Direct Inward Dialing: +1 408 916 9892
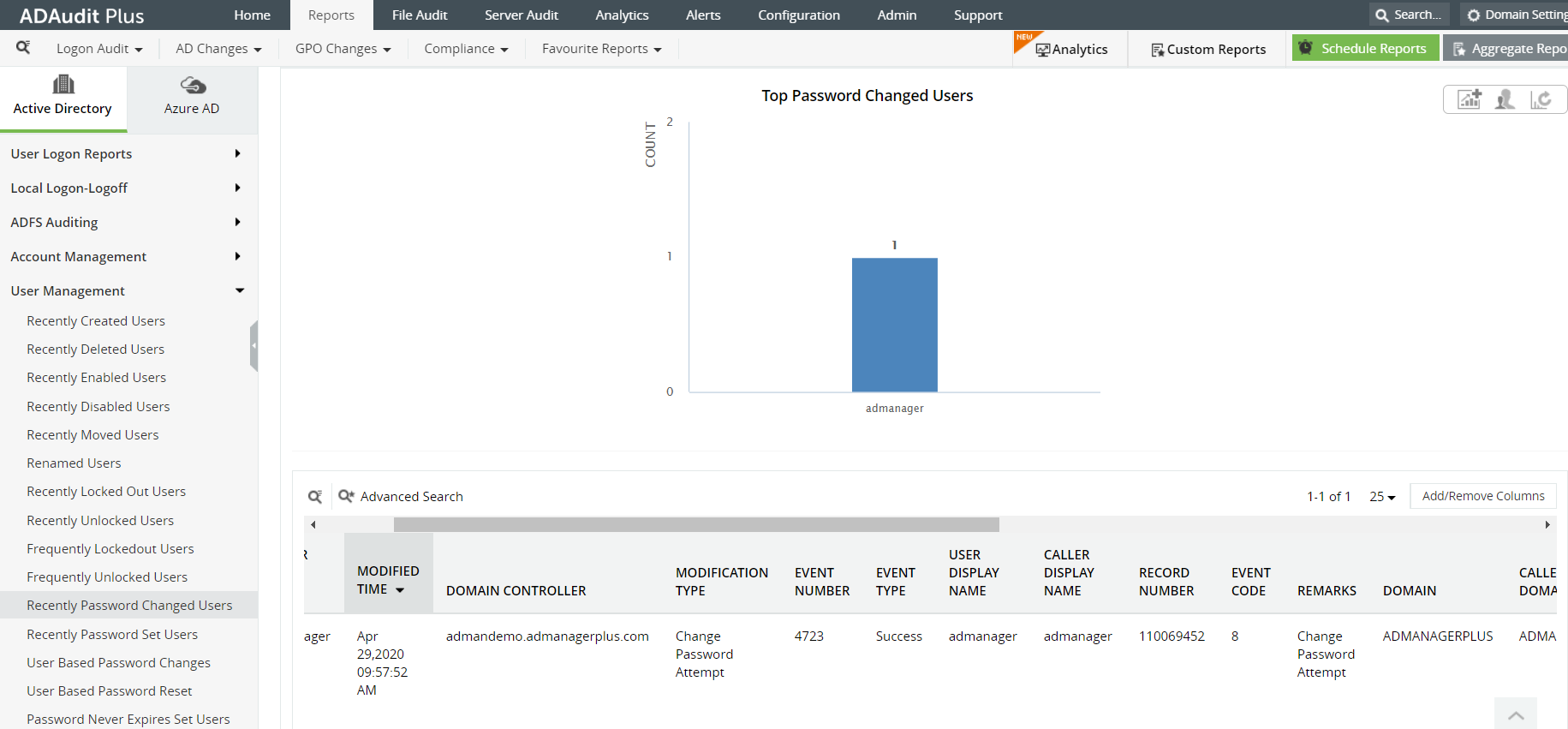
In the ADAudit Plus console, you can find password related reports under 'Reports'----> 'User Management'. You can access the 'Recently Password Changed Users' and 'Recently Password Set Users' to view password change or reset attempts.
Advanced search functionality offers you multiple filter attributes to look for a specific event.
Easily export your reports in CSV,HTML,PDF and XSL formats.
Correlate between other user management and computer management reports to spot anomalous behavior on the network.
