Direct Inward Dialing: +1 408 916 9892
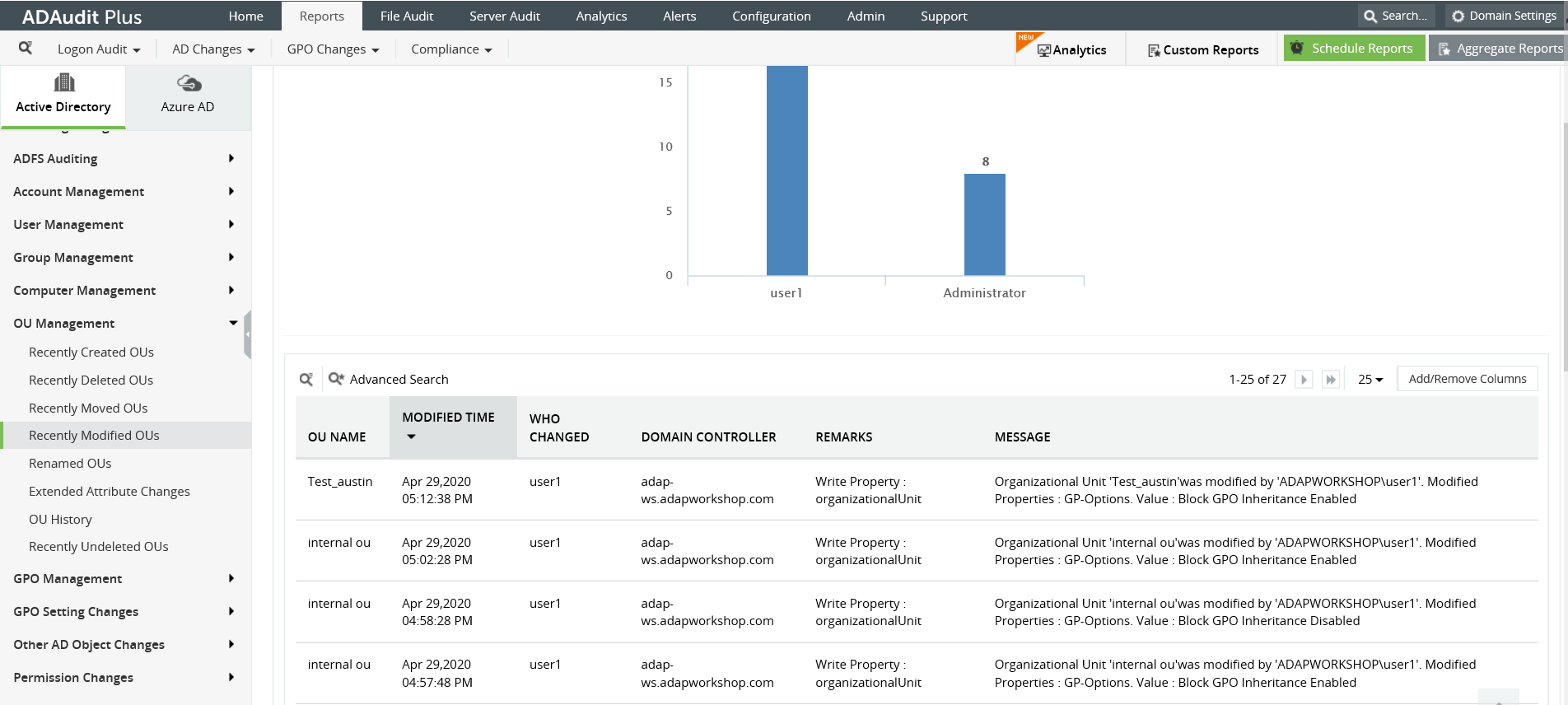
In the ADAudit Plus console, navigate to the 'Reports' tab and select 'OU Management'----> 'Recently Modified OUs'. This gives you a report on changes made to organizational units.
Advanced search functionality offers you multiple filter attributes to look for a specific event.
Easily export your reports in CSV, HTML, PDF and XSL formats.
Correlate between other user management and computer management reports to spot anomalous behavior on the network.
Launch the Server Manager in your Windows Server.
Under 'Tools', navigate to the 'Group Policy Management Console' (GPMC).
