How Deep Packet Inspection works in NetFlow Analyzer
Bandwidth metrics alone tell you how much traffic is moving, not why performance is degrading. NetFlow Analyzer has efficient traffic and application performance monitoring, and with DPI it goes further, helping IT teams get the complete visibility needed to understand the source of a problem faster.
Deep packet inspection capabilities in NetFlow Analyzer
NetFlow Analyzer brings this capability through the Remote Collector, which can be configured as a DPI engine. When set up this way, the Remote Collector captures mirrored packets and delivers response time and traffic volume. This data flows into NetFlow Analyzer, where it can be viewed across URLs, applications, and conversations, giving IT teams a clear picture.
Application and network response time monitoring
With the captured application response time and network response time across URLs, applications, and conversations, IT teams can view both metrics side by side and determine whether a performance issue is coming from the network or from within the application itself, without having to rely on guesswork or broad traffic averages.
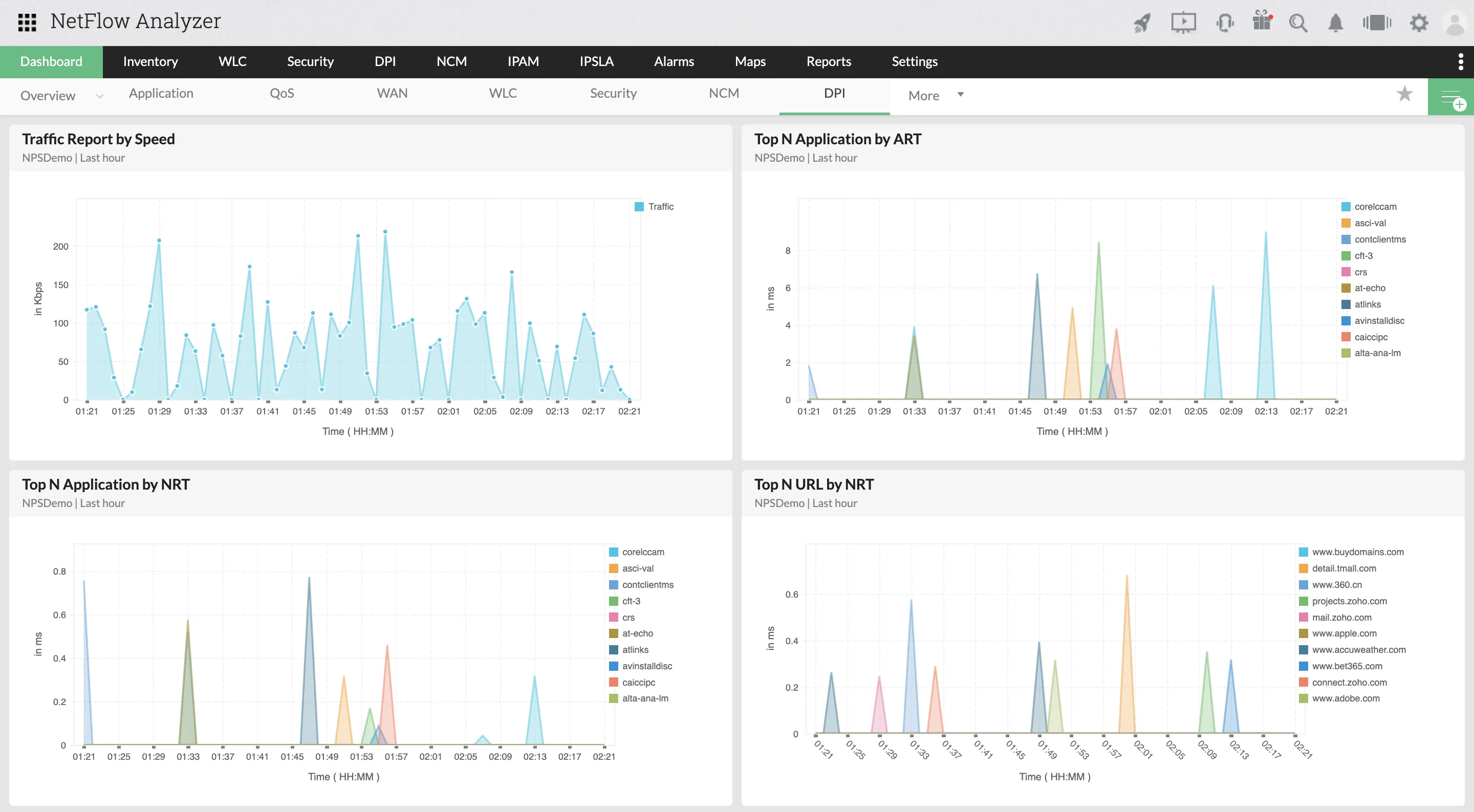
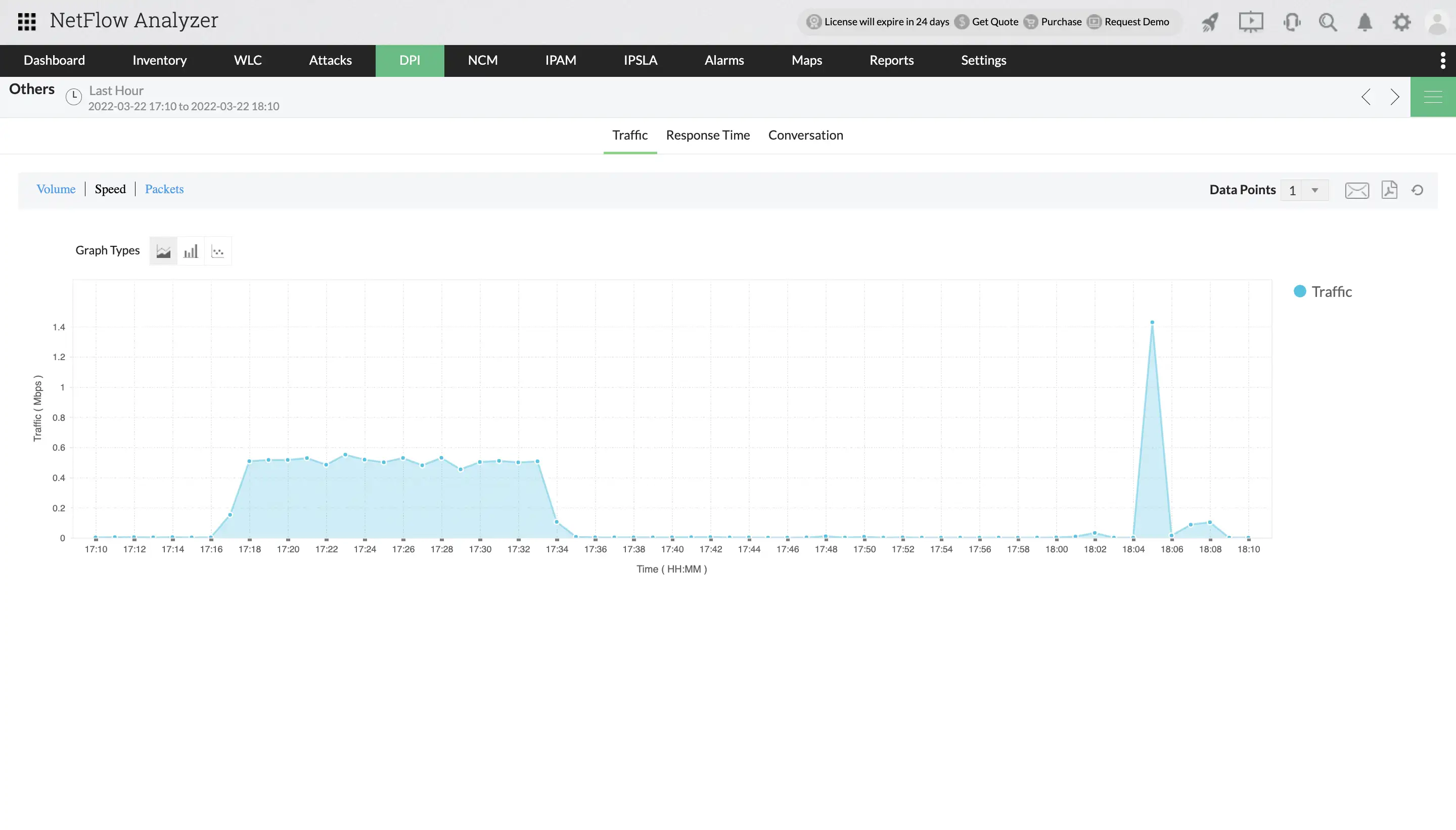
Traffic volume visibility
For TCP traffic, DPI captures volume data across URLs, applications, and conversations. For UDP traffic, it captures average volume by application, source IP, and destination IP. This gives teams a detailed picture of how traffic is distributed across the network at any given time.