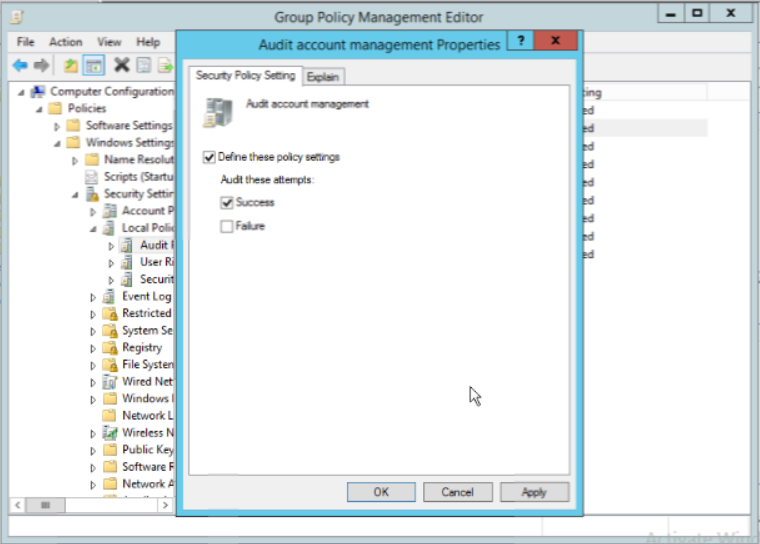
Launch the 'Server Manager' and open the Group Policy Management Console (GPMC).
In the left pane, expand the 'Forest' and 'Domains' nodes to reveal the specific domain you want to track the changes for.
Expand the domain and right click 'Default Domain Policy'. You can also choose a domain policy that is universal throughout the domain, or create a new GPO and link it to the Default Domain Policy.
Click on 'Edit' of the desired group policy, to open up the Group Policy Management Editor.
Expand 'Computer Configuration'--->Policies---->Windows Settings----->Security Settings----->Local Policies------->Audit Policies.
Enable 'success' and 'failure' options for 'Audit account management' properties. Exit Group Policy Management Editor.
In the GPMC choose the modified GPO, and click 'Add' in the 'Security' section on the right pane. Type 'everyone' in the text box and click 'Check Names' to include the value. Exit the GPMC.
To enforce these changes throughout the domain run the command 'gupdate /force', in the "Run" console.
From your Server Manager go to Tools and select ADSI Edit.
Right click ADSI Edit node from the left pane and select Connect to option. This pulls up the Connection Settings window.
Select the Default Naming Context option from the Select a well-known Naming Context drop down list.
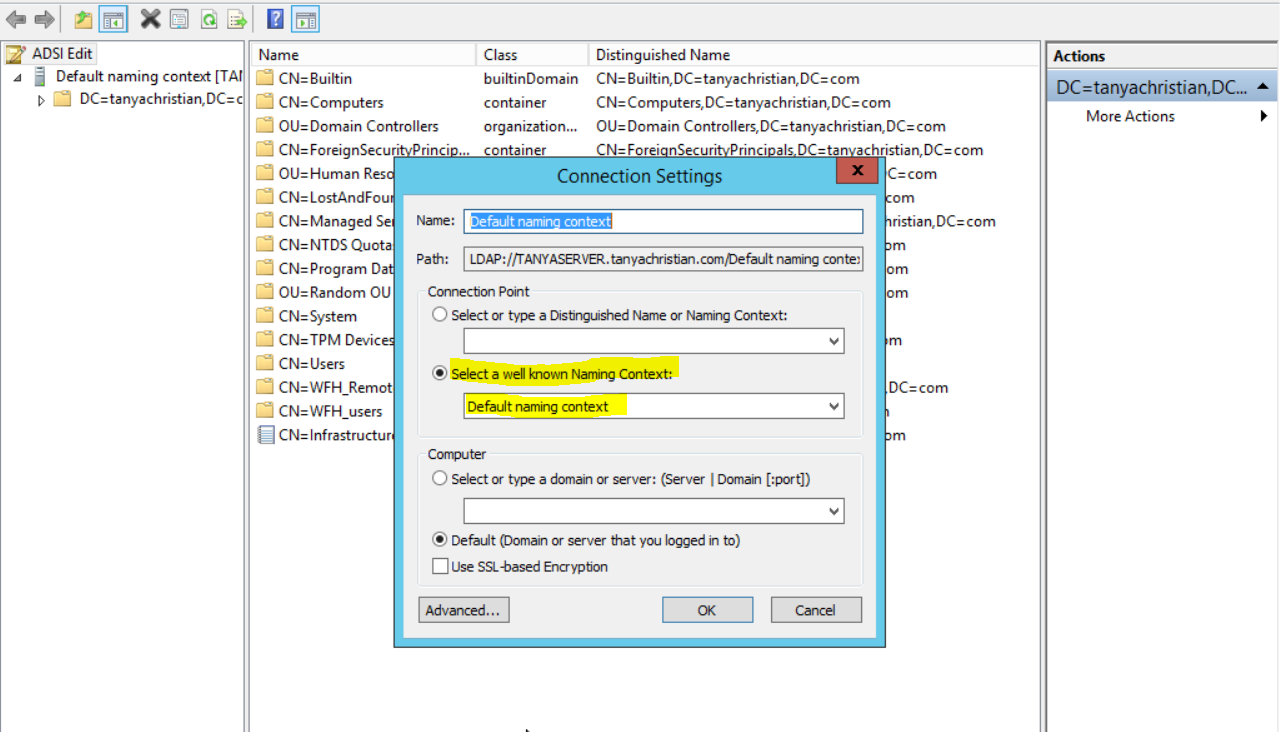
Click Okay and return to the ADSI Edit window. Expand Default Naming Context and select the associated 'DC' subnode. Right click this subnode and click 'Properties'.
