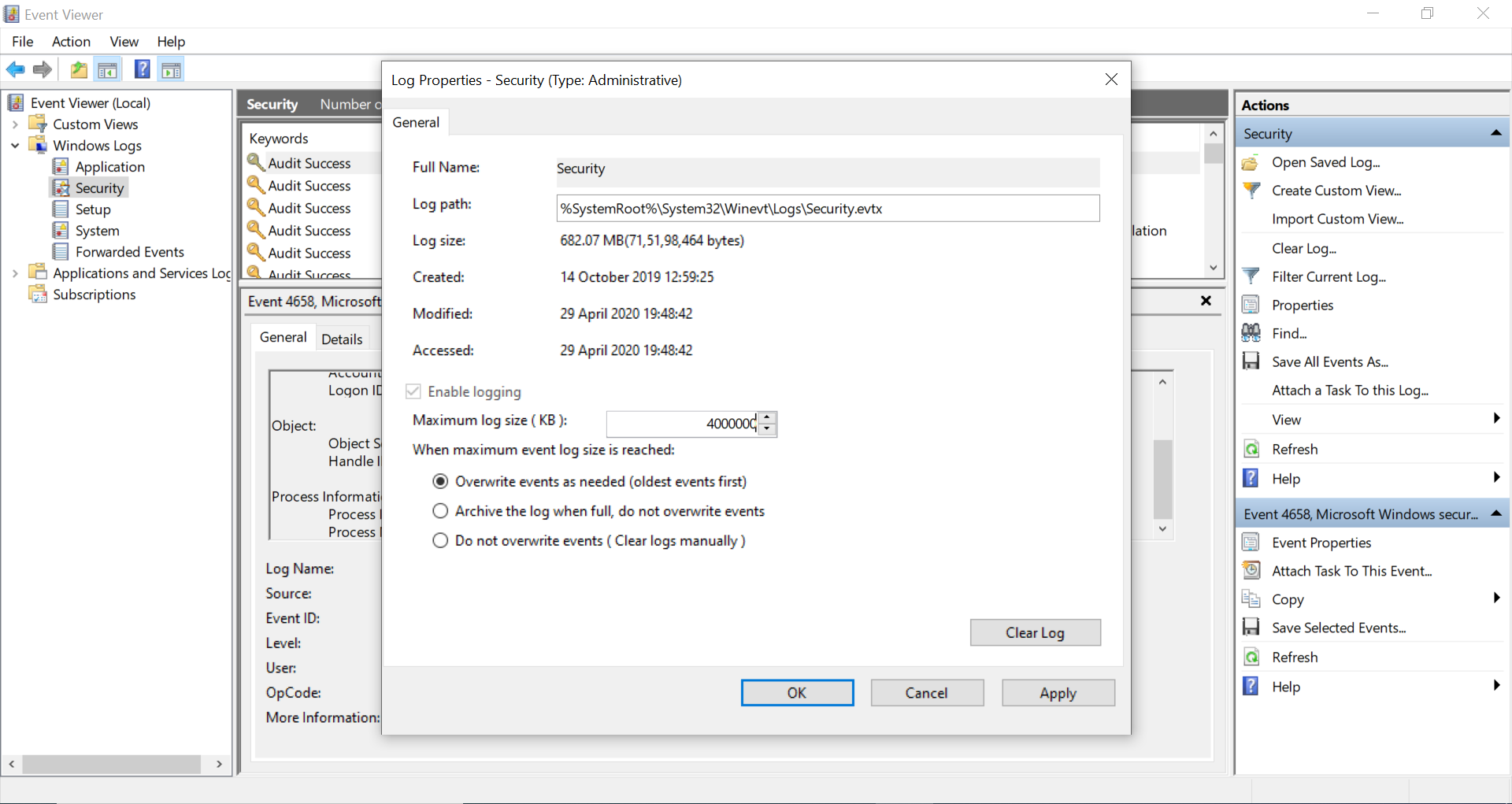
Properties -> Event Log:
Maximum security log size -> Define to 4,000,000 KB (or 4 GB)
Retention method for security log -> Define to Overwrite events as needed
Link the new GPO: Navigate to "Group Policy Management" -> Right-click domain or OU -> Click "Link an existing GPO" -> Choose the newly created GPO
Force the group policy update: In "Group Policy Management", right-click the defined OU -> Choose "Group Policy Update"
Open ADSI Edit -> Right-click ADSI Edit -> Connect to Default Naming Context -> Right-click DomainDNS object with your domain name -> Properties -> Security -> Advanced -> Auditing -> Add Principal "Everyone" -> Type "Success" -> Applies to "This object and descendant objects" -> Mark all checkboxes except "Full Control, List Contents, Read all properties, Read Permissions" -> Select "OK"
Configure LDAP:
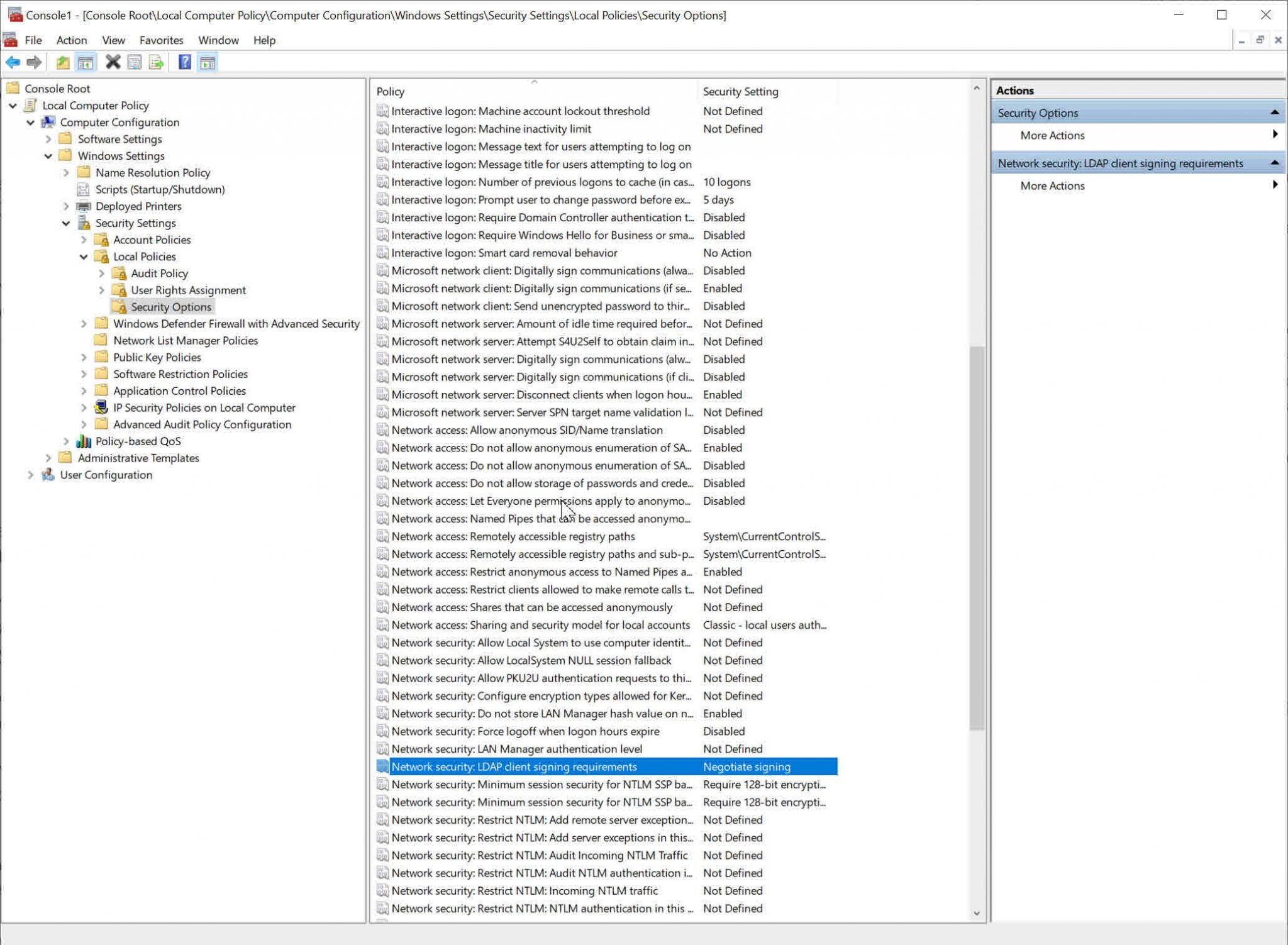
For server LDAP signing,
Domain controller: Go to Computer configuration -> Windows Settings -> Security Settings -> Local Policies -> Security options -> LDAP server signing requirements
For client LDAP signing,
Network security: Go to Computer configuration -> Windows Settings -> Security Settings -> Local Policies -> Security options -> LDAP client signing requirements
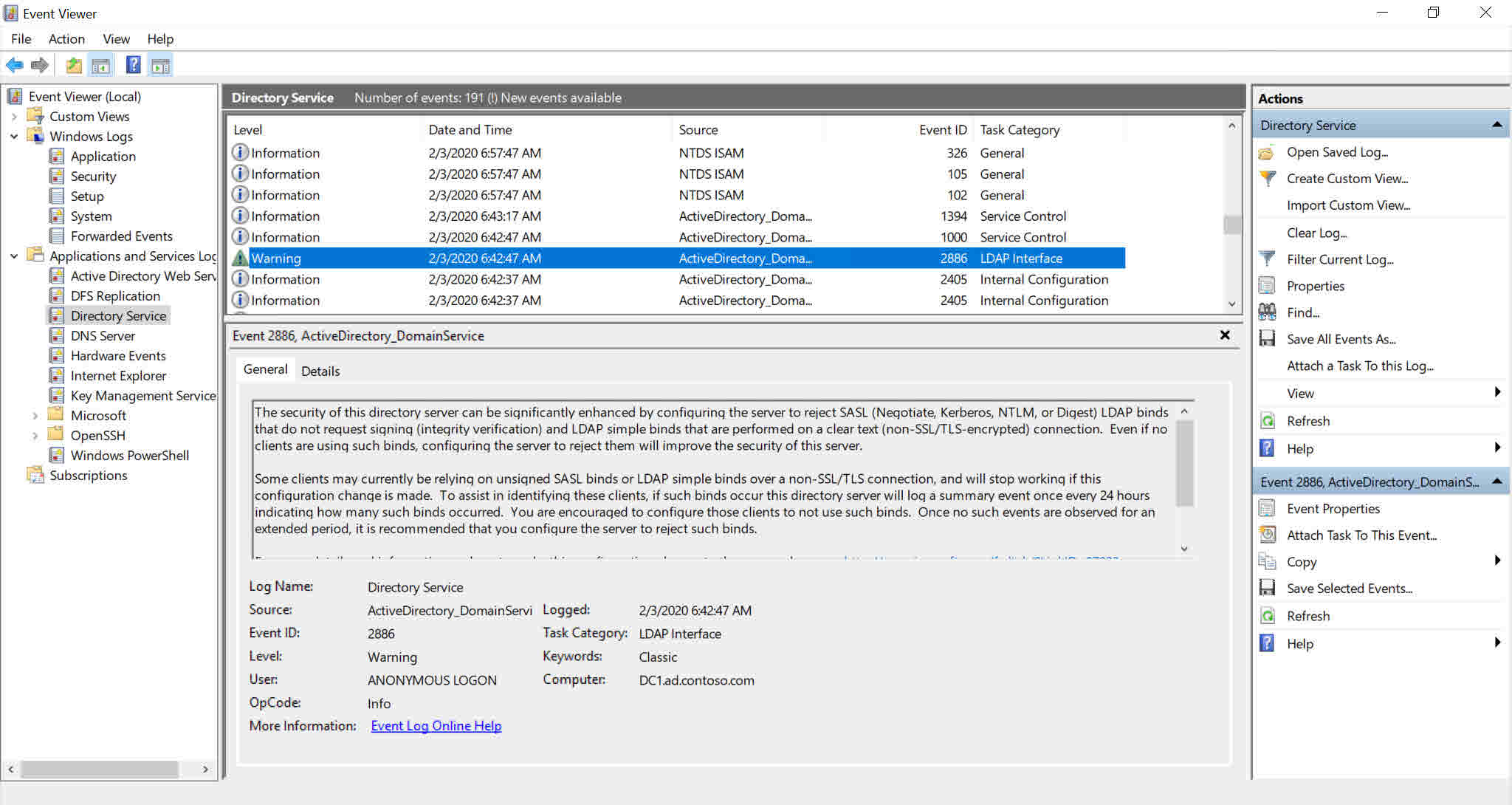
Open Event viewer -> Filter Security log to locate event IDs (Windows Server 2003/2008-2012):
2886: LDAP signing is not enabled in the domain
2887: Successful unsigned binding
Native auditing becoming a little too much?
Simplify LDAP auditing and reporting with ADAudit Plus.
Get Your Free Trial Fully functional 30-day trialHere are some of the limitations to generate a report to test LDAP connection in Active Directory using native auditing:
With ADAudit Plus, it is easy to obtain a report of LDAP connection tests in Active Directory in just a few clicks. The details like when the LDAP bind occurred, and from which domain, are displayed in a simple and intuitively designed UI.