DNS monitoring and DHCP monitoring
Deep packet inspection analyzes packet-level data to capture real-time DNS query and response activity. This helps IT teams monitor DNS performance, identify resolution delays, and detect issues that may be affecting application availability before users are impacted. Also, it captures real-time DHCP transaction data including client counts, failure rates, and average response times. This gives IT teams early visibility into IP address assignment issues that can disrupt network connectivity if left undetected.
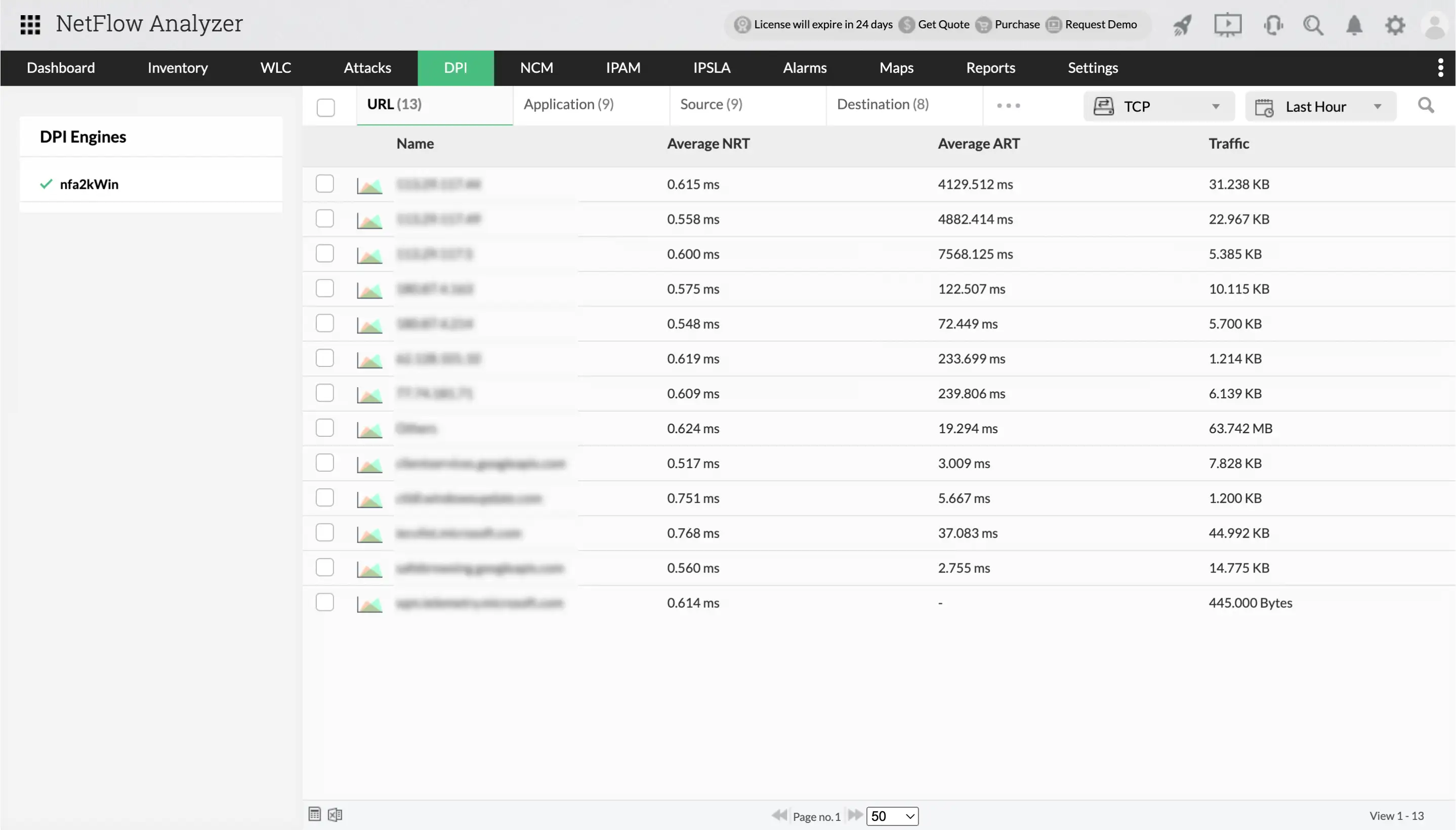
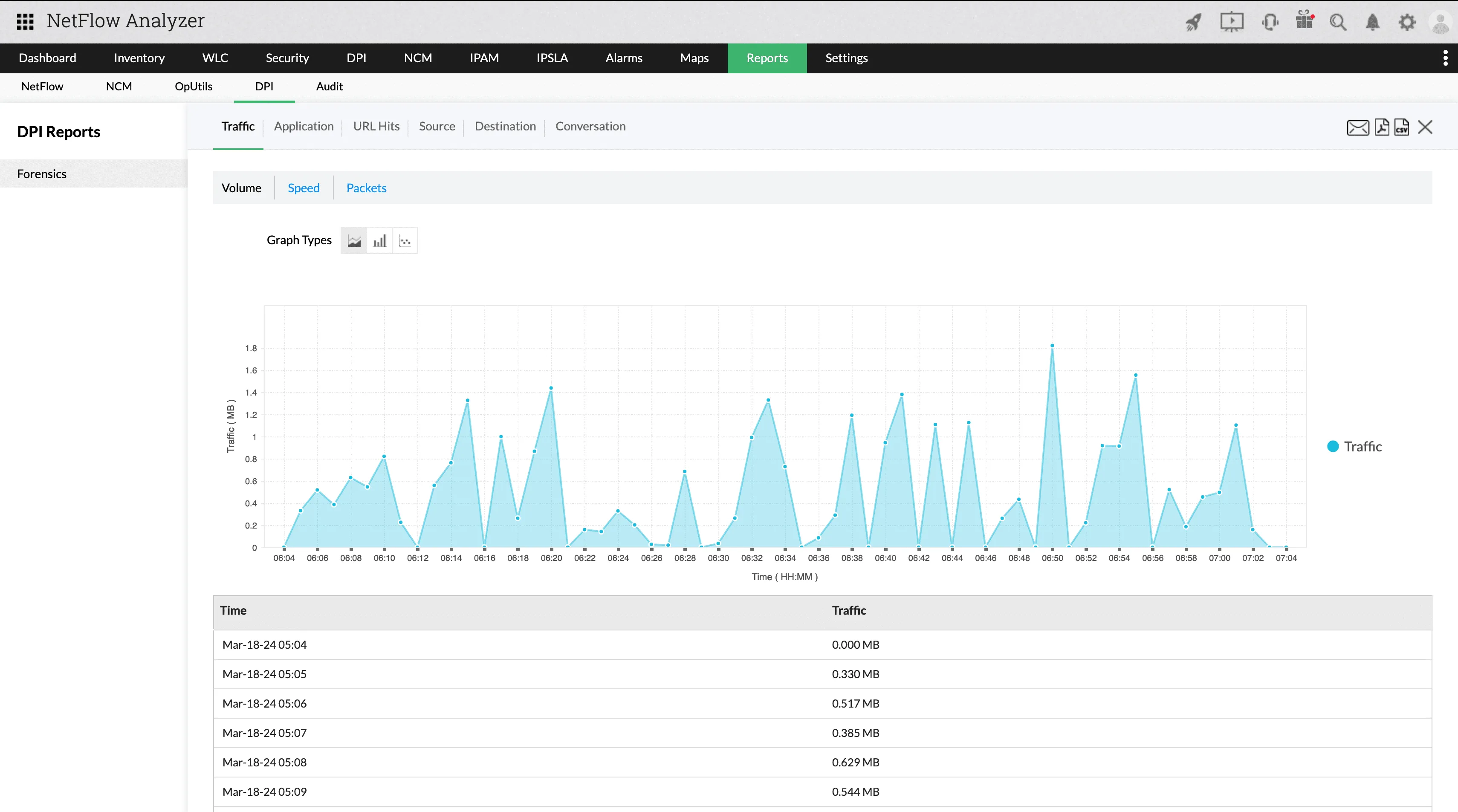
Traffic reporting and faster troubleshooting
NetFlow Analyzer converts DPI data into network reports that help IT teams troubleshoot performance issues with greater precision. Teams can generate reports based on application response time, network response time, and traffic volume across TCP and UDP protocols. This gives teams the detail they need to quickly identify where a problem is occurring.