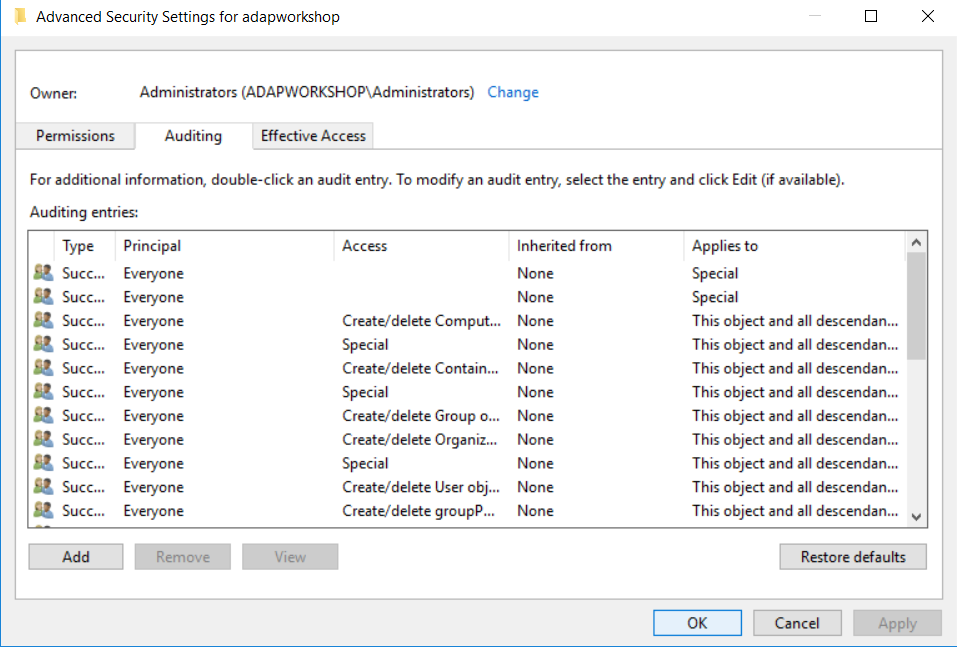
In the Properties window, go to the Security tab and select Advanced. After that select Auditing tab and click Add.
Click on Select a principle. This will bring up a Select User, Computer or Group Window. Type 'Everyone' in the textbox and verify it with Check Names.
The principle in the Auditing Entry window now shows 'Everyone'. In the 'Type' drop-down select All to audit for both 'success' and 'failure' events.
In the Select drop-down choose This object and all descendant object's. This allows the auditing of the OU's descendant objects. Select Full Control in the 'Permissions' section.
This selects all the checkboxes available. Unselect the following check boxes:
Full Control
List Contents
Read all properties
Read permissions
Open the Event Viewer and access the 'Security Logs' from 'Windows Logs'.
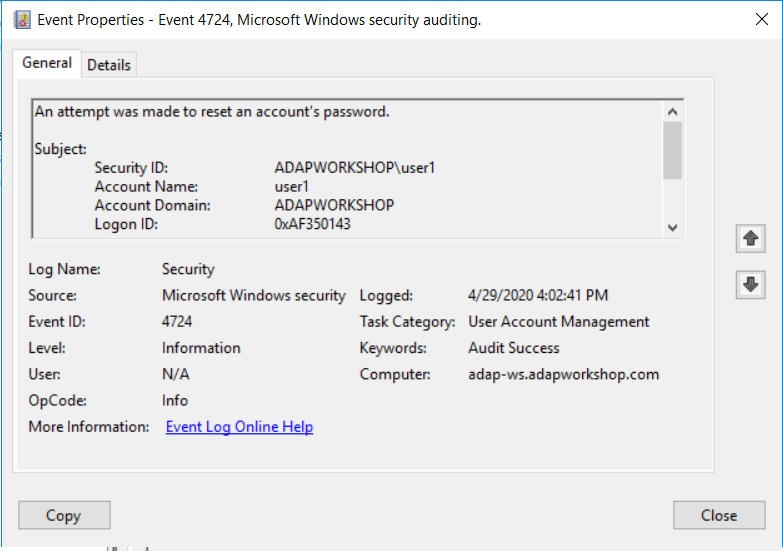
EventID 4724 describes any attempts made to reset the password of an account.
EventID 4723 describes any attempts by a user to change their password.
Does native auditing become a little too much?
Simplify password change auditing and reporting with ADAudit Plus.
Get Your Free Trial Fully functional 30-day trial