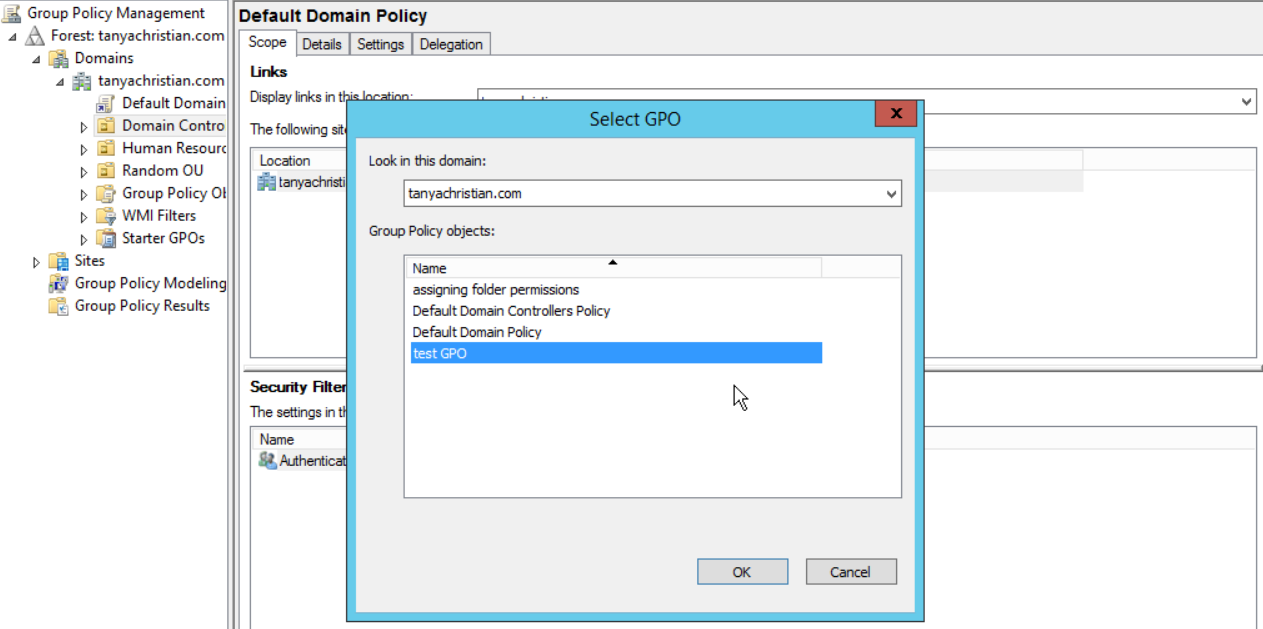
On the left pane right click the 'Domain Controllers' option. You can choose the 'Create a new GPO and link it here option' or 'Link an existing GPO' option accordingly.
Right click the desired GPO and select 'Edit'. This opens up the 'Group Policy Management Editor'. Expand the node and select the 'Computer Configuration'.
You can then select 'Policies' and navigate to 'Windows Settings'. Under 'Windows Settings' select 'Security Settings' and then navigate to 'Advanced Audit Policy Configuration'.
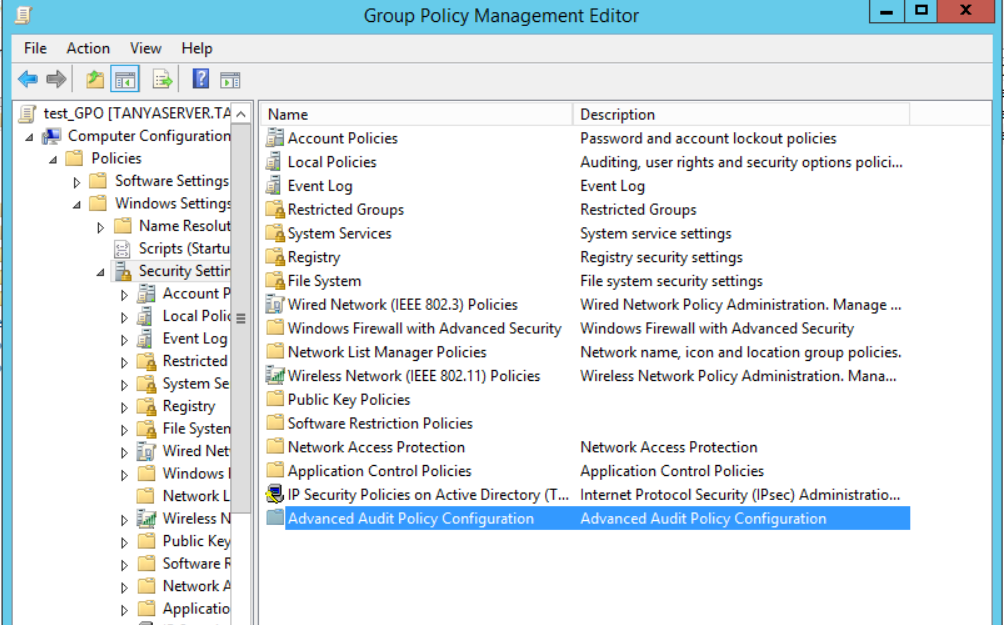
In the 'Advanced Audit Policy Configuration' option select 'Audit Policies' and expand the node. Then select 'DS Access and double click the 'Audit Directory Service Access' option.
