A beginner's guide to network traffic monitoring
With many services moving to the cloud, network infrastructures have become complex to maintain. While cloud adoption is advantageous productivity-wise, it can also give way to unauthorized access, leaving an IT system vulnerable to security attacks.
To stay sure of their network's security and smooth performance, IT admins need to monitor every link being accessed by users and the traffic consumed by every device. This process of analyzing how each packet is being transmitted over the network, how users are using the network, who is using it, and the volume of bandwidth utilized is known as network traffic monitoring.
The roadmap to network traffic monitoring
Network traffic monitoring can generally be divided into three steps:
1. Choosing the right data source
It is best to choose which data source you want to receive the traffic data from, then choose a tool.
Network traffic monitoring can be carried out in two ways: packet capture and flow analysis.
Packet capture
Packet capture is a traditional network traffic monitoring tool that will provide you with insights about how many packets have moved through the network. As a traditional traffic monitoring method, packet capture can offer features like VoIP reporting and web domain reporting.
Another main feature is deep packet inspection (DPI), which will review both the header and data portion of the packets. Unlike conventional packet filtering, DPI will read what is inside the header information and allow you to pinpoint the source of the data packet. Analyzing this information will help you find the root cause of an issue.
Flow analysis
In contrast, flow analysis gives you a statistical summary of the traffic data, not the exact data. It captures data from routers, switches, and firewalls and gives you real-time insights with high-level visibility into parameters such as source IPs, destination IPs, source ports, and destination ports.
Packet capture or flow analysis: which is better?
There are three main differences between these two methods
| Packet capture | Flow analysis |
|---|---|
| While packet capture can give you the exact traffic data as the traffic is evaluated from packet to packet, it consumes more storage. Therefore, you cannot archive all the historical data for analysis or drill down to the root cause. | Since flow analysis only aggregates the traffic data, it consumes less storage. Therefore, you can have a view into the historical data and get to the root cause of all the bandwidth-related issues. |
| Packet capture reviews even the payload of the packets, which can sometimes be beneficial but will not be necessary in most cases. Therefore, when you use a tool that is based on packet capture, your server load will increase, which in turn might affect network communications | By contrast, network traffic monitoring tools that use flow analysis only review the metadata, like the information on the authenticated user. Therefore, they will not induce an extra load on the server side while also helping you with security. |
| For packet capture, you need to connect cables between mirror ports and the DPI application. For every tool, the ease of implementation varies, so user-friendliness is not a strength for packet capture. | Flow-based network traffic monitoring solutions do not require any cables, and you will not even need an external agent or software clients in your system. |
2. Analyzing the endpoints
Once you have set up the monitoring tool in your network, you can start analyzing network endpoints, such as devices, interfaces, and applications. Devices include servers, routers, switches, and firewalls.
You can find the statistical traffic summary for the discovered network elements and drill down to find the traffic information with parameters like the network users and their geolocations.
Although monitoring network traffic of the entire infrastructure is beneficial, it is always better to monitor network traffic of certain endpoints where all the data converges. For example, instead of carrying out real-time network traffic monitoring for every IP address, you can group the IP addresses, interfaces, applications, and WLCs based on departments and branch offices. This way, you can view network traffic, see how each department is utilizing the allocated bandwidth and which departments need more bandwidth.
You can also define user roles and provide different types of accessibility for every role. With this, you will be able to save your time and effort in troubleshooting bandwidth issues. Traffic monitoring software can also help you manage your bandwidth requirements.
3. Optimizing with data
Going forward, you need to manage the network bandwidth using all the data gained. That is, you still need to keep track of aspects like performance and security even though there should be no potential drawbacks in your network now. Because while monitoring is great for knowing what is happening in the present, what you do with that data to curb future bandwidth challenges is also important, especially when your organization is growing.
The best network traffic monitor will let you know whenever the performance deviates from its normal behavior. You can set up the minimum or maximum bandwidth usage for that network element and detect any security attacks.
You can also set QoS policies to define which link or application has the highest priority to make sure all the business-critical applications operate seamlessly. While real-time traffic monitoring is usually sufficient, sometimes comparing traffic trends and looking into historical data will provide you clarity about changing network bandwidth requirements.
Choose tools that offer customizable reports about bandwidth performance, which help you identify blackouts and network shortages, and planning strategies to maximize performance, which we will discuss here.
The importance of using NetFlow traffic monitoring tools for organizations
With so many devices and interfaces in an organizational network, network administrators should be aware if the traffic of every endpoint is normal. This is because there might be unpredictable traffic spikes from some devices, which can slow down the performance of the network or even resemble security threats. Without a traffic monitoring tool, it is harder to prevent performance issues from escalating and to detect internal and external attacks.