Deep packet inspection vs packet capture vs flow monitoring
Modern network monitoring technologies differ in how they inspect traffic, the level of visibility they provide, and the operational impact they create. Understanding these differences helps enterprises choose the right approach for their environment.
| Technology | What It Inspects | Best For | Impact |
|---|---|---|---|
| Deep Packet Inspection (DPI) | Application response time, network response time, traffic volume, DNS query/response data, DHCP transaction data by protocol | Application performance diagnosis, separating network vs. application latency, DNS and DHCP monitoring | Moderate. Remote Collector handles capture independently. |
| Packet Capture | Full packet payloads stored for analysis | Forensics, deep troubleshooting, compliance audits | Heavy infrastructure and storage overhead |
| Flow Monitoring | Traffic metadata such as source, destination, ports, and protocols | Scalable traffic visibility and performance monitoring | Lightweight and scalable |
Business benefits of DPI with NetFlow Analyzer
Reduce time to diagnosis
When a performance issue arises, knowing whether the problem is in the network or the application layer changes everything. As we discussed, DPI provides both application response time and network response time, helping IT teams get to the right answer faster.
Monitor application response time granularly
DPI provides response time visibility across URLs, applications, and conversations. This gives teams a granular view of where degradation is occurring, making it easier to track down the exact source of a slowdown.
Gain real-time visibility into DNS
DPI captures DNS query and response data at the packet level in real time helping teams identify resolution delays and DNS performance issues that would otherwise go unnoticed until they start affecting application availability.
Stay on top of DHCP activity
DPI shows DHCP transaction data including client counts, failure rates, and average response times. This gives early warning of IP address assignment issues before they quietly start disrupting connectivity across the network.
Troubleshoot faster with protocol-level detail
By capturing data across TCP, UDP, DNS, and DHCP, Deep Packet Inspection gives IT teams the protocol-level context they need to isolate root causes accurately and resolve issues with confidence.
Ready to pinpoint where your network performance issues originate?
FAQs
What is deep packet inspection?
Deep packet inspection (DPI) is a network traffic analysis technique that goes beyond measuring bandwidth to know how applications are actually performing.
Why does deep packet inspection matter in modern enterprise networks?
Bandwidth metrics are insufficient for diagnosing performance issues and flow monitoring provides only traffic metadata but cannot distinguish whether latency originates at the network layer or within the application itself. DPI addresses this by capturing application response time, network response time, and protocol-level data including DNS query, and more. This gives IT teams the granular visibility needed to isolate causes accurately.
Is NetFlow Analyzer a deep packet inspection tool?
Traditional DPI can be resource-intensive. NetFlow Analyzer sidesteps this by having the Remote Collector handle packet capture locally, processing traffic at the source rather than routing everything through a central system. Only summarized response time and volume data is sent to NetFlow Analyzer, keeping the impact on network performance minimal.
What is the difference between DPI and flow monitoring?
DPI inspects packet content for detailed visibility, while flow monitoring analyzes traffic metadata such as source, destination, and protocol information.
Does DPI affect network performance?
Traditional deep packet inspection can be resource-intensive, requiring significant processing power and storage for full packet capture. In NetFlow Analyzer, the Remote Collector handles packet capture independently, processing traffic locally and sending summarized response time and volume data to NetFlow Analyzer. This architecture avoids the overhead associated with centralized packet capture systems, keeping the impact on network performance minimal.