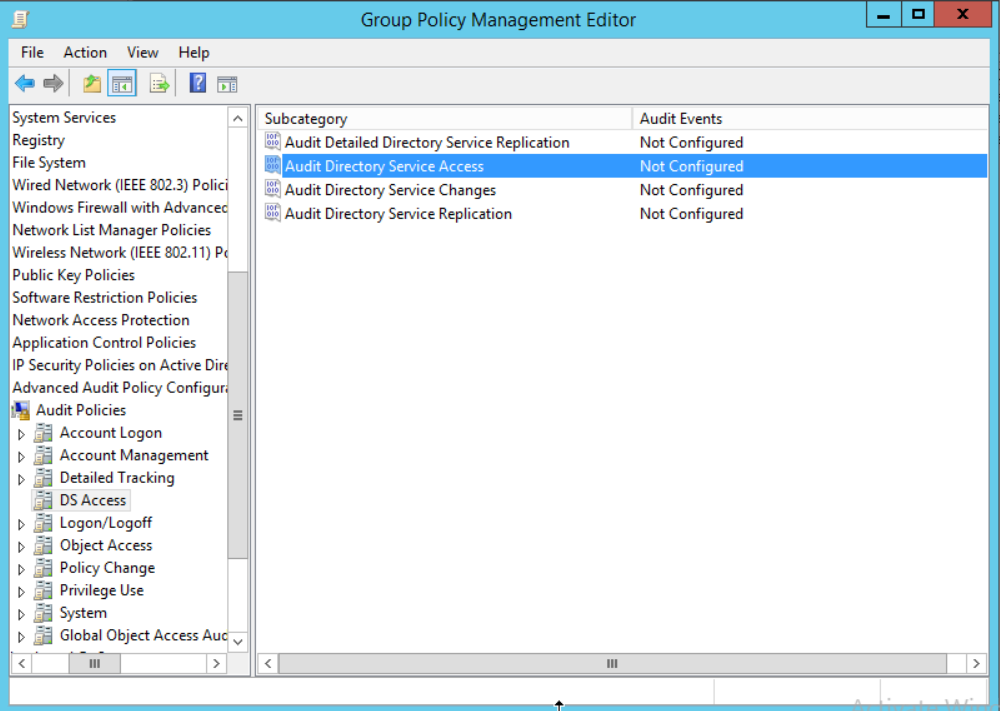
Configure this policy for both 'Success' and 'Failure'.
Also, configure 'Success and 'Failure' events for 'Audit Directory Service Changes'.
Exit the Group Policy Management Editor and return to the GPMC.