A traffic monitor is necessary in today's IoT and cloud-based services world. When such resource-intensive applications are used in an environment, the bandwidth left for other important operations can become insufficient. So network admins should view what traffic is passing between each interface so they can prioritize or block it
Here are some great advantages you can gain from a free network traffic monitoring tool besides optimal network performance:
- Proactive monitoring of all your devices to help you find the root cause of bandwidth bottlenecks
- Deeper insights into how much traffic has been consumed by each element
- The ability to shape app traffic and apply effective QoS policies to ensure better performance for business-critical applications
- Improved detection of unusual traffic spikes and network anomalies
- Tracking of the availability and health of voice, video, and data traffic
- Real-time and aggregated threshold alerts that notify you when the network exceeds its threshold behavior
- A reporting feature that interprets the changing bandwidth requirements and trends from the historical data
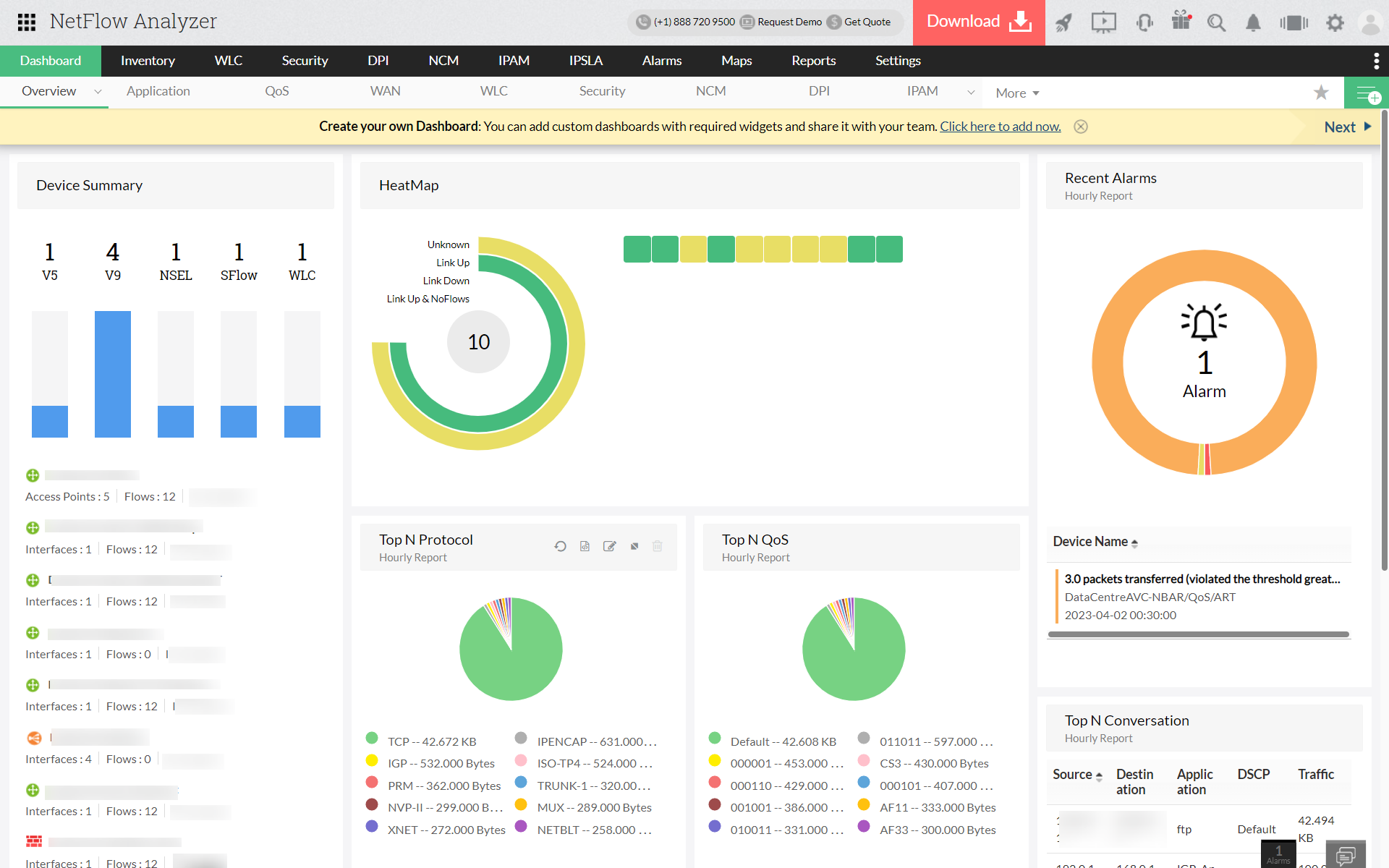
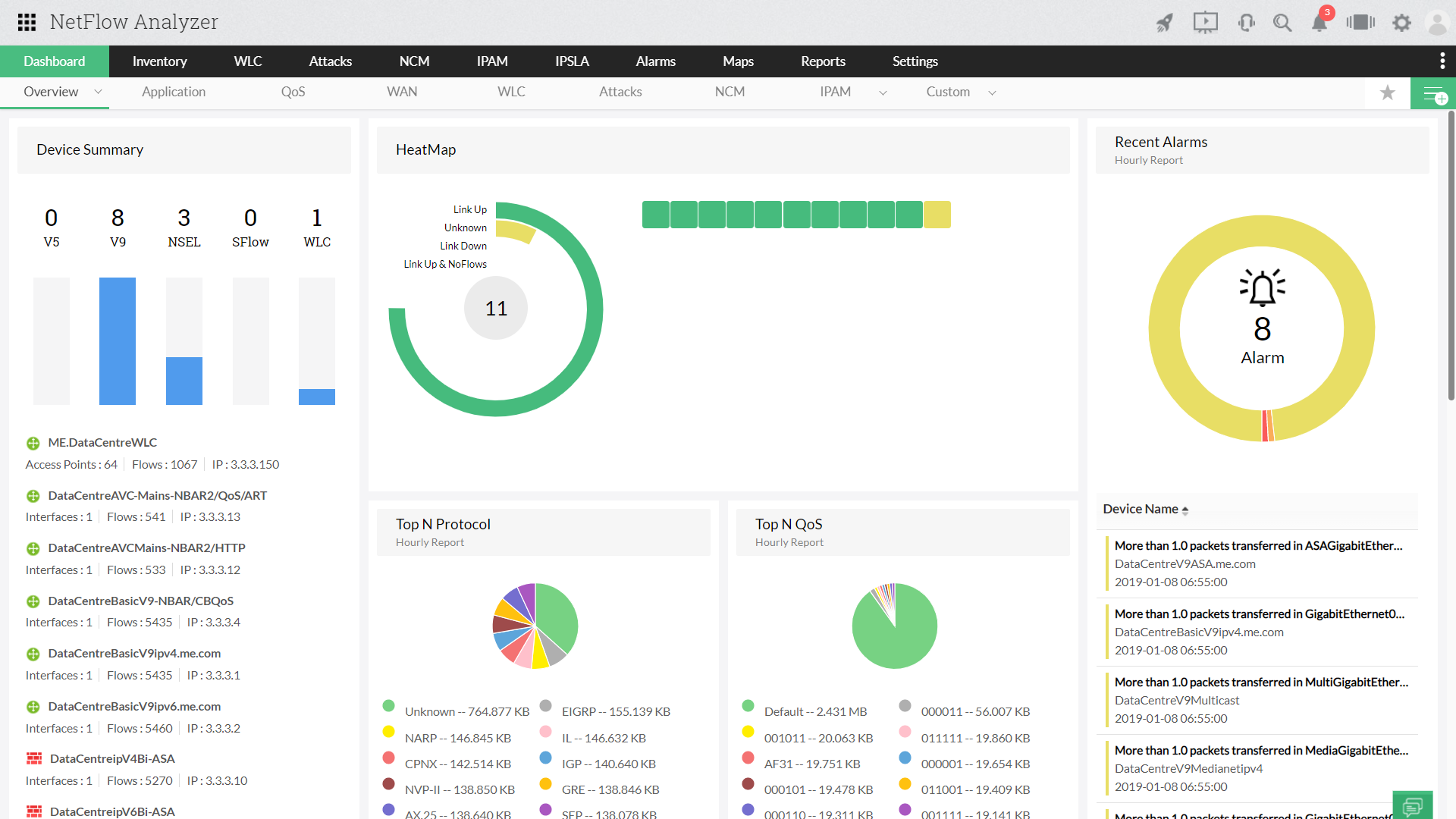
How NetFlow Analyzer can come in handy
A Windows or Linux network traffic monitoring tool like ManageEngine NetFlow Analyzer gives you deep insights into the traffic data for your devices, interfaces, and applications.
With NetFlow Analyzer, you can leverage both flow analysis and packet capture technologies. You can install the network traffic monitor on-premises and configure flow such that the tool starts collecting flows from your routers immediately. After the discovery process, the tool will start showing you the overview of the flow data collected with the top talkers of the network so you can start your bandwidth monitoring.
You can troubleshoot your network bandwidth issues faster when you discover the source and destination IP addresses with flow analysis technology. However, NetFlow Analyzer, a reliable traffic monitoring tool also offers a DPI mechanism that shows you metrics like the response times of applications, networks, and servers.
Traffic monitoring strategies that work well with NetFlow Analyzer
Group the network elements: When monitoring individual entities like source and destination IP addresses, WLCs can give you more insights as you do not have to manually glance at each and every interface while troubleshooting. In these cases, you can group these elements according to departments or branch offices and troubleshoot easily.
Track configurations: It is always necessary to routinely check the configurations of your network devices, like firewalls and routers, to make sure they do not allow unauthorized or harmful WAN links to interact with your network infrastructure. You can use NetFlow Analyzer's Network Configuration Manager (NCM) add-on to keep track of these configuration changes and maintain backups to mitigate breaches.
Set alerts: Monitoring has to be continuous since a security breach could start at the most unexpected hour. You must set alerts that notify you when there are any deviations from the normal traffic limit.
Focus on particular data: It is better to isolate the traffic you are most concerned about than to analyze everything and turn a blind eye to the evident network issues. For example, if you are facing an issue with a video conferencing app's performance, you must look at the stability of the network instead of the FTP traffic activity.
With wider visibility comes the opportunity for you to learn exactly what your organization's bandwidth capacity is. This allows you to optimize your existing bandwidth plans without investing in network upgrades. Try the fully functional demo of NetFlow Analyzer for your business now.