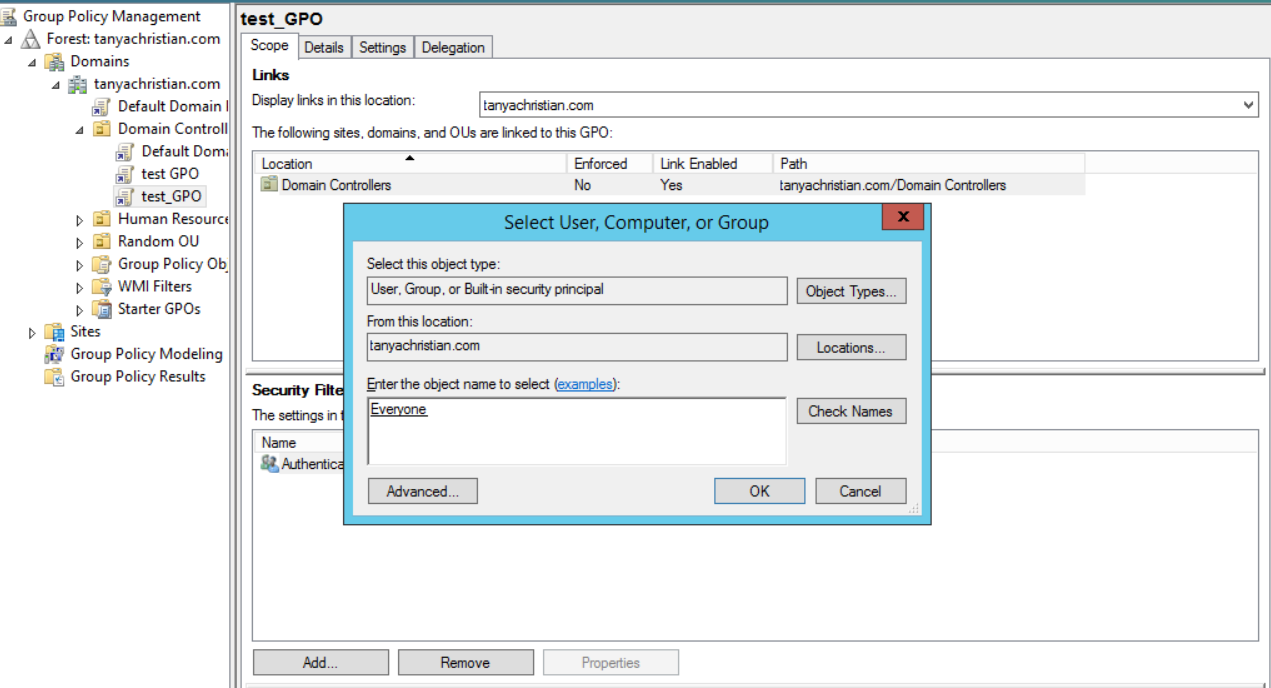
Go to the 'Domain Controllers' node and select the newly modified GPO. Under the 'Scope' tab on the right pane, you will find the 'Security Filtering' section. Select 'Add'.
This opens up the 'Select User, Computer or Group' window. Type 'everyone' in this window to apply this GPO to all objects.
You can now return to the GPMC. The group policy also needs to be applied through out the forest. You can do this by, opening up 'Run' on your server and executing gpupdate /force. You should receive a notification saying the policy update was successful.
From your 'Server Manager' go to 'Tools' and select 'ADSI Edit'.
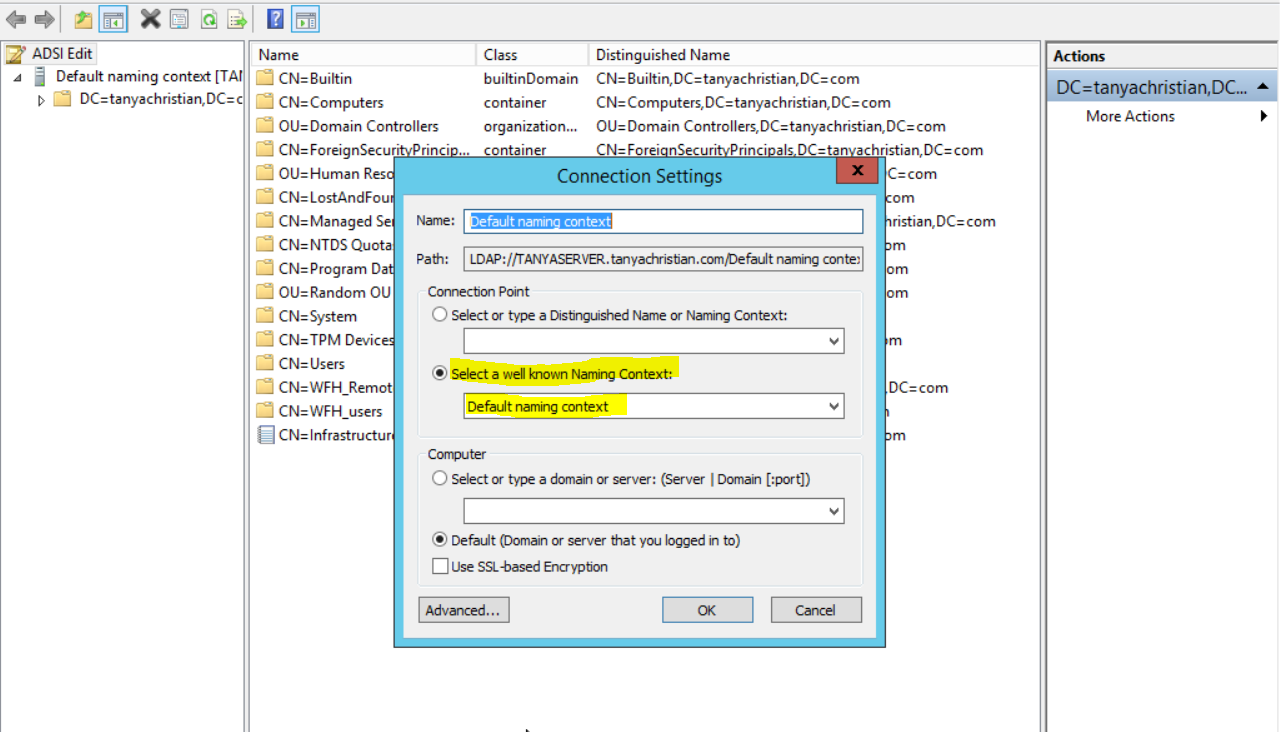
Right click 'ADSI Edit' node from the left pane and select 'Connect to' option. This pulls up the 'Connection Settings' window.
Select the 'Default Naming Context' option from the 'Select a well-known Naming Context' drop down list.
Click 'Okay' and return to the ADSI Edit window. Expand 'Default Naming Context' and select the associated 'DC' subnode. Right click this subnode and click 'Properties'.
In the 'Properties' window, go to the 'Security' tab and select 'Advanced'. After that select 'Auditing' tab and click 'Add'.
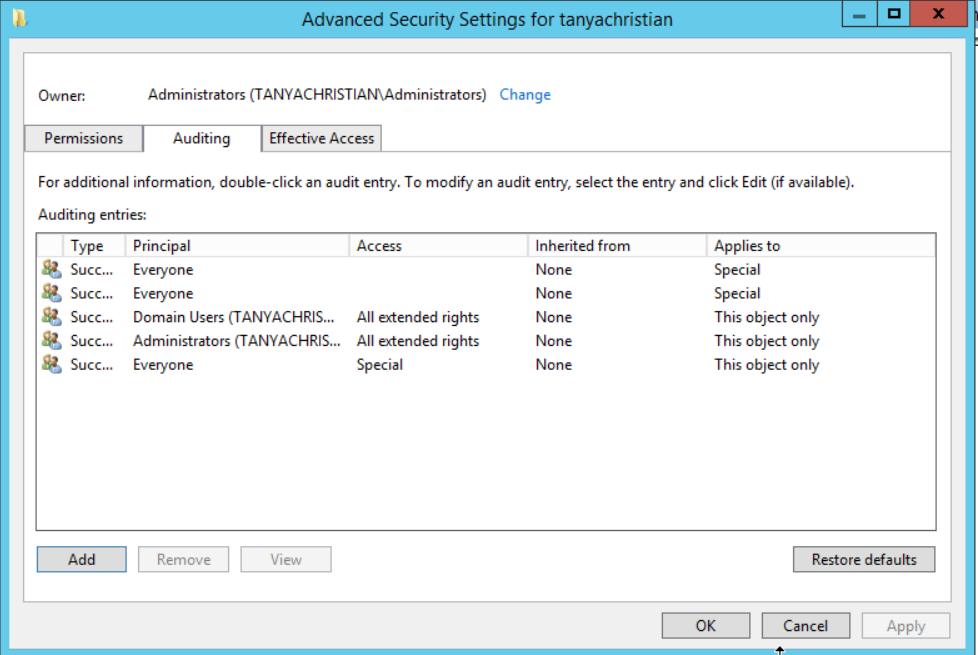
Click on ' Select a principle'. This will bring up a 'Select User, Computer or Group' Window. Type 'Everyone' in the textbox and verify it with 'Check Names'.
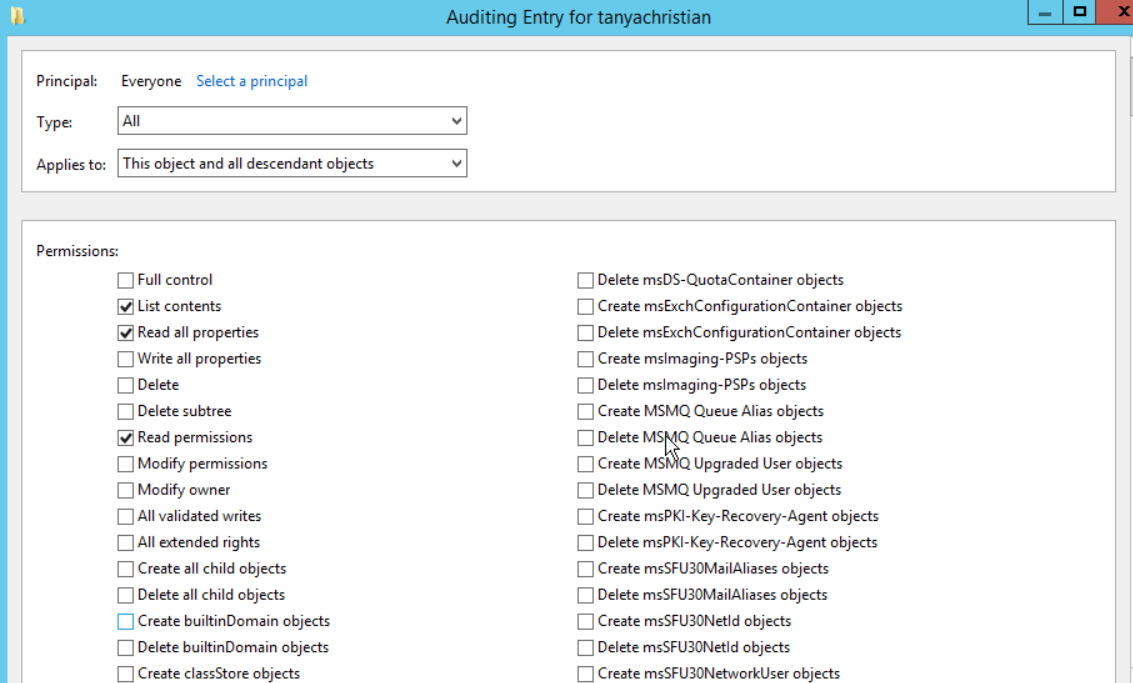
The principle in the 'Auditing Entry' window now shows 'Everyone'. In the 'Type' drop-down select 'All' to audit for both 'success' and 'failure' events.
In the 'Select' drop-down choose 'This object and all descendant object's. This allows the auditing of the OU's descendant objects. Select 'Full Control' in the 'Permissions' section.
Click 'Apply' and 'Okay' and close the window.
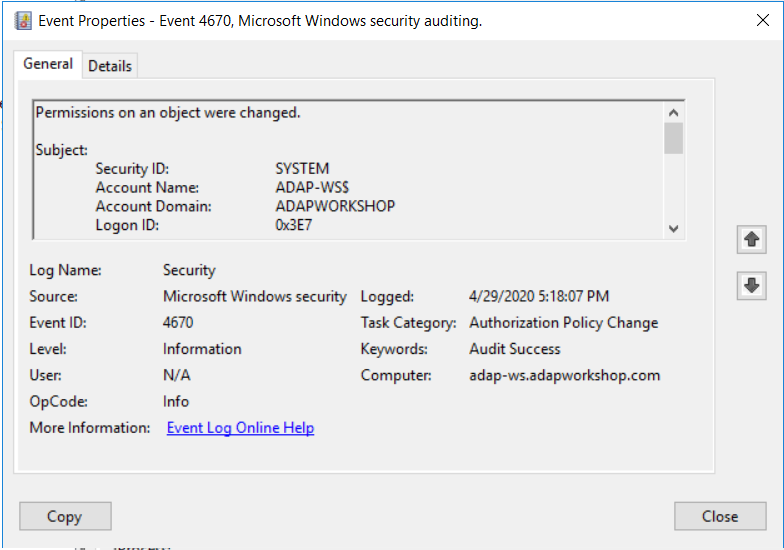
In the 'Event Viewer' you can look for the following Event IDs under 'Security Logs'.
Event ID: 4670 describes permissions on an object that were changed.
Does native auditing become a little too much?
Simplify file server auditing and reporting with ADAudit Plus.
Get Your Free Trial Fully functional 30-day trial